Clear Sky Science · en
Federated learning-powered real-time behavioral intrusion detection leveraging LSTM, attention, GANs, and large language models
Why Smarter Cyber Defense Matters to Everyone
Every email you send, photo you share, or bill you pay online travels through networks that are constantly under attack. Traditional security tools struggle to spot new, rare, or cleverly hidden intrusions without invading user privacy or flooding analysts with confusing alerts. This paper introduces a new way to watch over digital traffic that aims to be both highly accurate and deeply respectful of privacy, while also explaining its decisions in language people can understand.
Watching Attacks Without Collecting Your Data
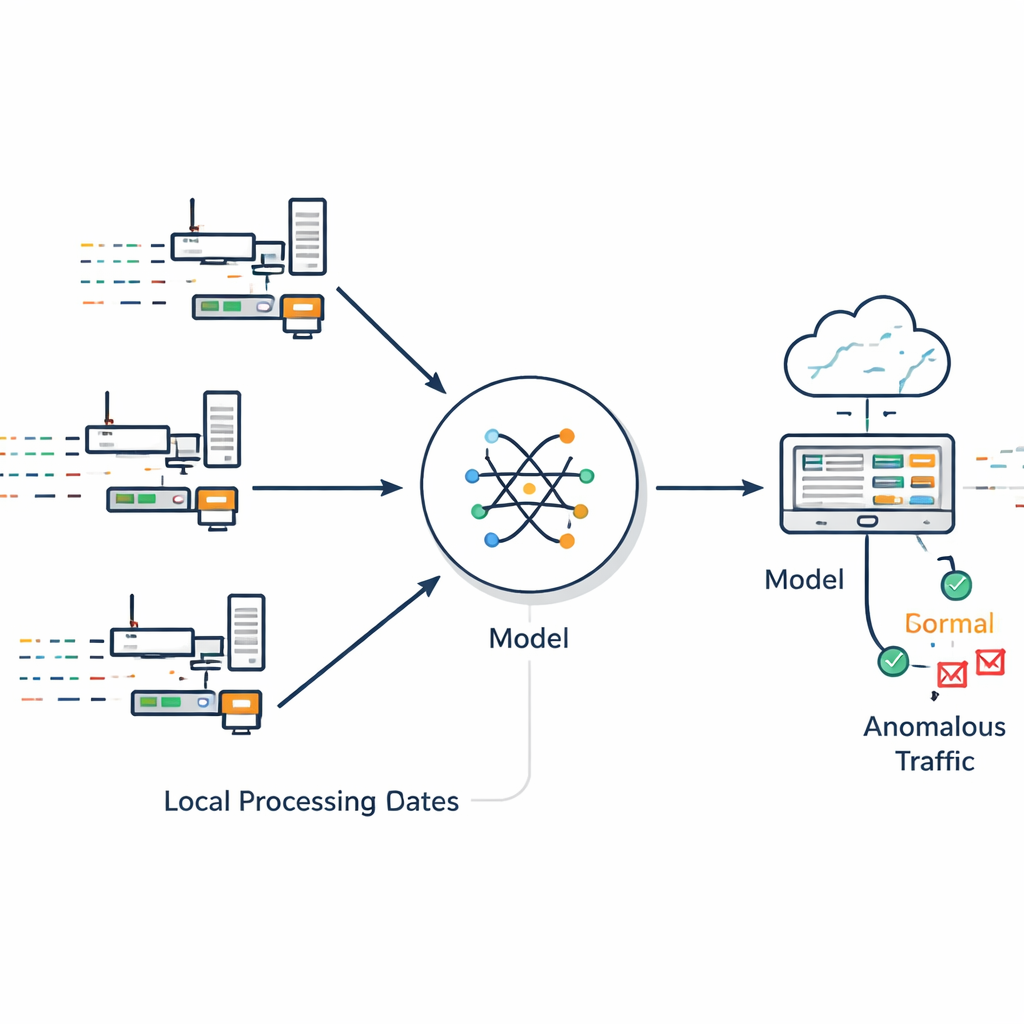
Most intrusion detection systems work like a central checkpoint: they pull raw data from many devices into one place and scan it for trouble. That raises obvious privacy worries and becomes harder to scale as networks grow. The authors propose a different approach called the Federated Intrusion Detection and Mitigation Framework, or FIDMF. Instead of shipping raw traffic logs to a central server, each participating device or site trains a local detection model on its own data. Only the learned model updates are shared and blended into a global model, which is then sent back to the devices. In this way, the system learns from a broad range of real‑world environments without ever exposing the underlying private data.
Learning from Behavior Over Time
Attacks often unfold as sequences: a scan, then a probe, then a break‑in, sometimes stretched over many moments. FIDMF focuses on these behavioral patterns rather than on simple signatures. It uses a sequence‑aware neural network that can remember what happened earlier in a connection and an “attention” component that highlights the most important parts of a traffic stream. This helps the system focus on features that truly signal suspicious behavior, such as sudden bursts of connection attempts or unusual combinations of protocols, instead of being distracted by routine variations in normal use.

Filling in the Gaps with Synthetic and Semantic Insight
Real networks include far more ordinary activity than attacks, and some types of attacks are extremely rare. Training a detector on such lopsided data usually leads it to miss unusual threats. FIDMF tackles this in two ways. First, it uses mathematical techniques to generate extra examples of rare attack types so the model can learn their patterns better. Second, it employs generative models guided by language‑based context to invent new, realistic attack variations that match how experts describe threats. This dual strategy gives the detector many more meaningful examples to learn from, making it better prepared to spot unfamiliar or “zero‑day” intrusions that differ from anything seen before.
Teaching Machines to Understand Network Stories
A key innovation in this work is bringing text‑oriented language models into the world of network defense. Many network features—like service names, protocol types, and connection states—carry subtle meanings that simple numerical codes cannot capture. The authors convert these categorical details into short phrases and feed them into compact language models that produce rich, context‑aware representations. These representations help the detector grasp relationships that would otherwise be invisible, such as how certain services and flags tend to appear together in risky situations. The same language technology also guides the synthetic data generator, ensuring that invented attack patterns remain coherent and realistic rather than random noise.
Clear Explanations for Human Analysts
Security teams are understandably wary of “black‑box” tools that raise alarms without saying why. FIDMF addresses this by pairing its behavior‑based detector with another language model that specializes in explanation. After the system flags an event as suspicious, it pulls out the features that contributed most to the decision—such as a burst of short connections or unusual protocol use—and turns them into a short, readable narrative. In tests with expert reviewers, these explanations were rated both understandable and useful for incident response, helping analysts trust and act on the system’s findings.
What the Results Mean for Everyday Security
Across several widely used benchmark datasets, FIDMF reached very high accuracy, correctly identifying both normal and malicious traffic in more than 99 out of 100 cases while leaving raw data on local devices. Just as important, it handled rare attack types far better than earlier methods and maintained strong performance on different kinds of networks. For everyday users, the takeaway is that it is becoming possible to build defenses that are not only stronger and more adaptable, but also more private and more transparent. Frameworks like FIDMF point toward a future where your devices quietly collaborate to keep you safe online—without surrendering your data or leaving you in the dark about how decisions are made.
Citation: AlHayan, A., Al-Muhtadi, J. Federated learning-powered real-time behavioral intrusion detection leveraging LSTM, attention, GANs, and large language models. Sci Rep 16, 10172 (2026). https://doi.org/10.1038/s41598-026-40763-5
Keywords: intrusion detection, federated learning, cybersecurity, deep learning, large language models