Clear Sky Science · en
Detection of DSCP-based traffic prioritization manipulations and their impact on network performance
Why your online traffic is not treated equally
Every time you place a video call, stream a movie, or join an online game, your data competes with millions of other packets racing across the internet. To keep things smooth, networks quietly give some traffic a fast lane. But those fast lanes can be cheated or misconfigured, letting the wrong packets jump the queue and slowing everyone else down. This paper explores how such unfair behavior can be spotted automatically using modern artificial intelligence, before it harms call quality, streaming, or other critical online services.
How the internet decides who goes first
Modern networks use a tiny field inside each data packet, called a Differentiated Services Code Point (DSCP), as a kind of color code for priority. Voice calls and live video get colors that tell routers to send them first, while normal web browsing gets a lower grade. When this system works properly, delay, jitter, and packet loss stay low for time‑sensitive apps. But if the markings are wrong—by mistake or on purpose—low‑value traffic can sneak into the fast lane, or important traffic can be pushed aside, leading to choppy calls, frozen video, and sluggish apps.
Ways the system can be gamed
The authors map out several kinds of manipulation that can quietly upset this priority system. In a downgrade, high‑priority streams such as voice or video are relabeled as ordinary traffic, so they suffer extra delay and glitches when the network is busy. In an upgrade, low‑priority flows are falsely painted as premium, hogging bandwidth at others’ expense. Other tricks randomly strip markings from packets, bounce them between priority levels, or give odd markings to control protocols that should follow strict rules. Each of these patterns leaves a subtle fingerprint in how packet delay, jitter, and throughput evolve over time.
Building a realistic testbed of internet flows
To study these fingerprints, the team created a controlled mini‑internet and generated everyday activities: video and audio streaming, online games, financial transactions, voice calls, and chat. They captured hundreds of thousands of packets, recording when they were sent, their size, which application they belonged to, and how they were marked and delivered. From this raw stream they computed performance measures like latency, jitter, throughput, and packet loss, then deliberately altered DSCP markings to simulate different manipulation scenarios. The resulting dataset mixed honest and tampered traffic, providing a demanding test for any detection method.
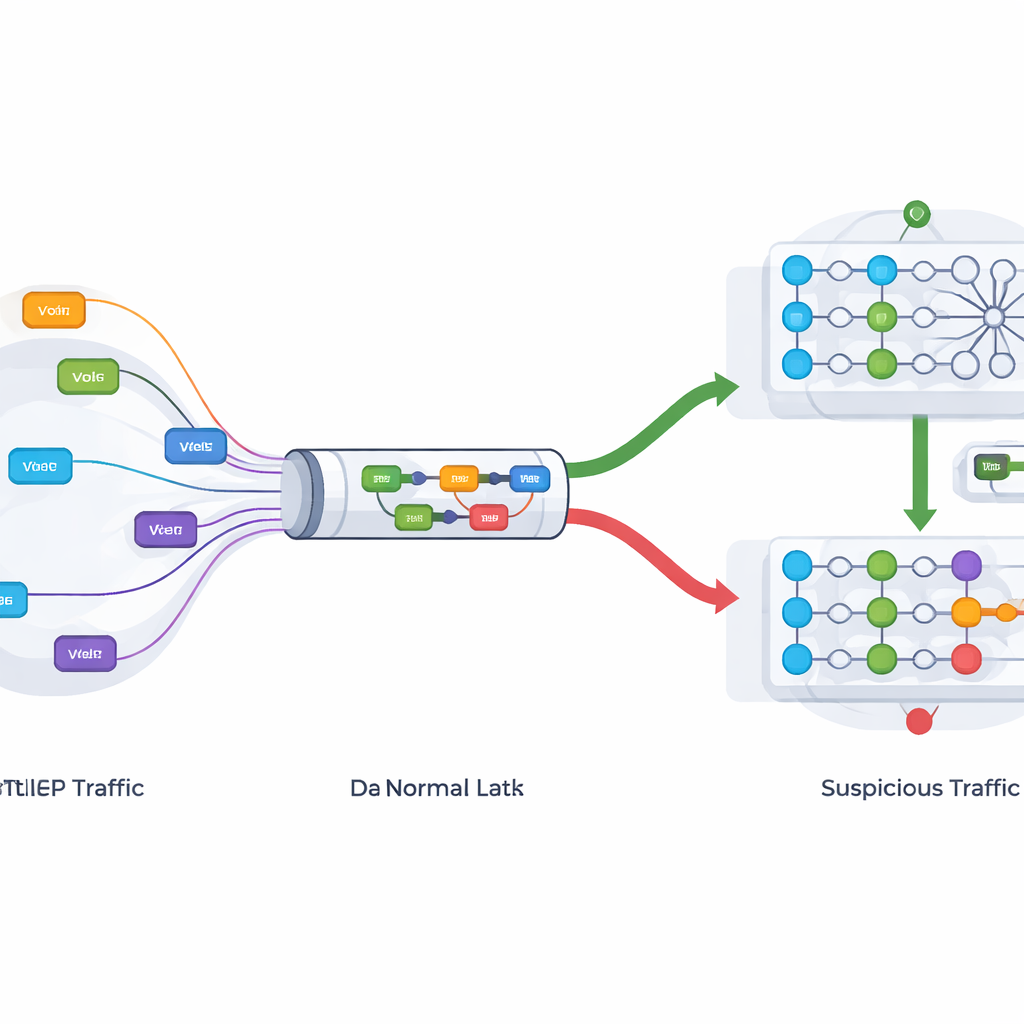
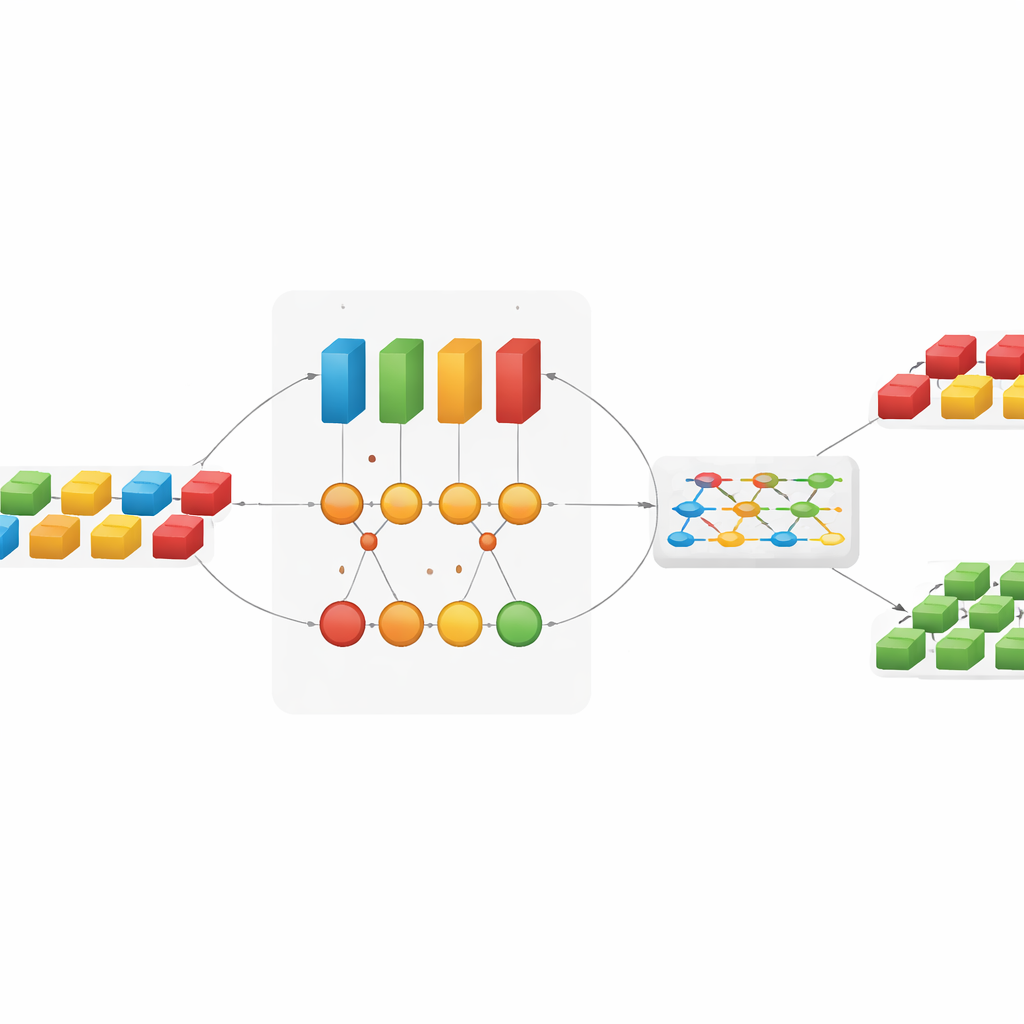
Letting deep learning watch the wires
Instead of relying on fixed rules, the researchers turned to deep learning models that can learn patterns directly from data. One model, a Convolutional Neural Network (CNN), specializes in spotting short, local bursts such as sudden shifts in packet priority or size. Another, based on Recurrent Neural Networks and their Long Short‑Term Memory (LSTM) variant, tracks longer‑term trends in a flow, such as gradual downgrades or periodic bleaching of markings. By feeding time‑ordered sequences of packet features into these models, the system learns how normal traffic behaves and how manipulated traffic subtly deviates from that norm.
How well the smart detectors performed
Each model on its own already did impressively well: the CNN correctly classified roughly 97 percent of cases, while the RNN and LSTM variants exceeded 99.7 percent accuracy in distinguishing manipulated from legitimate flows. To push performance further, the authors combined multiple models into an ensemble that takes a soft vote across their predictions. This combined approach reached about 99.3 percent accuracy, with equally strong scores for catching almost all manipulations while rarely sounding a false alarm. Compared with more traditional methods such as logistic regression or random forests, the deep learning approaches were far better at capturing the complex, time‑dependent behavior of real traffic.
What this means for everyday users
For the average person, the technical details boil down to a simple promise: smarter monitoring can keep the internet’s fast lanes honest. By continuously watching how packets are marked and how they actually move through the network, these deep learning models can flag unfair or malicious prioritization in near real time. That gives operators a way to restore balance—so that voice calls, emergency communications, and business‑critical services get the service they were promised, without being silently undercut by misconfigurations or gaming of the system.
Citation: Rahman, M.M.H., Alnaeem, M. & Ibrahim, A.A. Detection of DSCP-based traffic prioritization manipulations and their impact on network performance. Sci Rep 16, 10637 (2026). https://doi.org/10.1038/s41598-026-44350-6
Keywords: network traffic prioritization, DSCP manipulation, deep learning security, quality of service, internet performance