Clear Sky Science · en
Epistemic uncertain computing for intrusion detection with explainability & multi-criteria optimization using AA-NLS and GRUSO-GRU
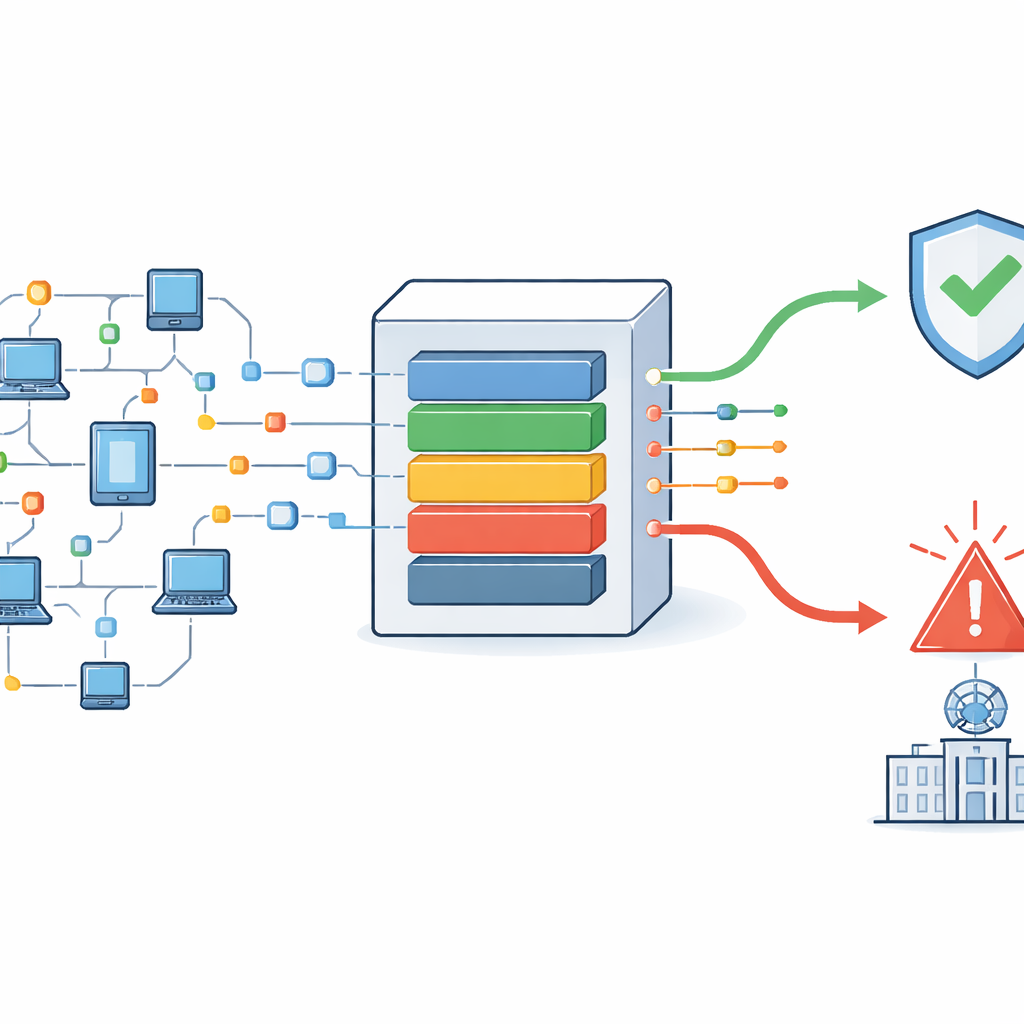
Why safer internet traffic matters
Every email you send, video call you make, or smart gadget you use depends on invisible streams of data rushing through networks. Hidden in that traffic are attempts by attackers to break in, steal information, or disrupt services. Modern defenses try to spot these intrusions automatically, but real-world network data is messy: packets arrive late, out of order, or with missing pieces. This study presents a new intrusion detection framework that not only copes with that uncertainty but also explains its decisions and prioritizes the most urgent alerts for security teams.
Messy traffic and hidden dangers
Traditional intrusion detection tools often assume that network data is clean and neatly ordered, or they focus mainly on known attack patterns. In practice, internet traffic is full of gaps, delays, and rearranged packets. These issues can cause dangerous confusion: an attack may look normal if its packets arrive late, or harmless activity might be flagged as hostile. The authors call this kind of “knowledge gap” epistemic uncertainty. They argue that many existing systems either ignore it or handle it only in limited ways, which leads to false alarms, missed threats, and overwhelming alert queues that slow down human response.
Building a smarter detection pipeline
The proposed system tackles the whole life cycle of network monitoring, from raw traffic to final alert. It begins by cleaning the data: duplicate records are removed and a tailored nearest-neighbor method fills in missing values without distorting local patterns. Next, a clustering step groups similar behaviors in the traffic so that unusual or rare activities stand out more clearly. From these groups, the system extracts key features, such as how often packets are exchanged, how long flows last, and how quickly data moves in each direction. These features provide a compact picture of how the network is behaving at any moment.
Understanding uncertainty and timing
A central innovation of the work is a dedicated module for judging the risk created by out-of-order packets. Using an extended logic framework, each packet is treated as having degrees of “attack evidence,” “normal evidence,” and “indeterminate evidence,” which are combined carefully so the total stays consistent and meaningful. In parallel, a temporal model learns how network states evolve over time, smoothing away impossible transitions and guarding against zero-probability blind spots. Together, these components capture both the uncertainty introduced by packet delays and the hidden rhythm of normal versus abnormal behavior in the network.
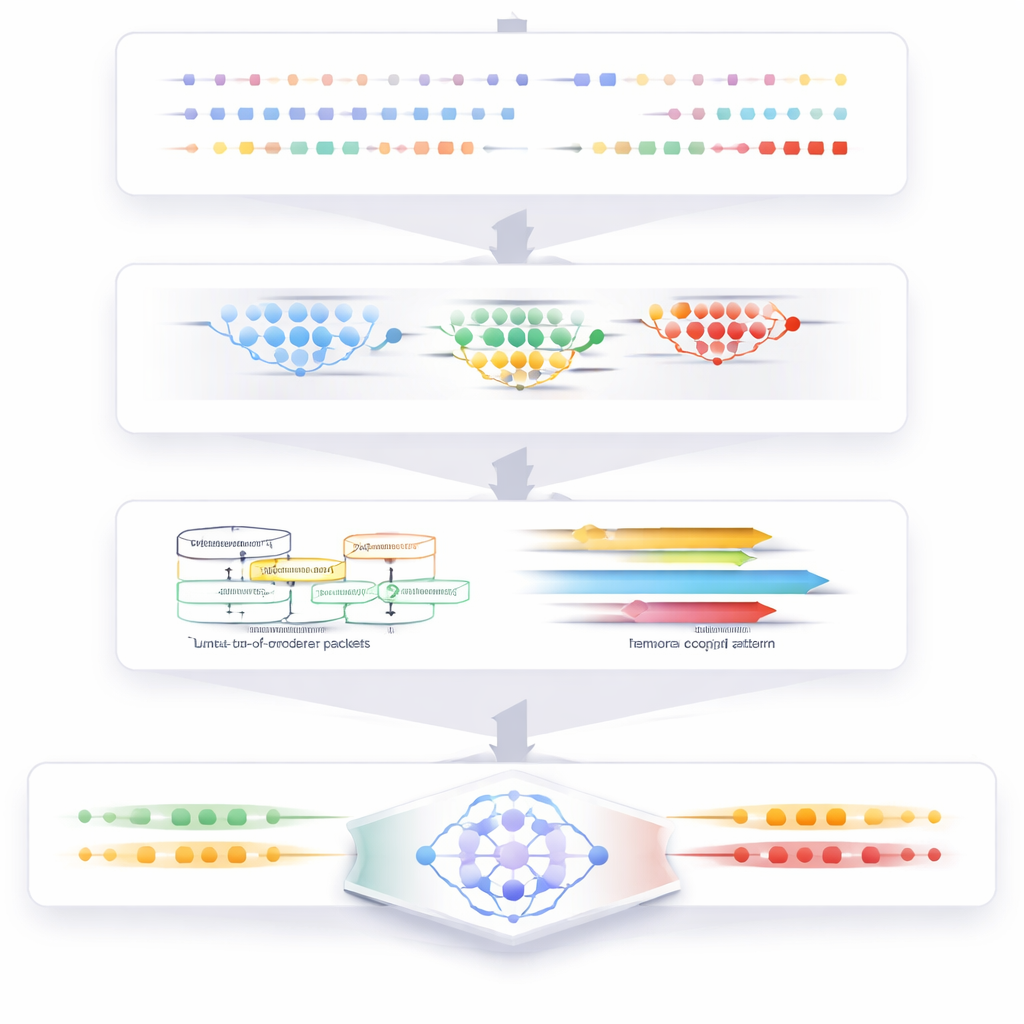
Learning to spot attacks and explain them
All of this processed information feeds into a customized deep learning classifier based on a gated recurrent unit. The authors redesign its internal wiring and activation functions so it learns faster, converges more reliably, and scales better than common recurrent models. The classifier labels traffic as benign or as one of several attack types, including denial-of-service, brute force, botnet, infiltration, and web attacks. To help analysts trust what the system reports, an explanation module then estimates how strongly each input feature contributed to a given decision, using an information-based weighting scheme that is more stable on skewed, real-world data.
Focusing attention on the most urgent threats
In busy networks, even a strong detector can flood operators with more alerts than they can handle in time. To address this, the framework adds an optimization layer inspired by the hunting behavior of desert foxes. This layer treats alerts as candidates to be ranked and searches for an ordering that maximizes detection quality while minimizing delay and resource use. A special mathematical function helps the search escape poor intermediate choices. Experiments on several public intrusion datasets show that this prioritization step increases throughput and cuts response times compared with other alert-handling strategies.
What the findings mean for everyday users
The authors report that their combined approach reaches over 99% accuracy in multi-class intrusion detection while also offering clearer explanations and faster, better-ordered alerts than competing methods. For a non-specialist, this means a more reliable digital “immune system” that is less likely to cry wolf and more likely to catch subtle attacks, even when data is incomplete or confusing. Although the method does not itself encrypt or protect the contents of user data, it significantly strengthens a key defensive layer in modern networks. With further work on end-to-end protection, approaches like this could help keep online services smoother, safer, and more trustworthy for everyone.
Citation: Kiruthika, K., Karpagam, M., Sardar, T.H. et al. Epistemic uncertain computing for intrusion detection with explainability & multi-criteria optimization using AA-NLS and GRUSO-GRU. Sci Rep 16, 14050 (2026). https://doi.org/10.1038/s41598-026-44214-z
Keywords: intrusion detection, network security, uncertainty, explainable AI, cyberattack alerts