Clear Sky Science · en
Hybrid intelligence-powered secure clustering with trust-optimized routing for next-generation MANET communication
Keeping Wireless Connections Safe on the Move
From swarms of drones to cars that talk to each other on the highway, many future technologies will rely on devices that connect directly to one another without fixed phone masts or Wi‑Fi routers. These "mobile ad hoc networks" are flexible and quick to deploy but also fragile: devices move, batteries run down, and attackers can slip into the conversation. This paper introduces a new all‑in‑one system that uses several kinds of artificial intelligence to keep these roaming networks fast, efficient, and hard to hack.
Why Moving Networks Are Hard to Protect
In a mobile ad hoc network, every phone, sensor, or vehicle acts as both user and mini–router, passing messages along to others. Because there is no central control, the network must constantly rebuild itself as devices move or switch off. That makes it easy for messages to get lost, for batteries to drain quickly, and for malicious devices to pretend to be helpful while secretly dropping or tampering with data. Existing solutions usually fix only part of the problem—perhaps saving energy, or spotting a narrow set of attacks—but rarely manage energy, reliability, and security together in one coordinated design.
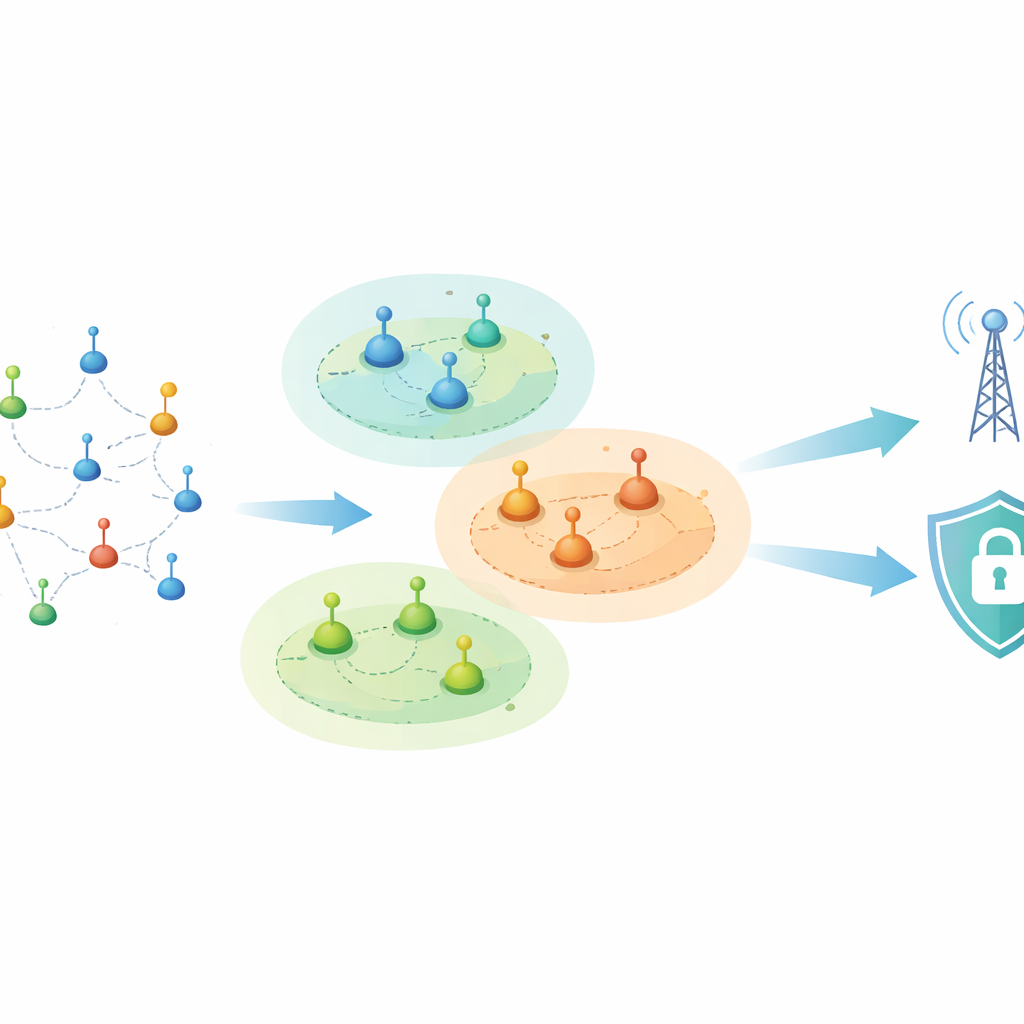
Turning Chaos into Stable Neighborhoods
To tackle this, the authors propose a framework called Hybrid Intelligence‑Powered Secure Clustering and Trust‑Optimized Routing (HISCTR). The first step is to bring order to the moving swarm by grouping nearby devices into local neighborhoods, or clusters. A method called Geographical Adaptive Fidelity Clustering shapes these clusters so that they are both physically close and have good radio links, and it changes them only when movement or misbehavior truly demands it. Within each cluster, a bio‑inspired search algorithm, modeled on a desert antelope, picks a main leader and a backup based on how much battery power a device has, how central it is, and how steadily it moves. This two‑leader structure keeps communication running smoothly even if the main leader fails.
Choosing Who to Trust on the Path
Once the network is clustered, HISCTR focuses on how messages travel from one cluster to another. Instead of assuming every device is honest, the system constantly scores each node’s behavior along several simple dimensions: does it reliably forward packets, does its behavior stay steady, and does it use energy sensibly? A fuzzy‑logic module blends these imperfect observations into a trust value that changes gradually over time, so one brief glitch does not condemn a node, but repeated bad behavior does. Routes are then chosen only among sufficiently trusted devices. A second optimization stage, inspired by quantum physics, searches for paths that balance low delay, high trust, and low energy cost, and can “jump” away from routes that look good at first but turn out to be poor choices.
Watching for Attacks from Two Angles
Trustful behavior alone is not enough when attackers invent new tricks. HISCTR therefore adds a dedicated intrusion detection engine that uses modern deep‑learning tools. One branch, built from transformer layers, examines how traffic patterns evolve over time, making it sensitive to slow‑burn or stealthy attacks. A second branch, made from convolutional neural networks, inspects local patterns in the data, catching sudden bursts or odd packet combinations. By combining these two views, the system can recognize a wide range of threats—from classic "blackhole" nodes that swallow traffic to harder‑to‑spot identity forgeries and zero‑day attacks—while still running fast enough for real‑time use.

Proving the Design at Large Scale
The researchers tested HISCTR in detailed computer simulations of large, busy networks with up to 1,200 nodes and many types of attacks mixed into normal traffic. Compared with several advanced competing methods, the new framework used noticeably less energy per node, kept data flowing at higher rates, and delivered a larger fraction of packets successfully, all while keeping delays and timing variations low. It also reduced errors in the transmitted bits and cut down on the “chatter” of control messages that usually clogs wireless channels. Most strikingly, its attack‑detection accuracy reached nearly 99 percent, and the simulated network stayed alive for thousands more communication rounds than with earlier schemes.
What This Means for Everyday Technology
In simple terms, this work shows that combining different kinds of intelligent decision‑making—clustering, trust scoring, route optimization, and deep‑learning security—into a single coordinated framework can make roaming wireless networks both sturdier and safer. For future applications like emergency response teams, connected cars, or large Internet‑of‑Things deployments in remote areas, such a system could mean longer battery life, more reliable messages, and stronger protection against cyberattacks, even when no traditional network infrastructure is available.
Citation: Anuprathibha, T., Maheswari, R., Suresh Babu, A. et al. Hybrid intelligence-powered secure clustering with trust-optimized routing for next-generation MANET communication. Sci Rep 16, 12988 (2026). https://doi.org/10.1038/s41598-026-41842-3
Keywords: mobile ad hoc networks, secure routing, trust-based networking, intrusion detection, energy-efficient wireless