Clear Sky Science · en
AI-enabled cybersecurity framework for future 5G wireless infrastructures
Why securing 5G matters to everyday life
Fifth‑generation (5G) wireless networks promise blazing‑fast downloads, smoother video calls, smart cities, remote surgery, and self‑driving cars. But the same features that make 5G powerful—connecting huge numbers of devices, pushing computing power out to the network’s edges, and slicing one physical network into many virtual ones—also open new doors to cyberattacks. This paper explores how to protect these future networks so that the services people rely on every day remain safe, trustworthy, and available.
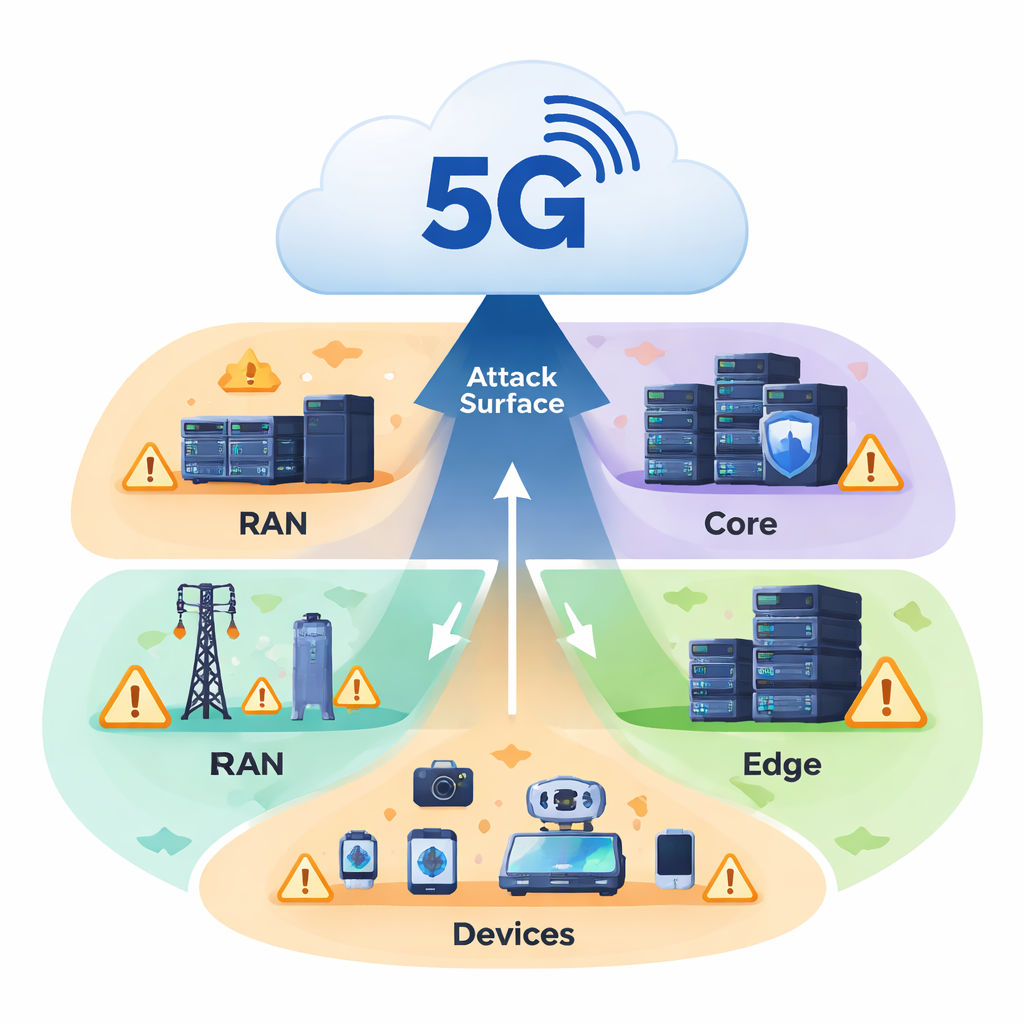
New strengths, new weak spots
Earlier mobile networks mainly focused on faster internet and clearer calls. By contrast, 5G is designed as a flexible digital backbone for everything from home sensors to industrial robots. It uses techniques such as network slicing (multiple virtual networks on shared hardware), edge computing (processing data close to where it is created), and dense deployments of small base stations. These advances greatly boost speed and responsiveness, but also multiply the points where attackers can break in. Insecure low‑cost gadgets, exposed software interfaces, and complex links between devices, radio towers, edge servers, and core data centers together create a much larger attack surface than in 4G.
How attackers could exploit 5G
The authors outline a broad threat landscape that spans both the physical and digital worlds. Physical equipment like antennas and roadside boxes can be vandalized or tampered with. Radio links can be jammed or spoofed so that phones and sensors connect to fake base stations. Inside the network, the heavy use of software and virtualization means a single compromised control program could reroute traffic, spy on users, or disrupt services. Network slices meant for different purposes—say, entertainment streaming and remote surgery—could leak into each other if isolation fails. Billions of inexpensive, poorly secured Internet of Things devices can be hijacked into botnets that flood the network with malicious traffic. On top of this, well‑resourced, state‑sponsored groups may quietly burrow into 5G infrastructure, waiting for the right moment to steal data or cause large‑scale outages.
Smarter defenses through layers and learning
To respond, the paper proposes a multi‑layered security framework that treats 5G as a stack of interconnected zones rather than a single perimeter to guard. At the bottom, every device must prove it is trustworthy before it connects, using secure hardware checks, verified software, and a dynamic “trust score” that is updated as its behavior is observed over time. In the middle, each network slice gets its own tailored security rules and strict separation from other slices, limiting how far an intruder can move. A special control layer watches how virtual network functions talk to each other; any unexpected connection between software components is flagged and can be shut down automatically. At the top, advanced artificial intelligence scans traffic patterns in real time, looking for subtle signs of attacks that older tools might miss.
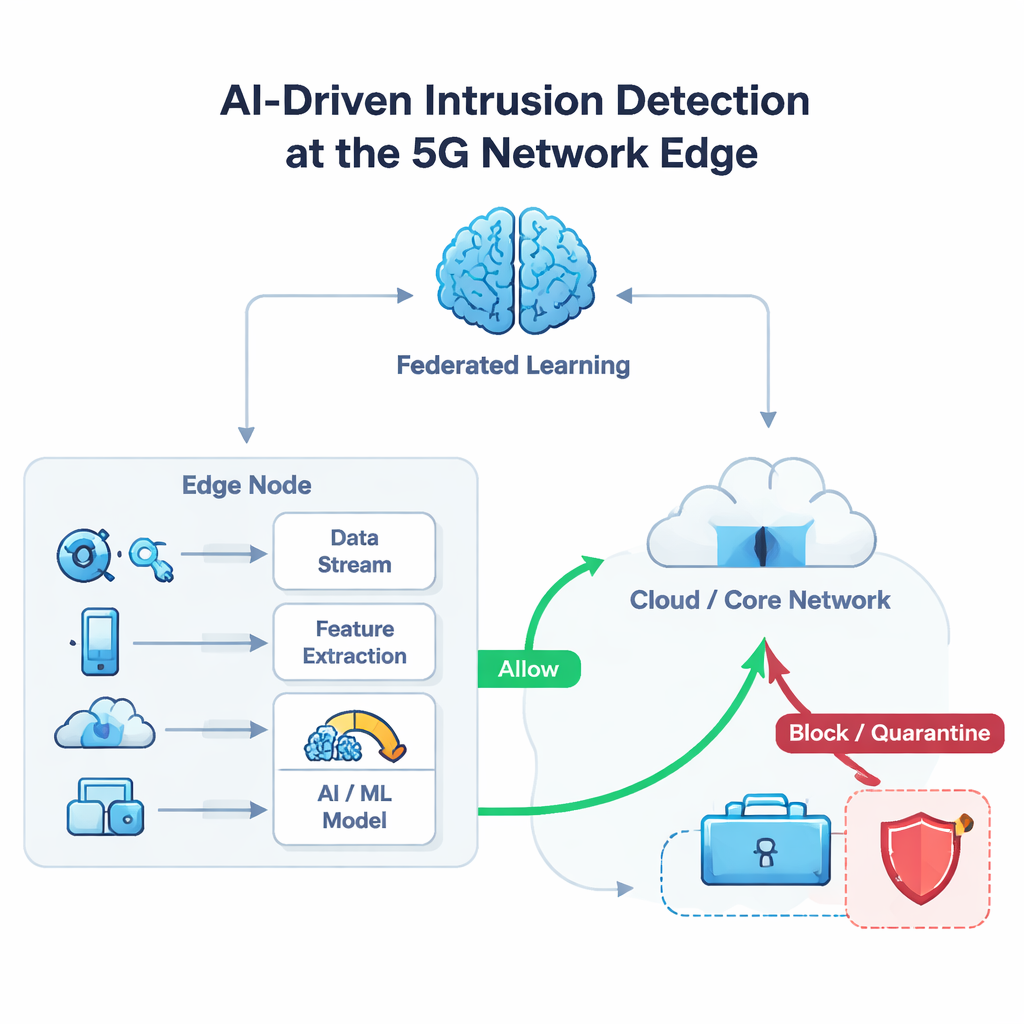
AI watching from the edge
A key idea in the framework is to push intelligence out to the edge of the network, where data is first generated. Edge servers run machine‑learning models that examine streams of packets from nearby devices and assign each flow a probability of being malicious. If the risk looks high, the edge node can instantly block that device, quarantine its traffic, or reroute it, stopping many attacks before they reach the core of the network. To train these models without copying sensitive information into a central database, the system uses federated learning: edge nodes learn from local data, then share only abstract model updates, not raw records. In tests using an emulated 5G environment with up to a million simulated devices and a mix of normal and malicious traffic, this approach detected threats with about 97.6% accuracy while keeping delays as low as 6.5 milliseconds even under active attack.
What this means for the future of connectivity
For non‑experts, the main message is that keeping 5G safe will not depend on a single magic shield, but on many coordinated layers that constantly measure trust, watch for unusual behavior, and react automatically in fractions of a second. The study shows that blending traditional security ideas with AI and careful network design can make future wireless systems both fast and resilient, even when they serve millions of devices at once. The authors argue that such proactive, AI‑enhanced defenses will be essential not only for today’s 5G rollouts but also for tomorrow’s 6G networks, which may need to protect even more demanding applications like holographic meetings and real‑time control of machines across the globe.
Citation: Alam, A., Umer, A., Ullah, I. et al. AI-enabled cybersecurity framework for future 5G wireless infrastructures. Sci Rep 16, 7055 (2026). https://doi.org/10.1038/s41598-026-37444-8
Keywords: 5G cybersecurity, AI-driven threat detection, network slicing security, edge computing security, IoT security