Clear Sky Science · en
A novel unified lightweight temporal-spatial transformer approach for intrusion detection in drone networks
Why safer drones matter
Drones are rapidly moving from hobby gadgets to everyday tools for delivery, farming, filming, and emergency response. But as more drones talk to each other and to ground stations over wireless links, they also open new doors for hackers. A successful attack could hijack a drone, disrupt a rescue mission, or expose sensitive video feeds. This paper introduces a new way to spot such attacks quickly and efficiently, using an artificial intelligence model designed to run on the limited hardware that drones actually carry.
The many ways to hack a drone
Modern drones rely on constant data exchange to navigate, coordinate, and send back information. Attackers can exploit this dependence in several ways: overwhelming the network so commands cannot get through, secretly inserting themselves between the drone and controller, replaying old messages to confuse guidance, or tampering with video and payload data. Existing defenses often assume powerful computers and generous energy budgets. That makes them hard to use on small flying machines, which must conserve battery power and react within fractions of a second. The authors argue that any realistic protection must be both highly accurate and extremely lightweight.
Why traditional defenses fall short
Earlier solutions borrowed tools from standard computer networks. Classical machine learning systems can detect some attacks but usually depend on hand-crafted features and offline tuning; they struggle when attackers change their tactics. More advanced deep learning models, such as recurrent neural networks and long short-term memory units, can see patterns that unfold over time, but they demand substantial memory and processing power. Recent transformer-based models, the same family of techniques behind many language tools, improve accuracy but often become even heavier. For fleets of drones that must make decisions on the fly, these approaches are either too slow, too power-hungry, or focused on narrow problems like only one attack type or only yes-or-no anomaly detection.
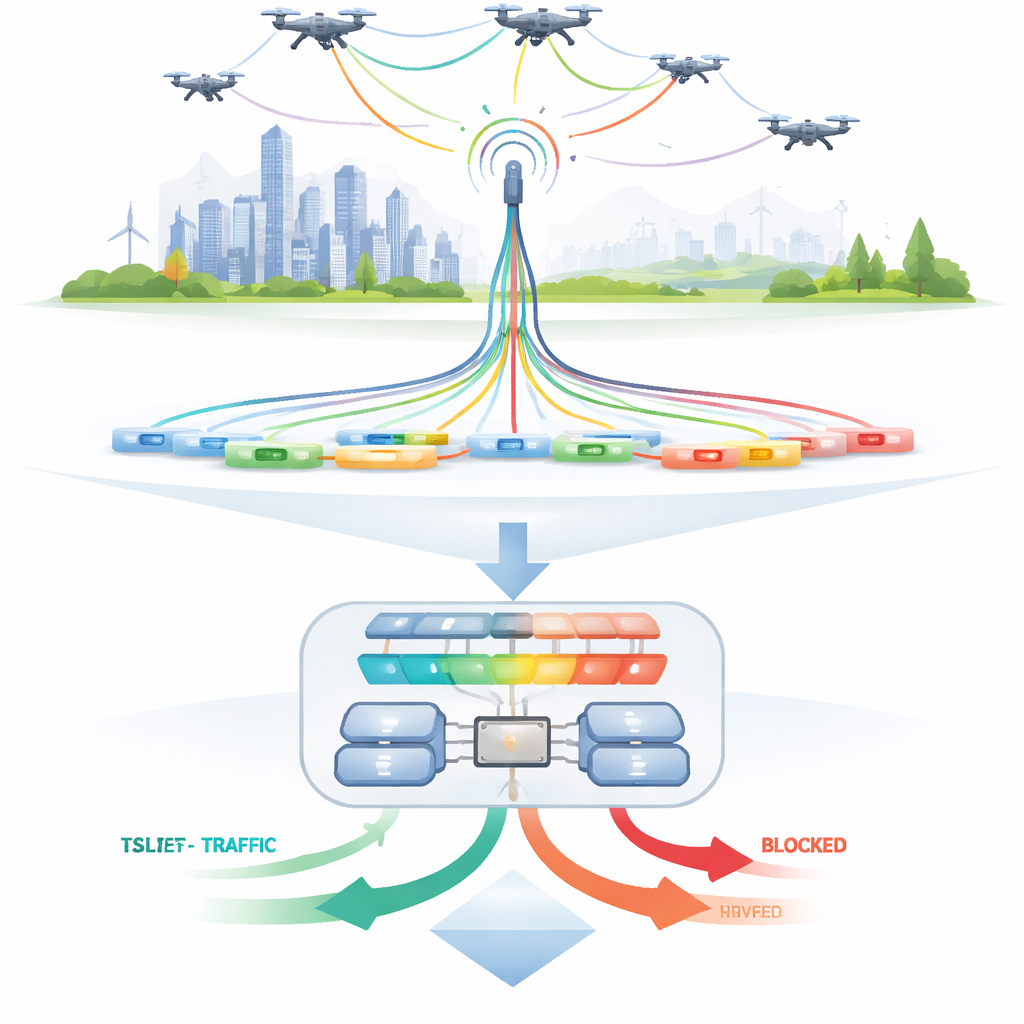
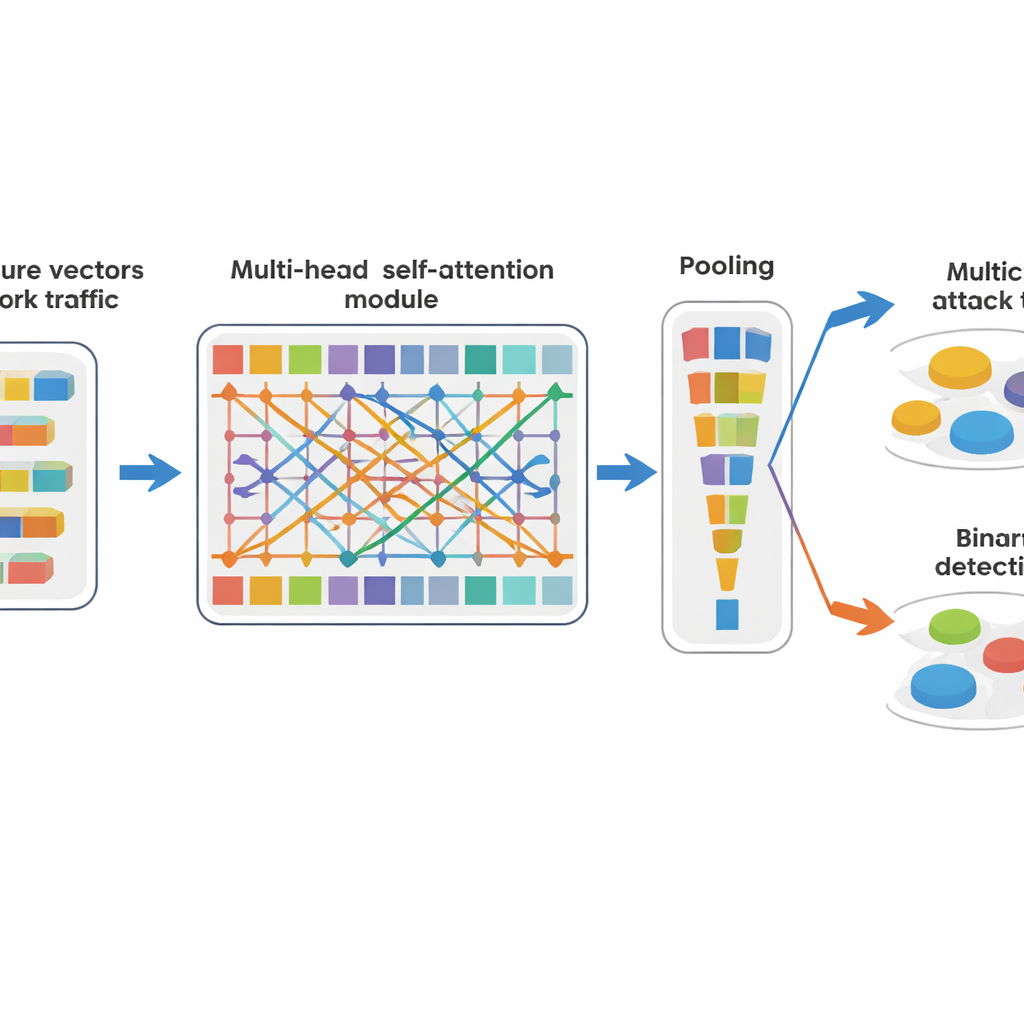
A compact "attention" engine for drone traffic
To tackle these constraints, the authors design TSLT-Net, a compact model that borrows the attention ideas of transformers but trims them down for drone needs. Instead of treating drone network data as long time series, the system reshapes each packet’s features into a small grid of tokens and lets the model learn which tokens should "pay attention" to which others. This lets it capture subtle relationships—such as unusual combinations of ports, payload size, and timing—without expensive loops over time. After this attention step, a simple averaging and a couple of small layers are enough to decide whether the traffic looks normal or suspicious. The same core engine feeds two outputs at once: one that flags traffic as safe or anomalous, and another that pinpoints the specific kind of attack.
Putting the model to the test
The team evaluates TSLT-Net on a large, realistically messy dataset of more than 2.3 million entries from real drone communication sessions. These records include many types of attacks—such as denial-of-service, password guessing, spoofing, replay, and video interception—alongside ordinary flight traffic. The authors take care to avoid overlap between training and testing sessions, so the model must cope with new days, different drones, and unseen variations in attack families. Despite these demanding conditions, TSLT-Net correctly identifies almost every instance: about 99.99 percent accuracy when distinguishing among multiple attack types and benign traffic, and effectively perfect performance when asked only to separate normal behavior from anything suspicious. It also maintains this accuracy across tests that hold out entire days, devices, or attack families.
Small model, big impact
Perhaps most striking is how little computing muscle TSLT-Net requires. It uses fewer than ten thousand trainable parameters, fits into roughly forty kilobytes of memory, and needs far fewer operations than common deep learning rivals. That makes it feasible to run directly on a drone’s modest onboard hardware or on nearby edge devices, while still reacting quickly enough for flight control loops. In practical terms, the model can watch network flows in real time, raise a flag when something looks wrong, and give the control software a chance to pause the mission, reroute communications, or isolate the affected drone. For non-specialists, the key idea is that this work shows it is possible to combine cutting-edge AI with strict limits on size and energy, paving the way for safer drone operations without bulky ground-based security systems.
Citation: Biswas, T.K., Zannat, A., Ishtiaq, W. et al. A novel unified lightweight temporal-spatial transformer approach for intrusion detection in drone networks. Sci Rep 16, 14473 (2026). https://doi.org/10.1038/s41598-026-45063-6
Keywords: drone cybersecurity, intrusion detection, transformer model, lightweight AI, unmanned aerial vehicles