Clear Sky Science · en
Adaptive feature selection with gradient-based relevance for intrusion detection systems
Why hidden attacks in power networks matter
Modern power grids and industrial energy systems now depend on constant streams of digital data to keep electricity flowing safely and efficiently. To protect sensitive information, almost all of this traffic is encrypted—locked in a kind of digital envelope. But the same encryption that protects ordinary customers can also hide the footsteps of hackers trying to inject false commands or steal data. This paper presents a new way to spot those hidden attacks in encrypted traffic quickly and accurately, without opening the envelopes or slowing the grid.

The challenge of seeing through digital locks
Traditional intrusion detection tools often look inside network packets, comparing their contents to known patterns of malicious behavior. Encryption makes that approach nearly impossible, since the content is scrambled and must remain private. At the same time, attackers have learned to tunnel their activities through encrypted channels, blending in with normal users. Existing work has tried to use artificial intelligence on encrypted traffic, but many methods need heavy computation, struggle in real time, or break down when the data is noisy or intentionally manipulated. This is particularly dangerous in energy systems such as smart grids and SCADA networks, where even small classification errors can cause power instability or incorrect control actions.
Choosing the right clues instead of all the data
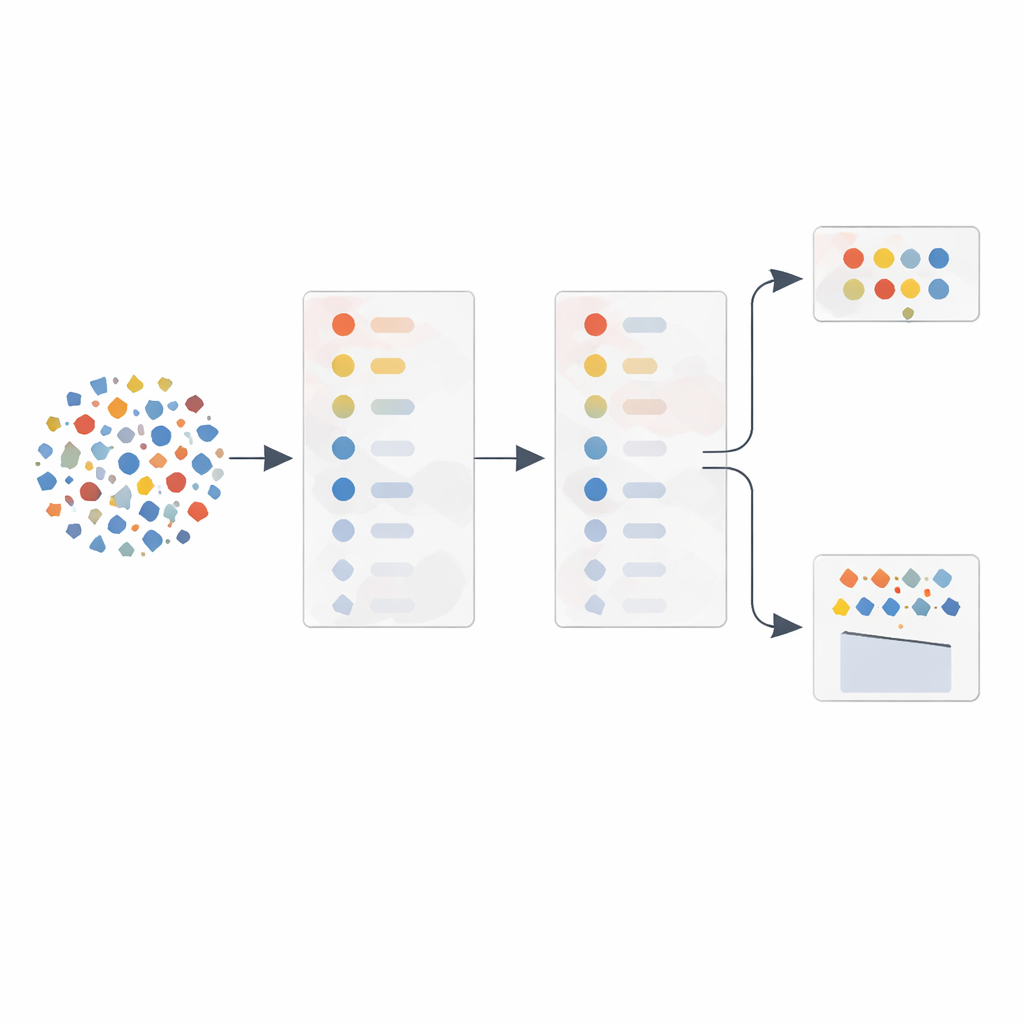
The authors focus on a key idea: not every measurable aspect of network traffic is equally useful for spotting attacks. Rather than feeding dozens of raw measurements into a learning algorithm, they propose an adaptive feature selection (AFS) method that automatically chooses the most informative clues. First, they use a standard statistical tool, principal component analysis (PCA), to rank traffic features—such as packet sizes, timing variations, and response delays—by how much they vary and how strongly they are related. Then, instead of trusting this ranking alone, they test features one by one in a classifier and track how much the detection quality improves each time a feature is added. This creates a performance curve that shows which features truly pull their weight.
Letting the data gradient guide the search
The heart of the method is what the authors call gradient-based relevance. As they gradually add features in PCA order, they measure how sharply the detection score jumps or flattens. Features that cause steep improvements on this curve are treated as especially valuable, even if their initial statistical importance looked modest. Features that add little or no benefit—often because they are redundant with earlier ones—are pushed aside. From this process they build two flexible feature sets: one with only the steep-jump features for lean operation, and another that supplements these with a few top-ranked features for extra robustness. A separate component monitors how noisy or tampered the training data appears, then automatically chooses between the smaller or larger set when classifying new traffic.
Proving the idea on real encrypted traffic
To test their approach, the researchers used a public dataset of encrypted DNS-over-HTTPS flows, which mixes normal browsing with malicious tunnels designed to smuggle data. They trained a logistic regression model—a relatively simple classifier—on traffic summarized by up to 27 different timing and size features. By applying their adaptive feature selection, they were able to reduce the number of active features to as few as four under high-noise conditions, or eleven under lower noise, while maintaining or improving accuracy. Across thousands of repeated trials, the adaptive method boosted the average detection rate by about a quarter compared with a standard PCA-only approach and by even more compared with using all features without selection. At the same time, it cut training time by roughly a third and sharply reduced memory use.
What this means for safer, smarter grids
In plain terms, the study shows that carefully picking which "clues" to feed an intrusion detector can make it both sharper and faster, even when working with encrypted traffic that must stay private. Instead of prying open packets, the system relies on how patterns of sizes and timings change when attacks are present, and it automatically adapts when the data becomes noisier or more heavily protected. For energy networks that must balance security, privacy, and real-time response, this kind of lightweight, adaptive filtering could become a key building block. While the results so far come from controlled experiments on one dataset, the authors argue that the same strategy can be plugged into existing monitoring tools and extended to other encrypted environments, helping critical infrastructure stay a step ahead of increasingly stealthy cyberattacks.
Citation: Lee, YR., Jeon, SE., Lee, SJ. et al. Adaptive feature selection with gradient-based relevance for intrusion detection systems. Sci Rep 16, 14308 (2026). https://doi.org/10.1038/s41598-026-42295-4
Keywords: encrypted traffic, intrusion detection, smart grid security, feature selection, cyberattack detection