Clear Sky Science · en
Artificial intelligence driven multi agent framework for adaptive cyber attack simulation and automated incident response in cyber range environments
Why smarter cyber drills matter
Every day, companies and governments rehearse for digital disasters using “cyber ranges” – safe, sandboxed networks where hackers and defenders can practice. But many of these training grounds still rely on scripted, predictable attack scenarios that look little like today’s stealthy, shape‑shifting threats. This paper introduces a new way to make those exercises far more realistic: using artificial‑intelligence “agents” that learn to hack and defend on their own, forcing human trainees and tools to contend with opponents that think and adapt.
From static scenarios to living war games
Traditional cyber ranges work a bit like a prewritten play: instructors choose an attack script, press start, and watch the action unfold. That’s useful for beginners, but it breaks down against modern adversaries who chain together many quiet steps, probe defenses, and change course when spotted. Studies cited in the article show that more than half of simulated attacks fail to include crucial tactics like moving from one compromised machine to another or hiding from monitoring tools. The result is training that looks neat on paper but underprepares analysts for the messy reality of the internet.
Teaching digital agents to attack and defend
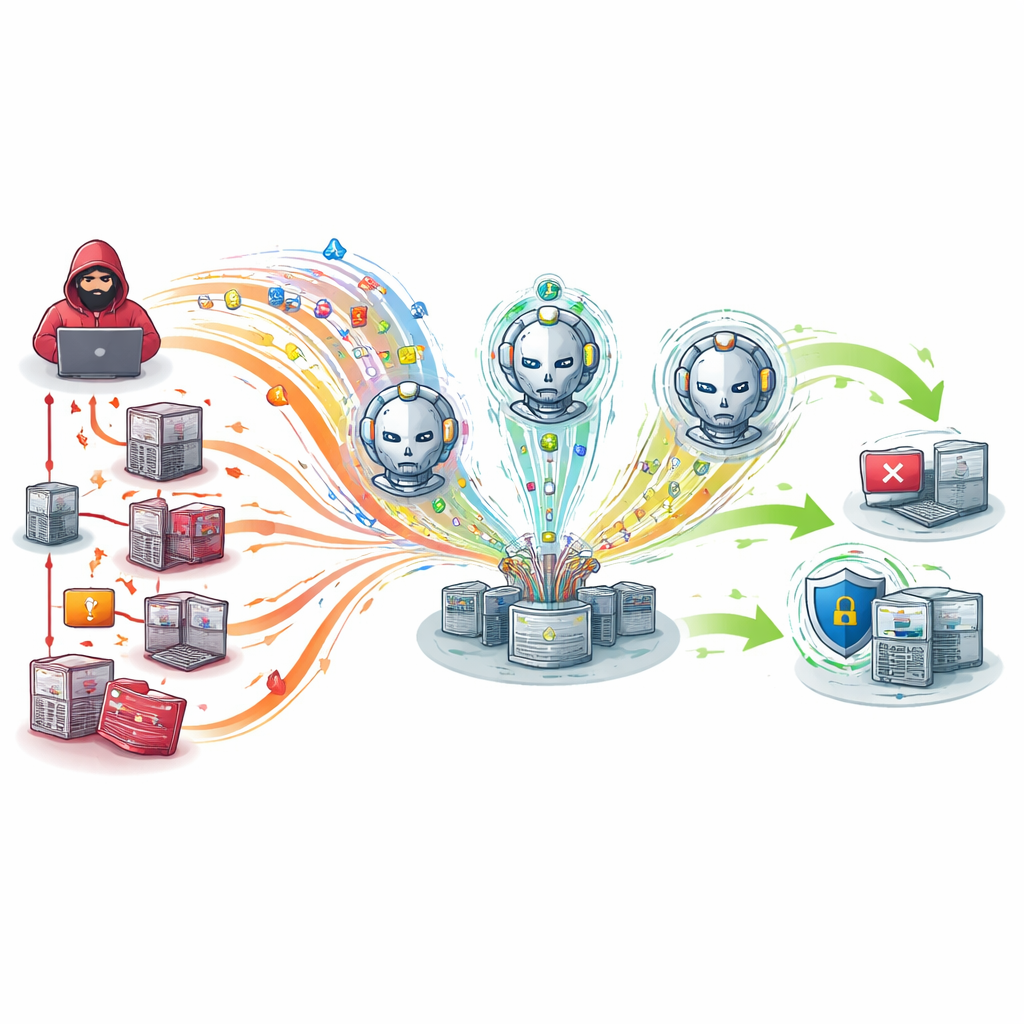
To close this gap, the authors build a multi‑agent system – a small society of software entities that act independently yet interact inside a shared virtual network. On one side are attacker agents that learn to plan and adjust their moves using reward‑and‑penalty feedback, much like a game‑playing AI learning to win. On the other side are defender agents that watch network traffic for unusual patterns and automatically choose how to respond, such as isolating a suspicious computer or blocking a risky connection. Both sets of agents are trained on large, real‑world collections of network activity so that their behavior reflects genuine malicious and normal use rather than toy examples.
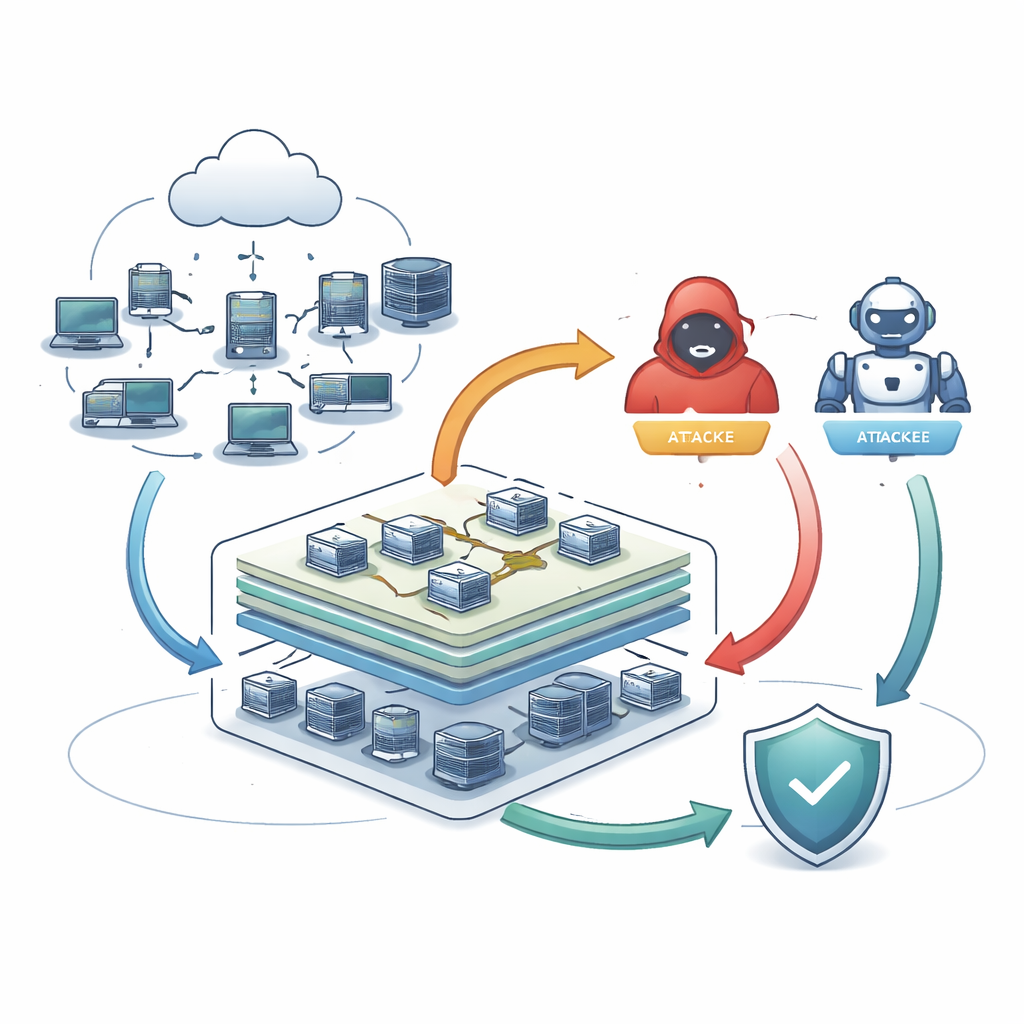
Building and wiring the testbed
The team integrates these agents into CyDER 2.0, a cloud‑based cyber range that can spin up different kinds of corporate‑style networks, from small setups with a few dozen machines to large environments with hundreds of hosts. Before training, they carefully clean and rebalance the underlying data so that rare attacks are not drowned out by everyday traffic. The attacker agent uses deep learning to explore multi‑step sequences such as scanning for weak machines, exploiting one, escalating privileges, and then spreading or stealing data, all while trying to stay unnoticed. Defender agents combine two complementary approaches: a traditional classifier tuned on labeled attacks, and an autoencoder that learns what “normal” looks like and flags deviations, including previously unseen tricks.
How the smart range performs in practice
The researchers pit their AI‑driven agents against two common alternatives: fixed scripts and a rule‑based multi‑agent setup whose behavior never truly changes. Across small, medium and large test networks, the learning agents detect attacks more accurately and with fewer misses. In the most demanding mixed‑attack scenario on the largest network, the new system maintains a strong balance of catching threats while avoiding false alarms, whereas static approaches degrade sharply. Just as important, its automated responses trigger several seconds faster than the baselines, a margin that can significantly limit damage in fast‑moving breaches. The attacker agents themselves grow more capable during training, stringing together longer, more intricate attack chains, while resource use for all agents stays within modest bounds.
What this means for real‑world readiness
Viewed from a layperson’s perspective, the study shows that cyber‑security drills can be upgraded from canned exercises into living war games where both sides think for themselves. By plugging learning attackers and defenders into realistic practice networks and feeding them genuine traffic records, the framework produces scenarios that look and feel much closer to actual incidents. In tests, this leads to sharper detection, faster reaction, and the ability to scale up to more complex environments without overwhelming the system. The authors argue that such intelligent ranges can better prepare security teams for future attacks and provide a foundation for more autonomous digital defenses, while future work will focus on slimming these powerful agents down so they can also operate on smaller, less powerful devices.
Citation: Agrawal, A., Nadeem, M., Al Nuaim, A. et al. Artificial intelligence driven multi agent framework for adaptive cyber attack simulation and automated incident response in cyber range environments. Sci Rep 16, 11673 (2026). https://doi.org/10.1038/s41598-026-45937-9
Keywords: cyber range, adaptive cyberattacks, multi-agent systems, AI-driven defense, incident response