Clear Sky Science · en
A novel 1D powered Chebyshev quadratic map-based image encryption using dynamic permutation-diffusion
Why hiding pictures really matters
We send photos all the time—to doctors, banks, government portals, or cloud backups—often without thinking about who else might see them. But images of medical scans, military sites, or ID documents can be extremely sensitive. If someone can intercept or slightly alter them, the consequences can be serious. This paper presents a new way to scramble digital images so thoroughly that even determined attackers find it extraordinarily hard to guess, analyze, or tamper with what they contain.
A new way to stir up digital chaos
At the heart of the work is a new mathematical recipe the authors call the “1D‑Powered Chebyshev Quadratic Map.” Despite the intimidating name, it’s basically a compact formula that, when repeatedly applied, produces a stream of numbers that behave like chaos: tiny changes at the start grow into completely different outcomes later. Classic chaotic formulas are already used in encryption, but many have weaknesses: they only behave chaotically for narrow parameter ranges, can be predicted in some conditions, or do not react strongly enough to small changes. The new map is engineered to avoid these pitfalls by combining two well‑known chaotic ingredients in a powered, or amplified, way, controlled by just two tunable parameters.
Testing how wild the chaos really is
To be useful in security, chaos must be both strong and measurable. The researchers therefore put their new map through an extensive series of dynamical tests. They examined how fast nearby values diverge (Lyapunov exponent), how the system’s behavior changes as parameters are varied (bifurcation diagrams), and how complex its geometric patterns become (correlation dimension and Poincaré sections). They also applied modern chaos diagnostics such as the so‑called 0–1 test, along with several notions of entropy that quantify randomness. Across wide parameter ranges, the new map maintained large positive Lyapunov exponents, high entropy, and irregular, non‑repeating patterns, outperforming several established chaotic maps. Randomness tests used by standards bodies to vet cryptographic random‑number generators confirmed that the sequences produced by this map look statistically indistinguishable from ideal noise.
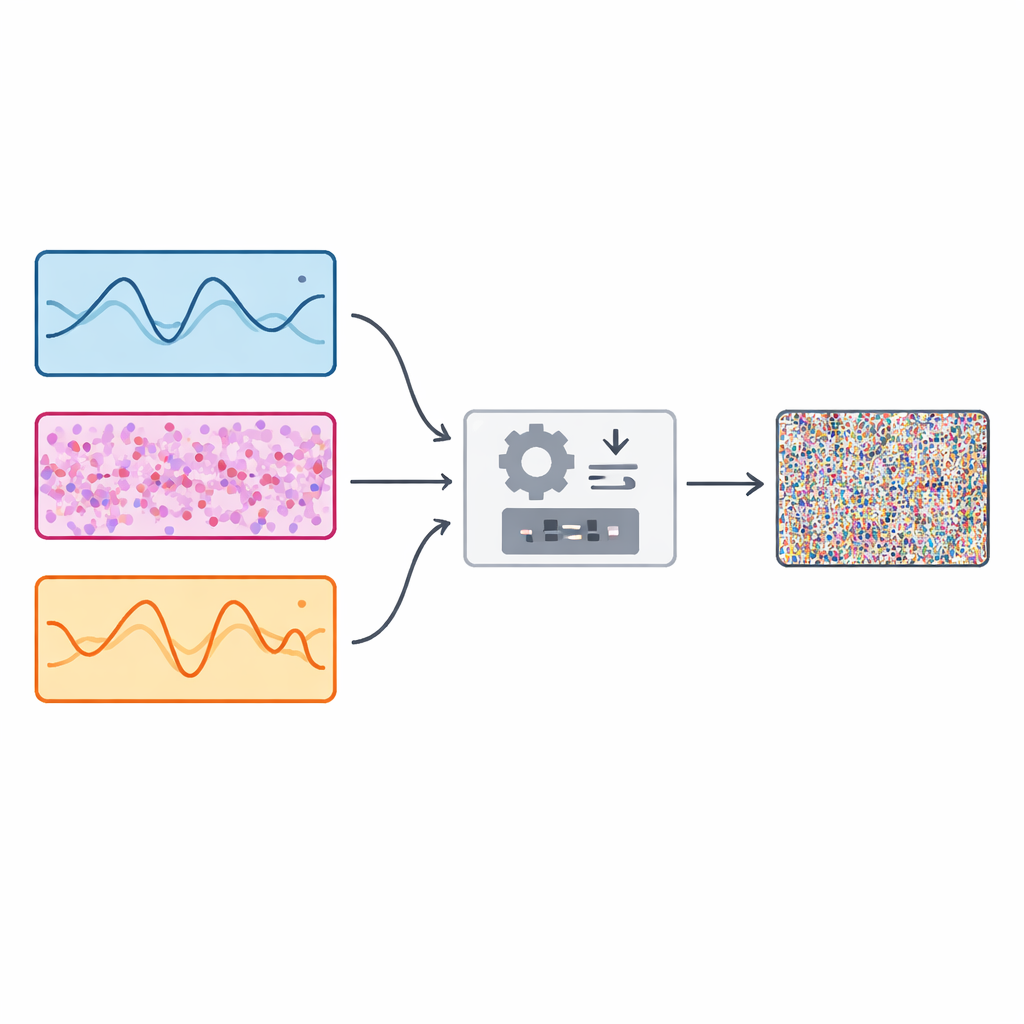
From equations to a practical image lock
Building on this chaotic engine, the authors design an image encryption scheme they call D3CM‑IES. Instead of relying on a single source of chaos, the system runs three different chaotic generators in parallel, including the new map and two existing ones based on sine and tangent functions. For every pixel in an image, the algorithm dynamically chooses one of these three chaotic sequences to guide the encryption steps. First, a permutation step shuffles pixels to new positions in a pattern that appears random but is exactly reproducible only if the secret key is known. Then a diffusion step alters the brightness of each pixel, using chaotic numbers to push values around almost as if noise had been added. Because the choice of chaotic source changes from pixel to pixel, the overall transformation is highly irregular and difficult to reverse without the exact key and parameters.
Putting the lock to the test
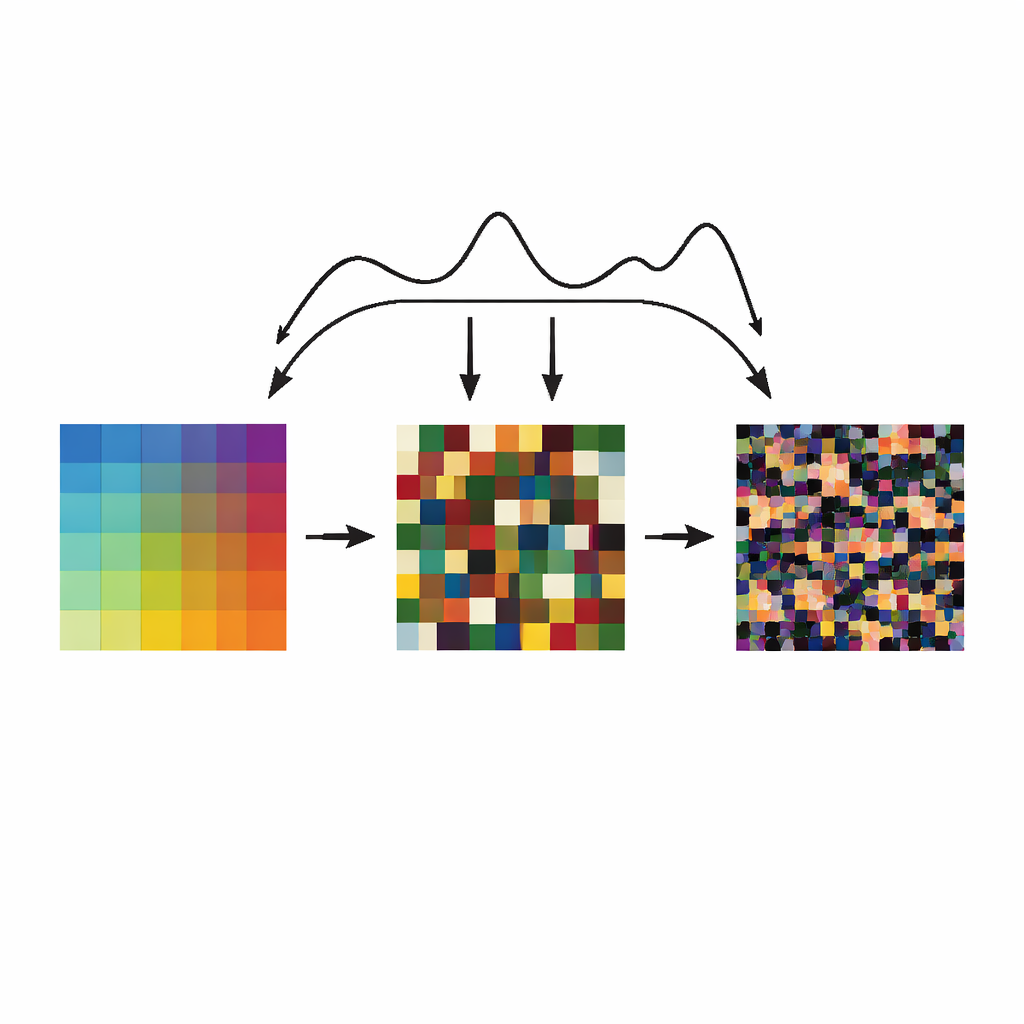
The team checks whether their scheme really hides structure by running a battery of security and image‑quality evaluations. When they encrypt standard test images, the resulting pictures resemble pure multicolored static, and statistical measures show almost no correlation between neighboring pixels. Histograms—the counts of how often each brightness level appears—flatten out, which means attackers cannot exploit visible patterns. When they change a single pixel in the original image, nearly every pixel in the encrypted version changes, and the amount of change in brightness across the image is close to the theoretical ideal for resisting “differential” attacks. The method also passes chosen‑plaintext tests, where attackers are allowed to pick special input images like all‑black or all‑white; even these produce cipher images that look random and unrelated. At the same time, the algorithm remains efficient: with straightforward software optimizations, it can encrypt medium‑sized images in well under a second on a standard laptop, and its operations are well suited to further acceleration on graphics chips or dedicated hardware.
What this means for everyday security
In essence, the paper shows that by carefully crafting and analyzing a new chaotic formula, then weaving it together with two others in a dynamic way, we can build an image “lock” that is both stronger and more flexible than many existing designs. The new system turns ordinary pictures into noise‑like patterns that reveal almost nothing, even under sophisticated mathematical probing, while remaining lightweight enough for real‑time use in devices and communication systems. For anyone concerned about the privacy and integrity of visual data—from telemedicine and smart cameras to satellites and drones—this work points toward more secure ways to protect what our images reveal.
Citation: Sarra, B., Sun, H., Dua, M. et al. A novel 1D powered Chebyshev quadratic map-based image encryption using dynamic permutation-diffusion. Sci Rep 16, 9469 (2026). https://doi.org/10.1038/s41598-026-38483-x
Keywords: image encryption, chaotic maps, digital privacy, secure imaging, cryptography