Clear Sky Science · en
A robust zero-watermarking and signcryption scheme for image copyright protection and license verification
Why protecting pictures without changing them matters
Modern medicine and online media both rely on images that must stay perfectly faithful to reality. Radiology scans guide life-or-death decisions, and high‑quality photos and graphics underpin creative work and business. Yet these images are copied, edited, and shared across networks where ownership can be disputed and licenses are easily abused. Traditional watermarking hides a mark inside an image by slightly altering its pixels, which is often unacceptable for medical use and still vulnerable to heavy editing. This paper introduces a way to prove who owns an image and who is allowed to use it—without changing a single pixel—while remaining resilient even when the image is rotated, cropped, compressed, or otherwise attacked.

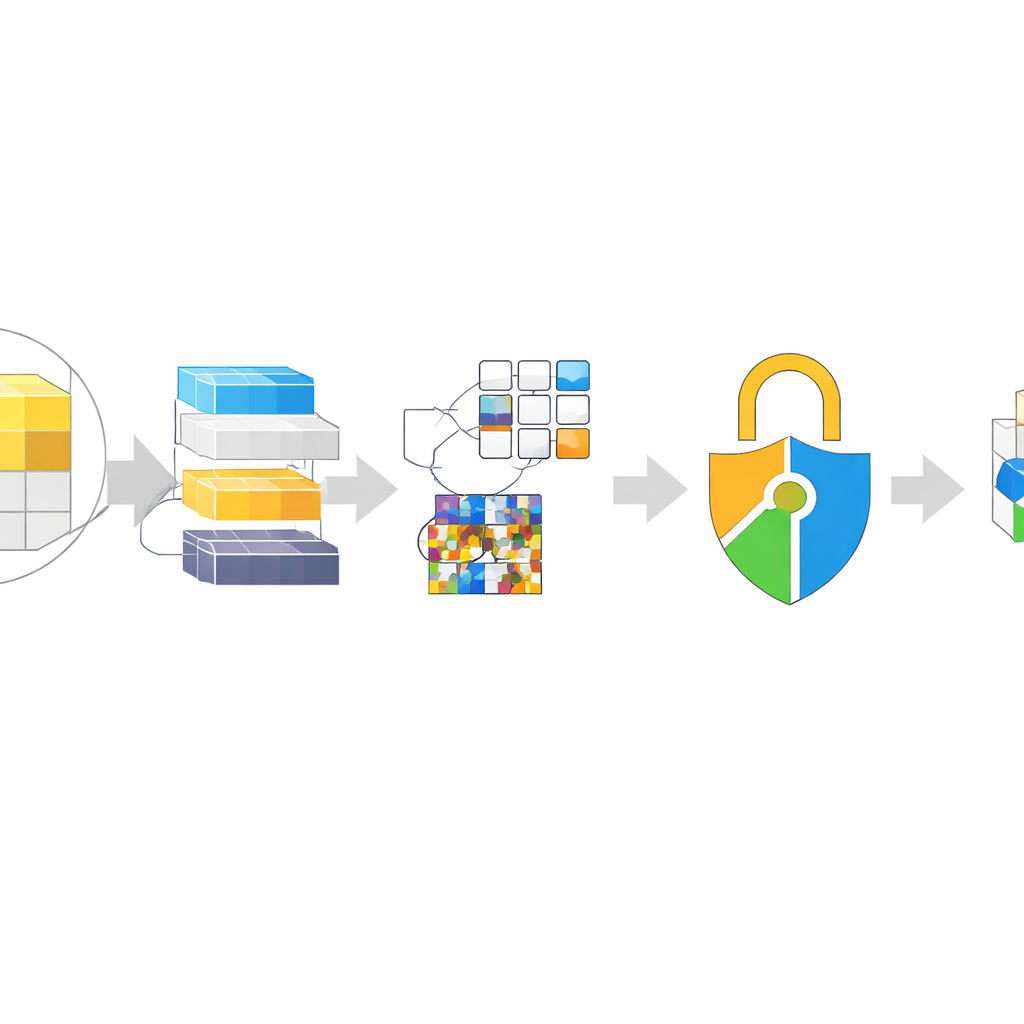
How to claim ownership without touching the image
The core idea is called zero‑watermarking. Instead of injecting a mark into the image itself, the system studies the image and builds a kind of fingerprint from its most stable details. These fingerprints are then mathematically combined with a secret logo that represents the owner. The combined result is stored in a separate database managed by a certification authority, not inside the image. When a dispute arises, the authority can recompute the fingerprint from the suspect image and compare it to the stored record. If they match, ownership is confirmed, yet the original image that doctors, artists, or companies rely on has never been altered.
Picking the most informative parts of an image
A major challenge is making sure the fingerprint survives real‑world changes such as rotation, resizing, or noise. The authors address this by carefully choosing which parts of the image to rely on. First, an algorithm hunts for visually distinctive points—tiny corners, edges, or patterns that tend to be found again even if the image is zoomed or rotated. Around each such point, a small patch is examined and its “information richness” is measured. Only the patches with the most complex structure are kept. From these selected zones, a two‑stage frequency analysis distills a compact pattern that acts like a robust ID card for that sub‑region. Many such local ID cards are produced across the image, so even if some areas are cropped or blurred, enough survive to reconstruct the owner’s logo.
Locking the watermark with modern cryptography
Storing these zero‑watermark codes in a central database creates another risk: if an attacker accesses the database, they might try to forge or reverse‑engineer ownership records. To counter this, the authors wrap each local code in a combined encryption‑and‑signature procedure known as signcryption. Here, the feature pattern and scrambled logo are fused and then locked using a public‑key method related to ElGamal encryption. Each stored record is tied not only to the image but also to the keys of the owner and, when a license is issued, to the keys of the authorized user. Even if the database is compromised, the attacker cannot read the underlying watermark or convincingly alter who owns or may use an image without breaking strong cryptographic protections.
Standing up to real‑world image attacks
The researchers tested their scheme on a collection of medical scans and standard color photos, subjecting them to many common transformations: adding noise, compressing with JPEG, blurring with filters, rotating by large angles, resizing, shifting, and cropping. For each attacked image, they attempted to recover the logo and measured how closely it matched the original. Across most geometric and everyday processing changes, the similarity remained almost perfect, clearly outperforming a recent state‑of‑the‑art method. The extra cryptographic layer added only a few thousandths of a second per image—tiny compared with the time needed for the image analysis itself—suggesting that the method is practical for hospital systems and large copyright platforms.
What this means for everyday image use
In plain terms, the article shows that it is possible to prove who owns an image and who is allowed to use it without ever changing the image, and to keep that proof strong even when the picture is heavily edited. By combining smart selection of the most informative image regions with a robust mathematical fingerprint and a tightly integrated encryption‑plus‑signature step, the scheme offers both technical robustness and legal‑grade trust. While there is still room to improve its resistance to extreme noise and to speed up verification for massive image collections, this approach points toward future systems where medical scans and valuable media can circulate freely while their origins and usage rights remain securely anchored.
Citation: Hung, P.T., Thanh, T.M. A robust zero-watermarking and signcryption scheme for image copyright protection and license verification. Sci Rep 16, 9103 (2026). https://doi.org/10.1038/s41598-026-38991-w
Keywords: image copyright, medical imaging security, digital watermarking, zero watermarking, signcryption