Clear Sky Science · en
GNN-based trust propagation and intelligent certificate revocation decision mechanism for large-scale IoT networks
Why smart devices need smarter trust
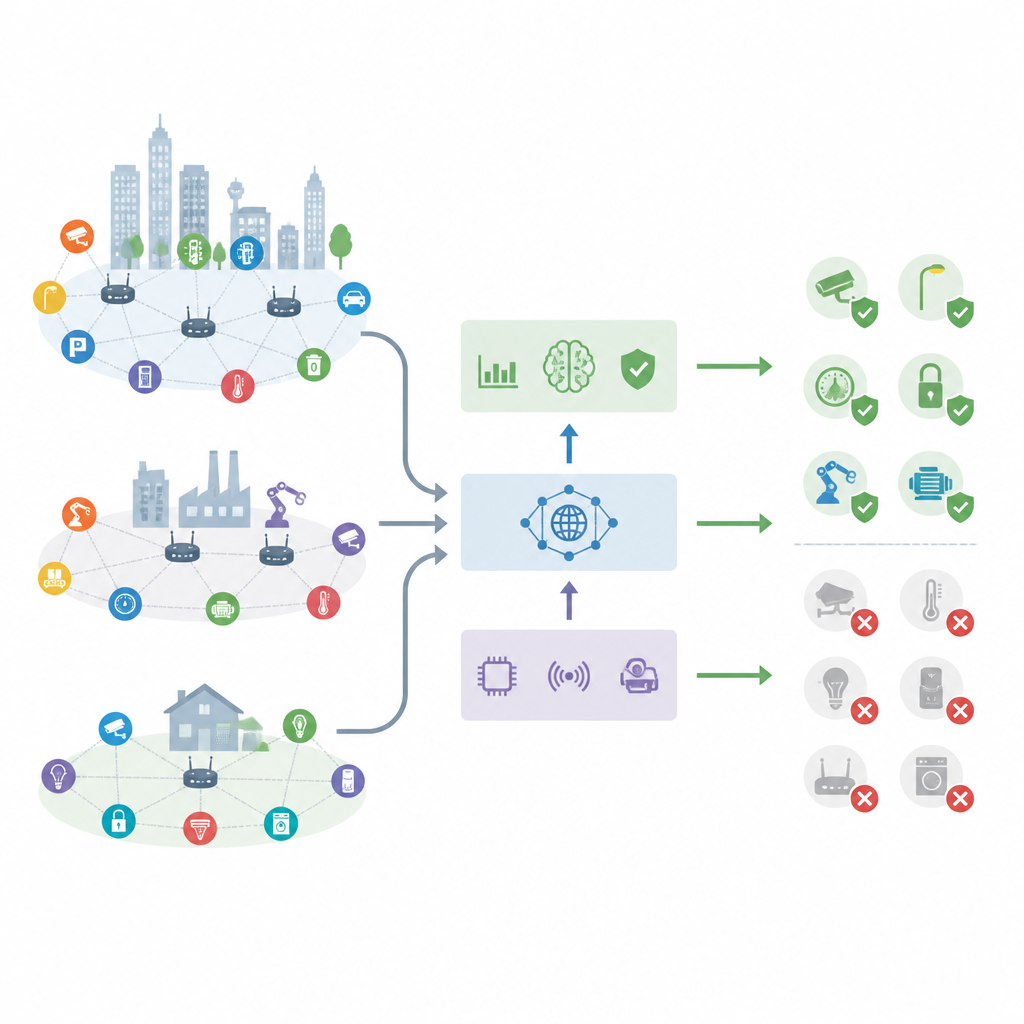
From home cameras to factory sensors, billions of gadgets now talk to each other and to the internet. Each one relies on digital ID cards, called certificates, to prove it can be trusted. But when a device is hacked, those IDs must be canceled quickly. Traditional tools often react too slowly for such huge, fast-moving networks. This study introduces an AI-driven system that helps large Internet of Things networks decide which devices to trust and when to cut off their certificates in near real time.
Growing pains of connected gadgets
As connected devices spread through cities, hospitals and industry, keeping track of which ones are still safe has become a major challenge. Old security systems were built for smaller, more stable networks, not for millions of low-power sensors that appear, disappear and move around. Lists of revoked certificates can take hours to update, and online checks for each device can overload the network. At the same time, simple reputation scores based on past behavior ignore the complex web of relationships between devices. The result is slow, blunt tools that either miss real attacks or shut down healthy devices.
Looking at devices as a living network
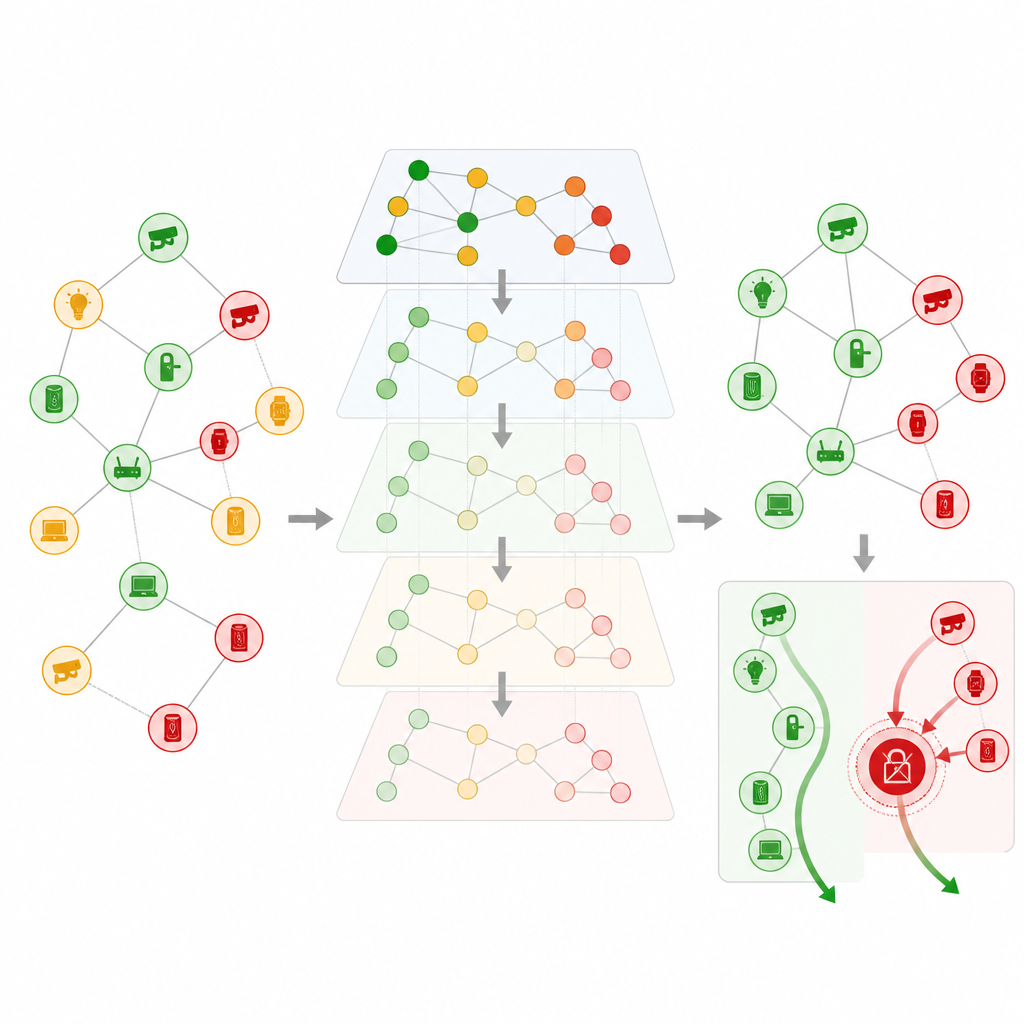
The authors argue that trust in such systems behaves more like a social network than a simple checklist. Devices do not just talk to a central server; they constantly interact with one another, forming a shifting graph of connections. To capture this structure, the team models the whole IoT deployment as a network of nodes and links. Each node carries information about its certificate status, behavior patterns and role, while each link reflects how often two devices talk and how trustworthy that relationship has been. This graph then feeds into a special kind of neural network designed to learn from connections, not just from individual data points.
How the AI learns and spreads trust
At the heart of the system is a graph attention model that spreads trust levels across the network. Instead of treating all neighbors equally, the model learns which nearby devices deserve more influence when estimating whether a node is trustworthy. It also bakes in the idea that old information fades in value over time, so stale records count less than fresh observations. By stacking several of these attention layers, the system can take into account not just direct neighbors but also devices a few steps away, without letting distant, unreliable information dominate. The result is a compact “trust fingerprint” for every device that reflects both its own history and its position in the wider network.
Turning trust signals into quick action
Trust scores alone are not enough; someone still has to decide when to pull a device’s certificate. The researchers therefore add a decision module that blends each device’s trust fingerprint with signs of odd behavior and how central it is in the network. This module assigns a risk score, then uses an adaptive threshold that shifts according to how many false alarms the system has been making. Devices can be left alone, watched more closely or have their certificates revoked right away. To keep overhead manageable in very large networks, risky devices are processed in batches that prioritize those most likely to cause near-term harm.
What tests on large networks reveal
The team tested their framework on data from a smart campus filled with diverse devices, adding realistic simulated attacks such as fake identities and trust manipulation. Across networks ranging from just over a thousand to more than a hundred thousand devices, the new method kept trust predictions closely aligned with ground truth while using computing resources efficiently. Compared with older reputation systems and standard graph models, it stayed accurate even as the network grew. For certificate decisions, it reached a strong balance between catching truly compromised devices and avoiding needless revocations, with risk scores that separated malicious from unusual but harmless behavior.
What this means for everyday security
In plain terms, the framework offers a way for large IoT systems to spot untrustworthy devices faster and with more nuance than current tools. By viewing trust as something that flows along the links between devices, and by letting an adaptive AI decide when to act, the system can cut the time between compromise and certificate revocation to just a few seconds in the tested setting. While the results depend on how closely real-world attacks match the study’s assumptions, the work points toward security tools that grow with our expanding fleets of connected gadgets instead of slowing them down.
Citation: Han, W., Sui, M., Gao, Y. et al. GNN-based trust propagation and intelligent certificate revocation decision mechanism for large-scale IoT networks. Sci Rep 16, 14991 (2026). https://doi.org/10.1038/s41598-026-43310-4
Keywords: Internet of Things, network trust, graph neural network, certificate revocation, cybersecurity