Clear Sky Science · en
An end-to-end convolutional neural network for secure image transmission via joint encryption and steganography
Why hiding pictures inside pictures matters
Every day, hospitals, banks, and ordinary people send vast numbers of photos across the internet—from medical scans to ID cards to family snapshots. Keeping these images private usually means scrambling them with encryption, which makes them look like random static, or hiding them inside other pictures, a trick called steganography. Each approach has a weakness: scrambled images draw attention, and hidden images can be exposed by clever analysis. This paper introduces a new deep‑learning system that blends both ideas, aiming to send secret images in a way that looks natural to human eyes yet remains hard for attackers to crack.
The problem with today’s protection tricks
Traditional encryption tools such as AES and DES are mathematically strong, but they turn a photo into a block of visual noise that clearly signals, “something important is hidden here.” Classic steganography does the opposite: it tucks information into the fine details of a normal‑looking picture, but often without strong cryptographic protection. If an attacker detects the trick, the hidden message may be easy to pull out. Recent deep‑learning methods improved either encryption or hiding, yet most treat them as two separate steps. That separation wastes computing effort and can let errors from one stage damage the other. The authors argue that what is missing is a single system that learns, end‑to‑end, how to both disguise and protect images at the same time.
A single brain that scrambles and hides
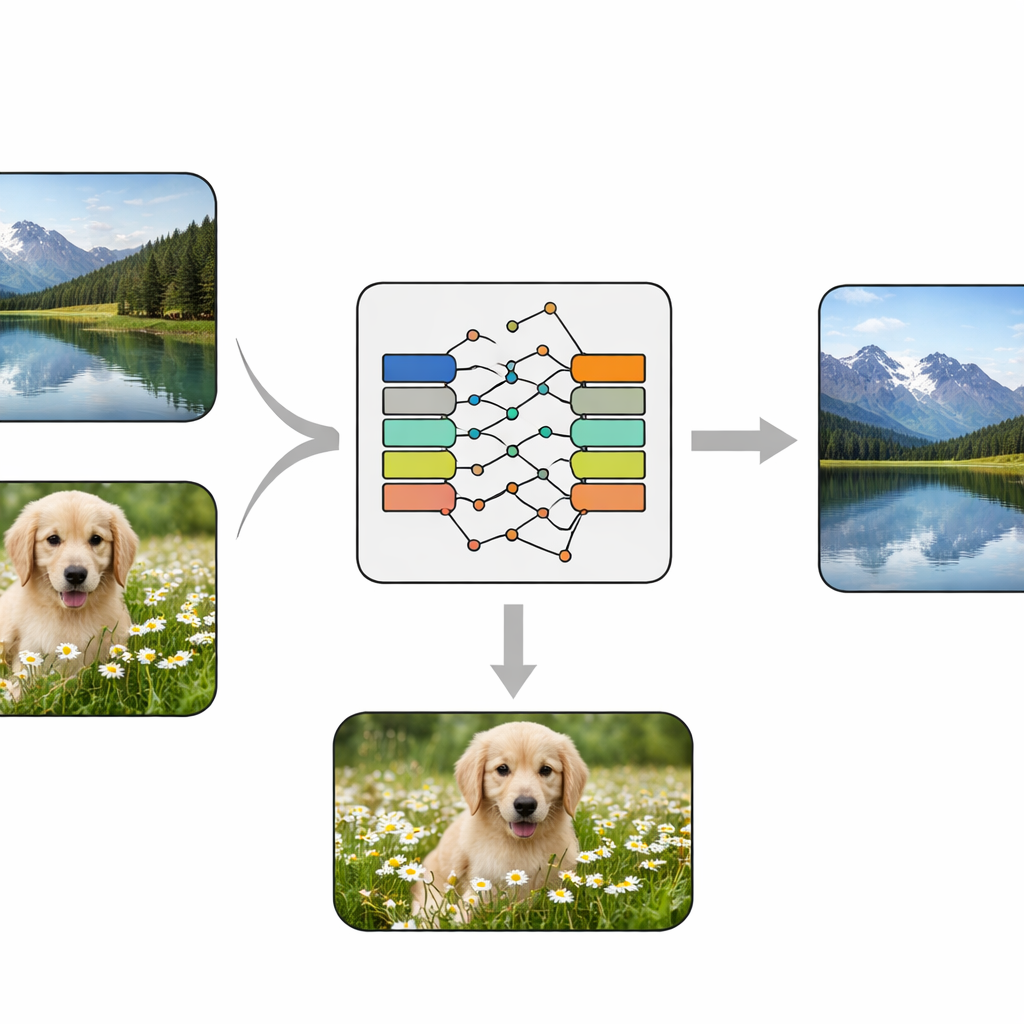
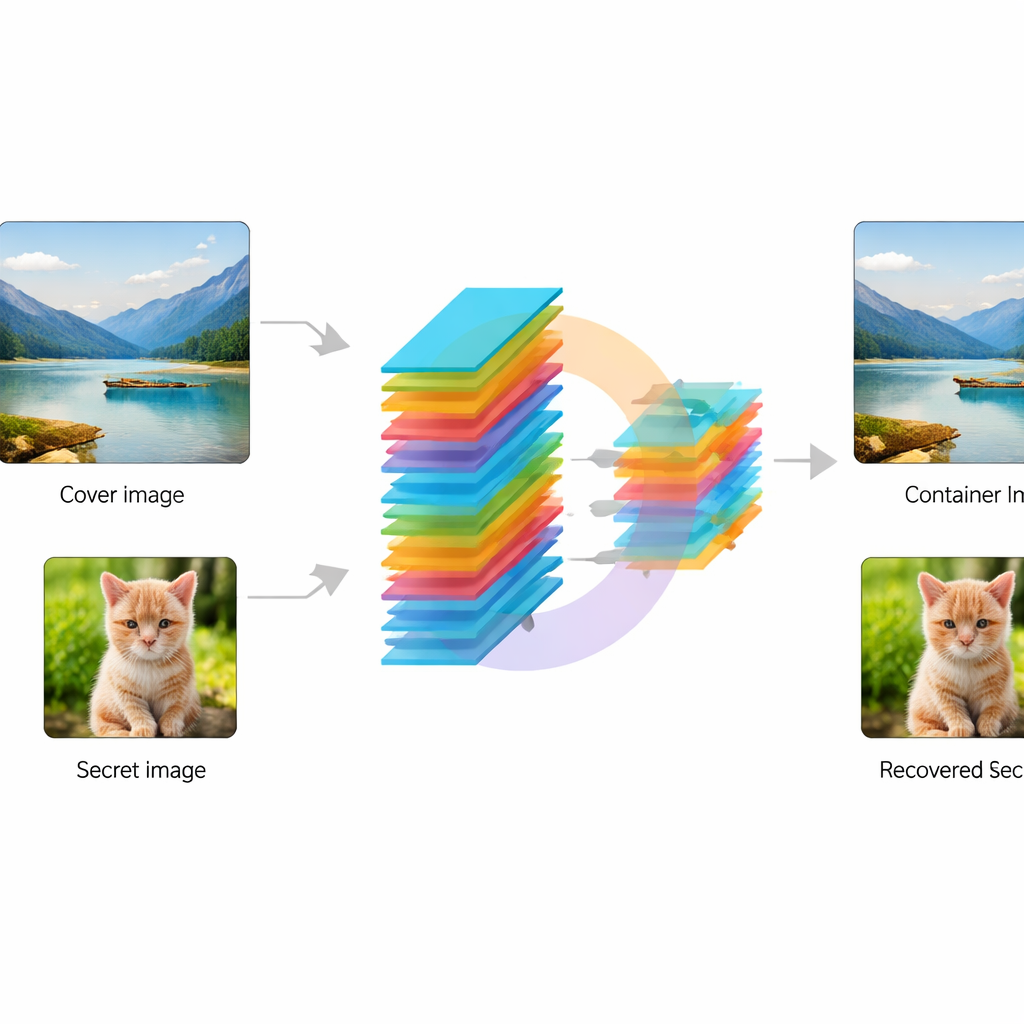
The researchers design an end‑to‑end convolutional neural network—essentially a trainable image‑processing pipeline—that takes in two images: a normal “cover” photo and a “secret” photo to be protected. First, a special module called the KeyMixer transforms the secret image using trainable numerical keys. Unlike fixed, hand‑designed ciphers, this mixer learns content‑aware changes that depend on textures and shapes in the image, introducing subtle, non‑obvious distortions. Next, an Encoder network softly blends this transformed secret into the cover image, creating a “container” picture that should still look natural. On the receiving side, a matching Decoder network takes only the container image and reconstructs the hidden secret, without needing extra keys or side information during recovery.
Teaching the network to balance secrecy and appearance
Training this system means asking it to achieve two goals at once: keep the container image visually close to the original cover, and recover the secret image as accurately as possible. The authors do this with a dual‑loss strategy that penalizes both visible changes to the cover and errors in the reconstructed secret. They use a popular benchmark collection of natural photos, the STL‑10 dataset, and apply standard data‑augmentation tricks such as flips and small rotations so the network sees varied scenes. During training, the model steadily improves until both objectives stabilize, showing that it can find a workable middle ground between invisibility and faithful recovery.
How well the hidden images survive
To judge quality, the team measures how similar the container images are to the covers, and how closely the recovered secrets match the originals, using standard image‑quality scores. On the test images, the method achieves high structural similarity for both cover and secret, with values above 0.90, meaning that shapes and details are largely preserved. Secret images in particular reach very high similarity, indicating nearly perfect perceptual recovery. When compared to several modern deep‑learning steganography systems and hybrid pipelines, the new end‑to‑end model delivers the best secret‑image reconstruction, even if some rivals slightly better preserve the cover. Statistical tests of pixel distributions, randomness, and sensitivity to changes suggest that the containers do not reveal obvious clues that something is hidden.
What this could mean for everyday privacy
In plain terms, this work shows that a single deep‑learning model can learn to both disguise and protect images so that a hidden picture can be recovered with high clarity, while the shared picture still looks ordinary. Rather than bolting encryption and steganography together in a clumsy chain, the system learns a smooth compromise between visual subtlety and security. Although it currently requires powerful hardware and further testing against advanced attacks, the approach points toward future tools that could quietly secure medical scans, personal photos, or other sensitive images in routine online communication without announcing that anything secret is there at all.
Citation: Iqbal, A., Sattar, H., Shafi, U.F. et al. An end-to-end convolutional neural network for secure image transmission via joint encryption and steganography. Sci Rep 16, 8228 (2026). https://doi.org/10.1038/s41598-026-39351-4
Keywords: image security, steganography, deep learning, neural encryption, privacy protection