Clear Sky Science · en
Hybrid quantum–chaotic key expansion enhances QKD rates using the Lorenz system
Why faster quantum security matters
As more of our lives move online—from banking and telemedicine to cloud gaming and smart homes—keeping data safe is becoming both more important and more difficult. Quantum key distribution (QKD) is one of the most promising ways to secure communications against even future quantum computers, but today’s QKD systems often produce secret keys far too slowly for high‑bandwidth tasks like video streaming or for large fleets of tiny Internet‑of‑Things (IoT) devices. This paper explores a way to boost QKD’s usable speed in software, without changing any hardware, by pairing it with a famous chaotic system known as the Lorenz attractor.
From fragile photons to practical keys
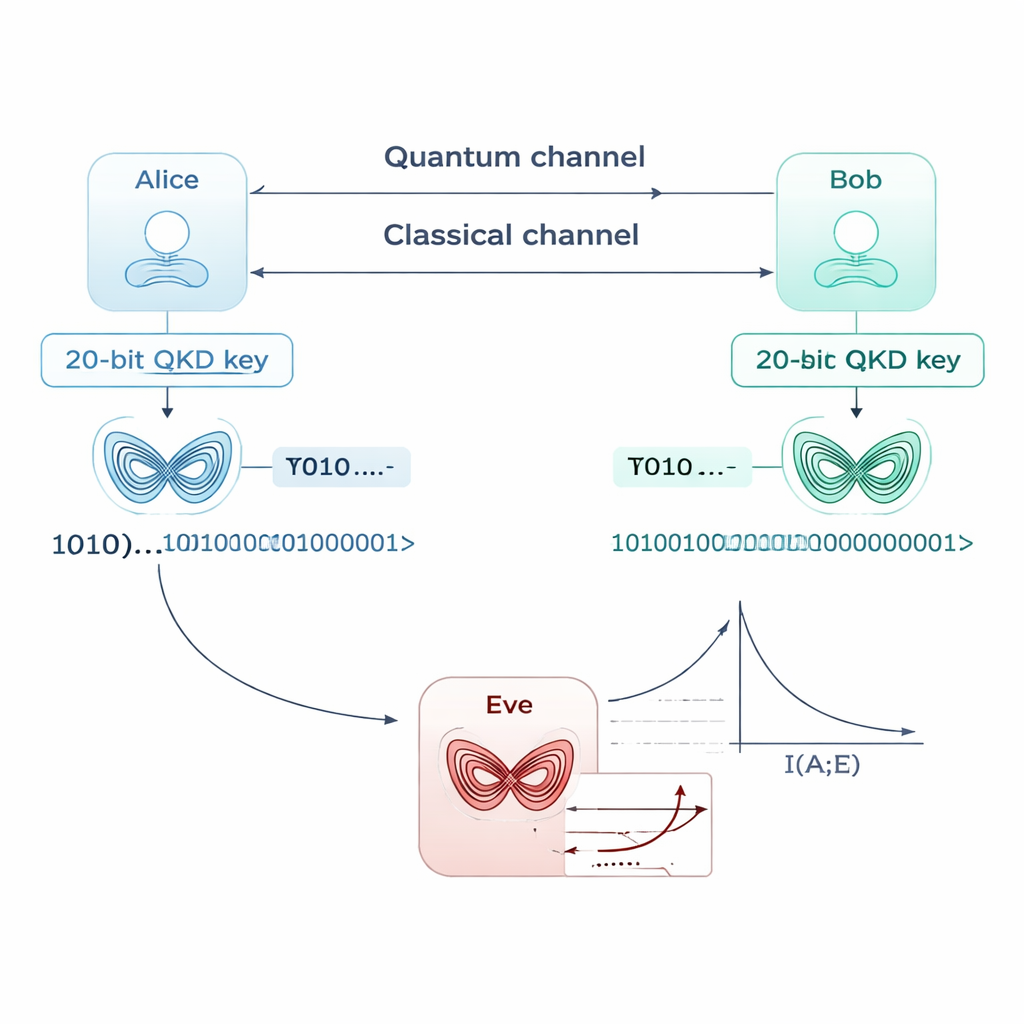
QKD lets two users, traditionally called Alice and Bob, share a secret key by sending quantum particles such as single photons. The laws of quantum physics guarantee that any eavesdropper, Eve, will disturb the particles in a detectable way. In principle this offers information‑theoretic security, stronger than anything based purely on mathematics. In practice, however, real‑world QKD setups struggle with fiber‑optic losses, imperfect detectors, and heavy post‑processing. As a result, many systems manage only a handful of secure bits per second over long distances—far below what is needed to encrypt high‑speed data links or swarms of edge devices in real time.
Turning a tiny seed into a long key
The authors propose a hybrid scheme: first run a standard QKD protocol (such as BB84 or E91) to obtain a short but truly secret digital seed, for example just 20 bits long. Instead of using that seed directly as the final key, Alice and Bob feed it into a software model of the Lorenz system, a set of equations famous for producing the "butterfly" pattern in chaos theory. The seed determines the initial state of this system at very high numerical precision. As the Lorenz equations are simulated step by step, their chaotic motion is sampled and converted into a long stream of bits, using simple quantization rules that map ranges of the system’s variables into 0s and 1s. In simulations, a 20‑bit seed is expanded into more than 20,000 bits within a few milliseconds, effectively multiplying the apparent key rate by hundreds.
Chaos as a shield against eavesdroppers
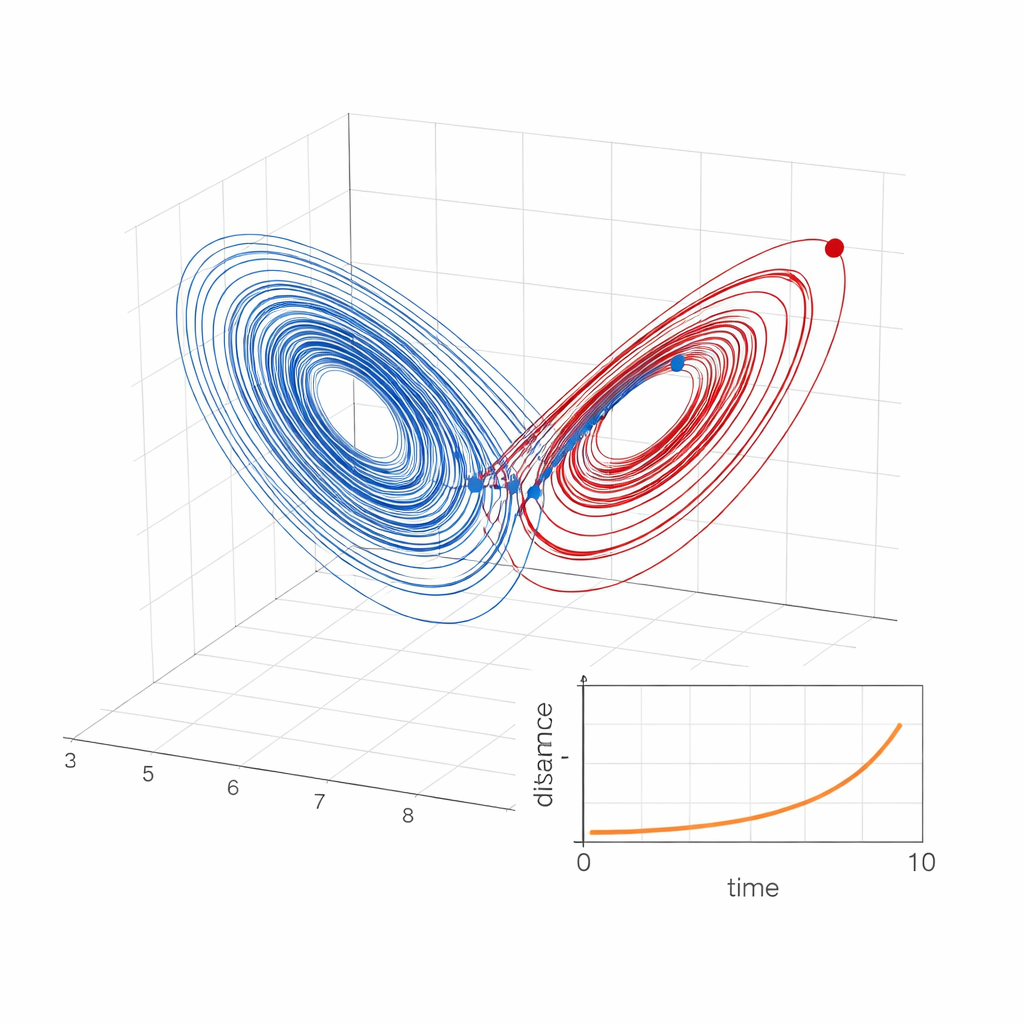
Chaotic systems have an unusual property: two trajectories that start almost—but not exactly—from the same point separate exponentially fast over time. This is quantified by the Lyapunov exponent, which measures how quickly tiny errors blow up. For the Lorenz system, even a difference as small as one part in ten billion in the starting point soon leads to completely different paths. In the proposed scheme, Alice and Bob share the exact same seed, so their simulations remain perfectly aligned and generate identical bitstreams. Eve, however, must guess the seed or reconstruct the initial state from limited, coarsely quantized observations. Any mismatch, no matter how small, causes her simulated trajectory to drift away rapidly. The paper backs this up with mathematical analysis: under reasonable assumptions about chaotic mixing, the mutual information between Eve’s bits and Alice’s bits decays exponentially with time, meaning Eve’s knowledge quickly becomes no better than random guessing.
Randomness tests and speed gains
To be useful in cryptography, the expanded key must not only be unpredictable to attackers but also pass stringent statistical tests. The authors generate million‑bit samples of the chaotic bitstream and analyze them with the widely used NIST randomness test suite. The sequences consistently show near‑maximal Shannon entropy (about 0.99 bits of uncertainty per bit) and pass frequency, runs, and more advanced structure tests at high rates, indicating no obvious patterns. They then compare effective key rates with and without the chaotic layer, using standard models of QKD performance over optical fibers. Because the chaotic expansion happens locally, after the quantum exchange, it sidesteps transmission losses. The simulations suggest a gain of more than two orders of magnitude in usable key throughput across a broad range of distances, without touching the quantum hardware.
What this means—and what it doesn’t
For a general reader, the key message is that chaos can act like a software "amplifier" for quantum‑generated secrets, stretching a small but truly secure key into a much longer one fast enough for demanding applications such as encrypted video or real‑time IoT control. However, the authors are careful to note a subtle point: because the Lorenz equations are fully deterministic, they cannot create new fundamental randomness. In strict information‑theoretic terms, the ultimate security is still capped by the entropy of the original QKD seed. The chaotic layer instead adds a powerful computational barrier, making it extremely hard in practice for an attacker to reconstruct the seed or stay synchronized, even with sophisticated machine‑learning or system‑identification attacks. As a drop‑in software extension that works with existing QKD protocols, this hybrid quantum‑chaotic approach offers a promising path to bring the strong guarantees of quantum cryptography closer to everyday, high‑speed communication needs.
Citation: Danvirutai, P., Wongthanavasu, S., Hoang, TM. et al. Hybrid quantum–chaotic key expansion enhances QKD rates using the Lorenz system. Sci Rep 16, 7327 (2026). https://doi.org/10.1038/s41598-026-37470-6
Keywords: quantum key distribution, chaos-based cryptography, Lorenz attractor, secure communication, key expansion