Clear Sky Science · en
Enhancing security in IoMT using federated TinyGAN for lightweight and accurate malware detection
Why smarter security matters for connected medical devices
From hospital beds to fitness watches, an exploding number of medical gadgets are now online, quietly collecting heart rates, insulin levels, and other sensitive data. This “Internet of Medical Things” (IoMT) promises better, faster care—but it also opens new doors for hackers. The paper summarized here introduces a new way to spot malicious software, or malware, on these devices that is both highly accurate and gentle on their limited battery, memory, and processing power.
The growing risk in a world of smart devices
Billions of everyday objects—from infusion pumps to home blood-pressure cuffs—communicate over the internet. Because they are cheap, tiny, and built by many different manufacturers, they often lack strong, uniform security. Malware that infects even one such device can quickly spread through a hospital or home network, steal private data, or launch disruptive attacks like the infamous Mirai botnet that once knocked major websites offline. Traditional defenses frequently rely on central servers that collect raw data from every device, analyze it, and send back decisions. While effective, this approach can overload fragile devices, introduce delays, and create juicy targets for attackers who need only breach the central database to access everything.

A new way to learn from devices without exposing their data
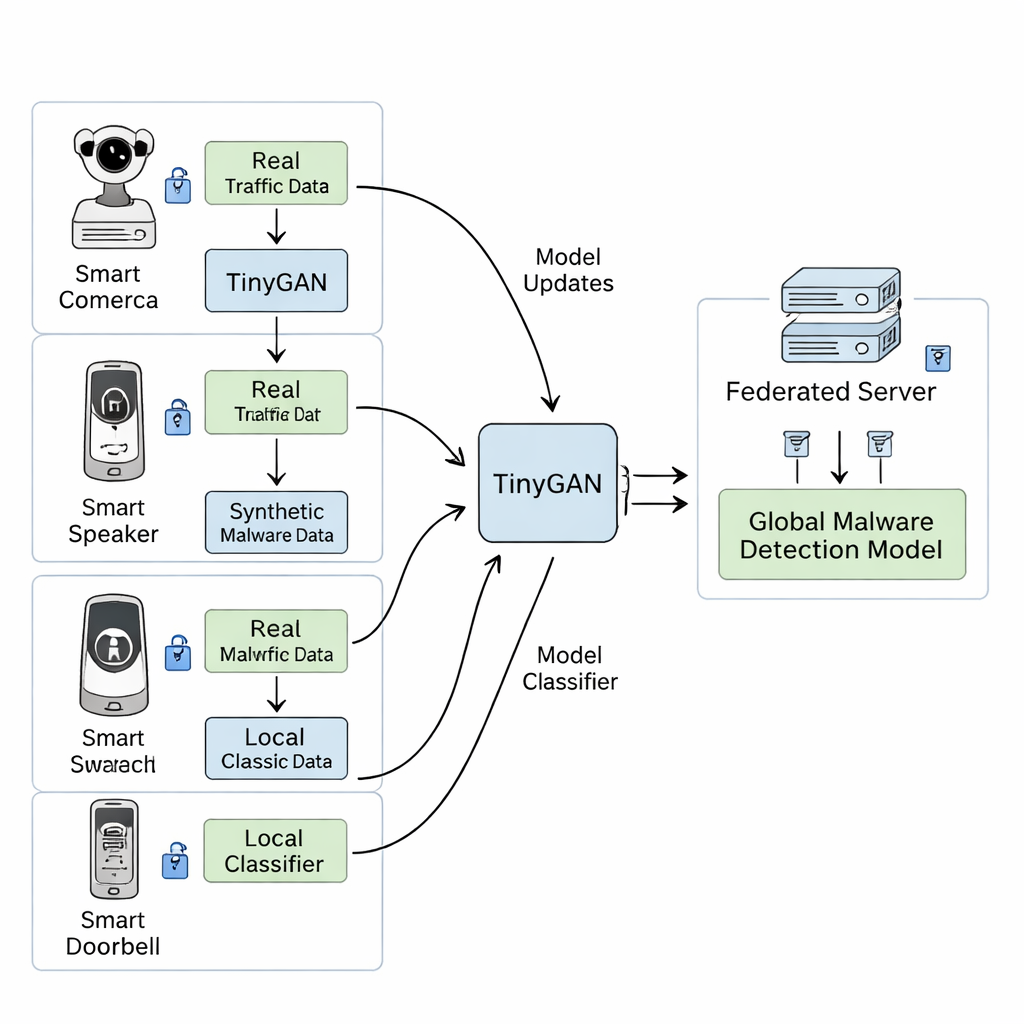
The authors propose a different strategy built on a technique called federated learning. Instead of shipping raw data to a central server, each device trains its own small detection model locally using its own traffic logs. Periodically, the devices send only anonymized model updates—like refined “rules of thumb”—to a central server, which averages them into a stronger, shared model and sends the improved version back. No personal or medical data ever leaves the devices. This design cuts down on bandwidth use, respects privacy laws and patient trust, and can adapt as new attack patterns emerge in the wild.
Teaching the system about rare and new attacks
A key challenge in security is spotting rare or never‑before‑seen (“zero‑day”) malware. Real-world datasets are often unbalanced: common attacks show up everywhere, while some dangerous variants occur only a handful of times. To tackle this, the framework adds a compact synthetic data generator called TinyGAN. On each device, TinyGAN learns the statistical “shape” of malicious network flows and then creates realistic fake examples that resemble hard-to-find malware. These synthetic samples are mixed with real traffic to train the local detector, giving it a richer sense of what bad behavior can look like without needing to collect huge amounts of real attack data.
Putting the system to the test on real network traffic
The researchers tested their approach on IoT‑23, a large public dataset of internet traffic that includes many well-known IoT malware families such as Mirai and Hajime. They deployed the system on two modest edge devices—a Raspberry Pi and an NVIDIA Jetson Nano—connected to a central server, mimicking a small but realistic IoMT setup. They compared three options: a simple neural network (MLP), a deeper model that mixes feedforward and memory-based layers (FNN/LSTM), and their federated TinyGAN design. While the heavier FNN/LSTM reached very high accuracy in a simple two-class task (malicious vs. benign), it struggled when asked to distinguish between many types of malware and required more time and resources. The simple MLP ran easily on small devices but failed to generalize across the very different data each device saw. In contrast, the federated TinyGAN system converged quickly—within about 20 training rounds—and delivered a precision of 99.30%, a perfect recall of 100%, and an overall F1 score near 99.5%, all while keeping model size and memory use low enough for real IoT hardware.
Robust, private protection for the medical internet
Beyond raw accuracy, the authors examined how their system behaves under stress. They showed that even if one device in the small network is compromised and deliberately mislabels data, or if the communication channel is noisy, the global model’s performance degrades only slightly and continues to improve over time. Analyses of the synthetic data confirmed that TinyGAN produces varied, realistic malware examples rather than merely copying the training set, helping the model avoid overfitting and better handle unfamiliar attacks. Overall, the study concludes that combining federated learning with a lightweight synthetic data generator offers a practical, privacy-preserving way to harden medical and other IoT devices against evolving malware, without demanding heavy hardware or exposing sensitive patient information.
Citation: S, D., Shankar, M.G., Daniel, E. et al. Enhancing security in IoMT using federated TinyGAN for lightweight and accurate malware detection. Sci Rep 16, 7116 (2026). https://doi.org/10.1038/s41598-026-37830-2
Keywords: IoT security, medical devices, malware detection, federated learning, synthetic data