Clear Sky Science · en
A hybrid XGBoost–SVM ensemble framework for robust cyber-attack detection in the internet of medical things (IoMT)
Why smarter medical gadgets need smarter guards
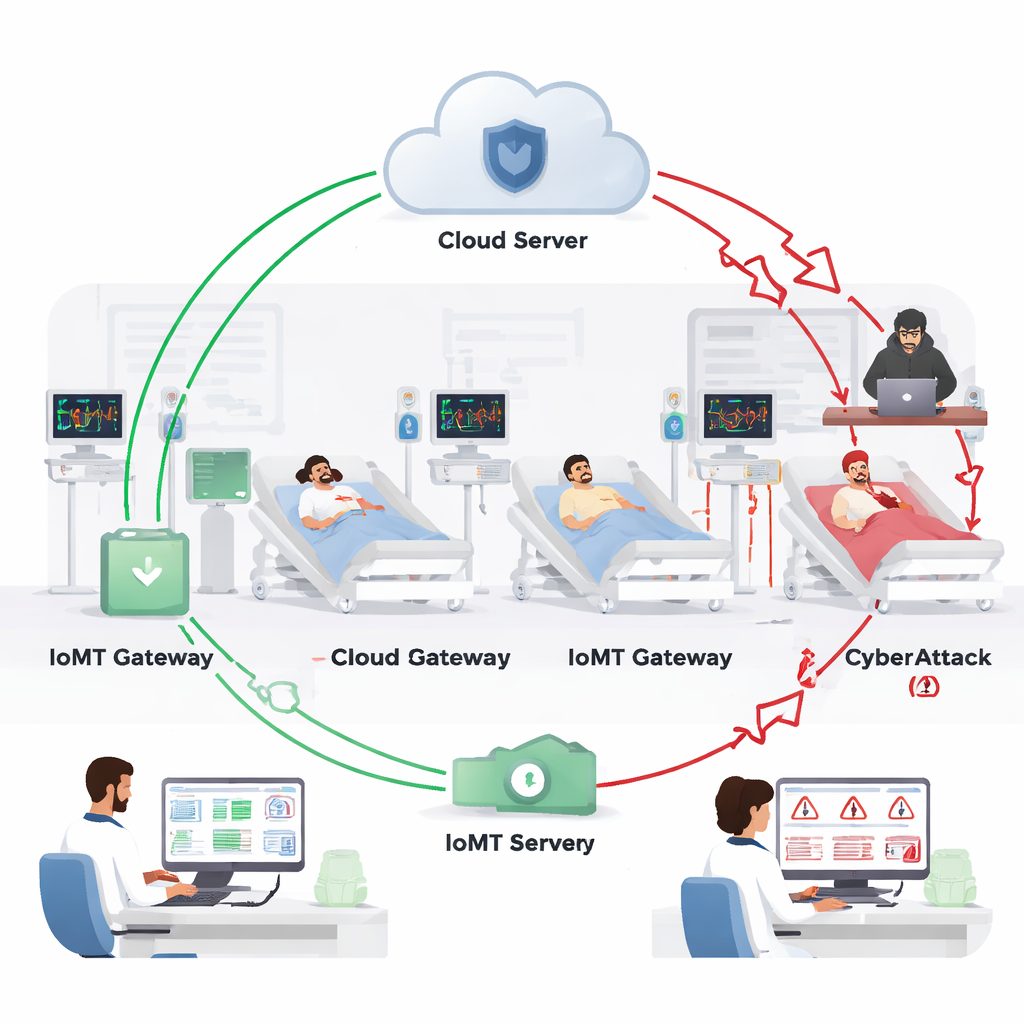
The devices that quietly watch over patients today – heart monitors, glucose sensors, smart pumps and wearables – are all part of the rapidly growing Internet of Medical Things (IoMT). These tools make care more convenient and can even save lives, but they also open new digital doors for hackers. This paper explores how a new kind of data‑driven “alarm system” can spot cyber‑attacks on medical devices quickly and accurately, helping to keep both patient data and patient safety intact.
The rise of connected care – and its weak spots
IoMT connects medical sensors, hospital equipment, mobile health apps and cloud services so that vital signs and other health data can flow in real time between patients and clinicians. This connectivity has exploded since the COVID‑19 pandemic, supporting remote monitoring, fewer hospital visits and lower costs. Yet the same networks that move life‑critical information are attractive targets for criminals. Attacks such as ransomware, data theft and man‑in‑the‑middle tampering can alter readings, block access to records or shut down services, with direct consequences for diagnosis and treatment.
Why old defenses are not enough
Traditional protections like passwords and basic encryption help, but they were not designed for the sheer number and variety of IoMT devices, many of which have limited computing power and rarely receive updates. Past research has tried rule‑based firewalls, heavy deep‑learning models and many single machine‑learning algorithms. These approaches either struggle to keep up with new attack tricks, consume too many resources for small devices, or generate too many false alarms. The authors argue that what is needed is a lightweight yet sharp “pattern reader” that can learn from real network and medical data how attacks truly behave.
Teaching machines to recognize hostile behavior
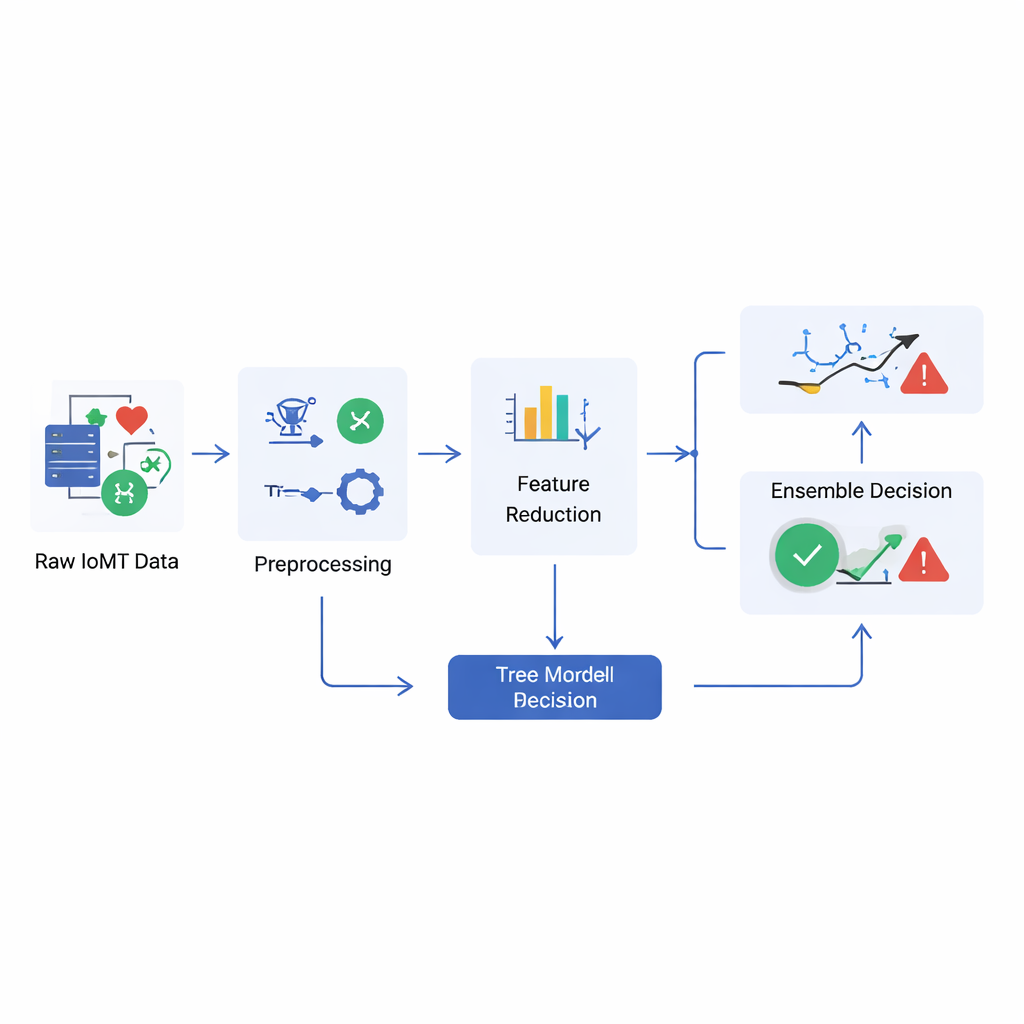
The study builds such a detector using a hybrid ensemble – a team of algorithms that vote together – trained on a real hospital‑style testbed called WUSTL‑EHMS‑2020. This dataset mixes normal traffic from sensors and gateways with carefully staged attacks that mimic denial‑of‑service, data injection and eavesdropping on patient streams. The system first cleans and condenses the data, then feeds it into two types of learners: a tree‑based method known for finding intricate combinations of clues, and support‑vector methods that excel at drawing crisp boundaries between “safe” and “unsafe” behavior in complex data. Each model produces its own assessment, and a soft‑voting scheme averages their probabilities to reach a final decision.
How well the new alarm performs
On the main IoMT dataset, the combined model correctly classified about 98% of cases, with very few missed attacks and few normal events wrongly flagged as threats. To test whether it would still work beyond the original lab setting, the authors also evaluated it on two well‑known security collections, TON‑IoT and CICIDS‑2017, which contain a wide range of network threats. There, the detector reached accuracy above 99%, suggesting that it can generalize to different environments and attack styles. Importantly, the authors measured how much memory, processing time and power the method used, showing that it can run on gateways and edge nodes typically found in hospital networks without the heavy footprint of deep neural networks.
What this means for patients and hospitals
For a non‑specialist, the core message is simple: by learning from real medical network data, this hybrid model becomes a highly sensitive and efficient tripwire for digital tampering. It does not replace basic security measures, but it adds an intelligent monitoring layer that can warn clinicians and security teams when anything unusual starts to happen in the data streams that guide care. If adopted and further refined, such techniques could make connected health systems more trustworthy, so that the benefits of smart devices – faster care, fewer complications, and more comfort at home – are not overshadowed by the risk of invisible cyber‑attacks.
Citation: Abdelhaq, M., Palanisamy, S., Gopinath, M. et al. A hybrid XGBoost–SVM ensemble framework for robust cyber-attack detection in the internet of medical things (IoMT). Sci Rep 16, 6855 (2026). https://doi.org/10.1038/s41598-026-37832-0
Keywords: Internet of Medical Things, medical device security, cyberattack detection, machine learning, healthcare data protection