Clear Sky Science · en
Deep learning-based HTTP TRACE flood detection in wireless sensor network using deep spectral multi-layer convolutional neural network
Why this matters for everyday connected devices
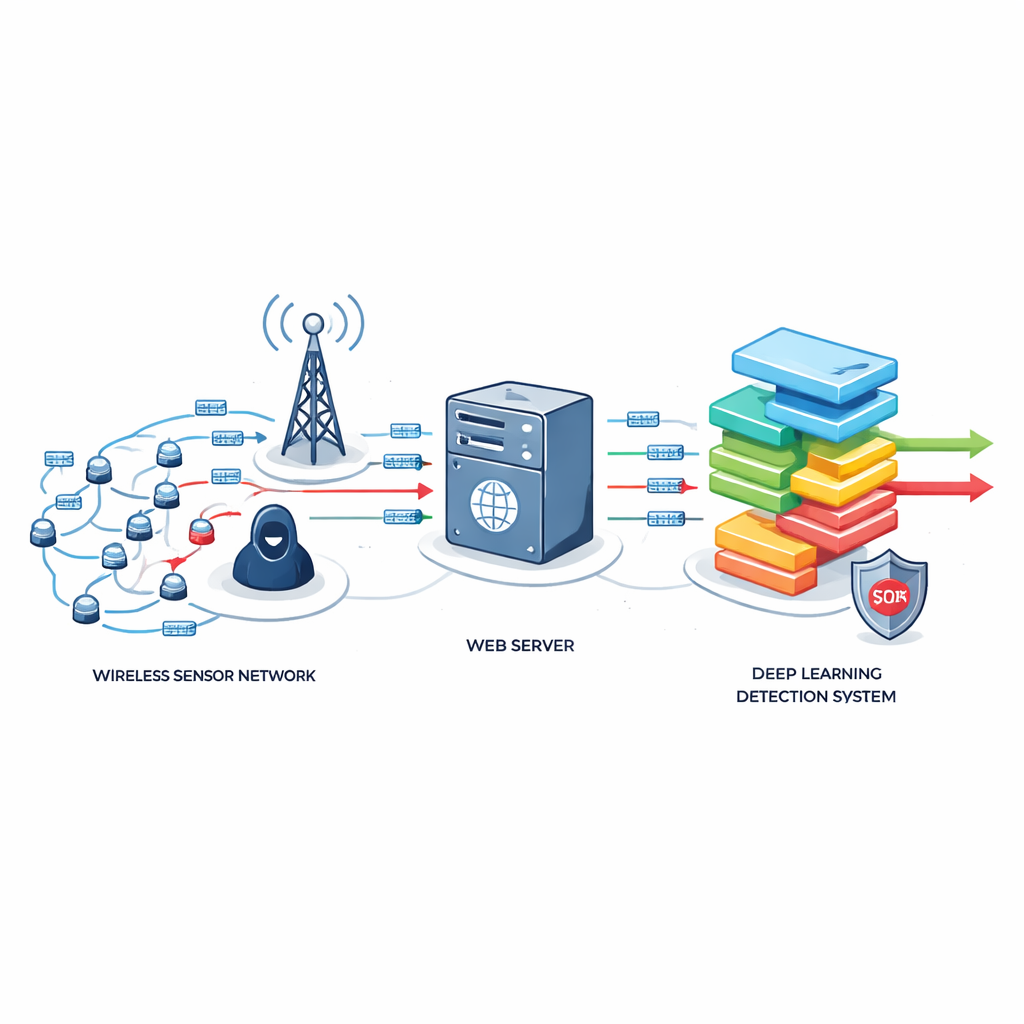
From smart streetlights to home security systems, more and more devices quietly talk to the internet through tiny wireless sensors. These wireless sensor networks make modern life smoother—but they also open new doors for hackers. This study explores a sneaky kind of web attack that can knock these small devices offline or steal data, and it introduces a new artificial-intelligence-based defense designed specifically for the tight limits of such low-power systems.
A quiet flood that looks like normal web traffic
The work focuses on Distributed Denial-of-Service (DDoS) attacks, in which an attacker overwhelms a target with internet requests until it can no longer respond to real users. A particularly slippery version uses ordinary web requests that look almost identical to what a regular browser would send. In this study, the spotlight is on the HTTP TRACE method—a rarely used web feature that simply echoes back what it receives. When abused at scale, repeated TRACE requests can both strain a tiny sensor network’s limited processor and memory and echo back sensitive information, such as session data, to an attacker.
Why small sensor networks are easy targets
Unlike big data centers, wireless sensor networks run on low-cost chips with modest processing power, little memory, and limited battery life. They often sit at the edge of the internet, gathering measurements like temperature, vibration, or traffic flow and relaying them through web servers. Because TRACE flood traffic closely mimics normal HTTP GET and POST activity, traditional defenses—which depend on clear spikes in traffic volume or heavy-duty analysis—either miss these attacks or consume too many resources. The authors show that many existing methods were built for powerful machines and do not account for how TRACE’s echo behavior and static URL patterns drain scarce energy and CPU cycles in these small networks.
A tailored deep-learning watchdog
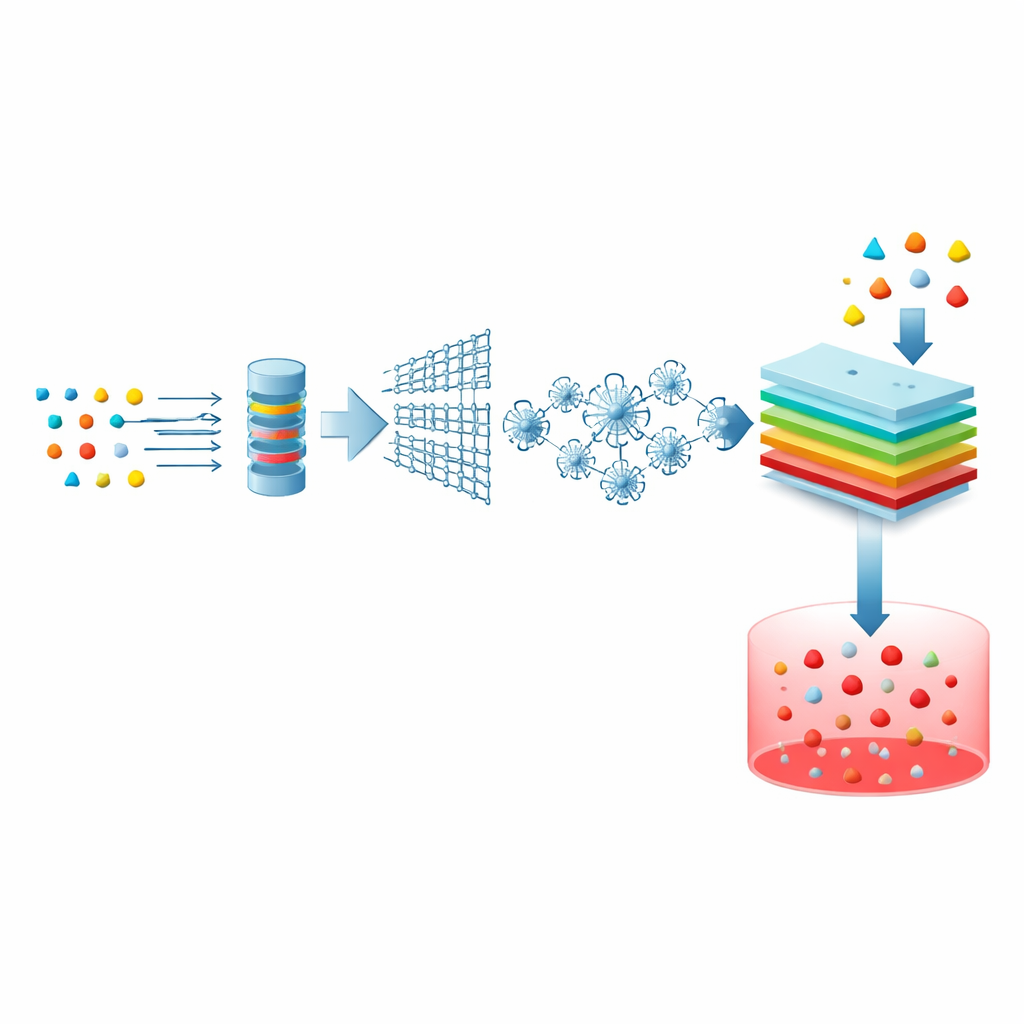
To address this gap, the researchers designed an Enhanced Deep Spectral Multi-Layer Convolutional Neural Network, or EDSMCNN, tuned for sensor networks. The approach starts by cleaning and simplifying real and simulated attack data, keeping only the most informative pieces of each web connection—for example, traffic rates, protocol information, and timing. A "lattice"-style service model evaluates how heavily each connection strains the system, while a spider-inspired optimization algorithm searches for the best combination of features, avoiding redundant or low-value signals. These compact, carefully chosen features are then fed into a deep learning model that uses layered filters to learn subtle traffic patterns associated with TRACE floods.
Putting the new guard to the test
The team evaluated EDSMCNN using a well-known DDoS dataset, supplemented or adjusted to represent TRACE-style behavior, and split it into training and test sets. They compared their method with several existing techniques, including software-defined networking defenses, epidemic-style traffic models, fuzzy logic, and k-nearest-neighbor classifiers. Across these tests, EDSMCNN consistently detected malicious TRACE-like activity with higher accuracy, sensitivity, and specificity. At the same time, it reduced false alarms, lowered CPU usage and memory demands, cut energy consumption, and shortened detection time—key advantages for battery-powered sensor nodes that must run unattended for long periods.
What this means for safer smart environments
In simple terms, the study shows that it is possible to build a smarter, lighter digital guard for tiny internet-connected devices. By teaching a tailored deep-learning model to recognize the subtle fingerprints of HTTP TRACE floods, the authors demonstrate a way to keep critical wireless sensor networks responsive and secure, even under attack. Their results suggest that future defenses for smart homes, cities, and industrial sites can be both precise and frugal with computing resources, and they point to expanding this approach to newer web protocols and evolving attack styles so that tomorrow’s sensors can continue to operate safely in an increasingly hostile online world.
Citation: Tamilselvi, S., Shieh, CS., Horng, MF. et al. Deep learning-based HTTP TRACE flood detection in wireless sensor network using deep spectral multi-layer convolutional neural network. Sci Rep 16, 12781 (2026). https://doi.org/10.1038/s41598-026-42474-3
Keywords: wireless sensor networks, DDoS attacks, HTTP TRACE flooding, deep learning security, intrusion detection