Clear Sky Science · en
Harnessing multimodal deep representation with dimensionality reducing approach for enhanced intrusion detection system in internet of things networks
Why Smart Gadgets Need Better Protection
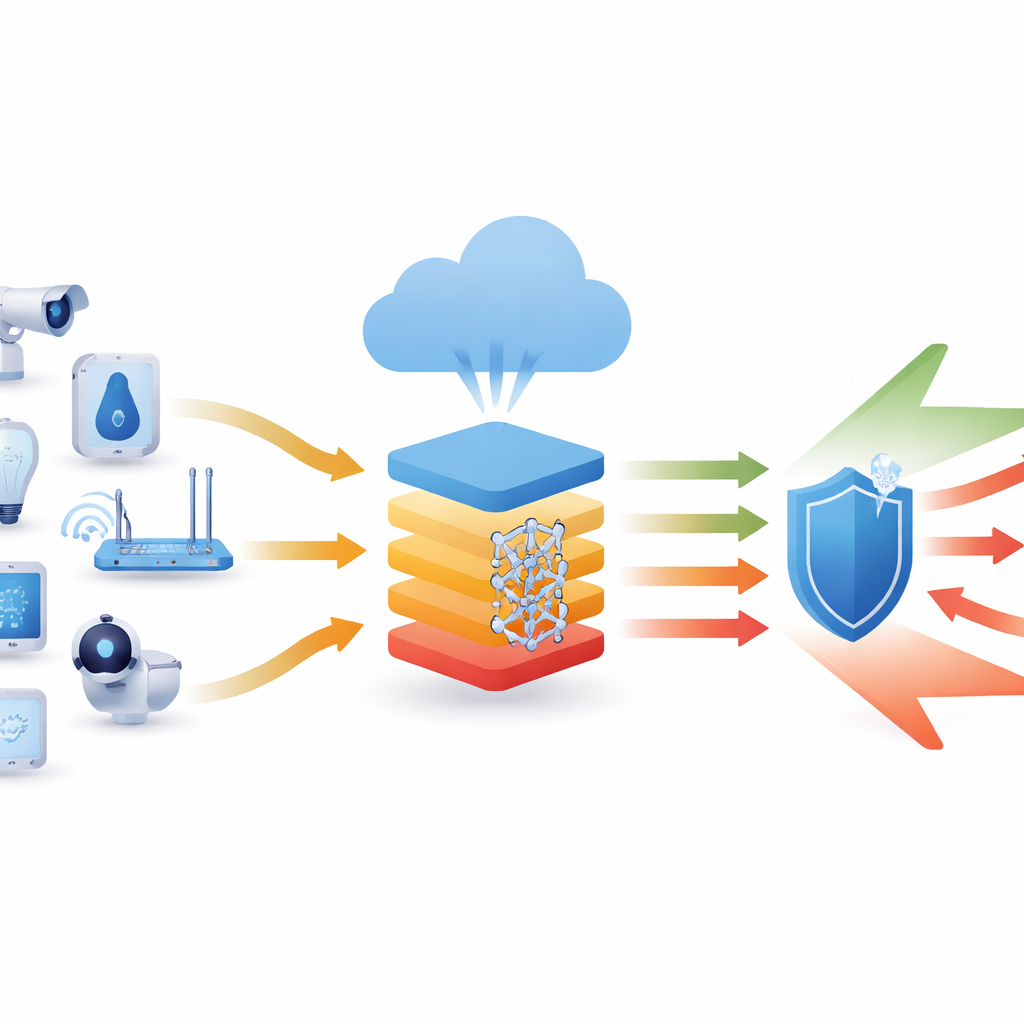
From smart doorbells to industrial sensors, billions of tiny internet-connected devices quietly monitor, measure, and control our world. Yet these gadgets are also new doors for cybercriminals, who can hijack them to steal data or launch large-scale attacks. This paper presents a new way to spot such intrusions early and accurately, using advanced pattern-finding tools from artificial intelligence tailored to the realities of Internet of Things (IoT) networks.
The Growing Shadow Over Connected Devices
Network attacks now cost the global economy billions of dollars, and IoT devices are an especially soft target. Many are inexpensive, widely deployed, and rarely updated, making them attractive stepping stones for attackers. Traditional intrusion detection systems watch network traffic for known signatures or simple statistical oddities, but modern attacks often hide within normal-looking data or exploit previously unseen weaknesses. In IoT environments, the challenge is even greater: data streams are huge, devices differ widely, and computing power at the edge is limited. The authors argue that effective protection must both recognize subtle patterns of misuse and run efficiently enough to be practical in such constrained settings.
A Smarter Watchdog for IoT Traffic
The study introduces an intelligent intrusion detection framework called OFSMDR-RIDS, designed specifically for IoT networks. Its goal is to distinguish routine device behavior from malicious activity with very high reliability. Instead of relying on hand-crafted rules, the system uses a deep learning model that learns directly from examples of normal and attack traffic. But rather than feeding raw, messy data into a large neural network, the method carefully prepares and trims the information first. This strategy both improves accuracy and keeps the system light enough to be used in real-world networks.
Cleaning and Distilling the Data
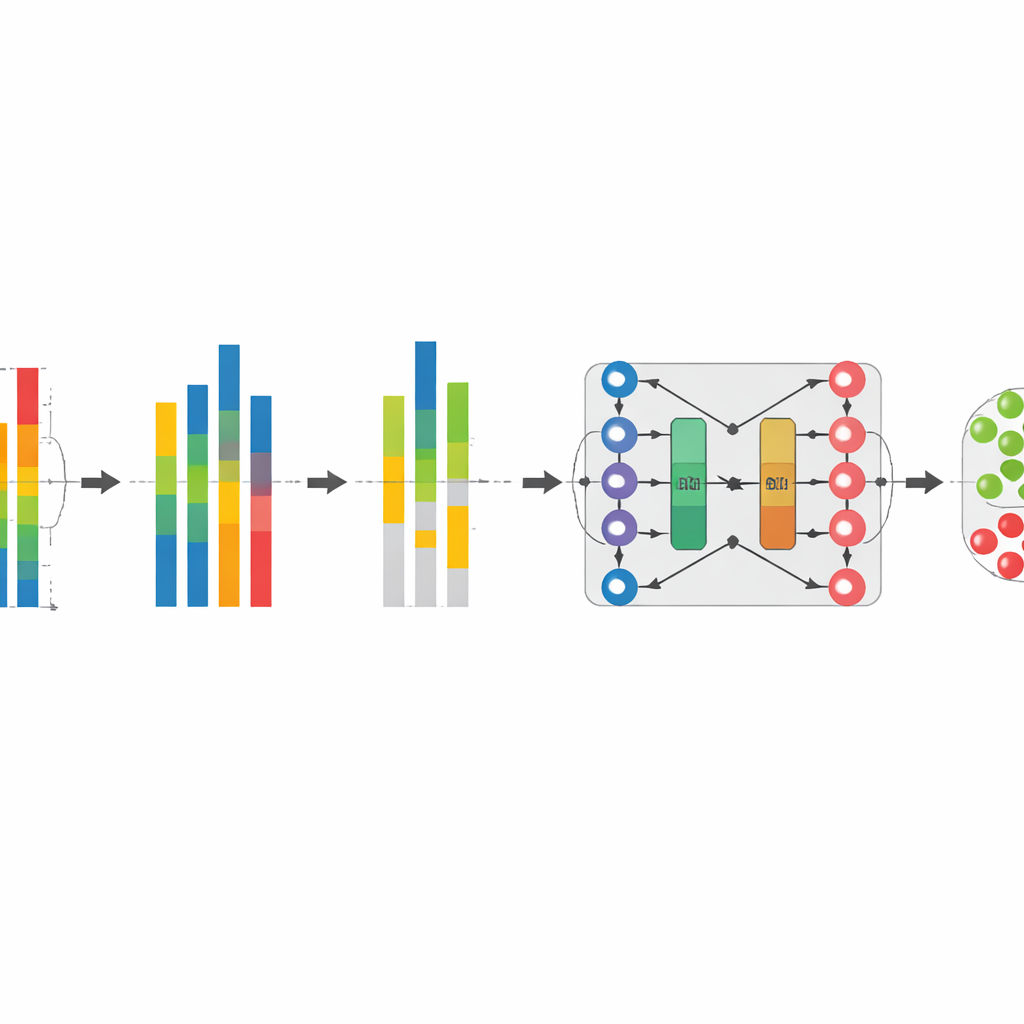
The first step in the pipeline is to standardize incoming network measurements using a process called quantile normalization. In everyday terms, this reshapes the data so that traffic from different devices and times follows a similar spread of values, while preserving the relative ranking of individual readings. That makes patterns easier to compare and reduces the effect of unusual spikes or mismatched scales. Next, the system performs feature selection with a method that seeks measurements that are strongly tied to whether traffic is normal or malicious, while avoiding redundant signals that say roughly the same thing. By keeping only the most informative pieces of each data record, the model becomes faster, less prone to overfitting, and easier to train on large IoT datasets.
Learning Patterns in Time
Once the data has been cleaned and distilled, it is passed to a hybrid deep learning model that combines two ideas: bidirectional long short-term memory (which excels at understanding sequences) and an autoencoder (which learns compact internal representations). Together, this BiL-AE structure learns how device traffic typically evolves over time and how to reconstruct it from a compressed form. Subtle deviations from learned patterns signal suspicious activity. By looking both forward and backward in each sequence, the model captures richer temporal context than conventional one-directional approaches, improving its ability to spot complex attacks that unfold over many steps while keeping false alarms low.
How Well the New Guard Dog Performs
The researchers tested their method using two widely used benchmark collections of IoT network traffic that include many types of attacks, such as denial-of-service floods, password guessing, and data injection. Across these challenging datasets, the proposed system consistently achieved accuracy near 99.5%, outperforming a range of recent intrusion detection methods based on other deep learning and optimization strategies. It also required fewer computing operations, less graphics-processor memory, and shorter processing times than several strong baselines, suggesting that it can be deployed even where resources are limited. Further experiments showed that each major component—normalization, feature selection, and the hybrid deep model—contributed to the final performance, with the full pipeline clearly superior to partial versions.
What This Means for Everyday Security
In plain terms, this work shows that by thoughtfully cleaning IoT network data, choosing the most telling signals, and then applying a time-aware deep learning model, it is possible to build a "smart alarm" that spots attacks with remarkable precision while staying efficient. Although the study still relies on pre-collected datasets and does not fully address encrypted traffic or brand-new attack types, it lays out a practical blueprint for next-generation intrusion detection in the rapidly expanding world of connected devices. As this approach is adapted and tested in live networks, it could help keep everything from home sensors to industrial control systems safer from unseen digital intruders.
Citation: Priyadharshini, K., Arulprakash, M., Jeya, R. et al. Harnessing multimodal deep representation with dimensionality reducing approach for enhanced intrusion detection system in internet of things networks. Sci Rep 16, 11442 (2026). https://doi.org/10.1038/s41598-026-36135-8
Keywords: IoT security, intrusion detection, deep learning, network attacks, cybersecurity