Clear Sky Science · en
Bridging disorder and order in random lasers for cryptographic applications via deep learning
Light, chaos, and hidden patterns
Every day, our private messages, banking details, and medical records are protected by digital keys—long strings of bits that should be impossible to guess. But as computers, especially quantum computers, grow more powerful, today’s mathematical tricks for generating and sharing these keys may no longer be safe. This study explores an entirely different approach: using a special kind of “random” laser and artificial intelligence to create and transmit keys in a way that is rooted in the laws of physics rather than in hard math problems.
A restless laser born from disorder
Instead of the carefully polished mirrors found in ordinary lasers, a random laser relies on disorder. Here, the authors use a short length of plastic optical fiber filled with dye molecules and tiny nanoparticles. When a green laser pulse enters this cloudy core, light bounces around unpredictably, gaining energy as it scatters. Above a certain pump energy, this mix of gain and scattering produces a laser whose spectrum looks like a forest of narrow, jagged spikes. The positions of these spikes in color stay fixed, but their heights flicker wildly from one pulse to the next. This restless behavior makes the device an appealing physical source of randomness, an essential ingredient for secure cryptography.
Random in time, but not in every way
The team first asks whether these intensity flickers over time can be predicted. They treat the spectrum at each color as a separate time series and feed long histories of these signals into several advanced neural network models that are usually excellent at learning patterns in data. For comparison, they also generate a conventional pseudo-random sequence, which is technically predictable because it follows a hidden formula. The networks easily learn the artificial sequence, reaching almost perfect prediction accuracy. In stark contrast, the same models perform extremely poorly on the laser data, even when given more training examples or longer histories. This shows that, pulse to pulse, the brightness at a given color channel is essentially unpredictable, reinforcing the laser’s value as a high-quality randomness source.
Order hiding inside the spectrum
Yet the story does not end with chaos. When the authors look across the spectrum at a single moment in time, they see hints of structure: some wavelengths tend to rise and fall together, while others oppose each other. To probe this subtle order, they compress each spectrum by sampling only the stable peaks and valleys and then task a deep neural network with a new challenge: predict the height of one or more missing peaks from the remaining ones at that same instant. Now the machine learning shines. Using only the intensities at other colors, the network can recover a single missing peak with about 99.99% accuracy and several peaks with still-high accuracy. In other words, although the laser is random in time, its spectral components at a given moment are linked by a hidden, deterministic relationship that a neural network can learn to exploit.
Turning flicker into digital secrets
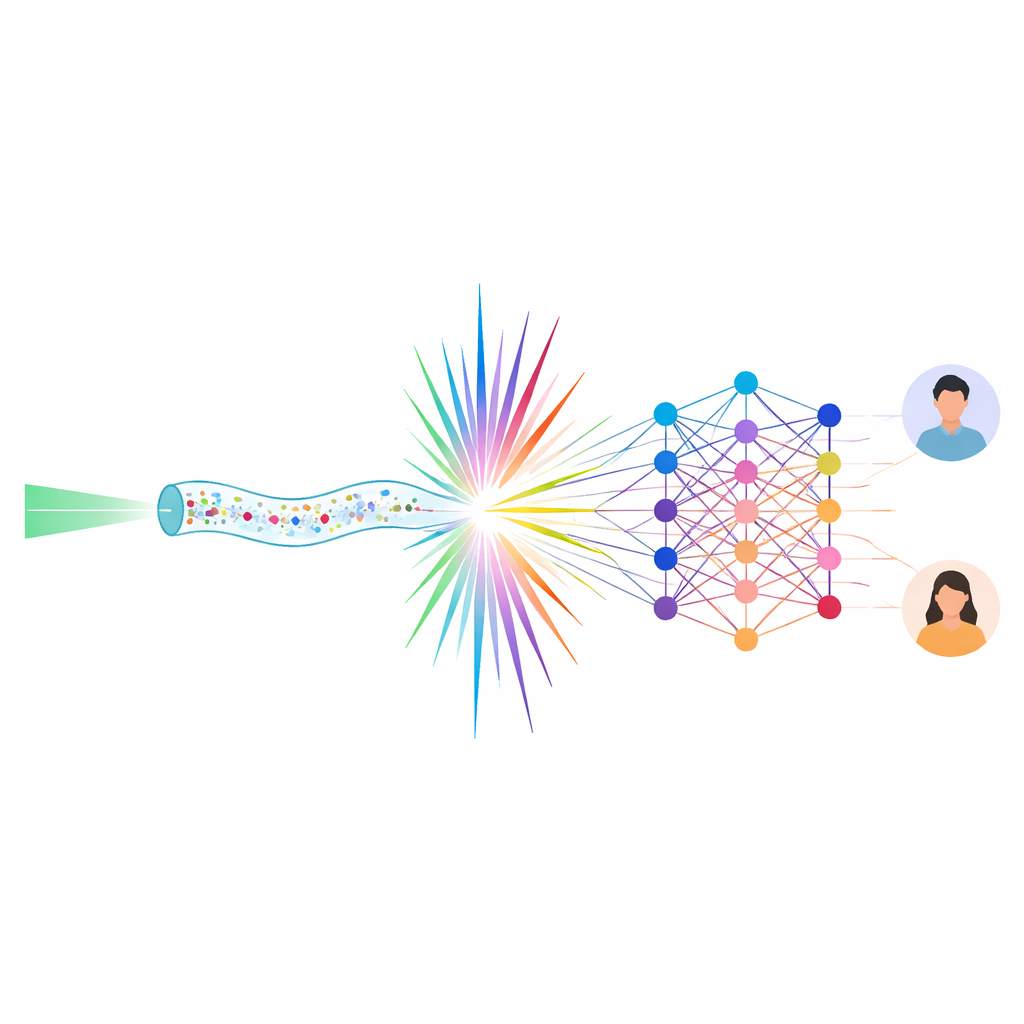
Building on this dual nature—random over time, ordered across colors—the researchers design a physical scheme for secure key generation and distribution. One party, Alice, measures the brightness of a chosen spectral peak over many pulses and converts this unpredictable sequence into random bits, carefully processing it so that zeros and ones appear with equal likelihood and pass stringent statistical tests. She then removes that peak from the spectrum and sends only the remaining light to Bob through free space. Bob measures the incomplete spectrum and feeds its peak and valley intensities into a neural network that has been trained beforehand. The network reconstructs the missing peak’s intensity at each pulse, allowing Bob to generate exactly the same bit sequence that Alice did—without ever having received the critical peak directly.
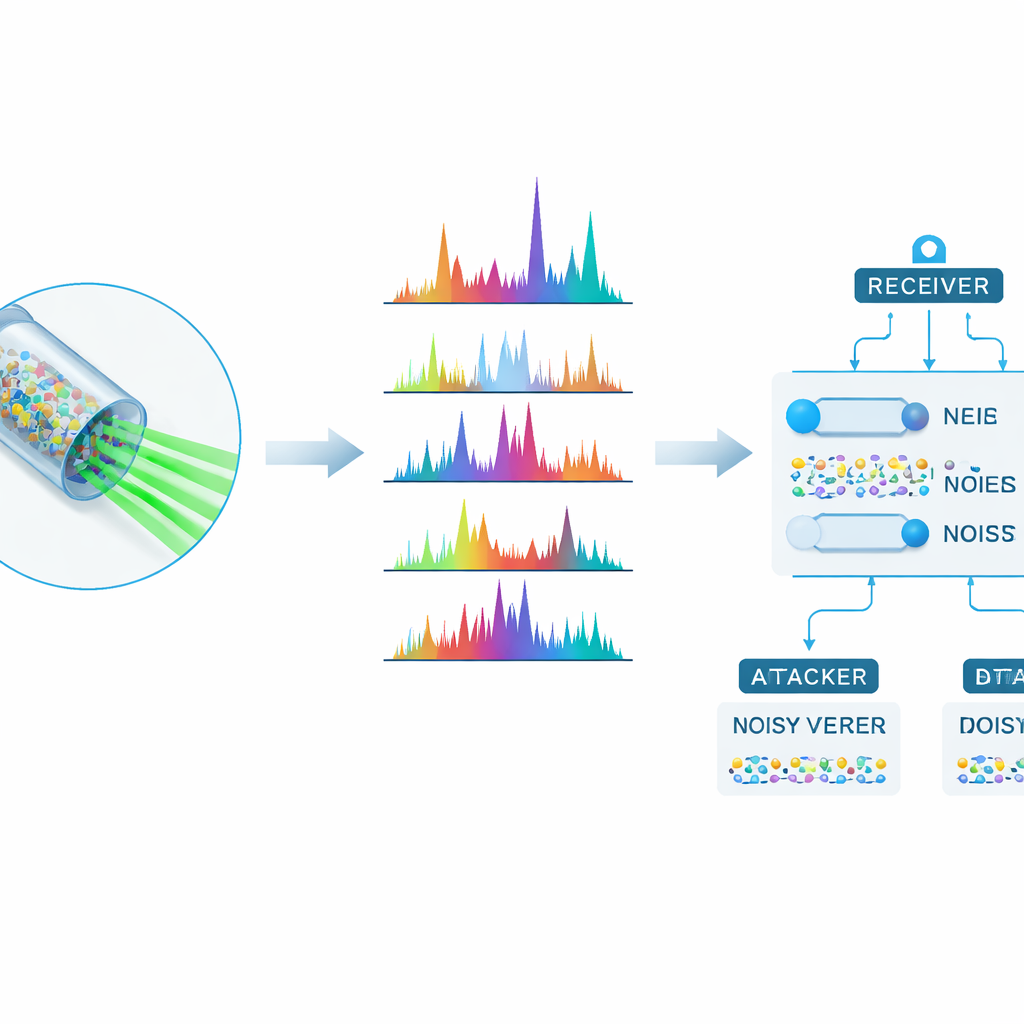
Keeping eavesdroppers in the dark
The authors also consider two types of eavesdroppers. One listens in without access to the specialized neural network and can only sample a nearby spectral channel; the other has the right network but receives a distorted, noisy signal that slightly shifts the sampling positions. In simulations, both attackers end up with keys that are essentially uncorrelated with Alice’s, while Bob’s reconstructed key remains almost perfectly aligned even in the presence of noise and changes in laser power. Error-correcting codes can further clean up Bob’s bits without helping the attackers. To a lay observer, the main message is that this hybrid of disorderly light and clever algorithms can create shared digital secrets that are extremely hard to steal, pointing toward new, hardware-based ways to secure our information in a future where traditional cryptography may no longer be enough.
Citation: Hu, Z., Qi, L., He, S. et al. Bridging disorder and order in random lasers for cryptographic applications via deep learning. Commun Phys 9, 132 (2026). https://doi.org/10.1038/s42005-026-02600-z
Keywords: random lasers, physical cryptography, deep learning, secure key distribution, optical fibers