Clear Sky Science · en
A hybrid deep learning approach with temporal awareness for intelligent intrusion detection in 6G-enabled IIoT networks
Smarter Shields for Future Factories
The next wave of wireless networks and smart factories promises faster production, remote control, and real-time monitoring of machines. But as more devices talk to each other over the air, they also open new doors for hackers. This paper explores a new way to automatically spot cyber intruders in future 6G-connected industrial systems, using an advanced kind of artificial intelligence that can watch network traffic over time and pick out subtle signs of danger before damage is done.

Why Tomorrow’s Factories Need New Guards
Modern industrial sites are filling up with connected sensors, robots, and controllers, all linked through what is called the Industrial Internet of Things. As 6G networks arrive, they will connect even more devices with faster speeds and almost no delay. That is good for tasks like remote surgery or self-driving vehicles inside a plant, but it also means that attacks can spread quickly and hide inside huge streams of data. Traditional security tools rely on fixed rules and known threat signatures; they work best when the attack is already well understood. In complex, rapidly changing 6G industrial networks, many attacks are new, rare, or cleverly disguised, so rule-based systems struggle to keep up.
Teaching Machines to Spot Subtle Threats
To tackle this problem, the authors turn to deep learning, a branch of AI that learns patterns directly from data. Instead of hand-coding what an attack looks like, the system studies large amounts of past network traffic from an open dataset called Edge-IIoTset, which includes many types of attacks such as denial of service, data theft, code injection, and malware, mixed with normal behavior. The dataset is highly imbalanced, with far more normal traffic than attacks, and some attack types are rare. To avoid misleading results, the researchers carefully prepare the data: they clean it, remove duplicates, convert text-like entries into numbers, drop unhelpful or overly specific fields, and use a stratified sampling technique so that both training and test sets contain a fair share of each attack type.
How the Hybrid AI Watchdog Works
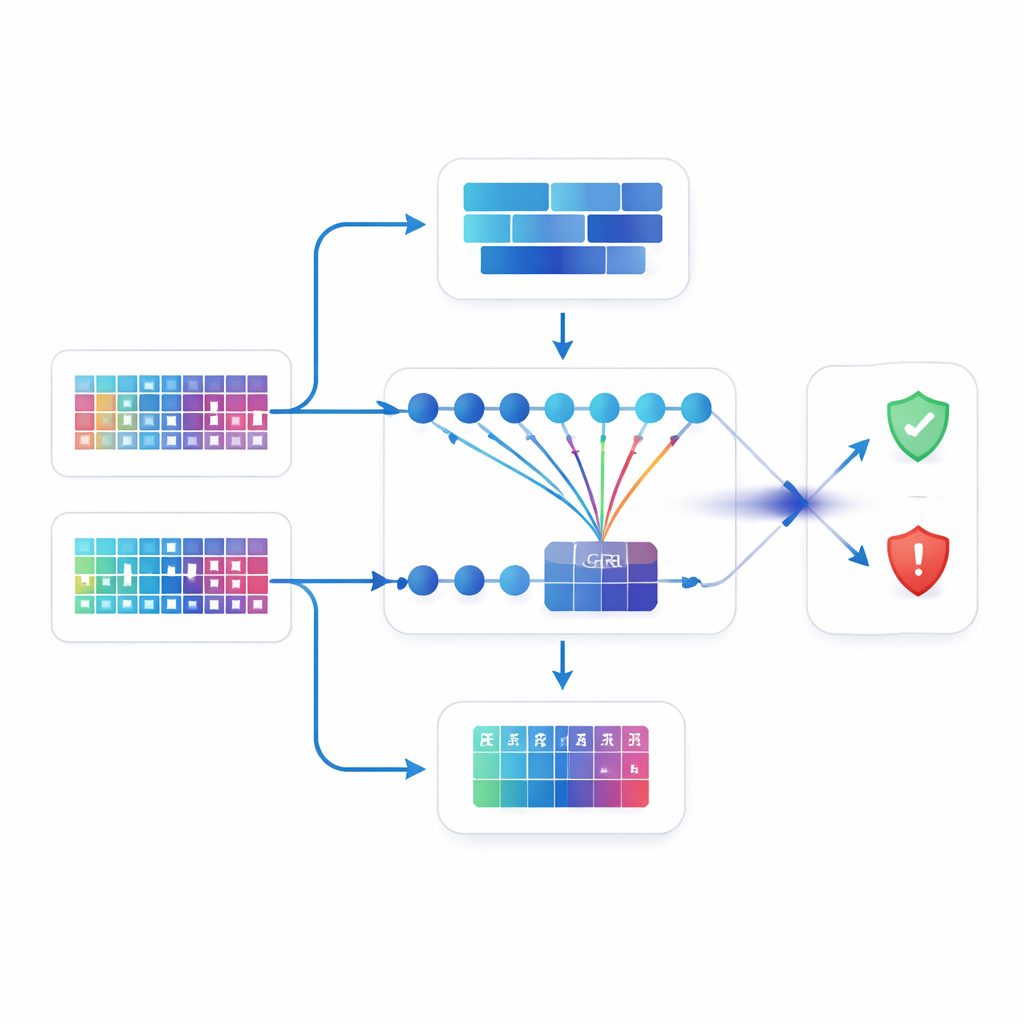
The heart of the study is a hybrid model that combines two different deep learning branches and an attention mechanism. One branch, a deep neural network, looks at traffic more like a snapshot, extracting broad, global patterns across all features. The other branch, called a bidirectional gated recurrent unit, is designed for sequences; it follows how traffic evolves over time, both forward and backward, capturing rhythms and context that may reveal slow or staged attacks. On top of this, an attention component acts like a spotlight, learning which moments in the traffic history matter most for deciding whether something is suspicious. The outputs of the two branches are then fused and passed into a final classifier that decides whether each piece of traffic is normal or belongs to one of several attack types.
Putting the New Guard to the Test
The authors compare their hybrid design against several widely used deep learning setups, including simpler neural networks, convolutional networks, and models that mix convolutional layers with recurrent layers. All models are trained and tested under the same conditions to make the comparison fair. The proposed model reaches an accuracy of about 96.9 percent and keeps the false alarm rate very low. It not only outperforms the baseline models built by the authors but also beats the best results reported in other recent studies on the same dataset. Detailed checks, such as confusion matrices and performance curves, show that the model can separate many different attack categories while rarely mislabeling normal traffic as malicious—important for avoiding needless shutdowns in a factory.
What This Means for Safer Connected Industry
For a non-specialist, the key takeaway is that this work demonstrates a more watchful and adaptable digital guard for future factories and industrial sites. By combining broad pattern sensing, time-aware analysis, and a focusing mechanism that highlights the most telling moments in network activity, the model can detect a wide range of cyberattacks in a busy 6G-enabled industrial environment with high accuracy and few false alarms. While the authors note that more work is needed to make the system easier to interpret, faster, and tested on additional real-world data, their results suggest that such hybrid AI approaches could become a central part of how next-generation industrial networks stay resilient against evolving cyber threats.
Citation: Guo, G., Qamar, F., Kazmi, S.H.A. et al. A hybrid deep learning approach with temporal awareness for intelligent intrusion detection in 6G-enabled IIoT networks. Sci Rep 16, 13474 (2026). https://doi.org/10.1038/s41598-026-43058-x
Keywords: 6G industrial networks, intrusion detection, deep learning security, Industrial IoT, cyberattack detection