Clear Sky Science · en
Adaptive bit placement for dual biometric using signature and finger print for DWT-DCT picture steganography
Why hiding ID inside a picture matters
Every time we unlock a phone with a fingerprint or send a scanned signature online, we are handing over pieces of our identity. If someone intercepts or copies this data, they can impersonate us in powerful ways. This paper explores a clever way to hide two kinds of biometric information—a handwritten signature and a fingerprint—inside a single ordinary-looking photo. The goal is to make the hidden data extremely hard to notice, hard to destroy, and still easy to recover for legitimate security checks.
Turning a picture into a secret carrier
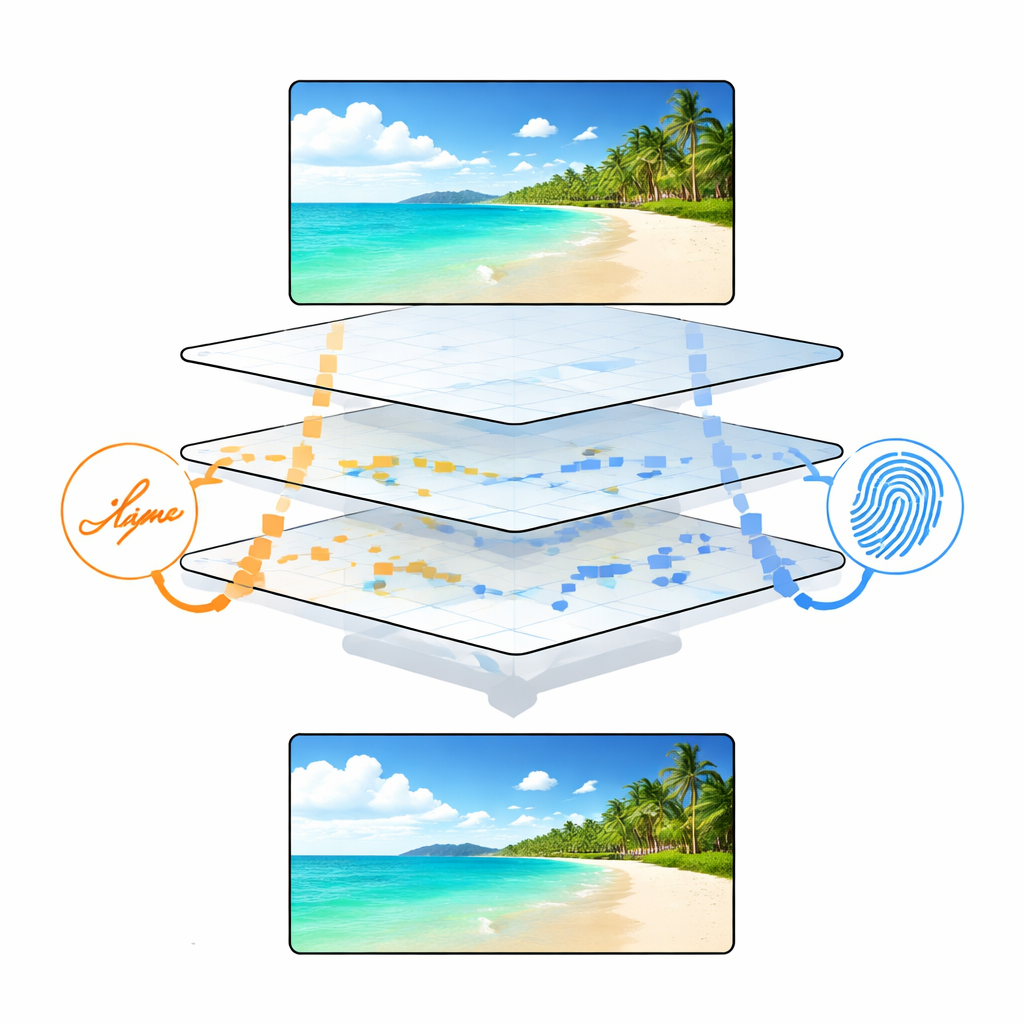
The researchers start with a common, detailed image such as the famous “Baboon” test picture. Such busy, textured photos are ideal hiding places because small changes are visually lost in the natural clutter. Before any data is hidden, the image is mathematically broken down into different layers that represent broad shapes and fine details. This is done with a pair of standard tools from digital imaging: one that separates the picture into low- and high-detail bands, and another that breaks those bands into building blocks of different frequencies. Together, these tools let the system decide where a tiny change will be least noticeable to the human eye while still surviving common image operations like compression or noise.

Hiding two body signs at once
The dual biometrics—signature and fingerprint—are first cleaned and simplified so that each becomes a neat grid of black and white pixels. These grids are then turned into streams of bits (zeros and ones). Instead of simply tucking those bits into fixed positions, the method assigns each type of biometric to a different layer of the transformed image: signature bits go into one band rich in horizontal detail, while fingerprint bits go into another rich in vertical detail. This separation means that even if part of the image is damaged or altered, the two biometrics can often still be recovered independently, offering a form of backup and making it much harder for an attacker to spoof or erase both at once.
Letting the picture choose where bits go
The centerpiece of the work is “adaptive bit placement.” Rather than overwriting the same positions everywhere, the algorithm measures how strong or important each tiny coefficient in the transformed image is. Bits are only hidden where the numbers are large or the local texture is complex—places where small nudges blend into natural variation. A threshold, derived from simple statistics of these values, decides which locations are safe. The strength of each change is also tuned so that the trade-off between invisibility and toughness can be controlled. In effect, the image itself guides where the secret lives, which makes statistical detection and machine-learning-based steganalysis far more difficult.
Putting the method to the test
To see whether this approach really works, the authors embed both biometrics into a variety of standard test images and then measure three things: how similar the stego image looks to the original, how much data it can carry, and how well the hidden biometrics survive abuse. The visual differences are so small that they are effectively invisible, confirmed by high scores on common quality measures. The method carries slightly more data than earlier dual-biometric schemes, even though it hides two complete templates. When the images are rotated, cropped, compressed as JPEGs, or sprinkled with noise, the recovered signatures and fingerprints still match closely enough for reliable authentication, with error rates that are markedly lower than those of competing methods.
What this means for everyday security
In simple terms, this research shows how a single, innocent-looking picture can securely “carry” both a person’s fingerprint and signature in a way that is hard to notice and hard to break. By letting the image structure itself decide where and how to hide the bits, the system keeps the picture looking natural while protecting the embedded identity against common digital tampering. Such a framework could strengthen identity checks in high-security settings—from defense and forensic work to medical devices and smart cities—where losing or leaking biometric data is not an option.
Citation: Bhattacharya, A., Welekar, A.R., Sarkar, P. et al. Adaptive bit placement for dual biometric using signature and finger print for DWT-DCT picture steganography. Sci Rep 16, 8758 (2026). https://doi.org/10.1038/s41598-026-37827-x
Keywords: biometric security, image steganography, digital privacy, fingerprint recognition, signature verification