Clear Sky Science · en
Quantum transfer learning for cross-domain cybersecurity threat detection and categorization
Why smarter defenses matter
Every time you browse the web, send a message, or connect a smart device at home, your activity flows through networks that are constantly under attack. Criminals probe these systems looking for weak spots, often using tricks that change faster than traditional defenses can keep up. This paper explores a new way to spot those threats by combining two powerful ideas—machine learning and quantum computing—to build security tools that can adapt across many different kinds of networks.
Growing dangers in a connected world
The authors begin by describing how the explosion of internet-connected devices and online services has widened the doorway for attacks such as malware, data theft, and denial-of-service floods that can knock systems offline. Older defenses often depend on fixed rules or known attack patterns, which means they tend to miss brand‑new tricks and rare but dangerous threats. Modern artificial intelligence has improved detection by learning from data, but these models struggle when the data are huge, messy, and different from one network to another—exactly the situation in today’s mix of corporate servers, cloud platforms, and Internet of Things gadgets.
A new mix of classical and quantum tools
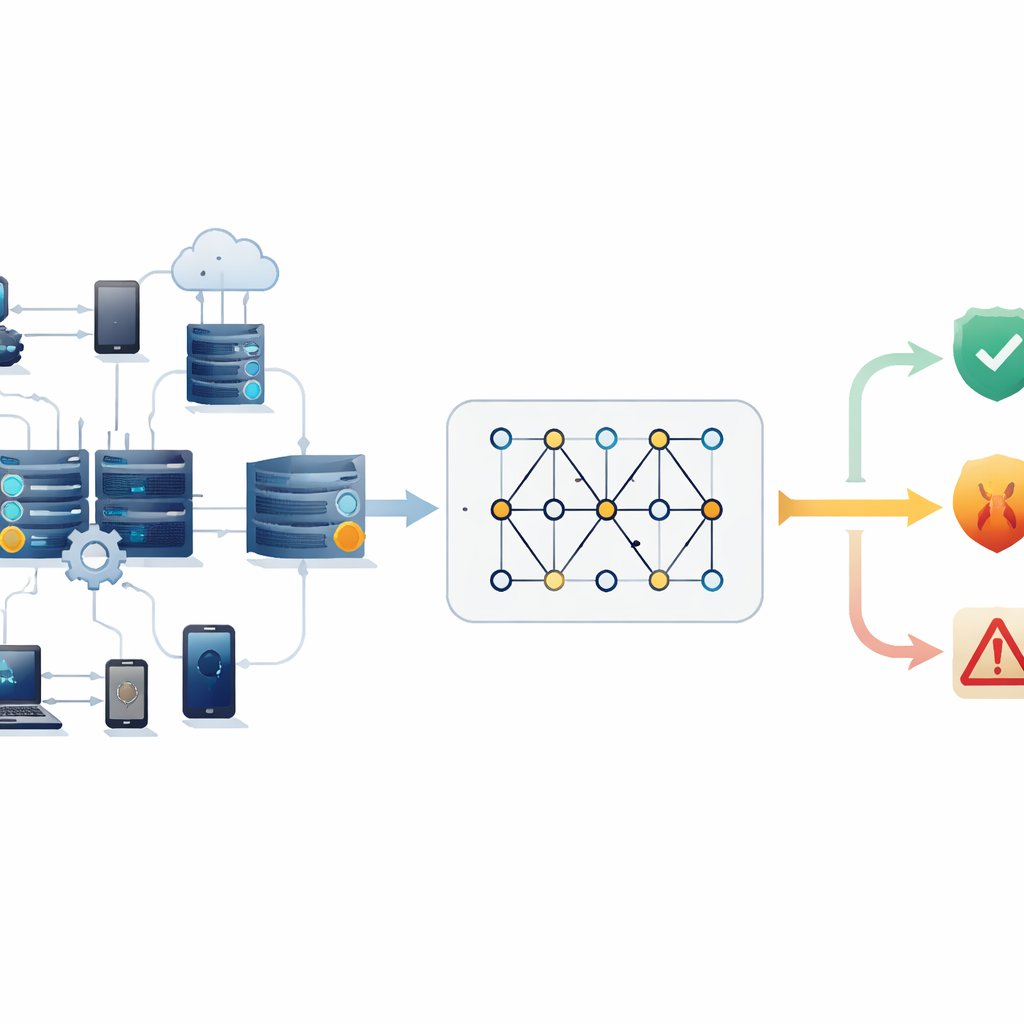
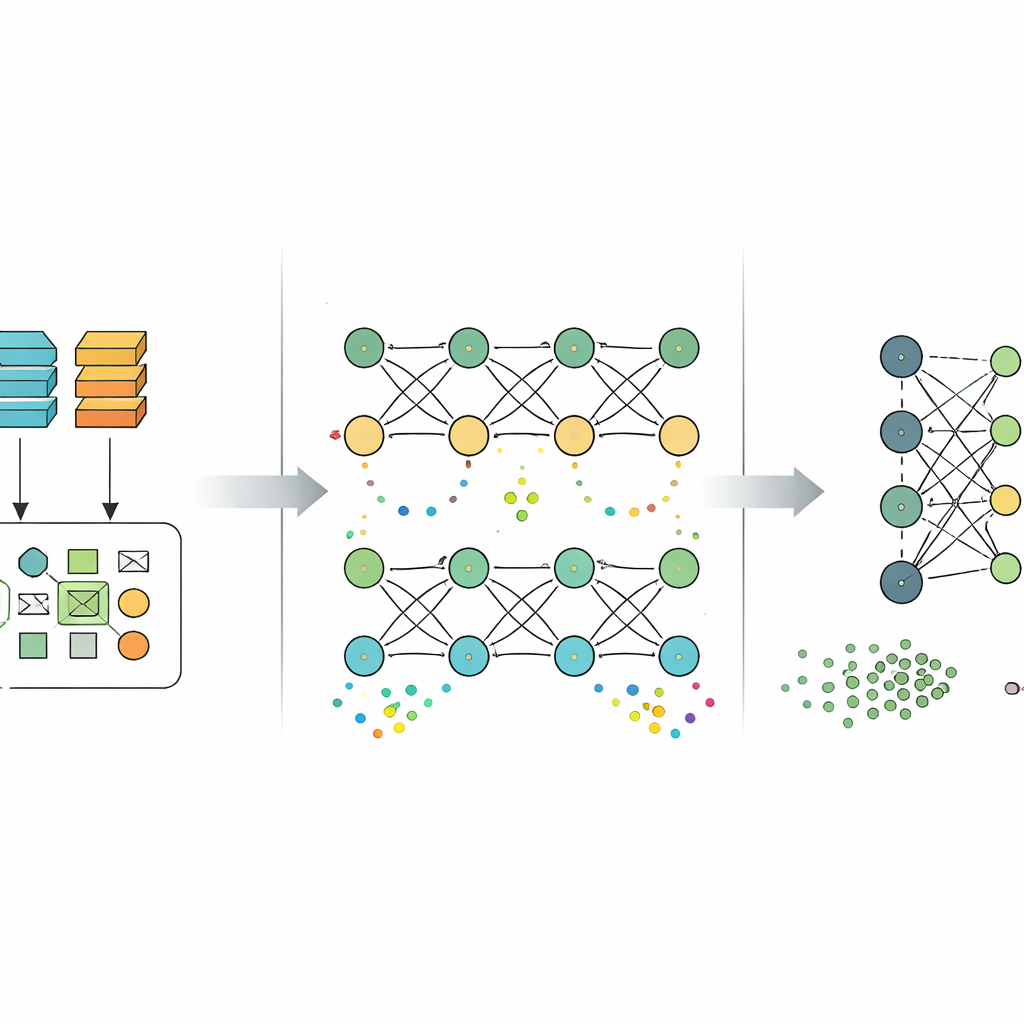
To tackle these limits, the study proposes a “hybrid” design that lets a quantum computer handle only the part it is best at: reshaping data into richer patterns before a standard deep‑learning model makes the final decision. The process starts with a large, well‑known security dataset called UNSW‑NB15, which contains millions of examples of both normal and malicious network behavior. The data are cleaned, unnecessary details like timestamps and raw IP addresses are removed, and the remaining numbers are compressed into a small set of key components. These compact features are then encoded into a simple quantum circuit that uses the strange behaviors of qubits—such as being in multiple states at once and influencing each other at a distance—to generate a new, more expressive description of each network event.
Teaching the model to travel across networks
Once the quantum‑enhanced features are created, they are passed into an ordinary deep‑learning network that learns to distinguish typical traffic from different kinds of attacks. Crucially, the authors do not stop with one dataset. After training on UNSW‑NB15, they reuse what the model has learned and fine‑tune it on two other large benchmarks, CICIDS2017 and CSE‑CIC‑IDS2018, which capture other attack styles, and then on a fourth dataset, TON_IoT, which focuses on smart‑device environments. Each time, the raw data are reshaped to match the structure seen during the first training phase, fed through the same quantum feature extractor, and then used to gently adjust the existing model instead of starting over. This approach, known as transfer learning, is meant to help the system carry useful knowledge from one digital setting to another.
How well the approach performs
The researchers evaluate their framework using standard measures of classification quality, such as how often it predicts the correct label and how reliably it detects harmful events. The hybrid model reaches about 83% accuracy on its initial UNSW‑NB15 training ground, 91% on the combined CICIDS2017 and CSE‑CIC‑IDS2018 data, and 86% on the TON_IoT dataset. It is especially strong at recognizing normal traffic and broad attack categories, though it still struggles with some rare or subtle attack types, which are under‑represented in the data. To limit skewed results, the authors discard a few extremely small or unstable classes and adjust the training process so that the system pays extra attention to attack examples that appear less often.
What this means for everyday security
For non‑specialists, the key takeaway is that quantum computing is not being used here as a magic replacement for existing cybersecurity tools, but as a way to enrich the patterns those tools can see. By using quantum circuits only to reshape the data—and leaving the final decision to proven deep‑learning methods—the authors create a design that could, in principle, run on near‑term quantum hardware while still fitting into current security systems. Their results suggest that this quantum‑assisted transfer learning can help a single model adapt to very different network environments without being retrained from scratch each time. If future work can make these methods efficient and reliable enough for real‑time traffic, they could strengthen the invisible shields that protect everyday online activities across homes, businesses, and critical infrastructure.
Citation: Alsubai, S., Ayari, M., Kryvinska, N. et al. Quantum transfer learning for cross-domain cybersecurity threat detection and categorization. Sci Rep 16, 10258 (2026). https://doi.org/10.1038/s41598-026-40634-z
Keywords: cybersecurity, intrusion detection, quantum machine learning, transfer learning, network traffic