Clear Sky Science · en
Smart IoT applications of multi attack detection using cluster F1MI approach
Why your connected gadgets need smarter protection
From smart doorbells and cameras to medical sensors and factory machines, the Internet of Things (IoT) now quietly runs much of daily life. But these connected devices are often poorly protected and easy targets for hackers who can spy on us, disrupt services, or steal data. This paper presents a low‑cost, automated defense system that watches network traffic, spots many kinds of attacks in real time, and sounds the alarm before serious damage is done.
A digital neighborhood watch for smart devices
Imagine your home or workplace filled with smart gadgets that all talk to each other through a common router. In the scenario the authors describe, an intruder tries to slip into this chatter, flooding the network with malicious traffic or quietly siphoning off data. A monitoring tool first captures all the packets flowing through the router and turns them into a structured dataset. A machine‑learning security module then studies this data to distinguish normal behavior from suspicious patterns, and, when it detects trouble, it alerts administrators and can trigger alarms. This setup acts as a kind of neighborhood watch for your devices, continuously scanning for abnormal behavior without needing a human to stare at dashboards all day. 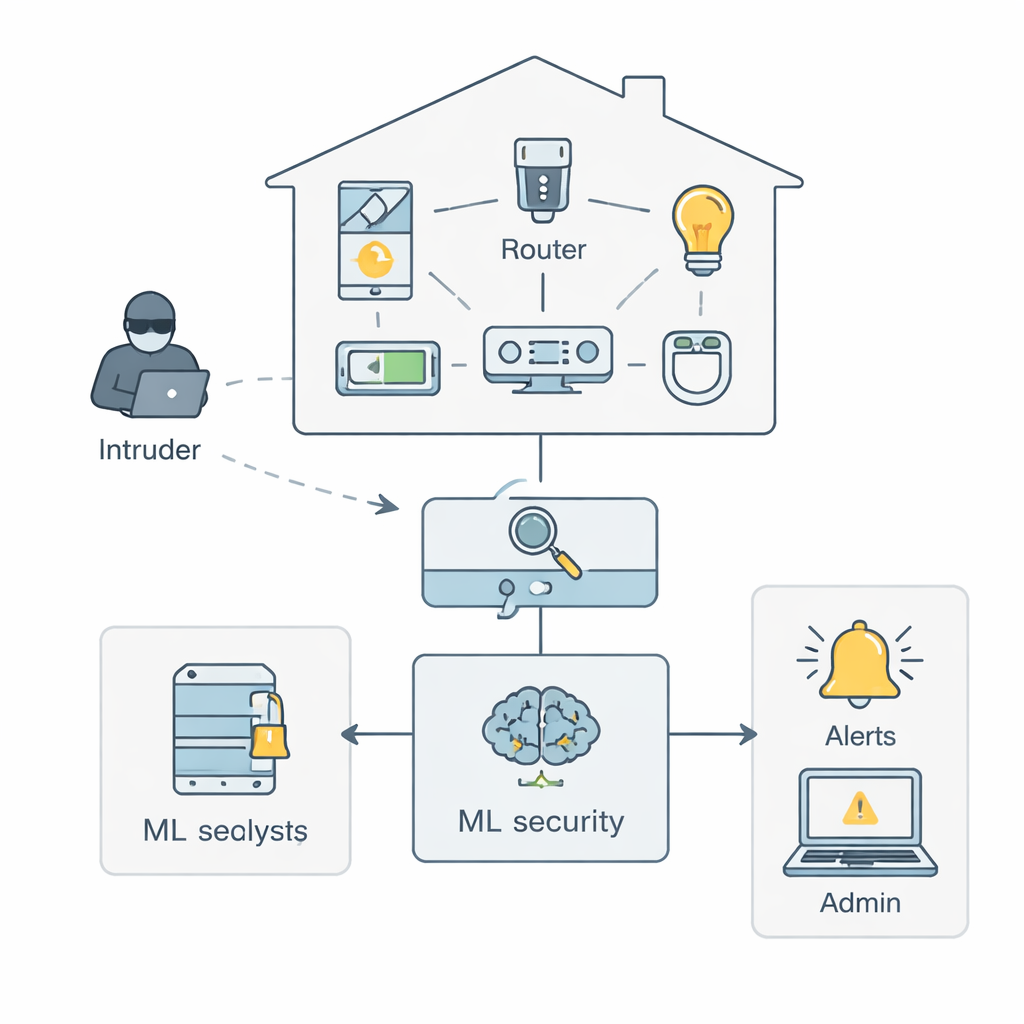
Teaching machines to focus on the right warning signs
Raw network data is messy: it contains millions of records and dozens of technical measurements for each connection, many of them repetitive or unhelpful. The authors propose a Smart Secured IoT Framework (SSIF) that first cleans and standardizes this data, then balances it so that rare but dangerous attacks are not drowned out by everyday traffic. Next comes the heart of their method: a feature‑engineering scheme called Cluster F1–MI. In simple terms, the system learns which measurements carry the most useful clues about attacks—such as how long a communication lasts, how many packets are sent in one direction, or how irregular the timing is between packets. It ranks these measurements by how well they help separate attacks from normal traffic, removes those that add little value, and groups similar ones into clusters so it can keep only a single representative from each group.
Turning traffic patterns into attack labels
Once the framework has boiled the data down to a compact set of strong signals, it trains a range of machine‑learning models to recognize different threats. The models are taught using the BoT‑IoT dataset, a large, realistic collection of traffic from simulated IoT devices that includes both normal activity and numerous attacks. These attacks fall into three broad families: intelligence gathering (such as network scanning and identifying device types), service disruption (including floods of fake traffic that overwhelm a device), and data exfiltration (stealing passwords, keystrokes, or other sensitive information). The authors test several popular algorithms—Support Vector Machines, Random Forests, Gradient Boosting methods, XGBoost, and Neural Networks—using rigorous cross‑validation and parameter tuning to avoid over‑optimistic results. 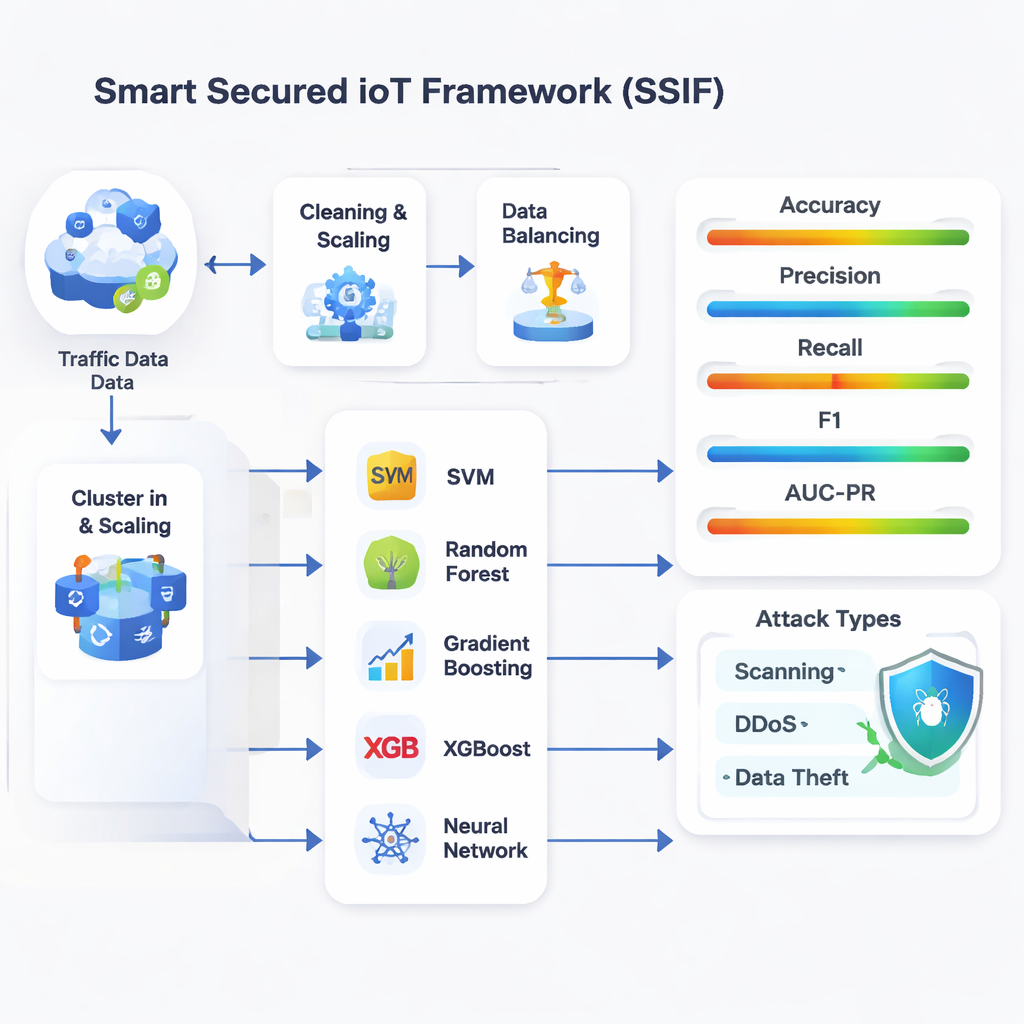
How well does the framework actually work?
The refined feature set and tuned models prove highly effective. Across 11 different attack types, the best‑performing model, Random Forest, reaches an accuracy above 97%, with similarly strong precision, recall, and F1 scores. In practice, this means the system not only catches most attacks but also keeps false alarms low. Even for subtle threats like credential theft or data breaches, which appear far less often in the data, the framework maintains high detection scores. Compared with earlier intrusion‑detection approaches that either used very few features or far too many, SSIF strikes a balance: it reduces the number of measurements the models need to consider while improving detection quality and keeping computing costs low enough for resource‑constrained IoT environments.
From lab framework to everyday shield
For non‑specialists, the key takeaway is that it is possible to build an automated, always‑on security layer that protects large fleets of smart devices without requiring expensive hardware or constant human oversight. By letting algorithms learn which patterns in device traffic truly matter, and by constantly checking for three main kinds of malicious behavior—reconnaissance, disruption, and data theft—the Smart Secured IoT Framework can provide early warnings via emails and alarms whenever abnormal activity is spotted. While future work will expand to richer, more varied real‑world datasets, this study shows a clear path toward turning today’s vulnerable smart homes, hospitals, and industries into far more resilient connected systems.
Citation: Nagavel, V., Bhuvaneswari, P.T.V. & Ramesh, P. Smart IoT applications of multi attack detection using cluster F1MI approach. Sci Rep 16, 6251 (2026). https://doi.org/10.1038/s41598-026-37695-5
Keywords: IoT security, anomaly detection, machine learning, network attacks, intrusion detection