Clear Sky Science · en
Design of a multi-layered privacy-preserving architecture for secure medical data exchange in cloud environments
Why safer sharing of your health records matters
Modern medicine increasingly depends on data that follow you everywhere: heart readings from your smartwatch, lab results from the hospital, and scans read by specialists halfway around the world. Much of this information now travels through commercial cloud services. That convenience comes with a price: once data leave the hospital’s walls, they become tempting targets for hackers, prying insiders, and even quiet tampering that could change a diagnosis. This study explores how to wrap cloud-based health systems in several coordinated layers of protection so that doctors still get the information they need, while patients keep their privacy and trust intact.

The problem with sending hospital data to the cloud
Health records used to live in paper folders and on computers inside the hospital. Today, cloud platforms make it easy to store huge collections of lab results, medical images, and continuous readings from body-worn sensors, and to share them for telemedicine and research. But the moment those records are pushed to an outside provider, several risks arise at once. Curious staff at a cloud company might browse data they do not need to see, different storage services might secretly cooperate to piece together more information about a person, and attackers might alter records in ways that are hard to detect. Many current defenses tackle just one of these issues at a time—for example, tools that only encrypt files, or systems that only look for strange behavior. The authors argue that this piecemeal approach leaves dangerous gaps once data move through complex, multi-cloud healthcare networks.
A layered pathway from bedside to cloud and back
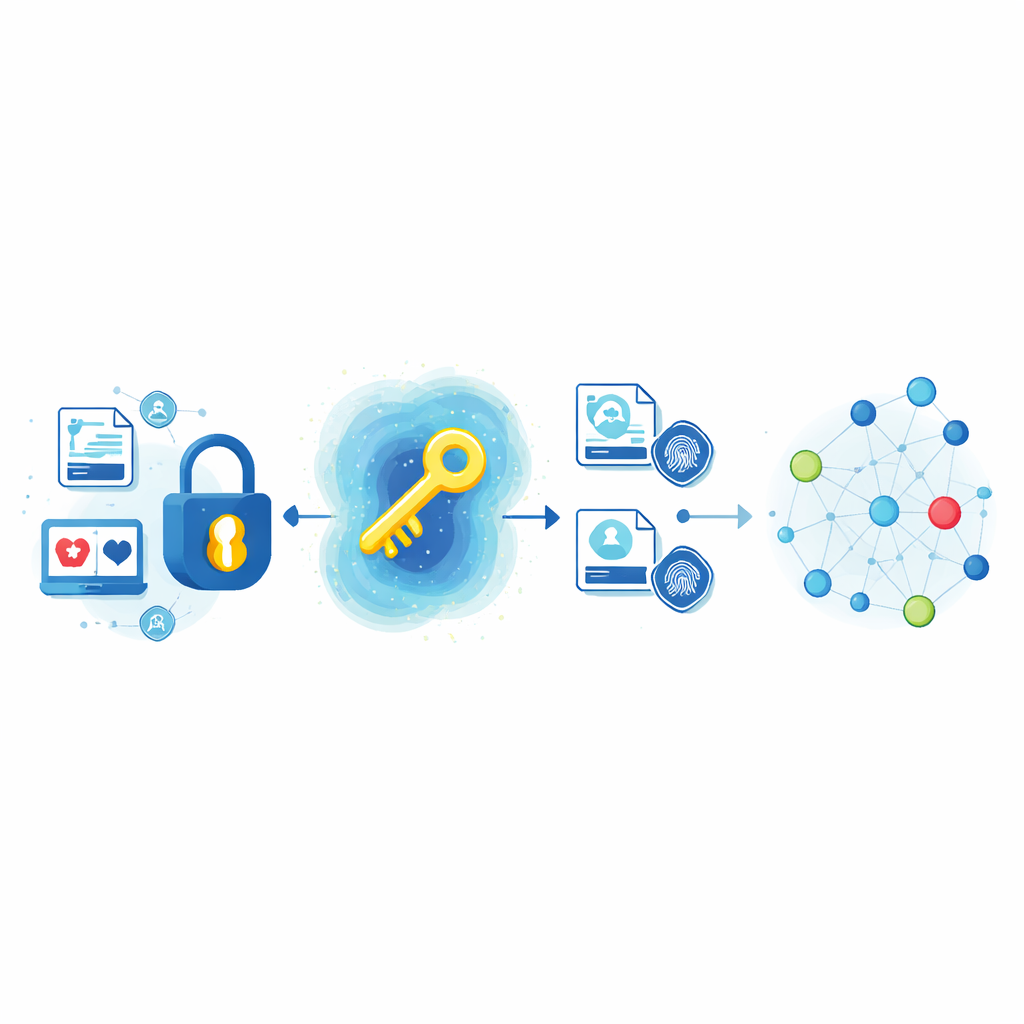
The researchers propose an end-to-end security pathway that follows health data from the instant they are created, through storage and sharing in the cloud, to every later access. When a personal health record is generated—by a device, a lab machine, or hospital staff—it is immediately scrambled using a special method called attribute-based encryption. Instead of simply locking a file with a password, this method ties access to who you are and what role you play, such as a cardiologist on duty or a lab technician on a certain team. A trusted key authority issues digital keys that embody these roles and can later revoke them. The cloud server stores only the scrambled versions and can help with part of the decoding work, but never sees the original content. This design lets hospitals change staff permissions or retire old accounts without having to re-encrypt years of past records.
Stronger keys and built-in tamper alarms
Good locks are only as strong as their keys. To prevent attackers from guessing or statistically analyzing keys, the team adds another layer that they call haze optimization. This is a search procedure that actively hunts for keys whose bit patterns are as random and unpredictable as possible, much like stirring a combination lock until every wheel is thoroughly mixed. On top of this, they attach a digital fingerprint to every encrypted record using a widely trusted recipe known as SHA-256. The fingerprint is calculated when the data are first stored, and then recalculated each time a record is retrieved. If even a single bit of the underlying data has been altered—whether by accident, hardware faults, or intentional tampering—the fingerprints will no longer match, and the system can automatically refuse access or trigger an alert.
Teaching the system to spot suspicious behavior
Cryptography alone cannot catch a nurse using someone else’s login or a technician quietly downloading far more records than usual. To address this, the framework adds an intelligent monitoring layer based on a modern type of machine learning that works on networks of relationships. Here, every user, device, and file becomes a node in a graph, and every login or data access becomes a connection between them. Over time, the model learns what normal activity looks like: which departments usually access which kinds of records, at what times, and from which devices and locations. When a new action deviates too far from these learned patterns—for instance, a non-medical staff member repeatedly touching sensitive files from an unusual device—the system flags the event as an anomaly within milliseconds, all without looking at the raw medical content.
What the tests say about safety and speed
To see whether layering these protections slowed the system down, the authors built a testbed using real electronic health records and realistic cloud hardware. They measured accuracy in spotting strange access patterns, the time needed to encrypt and decrypt data, the delay seen by users, network throughput, memory use, and energy consumption. The combined design achieved very high reliability in distinguishing normal from suspicious behavior, while blocking over 99% of simulated improper access attempts and preserving data integrity in nearly all checks. At the same time, it kept delays to a few thousandths of a second and supported many simultaneous users with modest computing resources. Compared with several earlier designs, it was both more secure and more efficient.
What this means for patients and clinicians
For non-specialists, the main message is that the authors do not rely on a single magic lock to protect cloud-based health data. Instead, they weave together smarter locks, better keys, built-in tamper alarms, and an always-on digital sentry that watches how the system is used. Their results suggest that hospitals and telemedicine providers can move more confidently toward cloud platforms without forcing a trade-off between privacy and performance. In practical terms, that could mean faster remote consultations, more accurate data-driven medicine, and fewer chances for your medical history to be exposed or silently altered along the way.
Citation: Muthuvel, S., Priya, S. & Sampath Kumar, K. Design of a multi-layered privacy-preserving architecture for secure medical data exchange in cloud environments. Sci Rep 16, 11282 (2026). https://doi.org/10.1038/s41598-026-40122-4
Keywords: cloud healthcare security, medical data privacy, health data encryption, anomaly detection, electronic health records