Clear Sky Science · en
Enhancement of cryptography algorithms for security of cloud-based IoT with machine learning models
Why protecting smart gadgets matters
Homes, hospitals, factories, and even cities are filling up with tiny internet-connected gadgets that constantly send data to distant cloud servers. That convenience comes with a serious risk: if attackers intercept or tamper with this data, they can invade privacy, disrupt services, or take control of devices. This paper explores how to keep those data streams both safe and efficient, even when the gadgets have very limited computing power, by combining clever data scrambling and machine learning–based attack detection in a single, end‑to‑end security design.

From simple sensors to distant clouds
In a typical Internet of Things (IoT) setup, small devices such as sensors or cameras send sensitive readings over the internet to cloud platforms for storage and analysis. Many of these devices are tiny computers with strict limits on memory, processing power, and energy. Traditional heavy-duty security methods, while strong, can overwhelm such constrained hardware. At the same time, the volume of traffic and variety of devices create many openings for cyberattacks such as denial‑of‑service floods, spoofing, and brute‑force break‑ins. The challenge is to shield this continuous flow of information without slowing it down or draining the devices.
Blending light and strong digital locks
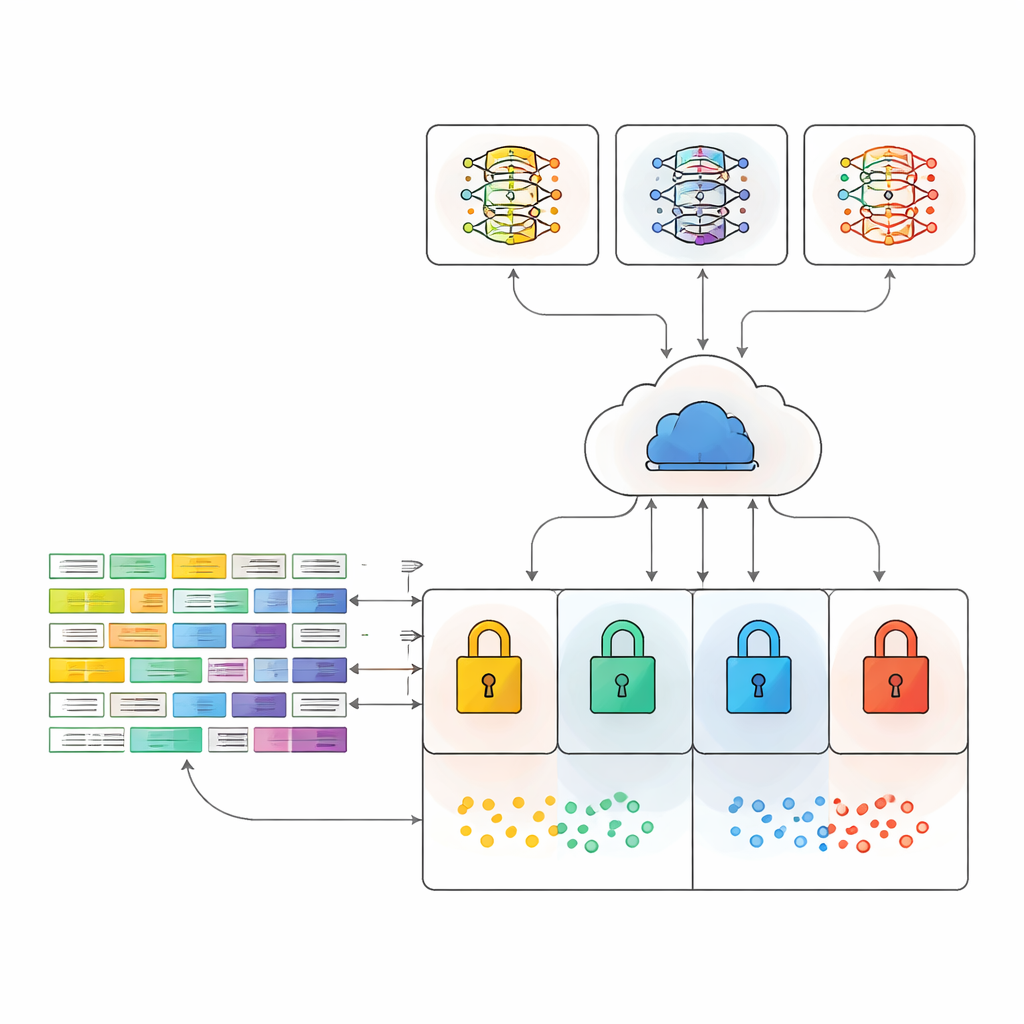
The authors propose a security framework that weaves together four types of data scrambling, or cryptography, with a realistic communication setup and modern machine learning tools. They test a very light method (XOR), a fast stream method (ChaCha20), the widely used Advanced Encryption Standard (AES), and a hybrid approach that combines AES with the RSA public‑key system. The hybrid method uses AES for quickly locking the data and RSA only to protect the secret key, aiming to get the best of both speed and strength. All data is then sent using MQTT, a popular lean messaging protocol for IoT, so the experiments mirror how real devices talk to cloud services.
Teaching machines to spot intruders
On the cloud side, the scrambled traffic is fed to several machine learning models trained to recognize suspicious patterns. The study uses well‑known ensemble methods, which rely on many decision trees or boosted trees working together to make a final judgment. These include Random Forest, XGBoost, CatBoost, and two combined models that vote on the outcome. Crucially, the models do not see the original clear‑text network data but instead learn to work directly on encrypted traffic, reflecting how a real‑world system would need to operate without exposing sensitive information.
Testing on real network attacks
To see how the framework behaves under realistic pressure, the authors evaluate it on two large public datasets of IoT network traffic. One (MQTTEEB‑D) focuses on attacks targeting the MQTT protocol, including floods, malformed messages, and slow denial‑of‑service attempts. The other (CIC IoT 2023) covers 33 different types of attacks across more than three million records in the subset used. For each encryption method, they carefully measure memory use, processor load, and a combined score called the Overall Resource Consumption Score, which balances these two factors. In parallel, they measure how accurately each machine learning setup can distinguish normal traffic from many forms of attack when the data arrives already encrypted.
Finding the sweet spot between safety and strain
The results reveal a trade‑off landscape. The simplest method, XOR, uses the least memory and processing power but offers the weakest protection. AES is strong but much heavier, especially on large datasets. The hybrid AES–RSA approach, however, turns out to be a sweet spot: it keeps memory use per traffic record modest while adding the benefits of public‑key protection and forward secrecy, where fresh keys are generated for sessions so past messages remain safe even if a key is later exposed. On the threat‑detection side, the voting ensemble model consistently provides the best or near‑best attack recognition, reaching about 93% accuracy on the MQTT‑focused dataset and about 81% on the larger, more complex IoT dataset—even though the traffic is encrypted.
What this means for everyday connected devices
For a non‑specialist, the key message is that it is possible to lock down data from smart devices without overloading them or blinding the systems that watch for attacks. By combining a carefully chosen mix of cryptographic methods with machine learning, and by testing them under realistic cloud messaging conditions, the authors show that hybrid encryption can keep data well protected while still allowing automated guards to spot hostile behavior. This integrated approach offers a practical blueprint for making the growing world of cloud‑connected gadgets safer and more trustworthy.
Citation: Qasem, M.A., Motiram, B.M., Thorat, S. et al. Enhancement of cryptography algorithms for security of cloud-based IoT with machine learning models. Sci Rep 16, 10972 (2026). https://doi.org/10.1038/s41598-026-45938-8
Keywords: IoT security, cloud encryption, machine learning, intrusion detection, lightweight cryptography