Clear Sky Science · en
Blockchain-driven smart contract with key exchange protocol for secure device-to-device communication using verkle tree K-ary structures
Why talking gadgets need better bodyguards
Billions of everyday gadgets—phones, sensors, meters, and medical devices—now talk to each other wirelessly. Often they must connect through a central base station, which can be slow, overloaded, or even knocked out in a disaster. This paper explores a new way for nearby devices to talk directly, keep eavesdroppers out, and record who said what using an energy‑saving form of blockchain. For readers, it offers a glimpse of how the invisible conversations between gadgets may soon become both faster and harder to hack.
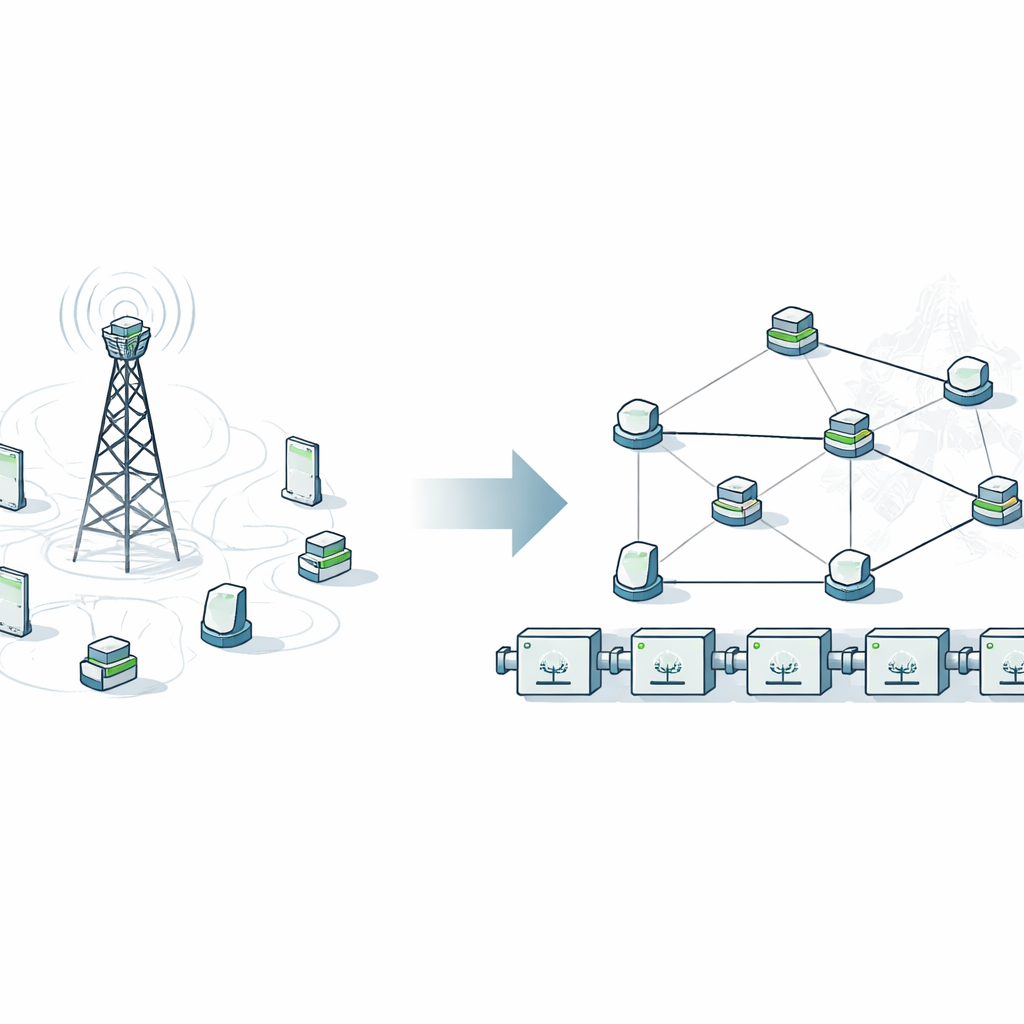
From crowded highways to local side streets
Today, even two phones sitting a few meters apart typically send their messages up to a cellular tower and back down again. That roundabout trip wastes time and clogs the network, especially as 5G and “beyond‑5G” applications demand instant responses. The authors focus on “device‑to‑device” communication, where gadgets connect directly like neighbors chatting over a fence. This local shortcut can boost speed, save battery power, and keep the wider network from getting jammed, which is vital in emergencies when base stations may fail.
Keeping secrets in a hostile neighborhood
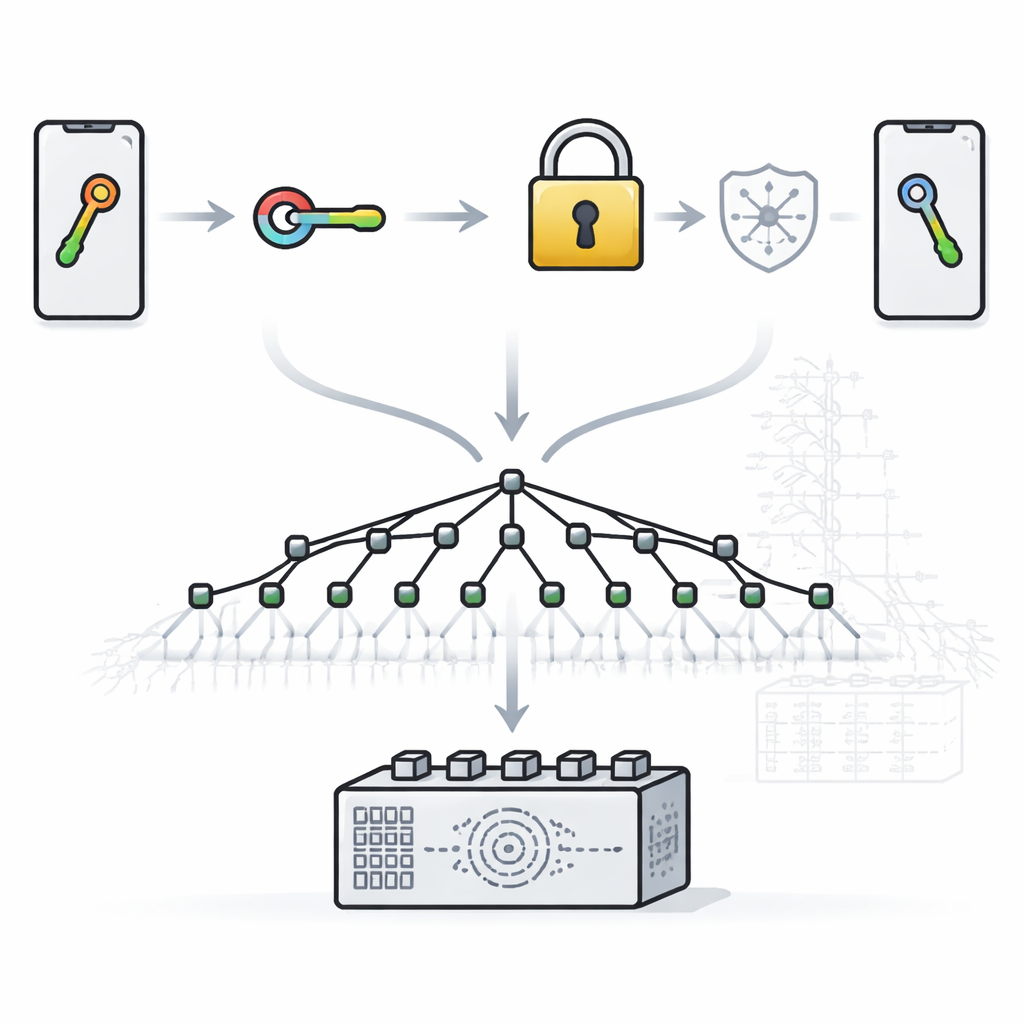
Letting devices talk directly also makes them tempting targets. Attackers can try to slip into the middle of a conversation, replay old messages, or pretend to be someone else. To defend against this, the researchers build their system on a well‑known mathematical trick called Elliptic Curve Diffie–Hellman. In simple terms, each device creates its own private “lock” and a public “key.” By exchanging only the public parts, both sides independently arrive at the same shared secret without ever revealing it. That secret then feeds an encryption method (AES‑256) so that even if someone captures the wireless traffic, the contents remain unreadable.
Smart contracts as impartial referees
The next challenge is trust. How can a device be sure a stranger’s public key is genuine, and not swapped by an attacker? The team turns to blockchain and smart contracts—self‑running code stored on a shared ledger. Devices register their identity and public key with a contract on an Ethereum‑style network. When two gadgets want to talk, the contract checks that both are known and authorized, helps them establish a secure session, and records key events. Because the ledger is shared and tamper‑resistant, it becomes very hard for an attacker to forge identities or quietly rewrite history.
Shrinking the blockchain’s baggage
Classic blockchains store transaction summaries in a structure called a Merkle tree, which proves that a given entry is really inside a block. While robust, these trees can require large “proofs” and extra time to verify, particularly as the system scales to millions or billions of entries. The authors replace this with a newer structure called a Verkle tree, which uses a different mathematical commitment under the hood. By allowing each node in the tree to have many children (a k‑ary structure), the tree becomes shorter and its proofs more compact. Simulations show that, for the same security level, Verkle‑based proofs can be up to 33 times smaller than those built from Merkle trees and validate roughly twice as fast.
Putting the pieces together in practice
To test the full design, the team implemented the smart contracts in Solidity on a private Ethereum test environment and ran the cryptographic steps in Python on an Internet‑of‑Things‑class processor. They compared their key‑exchange method with older standards like RSA and traditional elliptic‑curve schemes. While all offer similar theoretical security, RSA needs much larger keys and burns more time and energy. Their Elliptic Curve Diffie–Hellman setup, by contrast, used compact keys, exchanged them in a few thousandths of a second, and consumed the least energy. Combined with the Verkle tree ledger, it delivered low communication delay, reduced blockchain storage needs, and strong protection against a wide range of attacks, including man‑in‑the‑middle, replay, and impersonation attempts.
What this means for everyday connected life
In plain terms, the study shows that our gadgets can talk directly and securely without leaning so heavily on distant towers or fragile central servers. By blending efficient encryption, automated blockchain agreements, and a leaner way of organizing ledger data, the authors outline a path toward secure, fast, and scalable conversations among billions of devices. In the future, they plan to harden this approach even further against emerging quantum‑era threats, aiming to keep the digital “whispers” between devices private and trustworthy for years to come.
Citation: Simbu, A., Nandakumar, S. & Saravanan, K. Blockchain-driven smart contract with key exchange protocol for secure device-to-device communication using verkle tree K-ary structures. Sci Rep 16, 9470 (2026). https://doi.org/10.1038/s41598-026-38035-3
Keywords: device-to-device communication, blockchain security, smart contracts, elliptic curve key exchange, Verkle tree