Clear Sky Science · en
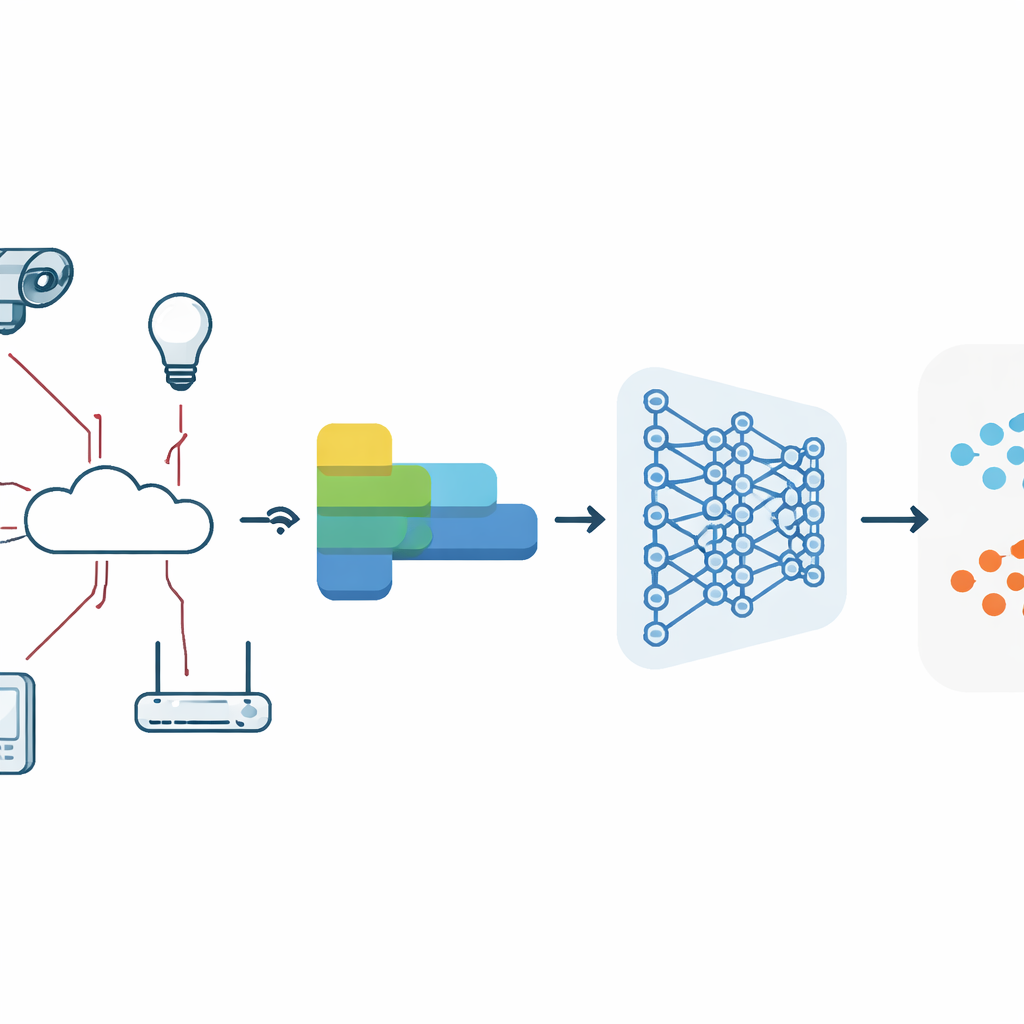
Malware detection in IoT networks with CNNs and integrated feature engineering
Why smarter malware detection matters
Everyday objects—from baby monitors and smart locks to industrial sensors—now sit on the internet, quietly sending and receiving data. This convenience comes with a hidden cost: cybercriminals can turn those devices into spying tools or building blocks for massive online attacks. Traditional antivirus tools were not designed for this fast-changing world. This paper explores how a new combination of data cleaning, clever data representation, and deep learning can catch malicious activity in these connected devices with remarkable accuracy.
Hidden threats in connected gadgets
Malware is software built to do harm: spying on users, stealing information, or hijacking computers and gadgets. In Internet of Things (IoT) networks, such malware can quietly move through traffic between devices like cameras, routers, and smart meters. Attackers constantly change their tactics, using tricks to conceal their code and imitate normal behavior. Older protection methods often depend on known “signatures” or simple rules, which struggle to keep pace with these shifting patterns. To protect modern networks, defenders need tools that can learn subtle clues from vast streams of traffic and adapt as attackers evolve.
Turning messy traffic into meaningful signals
The authors start from a large, realistic collection of network connections called UNSW-NB15, which includes both everyday traffic and several types of attacks. Raw network data is messy: it contains missing entries, duplicated records, inconsistent codes, and numbers on very different scales. The team first cleans this data by removing broken and repeated records, fixing odd values, and converting text-like entries—such as connection state or service type—into numeric form. They then normalize numerical values so that features like packet counts and durations fall into a common range, making them easier for a learning algorithm to compare.
Adding meaning with feature engineering
A key novelty of this work is its rich “feature engineering” pipeline applied to structured network traffic. Instead of feeding raw fields directly to a neural network, the authors reshape them using several complementary techniques borrowed from text analysis. Bag of Words and TF-IDF convert categorical fields into counts and importance-weighted scores, helping highlight rare but telling patterns. Word2Vec maps similar values to nearby points in a numeric space, capturing relationships that simple counts miss. Principal Component Analysis (PCA) then compresses these high-dimensional representations into a smaller set of informative directions, while recursive feature elimination and correlation analysis remove redundant or unhelpful inputs. The result is a compact, information-rich view of each connection that is well suited to deep learning.
Deep networks that watch traffic flows
On top of this engineered data, the researchers design and compare five one-dimensional convolutional neural network (CNN) models. CNNs are commonly known for image recognition, but here they slide small filters over sequences of traffic features to detect recurring patterns linked to attacks. The study explores multiple architectural variants, called M-blocks, that differ in depth, the number of filters, the use of batch normalization and dropout (which help stabilize training and prevent overfitting), and how the input is reshaped. The models are trained with standard optimization techniques, evaluated through careful cross-validation, and tested on an independent portion of the dataset that remains unseen during training.

What the results tell us
The progression of models shows how smarter preprocessing and architecture design steadily improve performance. Early CNN versions already detect most attacks but mistakenly flag many safe connections. As the authors add stronger feature engineering and refine the CNN structure, error rates drop sharply. The two most advanced models, which combine multiple text-like encodings (Bag of Words, TF-IDF, Word2Vec), dimensionality reduction (PCA), and a tuned CNN, reach perfect scores on the test data: 100% accuracy and a flawless ability to separate malicious from benign traffic. Despite this, the final model remains compact and fast, requiring only a fraction of a megabyte of memory and processing thousands of connections per second on a standard CPU—important for gateways and edge devices with limited resources.
What this means for everyday security
In simple terms, the study shows that teaching a deep learning system to "read" network traffic using rich, carefully prepared features can dramatically improve the detection of hidden attacks in IoT networks. By transforming raw data into meaningful patterns and letting CNNs learn the difference between normal and harmful behavior, the authors build detectors that are both accurate and efficient. While real-world conditions will always be more varied than any single dataset, this work points toward practical, adaptive defenses that can help keep our connected homes, businesses, and cities safer from evolving cyber threats.
Citation: Abd-Ellah, M.K., Alsayed, N.A., Elkomy, O.M. et al. Malware detection in IoT networks with CNNs and integrated feature engineering. Sci Rep 16, 12886 (2026). https://doi.org/10.1038/s41598-026-47389-7
Keywords: IoT malware detection, network traffic analysis, deep learning security, convolutional neural networks, intrusion detection