Clear Sky Science · en
Ensemble-based detection of distributed denial-of-service attacks in IoT networks using majority decision mechanisms
Why Smart Gadgets Need Strong Defenses
From smart doorbells and baby monitors to factory sensors and hospital equipment, more and more everyday objects are now connected to the internet. This convenience comes with a hidden danger: attackers can take over large numbers of these tiny devices and use them together to overwhelm online services, in what is known as a distributed denial-of-service (DDoS) attack. This paper explores a new way to spot such attacks quickly and reliably, even though these gadgets have very limited computing power.
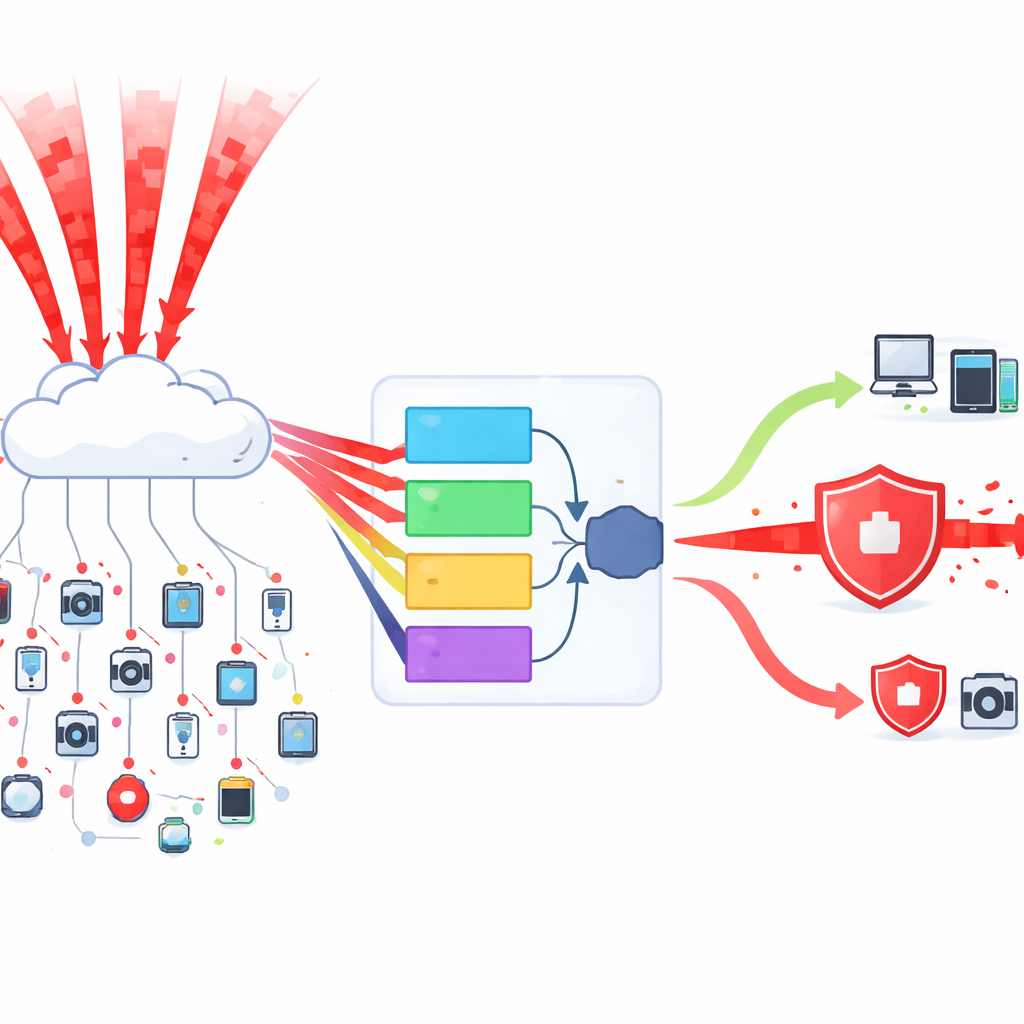
How Attackers Turn Gadgets into a Flood
In a DDoS attack, thousands or even millions of compromised devices send useless data toward a target at the same time, clogging the network so real users cannot get through. Internet of Things (IoT) gadgets are especially attractive targets because they are cheap, widespread, and often poorly protected. They also speak many different network “dialects,” which makes it hard for traditional security tools to learn what normal traffic looks like. Existing detection systems often struggle in this messy environment, either missing attacks or raising too many false alarms that waste time and resources.
Letting Several Minds Decide Together
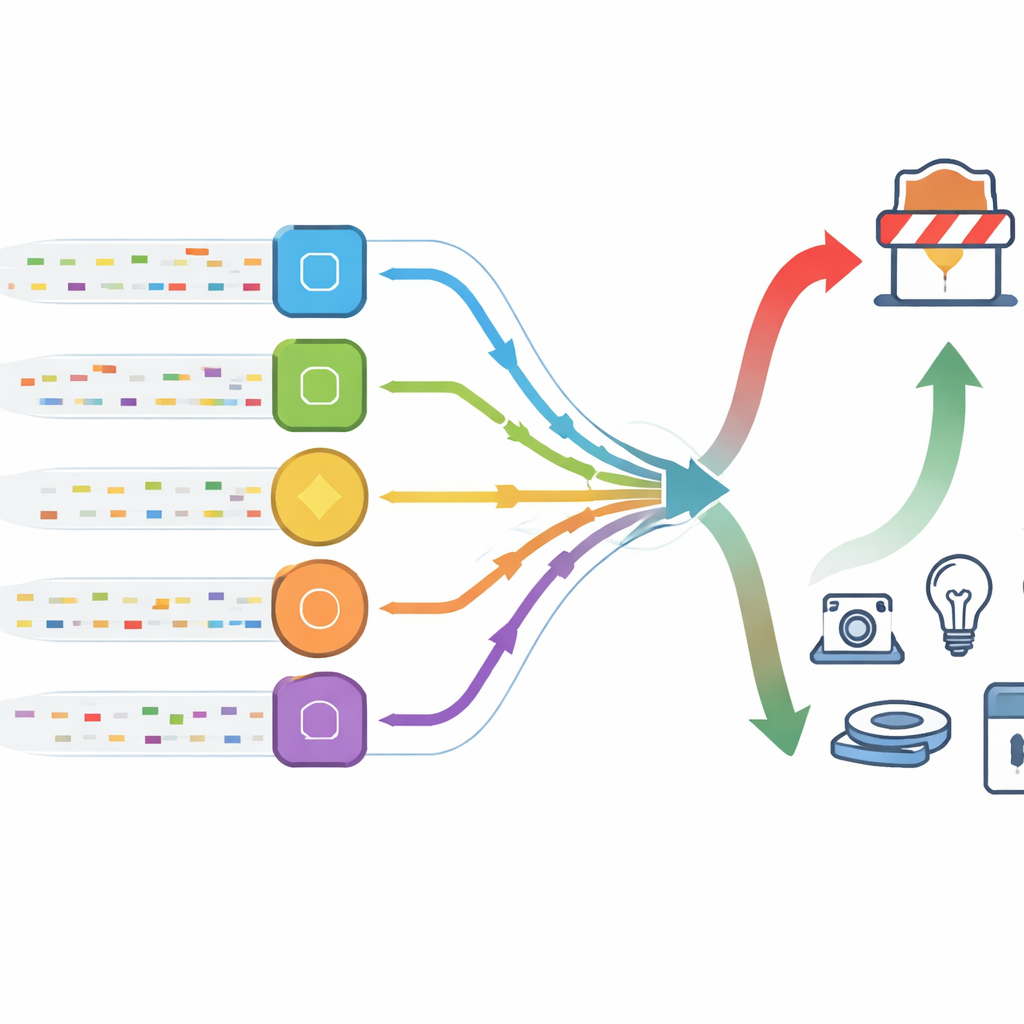
The authors propose an intrusion detection system that works like a small committee rather than a single judge. Instead of relying on one machine-learning model, they select five different high-performing models and let each one vote on whether a piece of traffic is normal or part of an attack. If most of them say “attack,” the system treats it as such. This majority-voting strategy means that even if one model is fooled, the group as a whole is less likely to make a mistake. The five models are chosen from a larger pool based on how accurate, fast, and stable they are, so the final committee combines different strengths while keeping computing costs low.
Cleaning and Balancing the Data First
To train this committee, the researchers first prepare very large real-world datasets that record both normal network behavior and many kinds of DDoS traffic. They remove broken entries, rescale the numbers so that features are on comparable ranges, and then tackle a key problem: attack traffic is far more common than safe traffic in these records. To avoid a biased system that simply shouts “attack” all the time, they trim back the overly common class and use a technique called synthetic sampling to generate realistic extra examples of the rarer class. They also pick only the most informative measurements from dozens of possible network features, which reduces noise and speeds up learning without sacrificing insight.
Near-Perfect Detection with Fewer False Alarms
Once trained, the voting system is tested on unseen data from two well-known collections of network traffic. On several major kinds of DDoS attacks that abuse different network services, the method reaches detection rates between 99.87% and 100%. Just as important, the number of safe connections that are mistakenly flagged as attacks is extremely low—below three hundredths of a percent in key tests. The authors compare their committee approach with popular alternatives, including deep learning models that process data over time. While some rivals come close in accuracy, they tend to run much more slowly and demand more memory, making them less suitable for tiny IoT devices and busy edge gateways.
What This Means for Everyday Connected Life
For non-specialists, the main message is that we can protect swarms of simple smart devices using clever combinations of relatively light-weight tools, rather than relying on one huge and complex model. By letting several different detectors “talk” to each other and vote, this approach achieves both high confidence in spotting attacks and a very low rate of false alarms, all while staying efficient enough for real-world use. As smart homes, hospitals, factories, and cities continue to fill with connected gadgets, such ensemble-based defenses offer a practical way to keep vital services available even when attackers try to turn our own devices against us.
Citation: Cheng, S., Feng, X. Ensemble-based detection of distributed denial-of-service attacks in IoT networks using majority decision mechanisms. Sci Rep 16, 10886 (2026). https://doi.org/10.1038/s41598-025-23638-z
Keywords: IoT security, DDoS detection, intrusion detection, machine learning ensemble, network traffic analysis