Clear Sky Science · en
OFDM-based quantum key distribution access network reaching Nyquist limits
Why future-proof secrets matter
Every time you shop online or send a private message, invisible digital keys protect your information. Today those keys are generated using hard math problems that even supercomputers struggle to solve. But powerful quantum computers now on the horizon could crack many of these problems, putting long-term privacy at risk. This paper explores a way to share secret keys that stays safe even in a quantum era, and shows how to do it efficiently for many users at once over existing fiber networks.
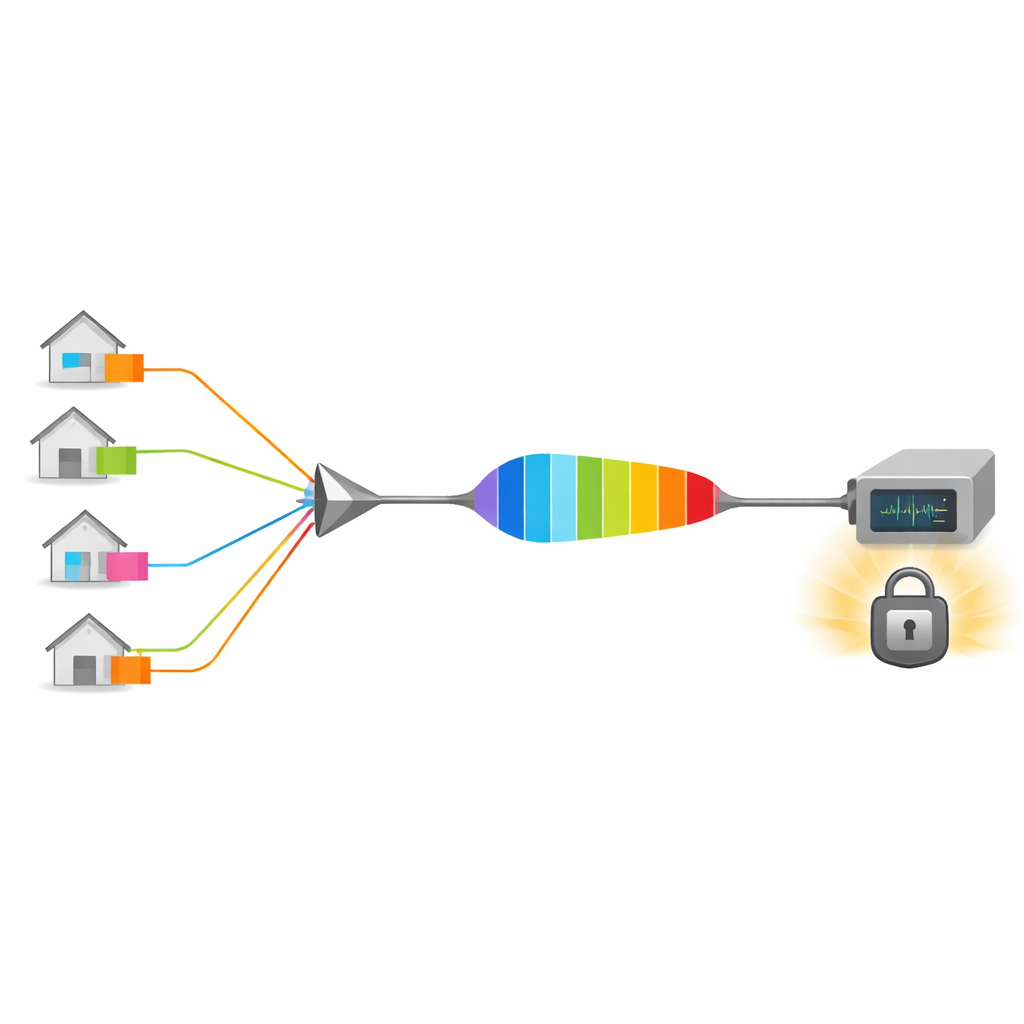
From one secure link to many
Quantum key distribution, or QKD, uses single particles of light to create shared random keys between two distant parties. Any attempt to eavesdrop leaves telltale traces in the quantum signals. While one-to-one QKD links are already well demonstrated, the real world needs networks: citywide and national systems where many users connect through shared infrastructure. In these networks, the biggest bottleneck is how much key material can be generated within the limited bandwidth of the fiber and receivers. Traditional approaches divide the resource in time or in frequency between users, which either slows everyone down or wastes spectrum on protective gaps between channels.
Packing more quantum signals into the same fiber
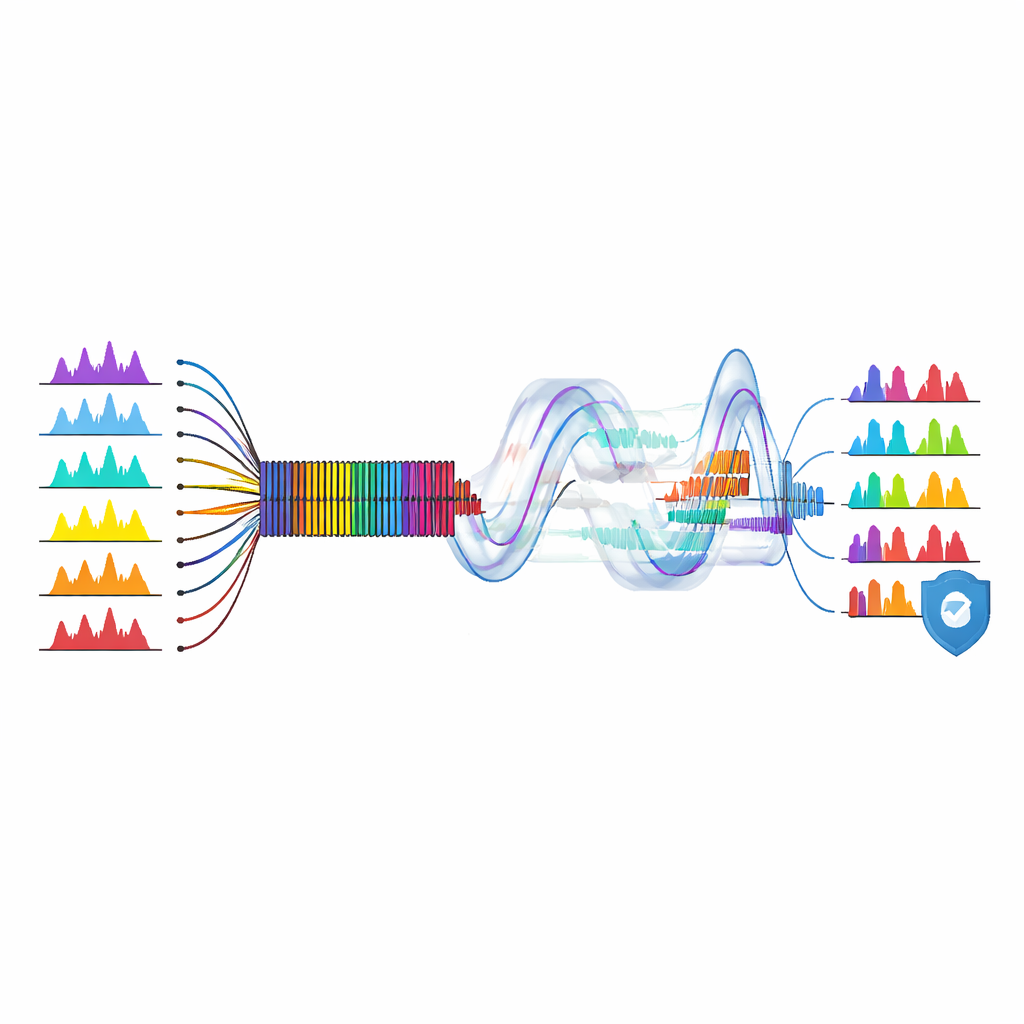
The authors propose a new architecture called an OFDM-based continuous-variable quantum access network. In simple terms, many users send their quantum signals at slightly different radio-like tones within the same light beam. These tones are arranged so that, in the frequency domain, they are perfectly non-overlapping and can be separated without the usual filters. At a central node, called the quantum line terminal, a single coherent receiver can recover all users’ signals by applying different digital demodulation patterns. By choosing the spacing between tones to match the data symbol rate, the scheme reaches the Nyquist limit: it packs as many quantum symbols per second into the available bandwidth as the laws of information theory allow.
Taming messy paths with a clever guard band
Real networks are not perfectly tidy. Different fibers have slightly different lengths and conditions, so signals from multiple users arrive at the combiner with small timing and frequency mismatches. This so-called multi-path effect causes the carefully arranged tones to leak into each other, introducing noise that can destroy the secrecy of the keys. To counter this, the team borrows a trick from modern wireless systems: a cyclic prefix. They add a short repeated segment in front of each quantum symbol, which acts like a shock absorber for timing differences. Their theoretical analysis, using a detailed quantum model, shows how this prefix allows the receiver to recover each user’s signal cleanly while trading off a modest reduction in net data rate.
From theory to a working multi-user demo
Building on this framework, the researchers construct a laboratory network based on existing passive optical network hardware, similar to what brings broadband into homes. A narrow-line laser is split among several user modules, each imprinting a faint, randomly varying pattern on its own subcarrier tone, plus a special pilot tone used to track slow drifts. These modulated beams are passively combined and sent through up to 40 kilometers of standard fiber to the central receiver. There, a single integrated coherent detector captures the optical field, and digital signal processing disentangles the overlapping tones, corrects phase variations, and extracts the quantum measurements for each user individually.
How fast and how far can it go?
Using their setup, the authors demonstrate secure key sharing for three simultaneous users (plus one pilot channel) with a total network capacity of seven users. At a distance of 25 kilometers, each user can obtain a secret key rate of about 4.06 megabits per second in the idealized limit of infinitely long data blocks, and 0.87 megabits per second when realistic finite data sizes are taken into account. They also study in detail how imperfections like timing mismatch and increased user count affect performance, and show that with appropriate cyclic prefix design their scheme can tolerate practical network variations while still approaching the Nyquist efficiency limit of roughly two symbols per hertz of bandwidth.
What this means for everyday security
In plain terms, this work shows how to turn a single fiber link into a highly efficient quantum "multi-lane highway" for secret keys, using digital signal processing techniques already common in classical telecom. By reaching the theoretical limit of how densely quantum symbols can be packed, and by showing a realistic multi-user experiment on a standard access network architecture, the authors provide a promising blueprint for scaling quantum-safe communication from isolated demonstrations to large, commercially viable networks. If future quantum networks adopt ideas like these, many homes and businesses could share unbreakable cryptographic keys over the same infrastructure that delivers their internet today.
Citation: Yuehan Xu, Xiaojuan Liao, Qijun Zhang, Peng Huang, Tao Wang, and Guihua Zeng, "OFDM-based quantum key distribution access network reaching Nyquist limits," Optica 12, 1668-1680 (2025). https://doi.org/10.1364/OPTICA.567089
Keywords: quantum key distribution, optical networks, OFDM, quantum cryptography, secure communication