Clear Sky Science · en
RNN-based detection of IoT malware using diverse feature engineering methods
Why smart gadgets need smarter protection
From baby monitors to factory sensors, billions of everyday gadgets now sit online, quietly exchanging data. This convenience comes with a hidden cost: many of these small devices are easy targets for malicious software that can spy, steal, or disrupt. The study behind this article asks a simple question with big consequences: can we train an artificial brain to spot such attacks in the stream of network traffic before they do harm?
The growing problem of invisible threats
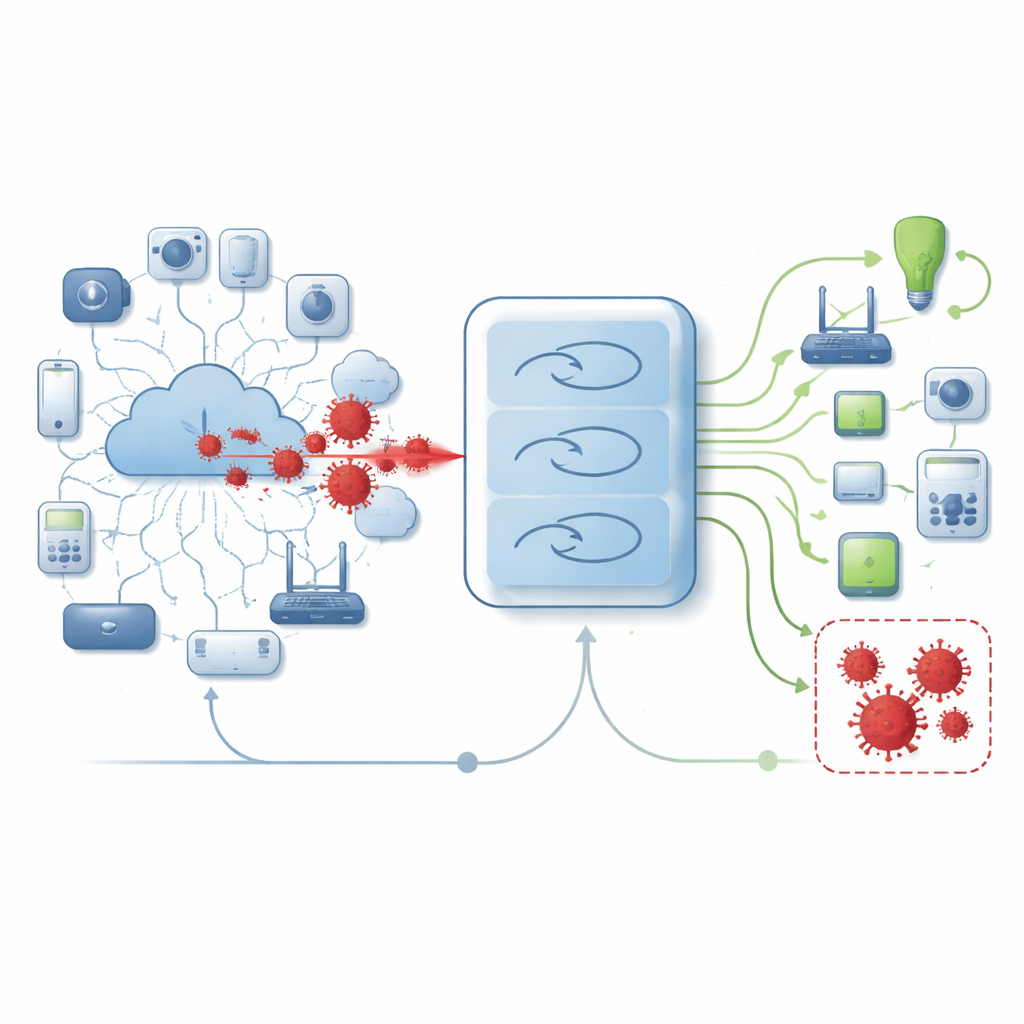
Malware is a catch all term for programs designed to hijack computers and connected devices. In the world of the Internet of Things, this includes home cameras, smart lights, industrial sensors, and more. These devices often have little computing power and weak built in security, yet they are always connected. Criminals exploit this by crafting new strains of malware that slip past traditional scanners, which usually look for known patterns or signatures. As a result, defenders are turning to learning based systems that can pick up subtle signs of trouble in how data moves across a network.
Teaching a model to read network behavior
The researchers built a detection system that watches network traffic from IoT environments and decides whether each connection looks normal or malicious. Instead of relying on a single trick, they combine several ways of describing the data before feeding it into a recurrent neural network, a type of model that is good at spotting patterns across sequences. They first clean the data, remove duplicates and damaged records, and convert text fields such as protocol names and service types into numbers. Then they scale all values into a common range so that no single field dominates the learning process.
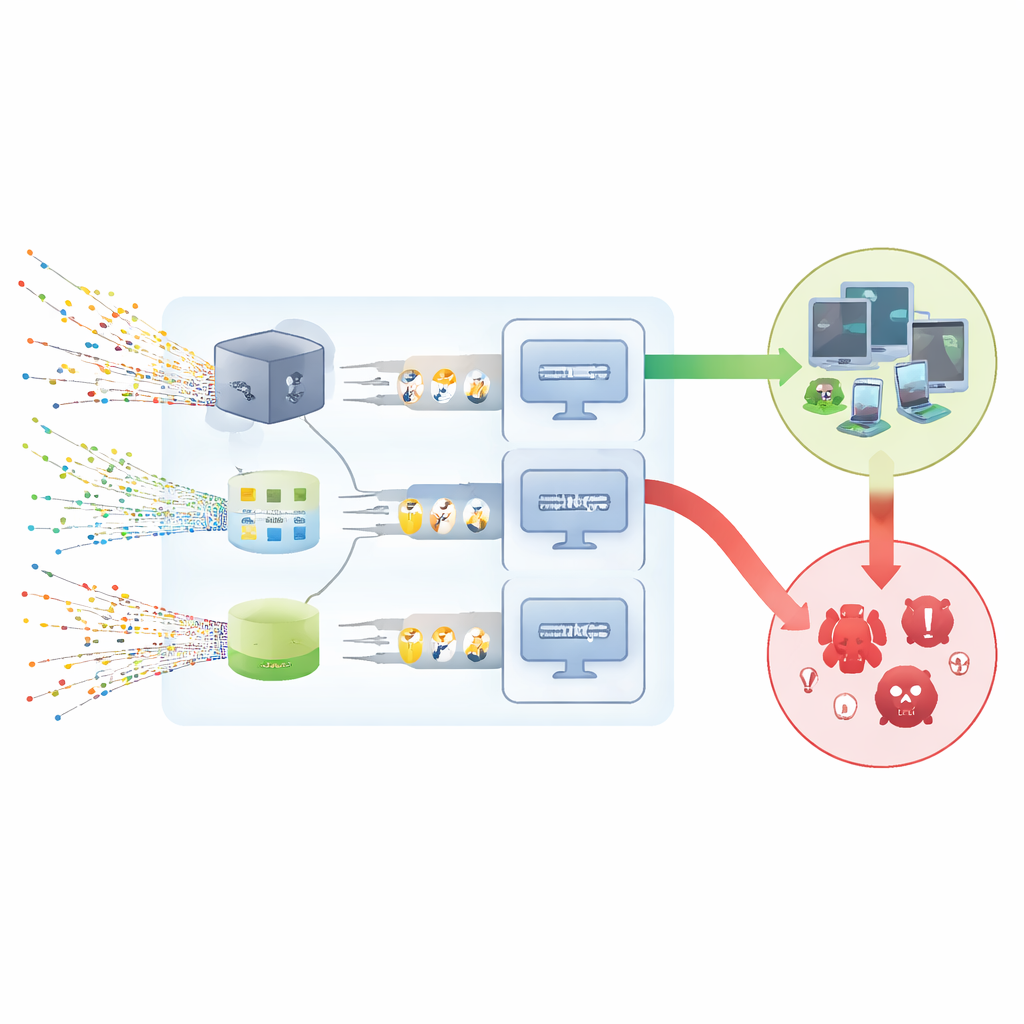
Turning messy traffic into useful signals
To make the raw records more informative, the team uses a toolbox of feature engineering methods. Simple counts of words, measures of how rare certain terms are, and word embedding techniques help capture the meaning of text based fields like attack category or connection state. At the same time, a method called principal component analysis compresses many numeric details down to a smaller set that still reflects almost all of the original variation. Another method, recursive feature elimination, repeatedly removes the least helpful inputs until only the most important ones remain. Together, these steps turn high volume traffic logs into compact, rich descriptions that a model can learn from efficiently.
How the different models performed
The study tests three versions of the system, each pairing a slightly different data description with a stack of simple recurrent layers. All are trained and checked using a widely used public dataset of network flows that includes both normal activity and nine types of attacks. The authors carefully avoid data leakage by learning all settings only on the training portion and then applying them unchanged to validation and test portions. Across five rounds of cross checking and a separate final test set, the models reach extremely high scores on key measures: they rarely miss an attack, rarely flag normal traffic by mistake, and draw a nearly perfect line between safe and unsafe behavior.
What this means for everyday security
For a non specialist, the main message is that combining several views of the same network data with a tailored learning model can make it much easier to spot when an IoT device is acting under the influence of malware. In this study, the best version of the system reaches almost flawless detection on the chosen dataset, suggesting that such designs could greatly strengthen intrusion detection tools used by companies and service providers. The authors stress that results on one dataset are not the final word, but their work shows that smart preparation of data, paired with compact neural networks, can turn streams of seemingly ordinary traffic into early warnings about hidden threats.
Citation: Abd-Ellah, M.K., Alsayed, N.A., Elkomy, O.M. et al. RNN-based detection of IoT malware using diverse feature engineering methods. Sci Rep 16, 14727 (2026). https://doi.org/10.1038/s41598-026-51074-0
Keywords: IoT malware, network intrusion detection, deep learning security, recurrent neural networks, feature engineering