Clear Sky Science · en
Research on infrastructure network protection strategy based on bayesian stackelberg game under asymmetric conditions
Why protecting hidden lifelines matters
Electricity, transport, communications and water systems are the hidden lifelines that keep modern society running. Yet recent incidents—from blackouts to attacks on bridges and power plants—show how vulnerable these interconnected networks can be. This study asks a simple but vital question: if determined attackers are probing these systems, how can defenders use limited resources, plus a bit of clever misdirection, to keep the lights on and the trains running? Drawing on ideas from network science and strategic decision-making, the authors propose a way for defenders to mislead attackers while still planning for both smart and impulsive adversaries.

Seeing infrastructure as a web of connections
The paper treats critical infrastructure as a web of nodes and links: power stations, communication hubs and transport junctions connected by cables, pipes and routes. Because so much depends on these interlocking systems, the failure of a single key node can trigger cascading breakdowns. Earlier protection methods often assumed that defenders simply react after something goes wrong, or that they know fixed failure probabilities for each component. They also tended to treat attackers as perfectly rational, all-knowing players. The authors argue that real-world confrontations are messier: information is incomplete, attackers have different goals and resources, and human decisions can be far from perfectly logical.
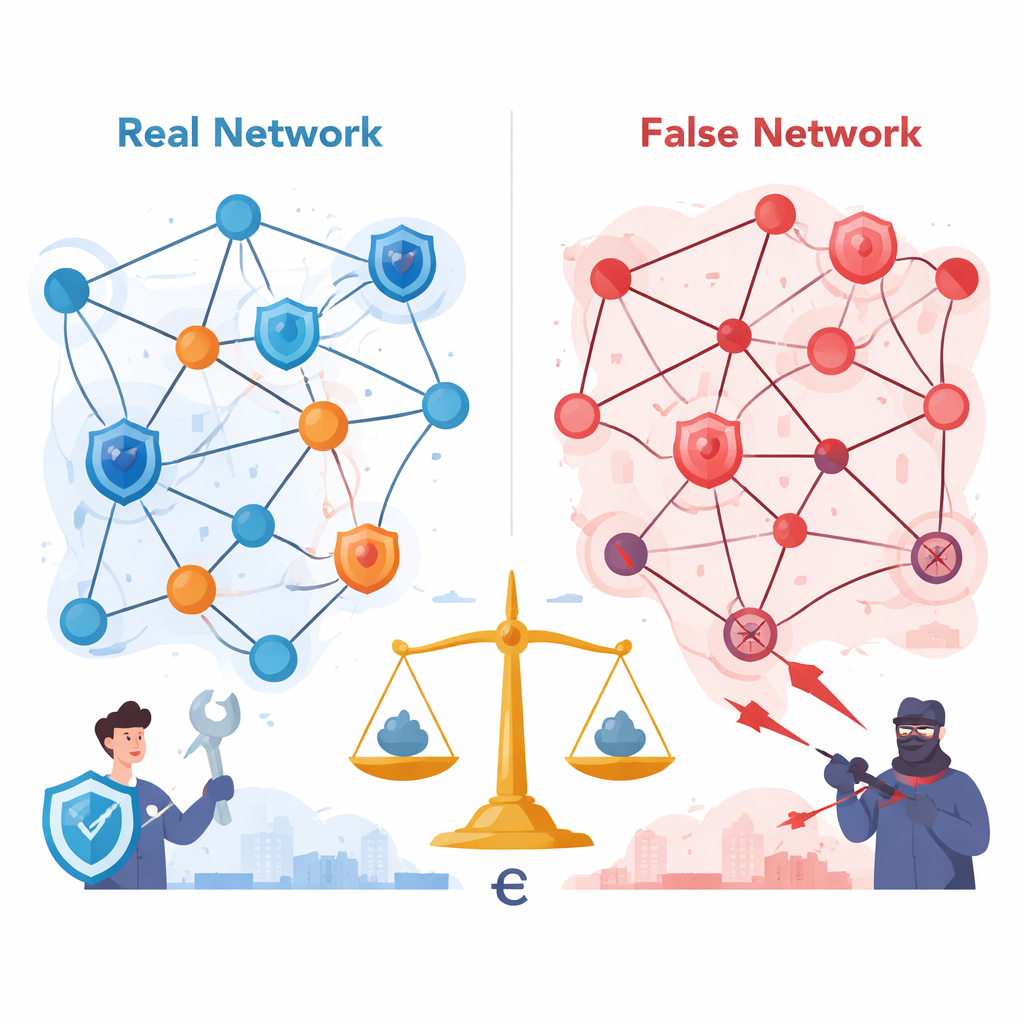
Outsmarting attackers with a fake map
Instead of only hardening known weak spots, the authors explore an "active defense" idea: let the attacker see a slightly wrong version of the network. They define a false network, a carefully altered copy of the real system. In this camouflage network, some genuine connections are hidden and some fake links are added, so that the network still "looks" realistic but its apparent weak points are moved away from truly critical nodes. To design this deception without manually rewriting hundreds of rules, they use a graph convolutional neural network that learns structural patterns from the real infrastructure. It then suggests which links to add or hide so that the fake map is convincing but steers attackers toward less harmful targets.
Planning for many kinds of attackers
Knowing that not all adversaries think alike, the study distinguishes between short-term and long-term attackers. Short-term attackers want to cause the biggest immediate disruption, such as shrinking the largest still-functioning part of the network. Long-term attackers care more about degrading overall capacity over time. The authors place these behaviors inside a "leader–follower" decision framework: defenders first choose a mixed pattern of protection across the network, and then attackers pick their preferred way to strike after observing this pattern. Because the defender does not know which attacker type will appear, they assign probabilities to each type and compute strategies that work reasonably well on average across them.
Allowing for imperfect, even irrational choices
Real attackers may not always pick the mathematically best move—they may misjudge risks, rush decisions, or be swayed by bias. To reflect this, the authors introduce a "strong ε equilibrium" concept. Here, ε measures how far an attacker’s choice is allowed to stray from the best possible payoff. The defender then plans for the worst case within this band of near-best responses, effectively assuming that the attacker may behave somewhat erratically but not completely at random. Using a specialized optimization procedure, they compute defense strategies that keep the defender’s minimum expected benefit relatively high, even when attackers are partly irrational. Simulations on a 500-node test network show that these strategies make the defender’s outcomes more stable and reduce the risk of disastrous surprises.
How well deception works in practice
The authors compare their learned false networks with two simpler ways of adding and deleting links: random changes, and changes based only on node importance. Their method moves slightly fewer links than a random scheme but produces substantially higher defensive benefit, and yields better value for money than the degree-based approach. When no camouflage is used, optimal attacks can greatly damage the system once resources reach a moderate level. With the proposed false networks and strong ε-based defense strategies, a significant portion of potential damage is diverted onto less critical parts of the system, raising the defender’s average benefit and cutting the effective vulnerability of the real network.
What this means for everyday security
For a lay reader, the core message is that defenders of critical infrastructure do not have to be stronger everywhere; they can be smarter instead. By carefully shaping what attackers see and by planning for multiple attacker types who may not always act logically, it is possible to shift attacks away from truly vital components and cushion the impact of failures that do occur. While the paper focuses on models and simulations, its ideas point toward future security tools that blend deception, probability and network analysis to keep essential services resilient in the face of unpredictable threats.
Citation: Zhang, J., Gao, Y., Kang, W. et al. Research on infrastructure network protection strategy based on bayesian stackelberg game under asymmetric conditions. Sci Rep 16, 7045 (2026). https://doi.org/10.1038/s41598-026-37843-x
Keywords: critical infrastructure, network security, game theory, deception defense, cascading failures