Clear Sky Science · en
Intrusion detection with HACDT-Net and TRBM-Net using a hybrid deep learning framework with enhanced sampling techniques
Why smarter online guards matter
Every time you shop online, stream a movie, or connect a smart home gadget, your data travels through networks that are constantly probed by attackers. Most of these attacks are blocked, but a few slip through—especially rare or brand‑new ones that traditional defenses fail to recognize. This paper explores two advanced artificial‑intelligence “guards” designed to spot both common and uncommon intrusions in real time, even in the noisy, uneven traffic of today’s internet and Internet‑of‑Things (IoT) devices.
The challenge of hidden and rare attacks
Modern intrusion detection systems watch network traffic and try to decide whether each connection is harmless or hostile. Older methods rely on fixed signatures, like mugshots of known criminals, which means they struggle with new tricks and subtle attacks. Deep learning can instead learn patterns directly from data, but it faces two big hurdles. First, network logs are heavily unbalanced: there are millions of normal connections for every rare attack. A model trained on such data easily “learns” to declare everything safe, missing the very incidents we care about. Second, attacks reveal themselves in both the shape of a single packet and the way activity unfolds over time. Many models focus on either space (which fields in a packet are unusual) or time (how behavior changes), but not both together.
Cleaning and balancing the view of traffic
To build more trustworthy detectors, the authors first carefully clean two large, real‑world datasets: CICIDS2017, representing conventional networks, and NF‑BoT‑IoT‑v2, representing IoT environments. They remove duplicate and clearly corrupted entries, filter out extreme outliers that could mislead training, and normalize all numeric values so no single feature dominates. The most critical step tackles imbalance directly. The team uses sophisticated resampling strategies that create realistic synthetic examples of rare attacks while trimming noisy or redundant normal traffic. In effect, they “rebalance the courtroom” so that the learning algorithms see enough examples of each type of attack to recognize them reliably, without being overwhelmed by background traffic.
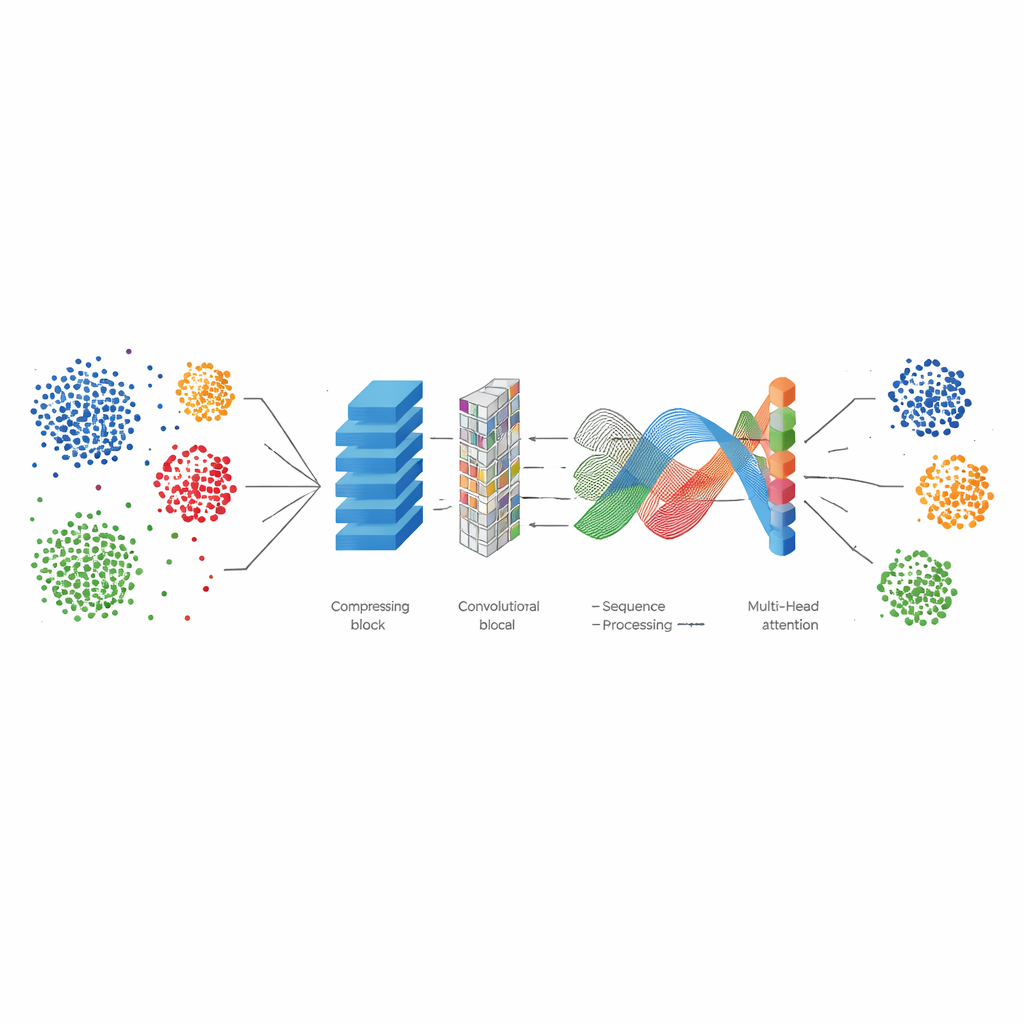
Two hybrid AI guards: one for patterns, one for sequences
The first model, HACTD‑Net, is built to excel at spotting complex patterns in what individual network flows look like. It starts with an autoencoder that compresses raw traffic into a cleaner, lower‑dimensional summary, stripping away redundancy. A convolutional network then scans these summaries for local patterns, a bit like detecting edges and shapes in an image. On top of this, a transformer module looks across all features at once, learning which combinations matter most for distinguishing attacks from normal use. Finally, a dense layer produces the decision. This model is paired with resampling methods called ADASYN‑SMOTE and Edited Nearest Neighbors, which boost rare attacks and delete confusing, mislabeled points.
A sequence‑savvy watchdog for evolving threats
The second model, TRBM‑Net, focuses on how events unfold over time—crucial for spotting botnets and slow attacks in IoT networks. It begins with temporal convolutional layers that efficiently scan sequences of packets, capturing long‑range trends without the heavy cost of classic recurrent networks. A ResNet block helps train deeper layers without “forgetting” important details, while a bidirectional GRU reads the sequence both forward and backward, capturing cause and effect in context. Multi‑head attention then highlights the most telling moments, such as spikes that hint at a denial‑of‑service attack. This model uses a different resampling mix—Borderline SMOTE combined with One‑Sided Selection—to focus new synthetic samples near decision boundaries and prune unhelpful normal traffic.
What the results mean for everyday security
Tested on millions of real network records, both models achieve strikingly high scores, with overall accuracies above 99 percent and strong performance even on rare and subtle attacks. HACTD‑Net shines at general accuracy, while TRBM‑Net slightly edges it out on catching hard‑to‑spot intrusions with fewer missed alarms, especially in IoT settings. For the average user, this means that future security tools based on such hybrid deep learning and smart data balancing can act like more vigilant, context‑aware guards. They are better at noticing the unusual footsteps in the hallway without constantly waking you up over harmless noise, moving us closer to reliable, real‑time protection for the growing web of connected devices.
Citation: Padma Priya, N., Mohanbabu, G. Intrusion detection with HACDT-Net and TRBM-Net using a hybrid deep learning framework with enhanced sampling techniques. Sci Rep 16, 11799 (2026). https://doi.org/10.1038/s41598-026-41422-5
Keywords: intrusion detection, deep learning, network security, imbalanced data, IoT attacks