Clear Sky Science · en
Spatial–temporal graph neural network with autoencoder pretraining for intrusion detection in healthcare IoT ecosystems
Why smarter security for hospital gadgets matters
Modern hospitals now rely on countless connected gadgets, from heart monitors to smart pumps, that quietly share data over the internet. These devices help doctors track patients in real time but also open new doors for cyber criminals. A successful break‑in could disrupt care or expose private health records. This study explores a new way to spot such intrusions early and accurately, even when the attacks are rare and hidden in a sea of normal activity. 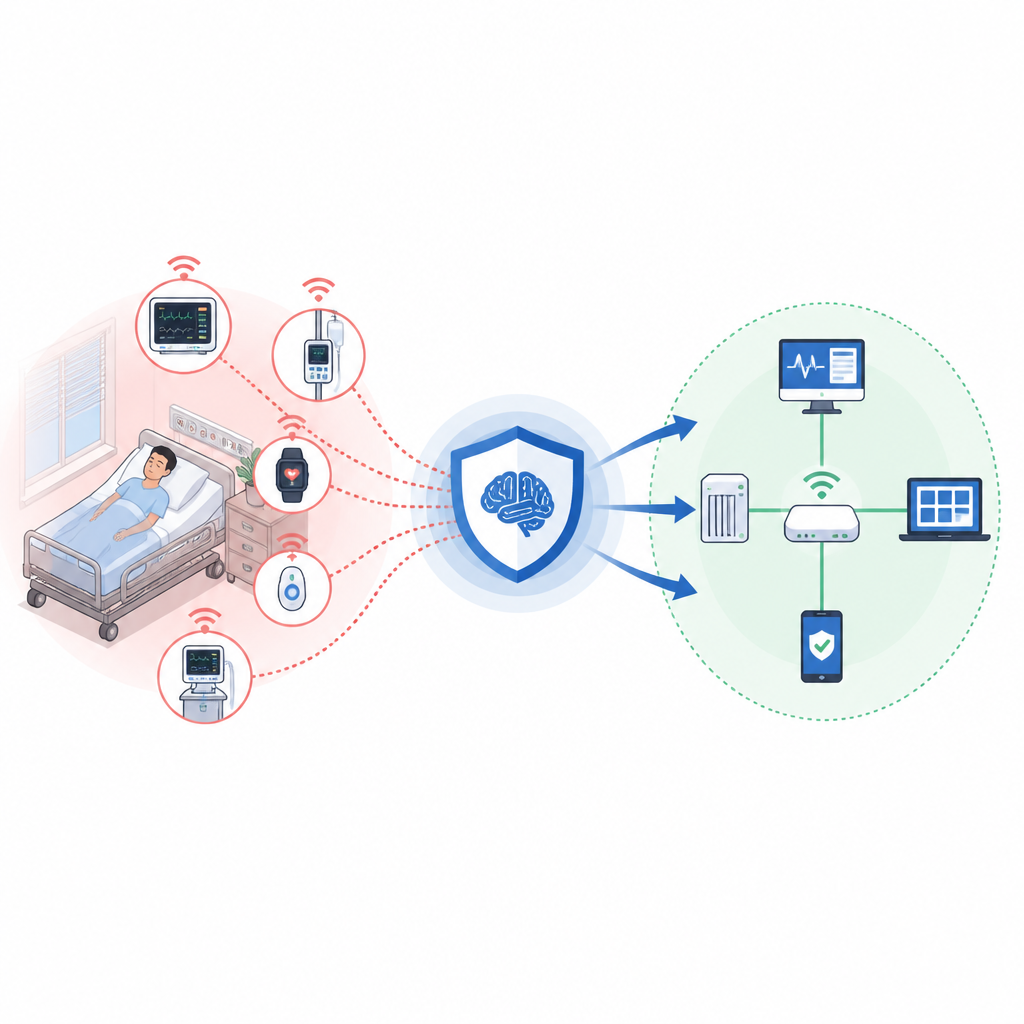
How hospital devices talk to each other
In a typical healthcare network, many different sensors and control units constantly send readings, alerts, and commands. Together they form a busy, ever‑changing web of digital traffic. Traditional security tools often look at each data packet in isolation or rely on fixed rules crafted by experts. That makes it hard to detect attacks that unfold slowly, hop between devices, or mimic normal patterns. The authors argue that a better approach must pay attention to how devices interact with one another and how those interactions change over time.
Turning a hospital network into a living map
The researchers model the hospital’s connected devices as a kind of living map, in which each device is a point and lines connect devices whose behavior closely moves together. Instead of needing a detailed wiring diagram of the hospital, they infer relationships from how sensors’ readings rise and fall in sync. For every short window of time, this produces a snapshot of the network’s structure. By feeding these snapshots into a special type of artificial intelligence that is designed to work with such maps, the system can learn what normal cooperation between devices looks like and what patterns suggest an attack.
Teaching the system with quiet practice
Real hospitals rarely have large, labeled collections of cyber attacks, because staging full‑scale breaches is unsafe and unethical. To work around this, the team first lets its model practice on mostly normal data without asking it to decide what is safe or unsafe. This warm‑up stage uses an autoencoder, a kind of neural network that learns to compress and then reconstruct the network’s behavior map. By learning to rebuild typical patterns, it develops a rich internal picture of normal device interactions. Later, this knowledge is reused when the system is trained to tell legitimate traffic from different kinds of intrusions. 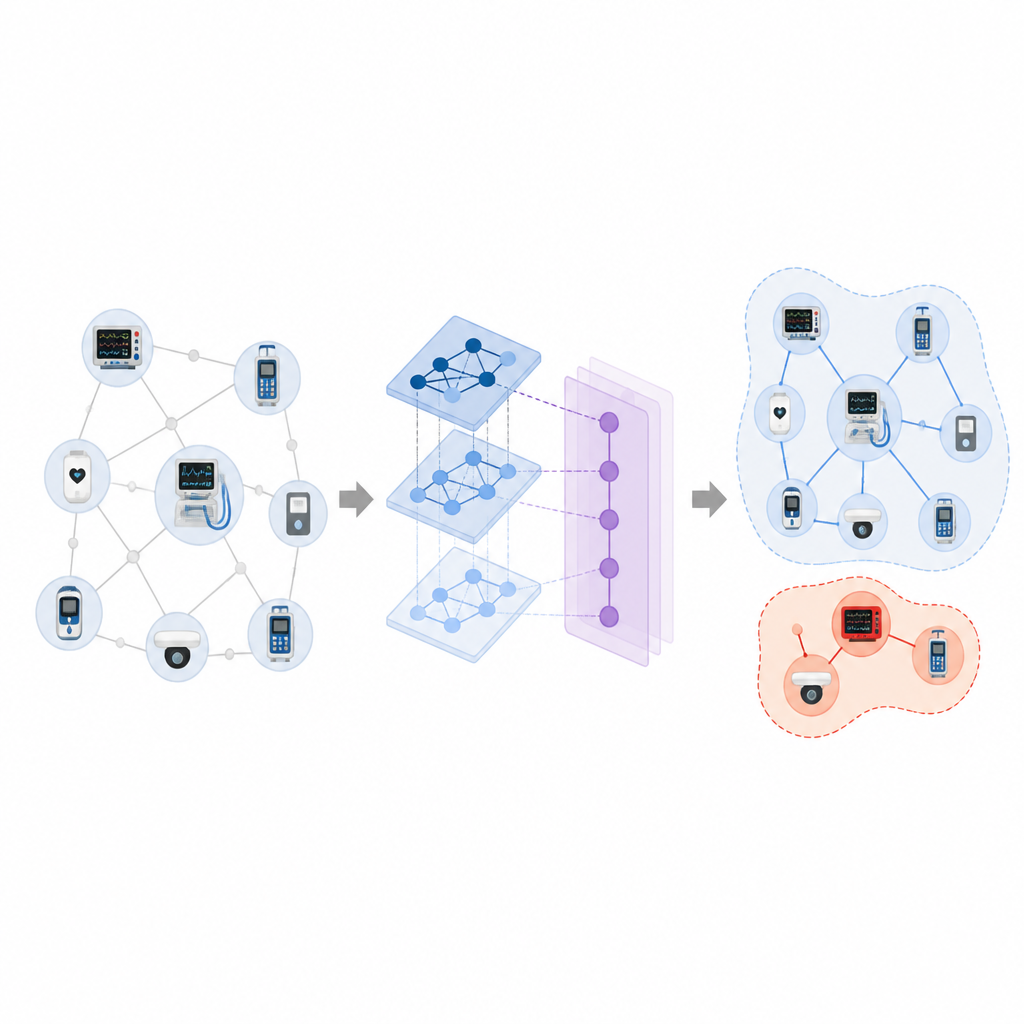
Following attacks across time
Once warmed up, the full system combines two kinds of learning. One part looks across the network map at a single moment, pooling information from neighboring devices to understand local structure. Another part tracks how these pooled signals evolve across a series of time windows, allowing it to recognize slow‑moving or staged attacks that unfold step by step. The final layer then decides whether each slice of activity is benign or belongs to one of several attack types, including those that are very rare but potentially severe.
How well the new approach performs
The authors test their method on a public dataset that simulates an intensive care unit with patient monitors and control devices, as well as on a broader collection of internet‑connected gadgets. Compared with classic machine‑learning tools and more recent deep‑learning and graph‑based models, their system reaches higher scores for accuracy and balance across all attack types. It proves especially strong at spotting rare intrusions that other systems tend to miss. When trained on the healthcare data and evaluated on the separate dataset, it maintains robust performance, suggesting it can handle shifts in device types and traffic patterns.
What this means for patients and hospitals
For non‑experts, the key outcome is that this study outlines a pathway to security tools that are more in tune with how real hospital networks behave. By learning the usual rhythms of many devices working together, and by practicing first on unlabeled data, the proposed system can better notice when something is off, even if it has seen only a few examples of a given attack. While the approach still needs to be made lighter and more transparent before it can run on small bedside devices, it offers a promising blueprint for keeping connected care both smart and safe.
Citation: Tanvir, M.I.M., Nadia, N.Y., Rabby, H.R. et al. Spatial–temporal graph neural network with autoencoder pretraining for intrusion detection in healthcare IoT ecosystems. Sci Rep 16, 15000 (2026). https://doi.org/10.1038/s41598-026-45041-y
Keywords: healthcare IoT, intrusion detection, graph neural network, cybersecurity, anomaly detection