Clear Sky Science · en
Secure authentication using a multidimensional retinal biometric encryption method
Why Your Eyes Could Be the Next Password
Most of us juggle too many passwords, and even strong ones can be stolen or guessed. This study explores a different path: using the unique pattern of blood vessels at the back of your eye—the retina—to help lock and unlock digital information. Instead of replacing proven encryption tools like AES, the authors show how a single retinal image can power three separate digital keys at once, making it much harder for an attacker to guess their way in. 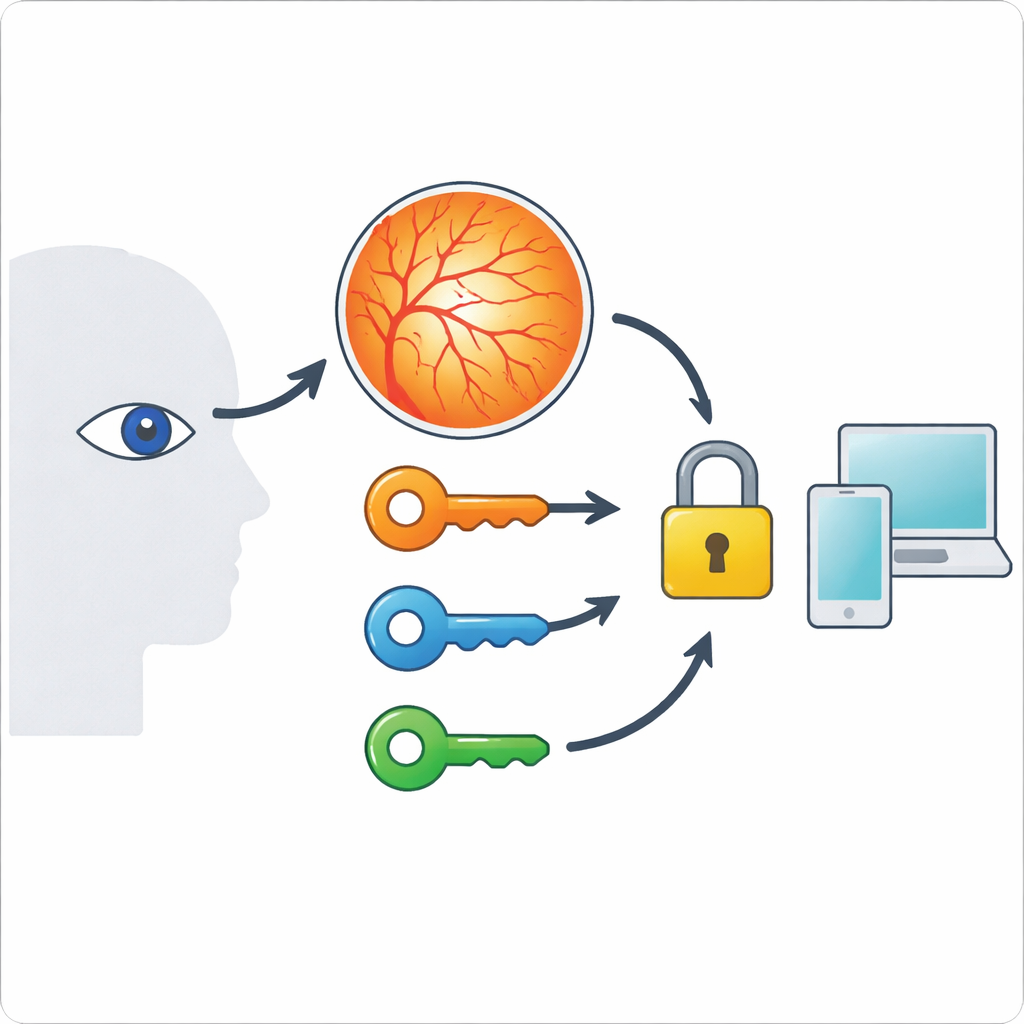
The Hidden Map Inside the Eye
The retina sits at the back of the eyeball and is crisscrossed by a delicate web of blood vessels. That web is effectively impossible to see from the outside, tends to remain stable over many years, and is different for every person. These traits make it attractive for secure identification. Earlier systems that used retinal images typically squeezed just one digital key out of this vessel map, limiting how many possible keys existed and how resistant the system was to brute-force guessing. The new work asks a simple question: if the retina is such a rich pattern, why stop at one key?
From Vessels to Digital Keys
To answer this, the authors first run each retinal photo through a careful cleaning and tracing pipeline. They enhance contrast, isolate the green color channel where vessels stand out most, remove bright structures that could confuse the process, and then turn the vessels into thin skeleton lines. The tips of these lines—called endpoints—act like landmarks. By measuring how far these endpoints are from different reference points, the system generates three separate sets of numbers. Each set forms one of three keys: one based on diagonal distances between vessel points, one based on distances from the center of the retina outward, and one based on the difference between those two. Because these measurements are grounded in real anatomy, they are consistent for the same person but sharply different from person to person. 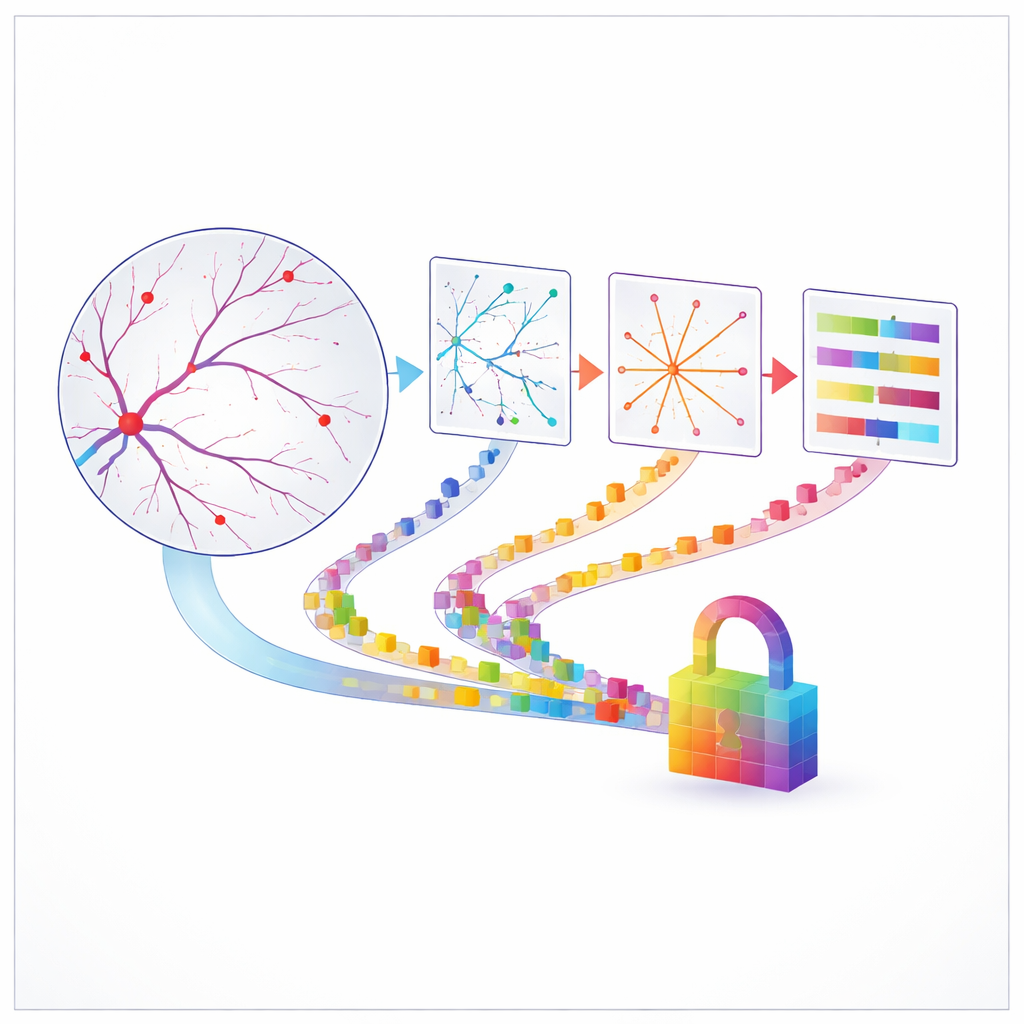
Turning the Eye’s Geometry into Encryption
Once these three numerical keys are extracted, they are scaled into ranges suitable for encryption and combined into shifting patterns that scramble text, a bit like a modern take on classic polyalphabetic ciphers. The authors spell out the exact math used to convert characters into numbers, mix in key values and pixel coordinates, and then convert back to symbols, always staying within a fixed symbol set of 124 possibilities. They also design the system so that any of the three keys can be used on its own, or together, to strengthen a password or help generate short-lived session keys during login. Crucially, the threat model is modest and clear: the method is meant to harden authentication in controlled settings where attackers do not have access to the user’s retinal scan, not to withstand the most advanced nation-state attacks.
Does It Actually Look Random?
To test whether these retinal keys are truly hard to predict, the team runs a battery of checks often used in cryptography. They measure the entropy, or unpredictability, of each key stream and find values close to the theoretical maximum. They then subject the keys to a standard U.S. government randomness test suite and show that most tests are passed comfortably, especially for keys based on diagonal distances and the diagonal–radial combination. They also estimate how long a powerful computer guessing a trillion keys per second would need to try every possible key: for the richest retinal sample, the answer is a staggeringly large number of years. Additional experiments show that keys generated from slightly noisy or blurred versions of the same eye stay similar, while keys from different people differ sharply and never collide when hashed, confirming both stability and distinctiveness.
Where This Approach Fits—and Its Limits
The authors are careful to stress what their system is and is not. It is a way to turn the fine-grained geometry of the retina into multiple, high-quality keys that can support login and identity checks, making stolen passwords or leaked databases less dangerous. It is not meant to replace industrial-strength encryption standards or to defend against attackers who can spoof an eye or eavesdrop on the hardware itself. The method also depends on good-quality images and accurate tracing of tiny vessels; poor scans or very sparse vessel networks could weaken the keys. Even so, the results suggest that the quiet map inside your eye could be a powerful ally in keeping your digital life secure, especially when combined with other safeguards such as liveness checks and established encryption algorithms.
Citation: Banu, Y., Rath, B.K. & Gountia, D. Secure authentication using a multidimensional retinal biometric encryption method. Sci Rep 16, 9205 (2026). https://doi.org/10.1038/s41598-026-40962-0
Keywords: retinal biometrics, biometric encryption, secure authentication, cryptographic keys, randomness testing