Clear Sky Science · en
Explainable attention based few shot LSTM for intrusion detection in imbalanced cyber physical system networks
Why smarter defenses matter for connected machines
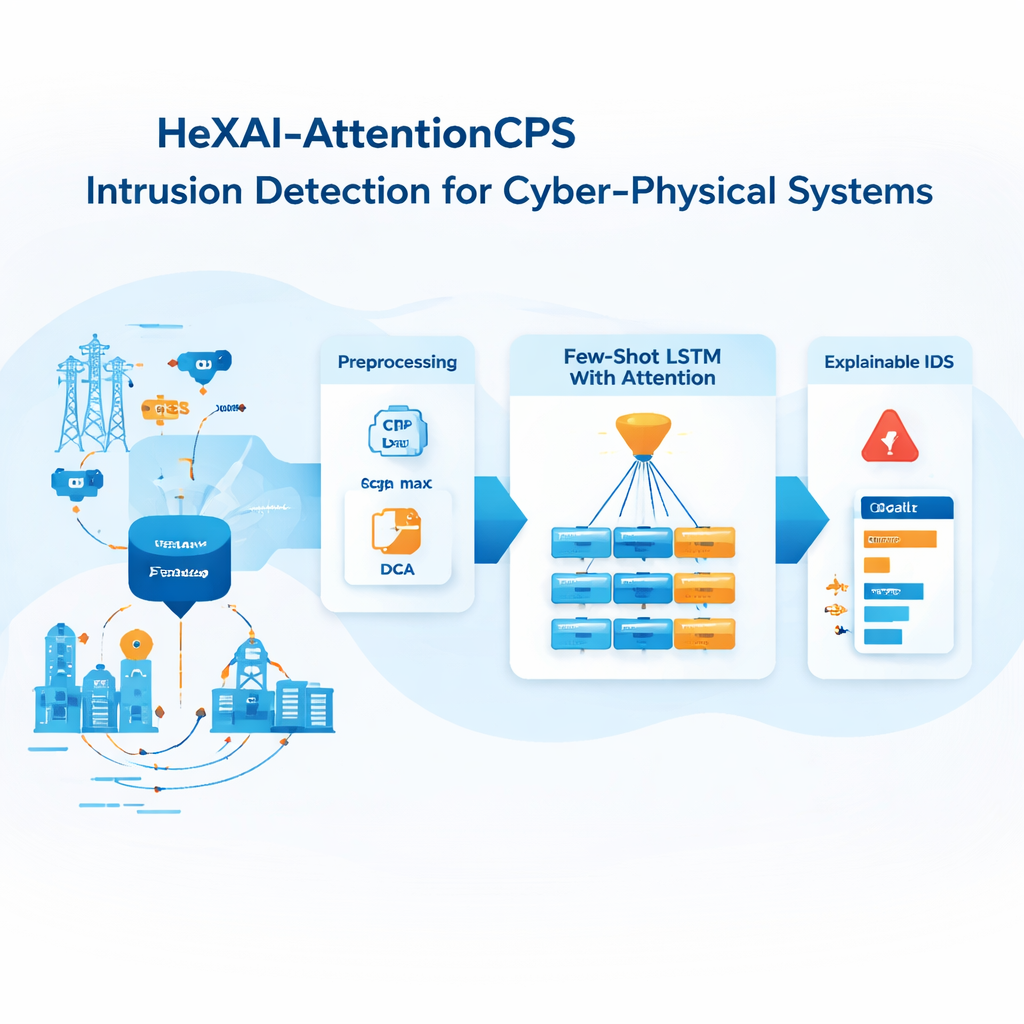
From power grids and water plants to factory robots and hospital devices, our physical world increasingly runs on networked machines known as cyber-physical systems. A single hidden break-in on these networks can shut down services, damage equipment, or even endanger lives. Yet many security tools still miss rare but dangerous attacks or flood operators with false alarms they cannot interpret. This study introduces a new intrusion detection approach, HeXAI-AttentionCPS, designed to spot both common and rare threats in these critical networks while also explaining to humans why an alert was raised.
Hidden dangers in digital traffic
Cyber-physical systems constantly exchange vast amounts of data, most of which is routine. Attack traffic is like a few odd-colored threads woven into a huge fabric. Traditional intrusion detection systems tend to focus on the most common patterns they see. As a result, they become very good at recognizing frequent events but overlook rare and emerging attacks, such as sophisticated man-in-the-middle schemes. When researchers try to fix this by artificially multiplying rare attacks in the data, they often introduce noise, making models less stable and slower, and still not fully reliable on new types of threats.
A learning system that focuses on the rare and important
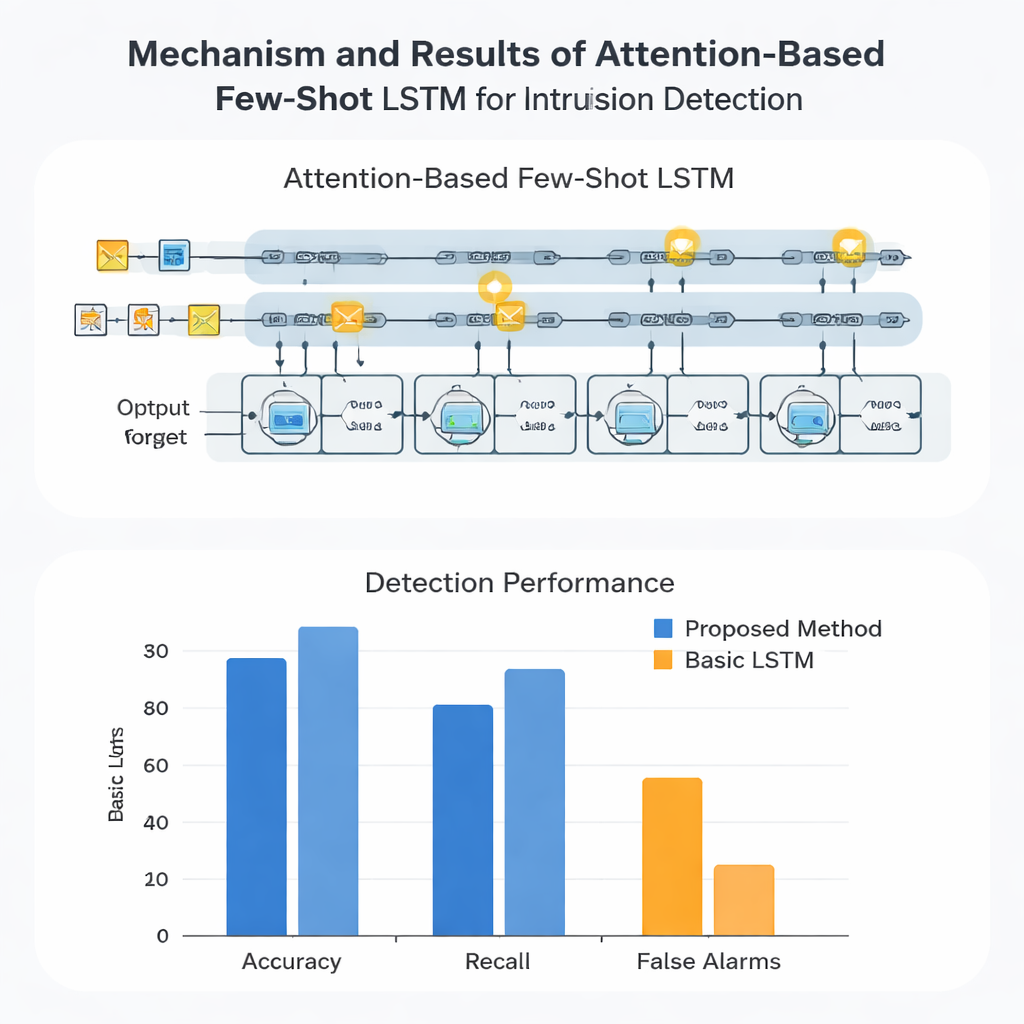
The proposed HeXAI-AttentionCPS framework tackles these issues by changing both how the system learns and what it pays attention to in network traffic. First, it uses a sequence model called an LSTM to read data over time, much like how we understand meaning from a sentence rather than from isolated words. On top of this, an attention mechanism acts like a spotlight, highlighting the most telling moments in the traffic sequence instead of treating every data point as equally important. The model is trained in a "few-shot" fashion: during training it repeatedly practices recognizing attack types from only a handful of examples, mirroring real situations where only a few labeled samples of a new attack are available.
Balancing the scales without faking the data
Instead of generating synthetic attacks to fix imbalance, the system uses a special loss function called focal loss that deliberately emphasizes mistakes on rare classes while downplaying already easy decisions on common traffic. This nudges learning toward the hard-to-detect attacks without distorting the dataset itself. Before learning, the data are also compressed with a mathematical lens called Principal Component Analysis, which keeps the most informative patterns while discarding redundancy. This combination reduces computational load and helps the attention mechanism concentrate on truly meaningful variations in the traffic, improving both speed and accuracy.
Turning black-box alerts into understandable clues
A major barrier to trusting automated defenses is that many behave like black boxes, issuing alerts with no explanation. HeXAI-AttentionCPS integrates an explanation method known as SHAP, which breaks down each prediction into contributions from individual features such as source and destination ports, IP addresses, traffic duration, and connection state. For an operator, this means that when the system flags a man-in-the-middle attack, it can also show which ports, IP patterns, or timing behaviors pushed the decision toward "malicious." Over many alerts, this view reveals which aspects of the network are consistently involved in attacks, offering guidance for hardening the system.
What the results mean in practice
The authors tested their framework on a realistic benchmark dataset that mimics modern industrial networks with nine different attack types. Compared with several deep-learning baselines, HeXAI-AttentionCPS achieved very high accuracy and F1-scores while keeping false alarms extremely low, even for rare attacks that other systems often miss. For security teams, this means fewer missed serious intrusions and fewer distracting false alerts, plus clear insight into why the system reacts as it does. In simple terms, the study shows that it is possible to build a watchdog for critical infrastructures that is not only sharper-eyed about unusual threats, but also able to explain its reasoning in ways humans can act on.
Citation: Abdulganiyu, O.H., Fadi, O., Moukafih, Y. et al. Explainable attention based few shot LSTM for intrusion detection in imbalanced cyber physical system networks. Sci Rep 16, 7217 (2026). https://doi.org/10.1038/s41598-026-38668-4
Keywords: intrusion detection, cyber-physical systems, imbalanced data, explainable AI, few-shot learning