Clear Sky Science · en
A user centric group authentication scheme for secure communication
Why many devices must prove they belong
As homes, cars, factories, and even satellites fill up with connected gadgets, those devices constantly need to prove they are legitimate before they can talk to each other. Doing this one by one quickly becomes too slow and wasteful when thousands of sensors or vehicles come online at once. This paper introduces a new way for large groups of devices to prove, in a single shot, that they all belong to the same trusted community—and to do so in a way that is fast, hard to cheat, and still lets the system pinpoint misbehaving members.

What group checks are and why old methods fall short
Instead of checking each device individually, group authentication schemes allow many devices to be verified together as members of one group, while at the same time setting up a shared secret key so they can encrypt their traffic. Earlier generations of these schemes relied on heavy mathematical machinery similar to that used in traditional internet security, or on clever hardware tricks. They often worked well for small, static groups, but they struggled when a single bad participant could disrupt the entire process, or when anonymity hid which exact devices were involved. In emerging Internet of Things networks, where countless simple devices share crowded wireless channels, these weaknesses can lead to denial-of-service attacks, wasted energy, and difficulty tracing which node went rogue.
A new way to share a secret without sharing secrets
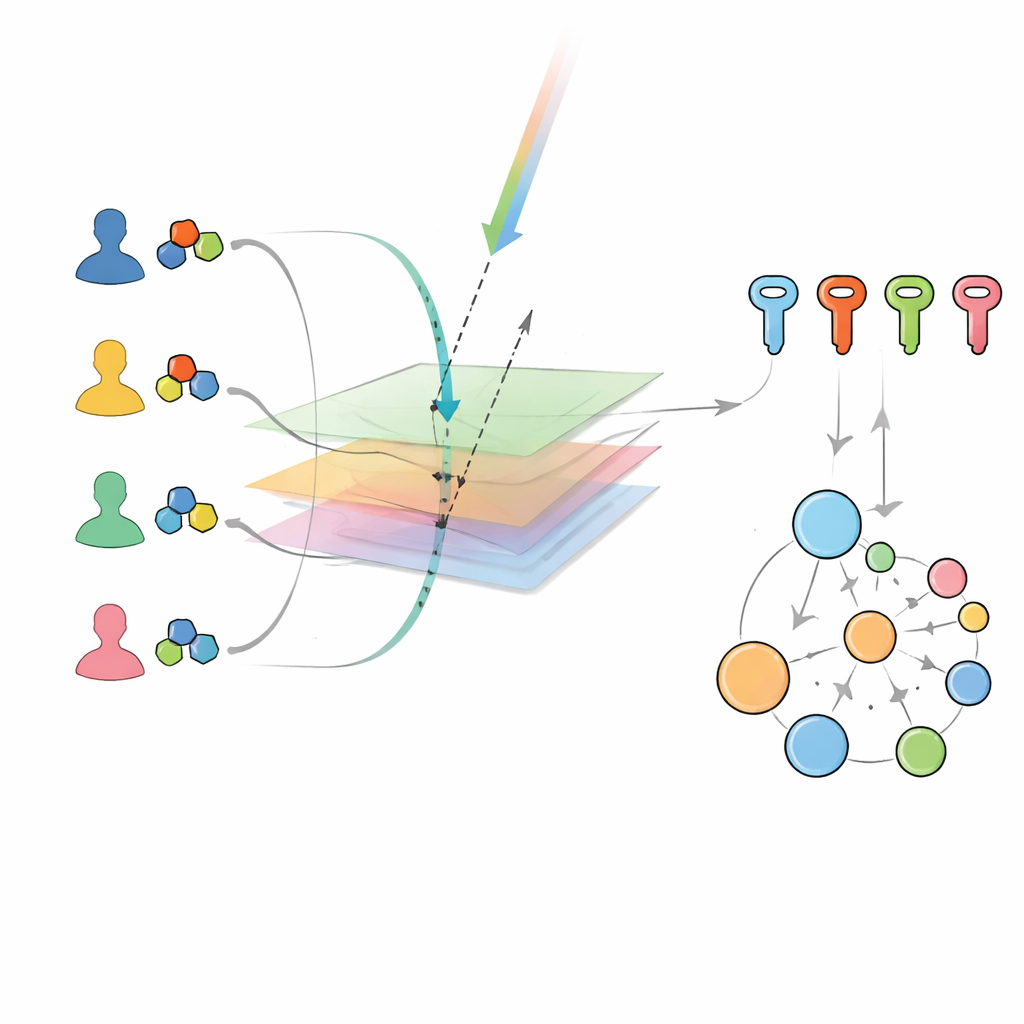
The authors build on a recent family of methods that treat secret data as geometric objects living in a shared space. A central group manager privately defines a hidden “subspace” in this space and gives each legitimate device its own personal set of building blocks, or basis, tied to that subspace. Public information is then broadcast to everyone, such as two random geometric vectors. Each device uses its private basis and the public data to perform a projection and an inner product—operations that can be computed very efficiently even on low-power hardware. Remarkably, every honest device arrives at exactly the same final value: a shared group key. They never reveal their private pieces, and they do not need to talk to one another directly; only public broadcasts and local calculations are required.
How the system spots who is really talking
Earlier versions of this geometric approach could confirm that “someone from the right group” was present, but could not say which specific devices were participating. That limitation made it easier for a legitimate device to secretly lend its powers to an outsider. The new scheme fixes this by tying each device’s public identity to the way its private basis is constructed. During group authentication, each member computes a simple numerical factor from its public identity and uses it to transform part of its basis before sending an encrypted result to the manager. Because the manager alone knows the hidden function that links identities to private values, it can check whether each response is consistent with a genuine registered device. At the same time, the underlying geometry still ensures that only true members can help compute the correct shared key, shutting non-members out from the start.
Finding troublemakers without stopping the crowd
Beyond confirming who is allowed in, the scheme also helps locate misbehaving members. If the combined group test fails, the manager divides the participants into two subgroups and repeats the authentication, recursively splitting any failing subgroup until only a handful of devices remain to inspect. Because outsiders cannot even take part in the core calculation, any error must come from a registered device sending wrong data. This divide-and-test strategy lets the system isolate malicious insiders—those trying to disrupt communication or leak group credentials—without repeatedly shutting down the whole network. The protocol is also designed so that an existing legitimate member can safely add a newcomer to the group when the main manager is offline, while keeping that action traceable.
Fast, lightweight and ready for crowded networks
To see whether this design is practical, the authors compared its performance with several well-known group authentication methods. Because their scheme uses only simple multiplications, divisions, and inner products instead of expensive cryptographic operations, it runs much faster as the number of devices grows, and it remains efficient even when tested on modest hardware like a Raspberry Pi. The overall conclusion is that this user-centric group authentication method can cheaply confirm both “who you are” and “which group you belong to,” while resisting common attacks and scaling to thousands of devices. For everyday users, this means that future smart homes, connected cars, and industrial sensors could join and leave secure conversations quickly and safely, without overloading tiny devices or risking that a single bad actor silences the rest.
Citation: Gerenli, O., Karabulut-Kurt, G. & Ozdemir, E. A user centric group authentication scheme for secure communication. Sci Rep 16, 14400 (2026). https://doi.org/10.1038/s41598-026-41463-w
Keywords: group authentication, Internet of Things security, lightweight cryptography, secure communication, malicious device detection