Clear Sky Science · en
An intrusion detection model for electric vehicle supply equipment based on multi-task learning and probability transfer mechanism
Why Smarter Charging Matters
As electric cars spread through cities, the humble charging post becomes a quiet but critical link between millions of vehicles and the national power grid. If these chargers are hacked, the consequences go far beyond a single stalled car: attackers could drain wallets, steal private data or even destabilize parts of the grid. This paper presents a new way to spot such digital break-ins quickly and accurately, using a deep‑learning system that watches what is happening inside the charger itself rather than just the data flowing over the network.

Hidden Risks at the Plug
Electric vehicle supply equipment (EVSE) sits at the crossroads of cars, apps, payment systems and high‑voltage power lines. When a driver scans a code or opens an app to start charging, that request ultimately reaches the national grid through layers of communication and control. Past attacks overseas have shown that chargers can be hijacked to shut down stations, manipulate loads or tamper with billing. Traditional security tools focus on network traffic and often reduce events to a simple verdict: "malicious" or "benign." But in this setting, different kinds of attacks—such as cryptomining on the charger’s computer, denial‑of‑service floods, or backdoors—have very different consequences for safety and grid stability. Recognizing only that "something is wrong" is no longer enough.
Looking Inside the Charger
To move beyond this coarse view, the authors build an intrusion detector that watches host‑level behavior inside the EVSE controller. Instead of only logging who talks to whom over the network, the system monitors low‑level performance counters and operating‑system events: instructions executed, cache misses, memory allocations and device I/O. These signals, already available on typical embedded Linux hardware, capture how the charger’s brain is actually working. Benign charging sessions and different attack programs leave distinct "fingerprints" in this internal activity. The model first cleans and normalizes these measurements, separating features that are mostly zero from those that vary more richly, and then feeds them into a pair of neural networks that learn both complex patterns and how different features interact.
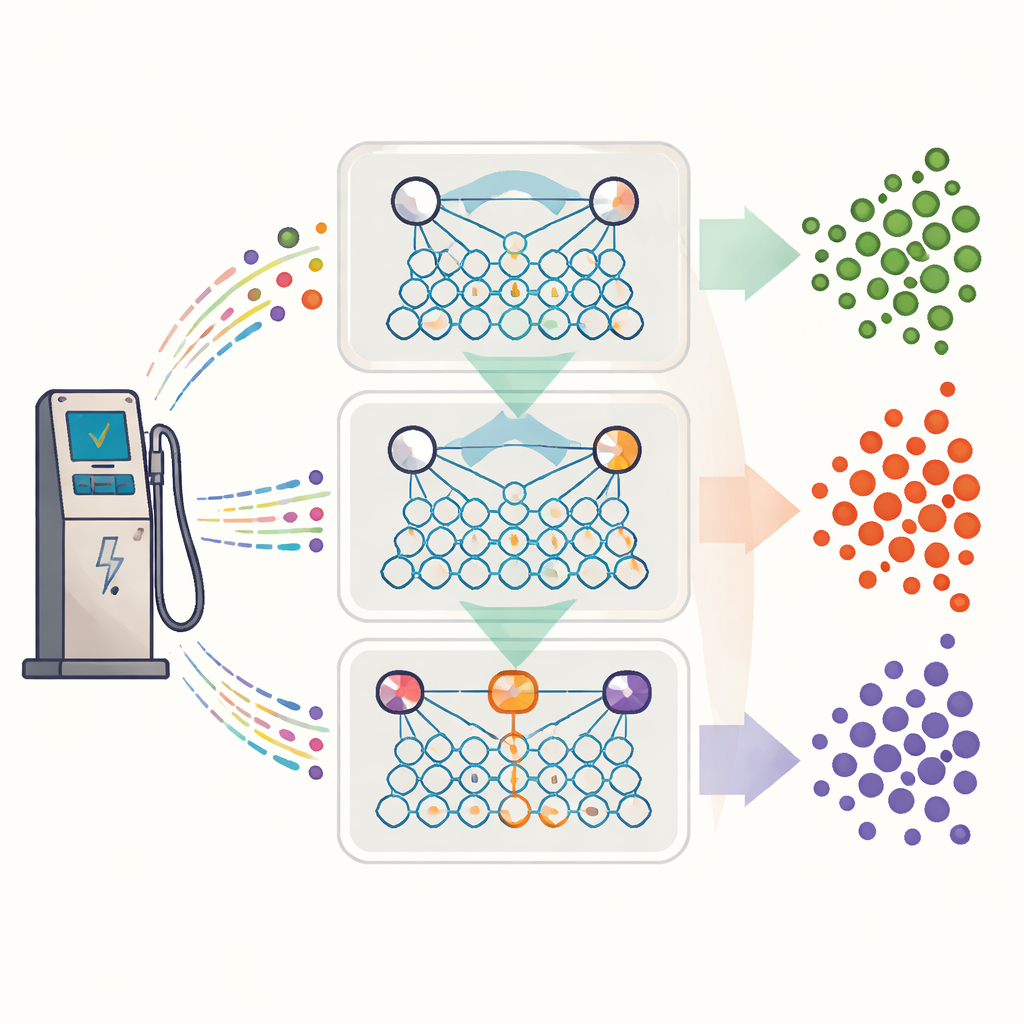
Many Questions, One Shared Brain
A key idea of the work is multi‑task learning: instead of training separate detectors for each security question, a single shared model answers three at once. The first task asks whether a sample is malicious or not. The second groups malicious behavior into broader families, such as denial‑of‑service or host attacks. The third drills down to specific attack types, like port scans or particular flooding strategies. All three tasks share a common internal representation of the charger’s behavior, so the model does not have to relearn basic patterns from scratch each time. This shared setup slashes training and prediction time, which is crucial if thousands of chargers must be protected in real time.
Passing Along Probabilities Instead of Mistakes
Multi‑task systems can suffer when one task misleads the others. To avoid this, the authors introduce a "probability transfer" mechanism. Rather than passing hard yes‑or‑no decisions from one task to the next, the model passes full probability distributions. The confidence score from the simple malicious‑versus‑benign task is mathematically transformed into a prior hint for the family‑level classifier, which in turn guides the fine‑grained classifier. This soft guidance encourages logical consistency—fine‑grained decisions are nudged to agree with higher‑level ones—while still allowing each task to correct upstream uncertainty based on its own evidence. In tests on a public EVSE dataset and two standard intrusion‑detection benchmarks, this strategy raised detection accuracy by up to roughly 27 percent and cut detection time by over 40 percent compared with strong existing methods.
What This Means for Everyday Drivers
For drivers and grid operators, the message is reassuring: it is possible to build security systems for charging stations that are both fast and subtle. By watching the internal behavior of chargers and using a shared, probability‑aware learning framework, the proposed EVSEMTLIDS model can distinguish normal activity from many different attack types with high reliability, while running efficiently enough for real‑world deployment. In practical terms, this means a better chance of catching dangerous or fraudulent behavior early—before it can damage equipment, threaten the grid, or put people at risk—without overwhelming operators with false alarms.
Citation: Yang, K., Cai, L. & Wu, J. An intrusion detection model for electric vehicle supply equipment based on multi-task learning and probability transfer mechanism. Sci Rep 16, 12983 (2026). https://doi.org/10.1038/s41598-026-42331-3
Keywords: electric vehicle charging security, intrusion detection, multi-task learning, cyber-physical systems, deep learning models