Clear Sky Science · en
Ensemble machine learning for proactive android ransomware detection using network traffic
Why your phone’s internet chatter matters
Our smartphones quietly talk to the internet all day long. Hidden in that chatter, cybercriminals can sneak in a nasty kind of attack called ransomware, which locks your files or even your whole device until you pay a fee. This paper explores how carefully watching that network chatter—not the apps themselves—can expose Android ransomware early, using a team of smart machine-learning models that learn and adapt as criminals change their tricks.
How ransomware hijacks an Android phone
Ransomware usually starts with a simple mistake: installing what looks like a harmless app from a third-party store, a link in a message, or a fake update. Once on the phone, the app asks for broad permissions, such as access to storage, camera, microphone, or system controls. With those granted, it quietly encrypts photos, documents, and messages, and may send sensitive data back to remote servers. Only then does it reveal its true nature, displaying a lock screen or warning message and demanding payment, often in cryptocurrency, to restore access. Some strains are built to survive removal attempts, making them especially hard to eliminate and turning a moment of inattention into days of disruption for individuals and businesses.
Watching the flow instead of the files
Traditional antivirus tools look for known malicious code “signatures,” which works poorly when attackers constantly rewrite and disguise their software. This study takes a different route: it focuses on network traffic metadata—numbers that describe how data moves in and out of the phone, such as packet sizes, timing between packets, and connection patterns. Using more than 200,000 traffic records that include normal activity and ten notorious ransomware families, the authors build a system that learns the telltale rhythm of ransomware: sudden bursts of traffic, unusual connection durations, or odd combinations of technical flags that rarely appear in everyday use. Because this method looks at behavior rather than code, it can spot new or modified ransomware families that have never been cataloged before. 
Building a team of digital “judges”
Instead of trusting a single model, the researchers combine several machine-learning approaches—Light Gradient Boosting Machine, XGBoost, Random Forest, and others—into an ensemble, much like consulting a panel of experts rather than one lone reviewer. They first clean and normalize the data, then select the most informative features using a three-step pipeline that filters, tests, and ranks network attributes. Techniques such as SMOTE are used to balance the dataset so that ransomware examples are not drowned out by ordinary traffic. After careful tuning and five-fold cross-validation, the models are benchmarked head-to-head. LightGBM in particular delivers striking performance, correctly distinguishing ransomware from benign traffic in nearly all test cases, while using a relatively small and efficient set of features suitable for real-time use on resource-limited devices.
Opening the black box for human analysts
High accuracy alone is not enough for security teams, who need to understand why a system flagged a connection as dangerous. To tackle this, the authors apply explainable AI tools called SHAP and LIME. These methods reveal which traffic patterns most influenced each decision—for example, extremely short gaps between packets that resemble rapid-fire encryption, or unusually long data flows that look like information being smuggled out to a remote server. By mapping such features to well-known attacker tactics cataloged in the MITRE ATT&CK framework, the system’s alerts become more than just yes-or-no answers; they become clues investigators can follow. This transparency makes it easier to trust the model, refine defense rules, and respond more quickly when a new wave of ransomware appears. 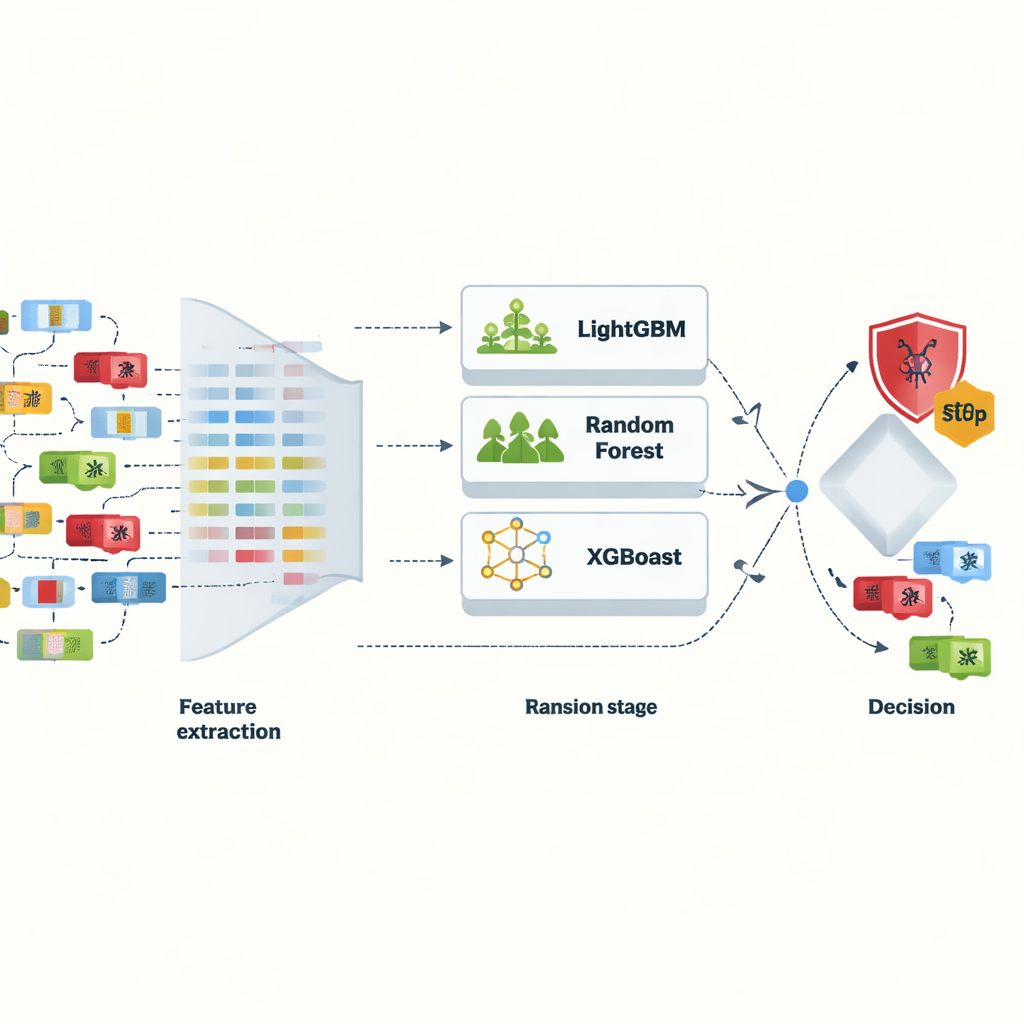
Staying adaptive as attackers evolve
Cybercriminals do not stand still, so a fixed, one-time-trained model will gradually lose its edge as ransomware evolves. To explore how to stay current, the researchers simulate the passage of time by splitting their traffic data into five chronological blocks and updating a LightGBM model step by step, mimicking an online-learning scenario. While a static model’s accuracy erodes under this shifting landscape, the incrementally updated version maintains stronger performance, even though it still loses some ground by the final block. This experiment highlights both the value and the limits of incremental learning: continuous updates help, but long-term robustness will still require periodic retraining or more advanced adaptive strategies, especially as attackers invent new ways to hide in encrypted and noisy network environments.
What this means for everyday users
For non-specialists, the message is reassuring: by paying attention to how data moves rather than trying to catalog every possible malicious file, security tools can detect Android ransomware quickly and accurately—even as it changes shape. The framework proposed in this paper shows that a well-designed ensemble of machine-learning models, supported by careful data handling and clear explanations, can form the backbone of practical, real-time protection for mobile devices. While more work is needed to harden these methods against future threats and to run them efficiently on phones and edge devices, this study points toward a future where the subtle patterns in your phone’s network traffic serve as an early warning system, quietly blocking ransomware before it ever has a chance to lock your digital life.
Citation: Kirubavathi, G., Padma Mayuri, B., Pranathasree, S. et al. Ensemble machine learning for proactive android ransomware detection using network traffic. Sci Rep 16, 9498 (2026). https://doi.org/10.1038/s41598-026-38271-7
Keywords: Android ransomware, network traffic analysis, machine learning security, ensemble models, mobile cybersecurity