Clear Sky Science · en
Hacking continuous-variable quantum key distribution using the photorefractive effect on proton-exchanged/annealed-proton-exchanged waveguide
Why this matters for secure communication
Every day, more of our private data travels through optical fibers: financial transactions, medical records, even government communications. Quantum key distribution (QKD) is often hailed as the future-proof way to protect these secrets, because it relies on the laws of physics rather than assumptions about computer power. This paper shows that even quantum systems can be quietly sabotaged—not by breaking the physics, but by nudging real-world hardware away from its ideal behavior using a faint beam of visible light.
How quantum keys are supposed to stay safe
In continuous-variable quantum key distribution, information is encoded in delicate properties of laser light and sent through optical fibers. Two users, customarily called Alice and Bob, share random keys by modulating the strength and phase of light pulses, then measuring them with sensitive detectors. The security proofs that guarantee eavesdroppers cannot learn the key all assume that Alice’s and Bob’s devices behave exactly as modeled—for example, that a "variable optical attenuator" really applies the intended amount of dimming to each outgoing pulse. If a real device deviates from this ideal model, a hidden side channel can appear, opening a back door for an attacker.
A subtle way to push hardware off course
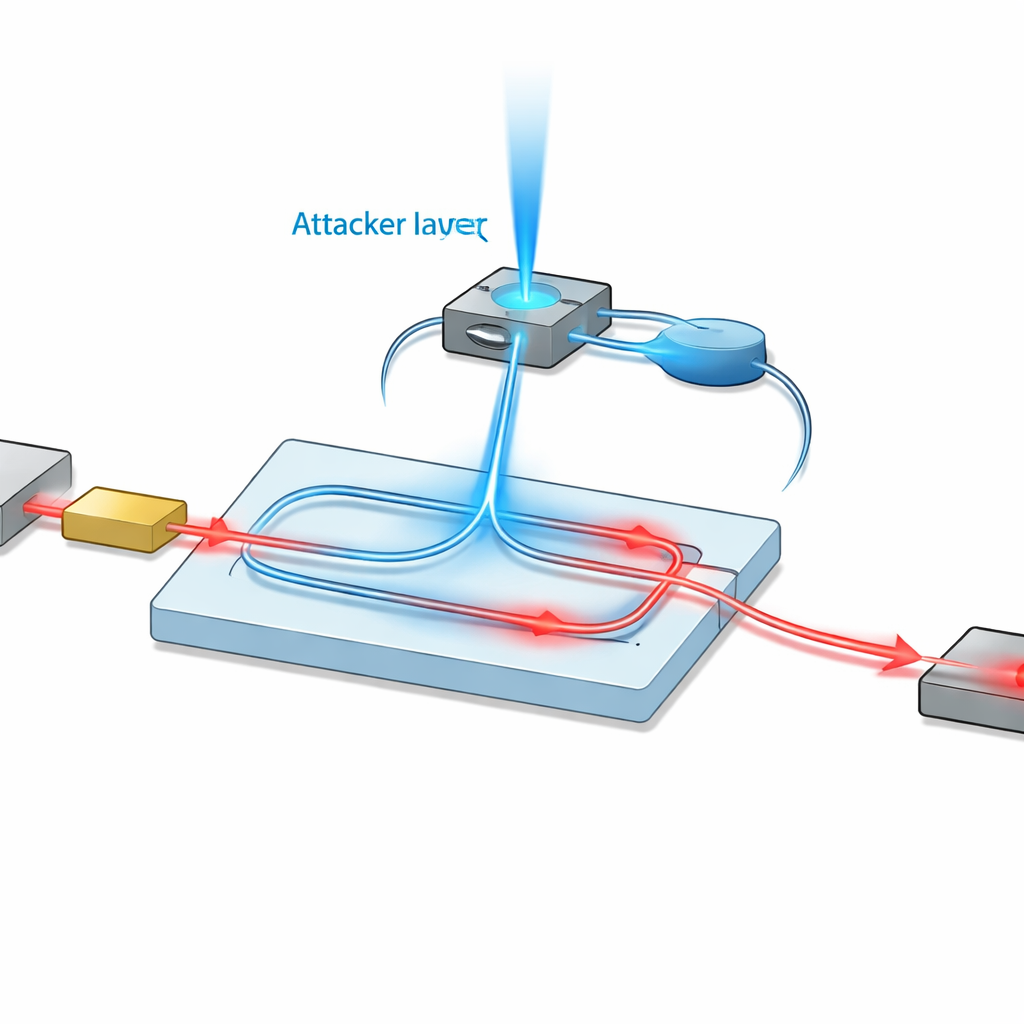
Many components in modern quantum communication systems are made from lithium niobate, a crystal prized for its ability to shape and modulate light on a chip. Lithium niobate has a lesser-known side effect: when illuminated, its internal structure can rearrange in a way that slightly changes how it bends light, a phenomenon called the photorefractive effect. The authors examine what happens when an eavesdropper, Eve, injects a very weak 488-nanometer visible beam into Alice’s lithium-niobate-based attenuator. That extra light induces small but lasting changes in the crystal’s refractive index, which in turn alters the phase balance inside a tiny interferometer that actually performs the attenuation. The net result is that the device quietly stops dimming the signal as much as Alice believes.
From tiny changes to exploitable loopholes
The study models this effect in detail for two common lithium niobate waveguide technologies, known as proton-exchanged and annealed-proton-exchanged. By relating the injected light power to the crystal’s index change and then to the interferometer’s output intensity, the authors show how even low irradiation—on the order of a few watts per square centimeter, corresponding to sub-microwatt total power—can noticeably reduce attenuation. Crucially, Alice and Bob typically infer how much noise and loss are in the communication channel by comparing a subset of their data to a theoretical model. When the attenuator has been altered, their statistics shift in a way that looks like a cleaner, less noisy channel: they overestimate the fiber’s quality and underestimate the disturbance, leading them to believe they can safely extract more key bits than they really can, without ever seeing an obvious anomaly.
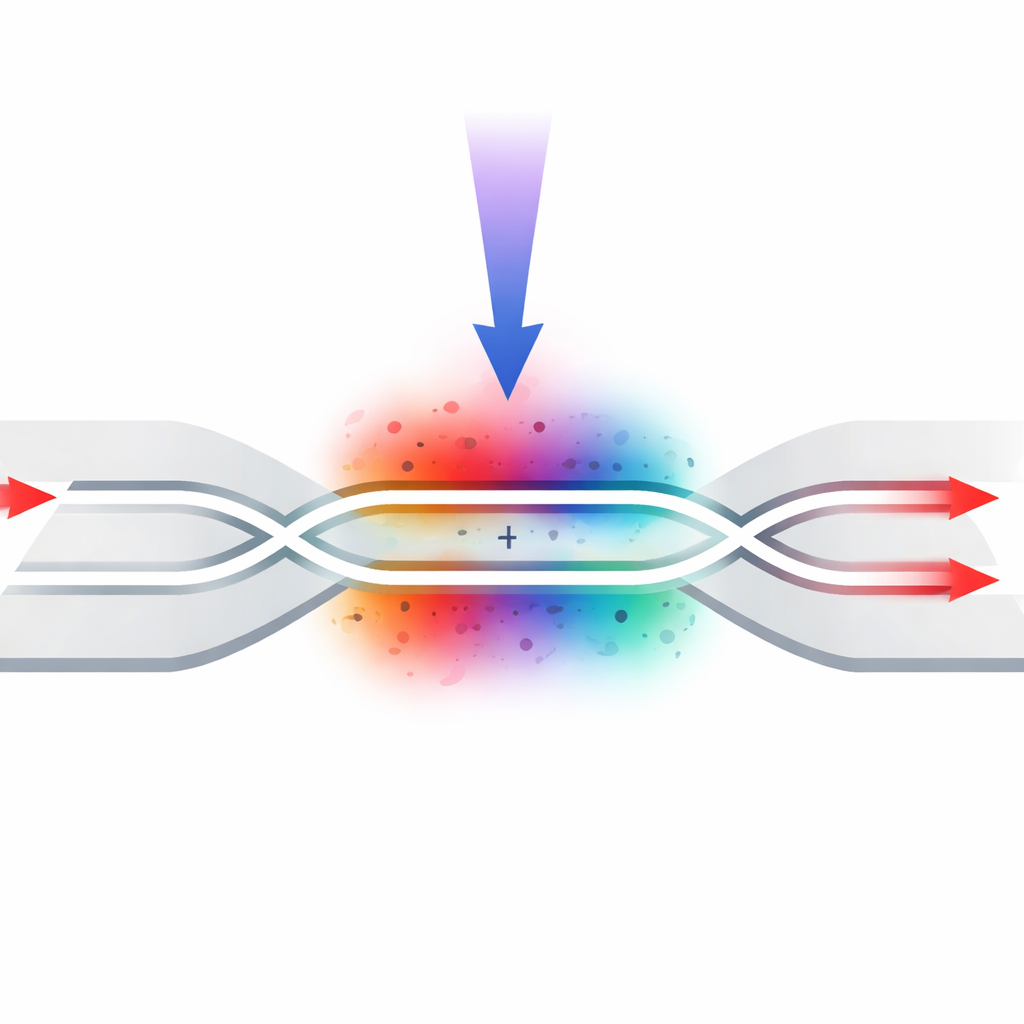
Attacking advanced "device-independent" style protocols
The work goes beyond basic one-way quantum key distribution and analyzes continuous-variable measurement-device-independent (CV-MDI) schemes, which are designed specifically to close all loopholes on the detector side by placing the most vulnerable measurements at an untrusted relay. That leaves the source devices as the last major weak point. The authors show that the same light-induced changes in lithium niobate attenuators on the users’ sides can undermine CV-MDI security as well. Depending on how the classical error-correction step is arranged—whether Alice’s or Bob’s data are used as the reference—Eve gains more by attacking one user, the other, or both. Simulations reveal that with only modest injected power, she can create a large discrepancy between the “apparent” secure key rate the users compute and the much smaller rate that is actually safe.
Possible defenses and their limits
Recognizing that completely redesigning hardware is difficult, the authors discuss practical countermeasures. Filters and wavelength-selective components can reduce unwanted light, but the photorefractive effect spans a broad range of colors, and commercial filters or dense wavelength-division multiplexers may not provide enough suppression. Optical isolators can be weakened under strong illumination or magnetic fields, and even improved power-limiting devices may still pass more light than this attack requires. A more promising approach is active monitoring: tapping a small fraction of the attenuated signal with an extra photodiode and continually checking whether its intensity matches the expected value. If it does not, Alice can correct her data or halt the protocol, closing the loophole created by the induced changes in her device.
What the study ultimately shows
In plain terms, this research demonstrates that quantum security can fail not because quantum theory is wrong, but because real components made from lithium niobate are subtly sensitive to stray light. By exploiting this sensitivity, an attacker can tilt the behavior of critical chips just enough to fool standard security checks, even while using extremely low light levels that are hard to detect. The findings underscore that building truly secure quantum networks requires not only sound protocols and proofs, but also a deep understanding of the materials and devices those proofs rely on—and may inspire more robust designs and monitoring strategies for future quantum communication infrastructure.
Citation: Mao, N., Zhang, H., Zuo, Z. et al. Hacking continuous-variable quantum key distribution using the photorefractive effect on proton-exchanged/annealed-proton-exchanged waveguide. Sci Rep 16, 8934 (2026). https://doi.org/10.1038/s41598-026-42620-x
Keywords: quantum key distribution, side-channel attack, lithium niobate, photorefractive effect, continuous-variable cryptography