Clear Sky Science · en
A federated deep learning approach for SDN security with quantum optimized feature selection and hybrid MSDC net architecture
Why smarter defenses matter for tomorrow’s networks
Modern digital life runs on massive, programmable networks that quietly decide where every email, video call, and bank transfer goes. These software-defined networks (SDNs) are agile and efficient, but their very flexibility opens new doors for cyber attackers. This paper introduces LightIDS‑SDN, a new intrusion detection system designed to spot and stop attacks on SDNs with high accuracy, while keeping data private and explaining its own decisions. It blends ideas from artificial intelligence, collaboration across many network sites, and even quantum-inspired optimization to build a defense system that can keep up with fast-changing threats.
The promise and peril of programmable networks
SDNs break with the old model of networking by separating the “brain” of the network from the “muscle.” A central controller decides how traffic should flow, while switches and routers simply forward data. This makes it much easier to reconfigure networks on the fly, support cloud services, and serve the exploding number of connected devices. But centralization also creates an attractive single point of failure. If attackers overwhelm or hijack the controller, they can disrupt or spy on the entire network. Traditional security tools, built for slower and more rigid networks, struggle with SDN traffic that is heavier, more varied, and constantly changing. Signature-based tools miss new attacks, while anomaly detectors often raise too many false alarms to be useful.
A lightweight yet powerful security pipeline
LightIDS‑SDN tackles these challenges with a carefully staged pipeline running alongside SDN controllers. It begins by cleaning and preparing traffic data, then applies a quantum-inspired feature selection method that automatically picks the most informative traffic measurements—such as flow timing and control-plane activity—while discarding noise. This step, called DFE‑GQPSO, reduces the number of inputs the system must examine, which speeds up learning and cuts the risk of overfitting to quirks in past data. On top of these refined inputs, the authors build a deep-learning model, MSDC‑Net, which combines three complementary components to capture how attacks unfold over space, time, and context in the network. 
Looking at traffic from multiple angles
The heart of MSDC‑Net is its ability to understand network behavior from different perspectives at once. Transformer layers look across all features to find long-range relationships—such as patterns spread across many flows or devices. Capsule Networks preserve structured patterns, helping the system recognize how small irregularities add up to a larger, suspicious behavior. Bi-directional LSTM units read traffic sequences forward and backward in time, capturing how earlier and later events combine into an attack. This multi-view design allows LightIDS‑SDN to distinguish normal bursts of activity from coordinated floods, password-guessing attempts, or stealthy probing that might precede a major breach.
Collaborative learning without sharing raw data
Real networks are spread over many sites owned by different organizations, which often cannot or will not pool raw traffic data for privacy and regulatory reasons. LightIDS‑SDN addresses this with federated learning: each SDN controller trains its own local copy of the model on its own data, then sends only the updated model parameters—not the underlying traffic—to a central server. That server averages the updates and sends back an improved global model to all participants. In tests that simulated multiple controllers, this collaborative process reached nearly the same accuracy as training on all data in one place, while preserving data privacy. The authors also show that distributing training across clients reduces per-node training time, even if it introduces some communication overhead. 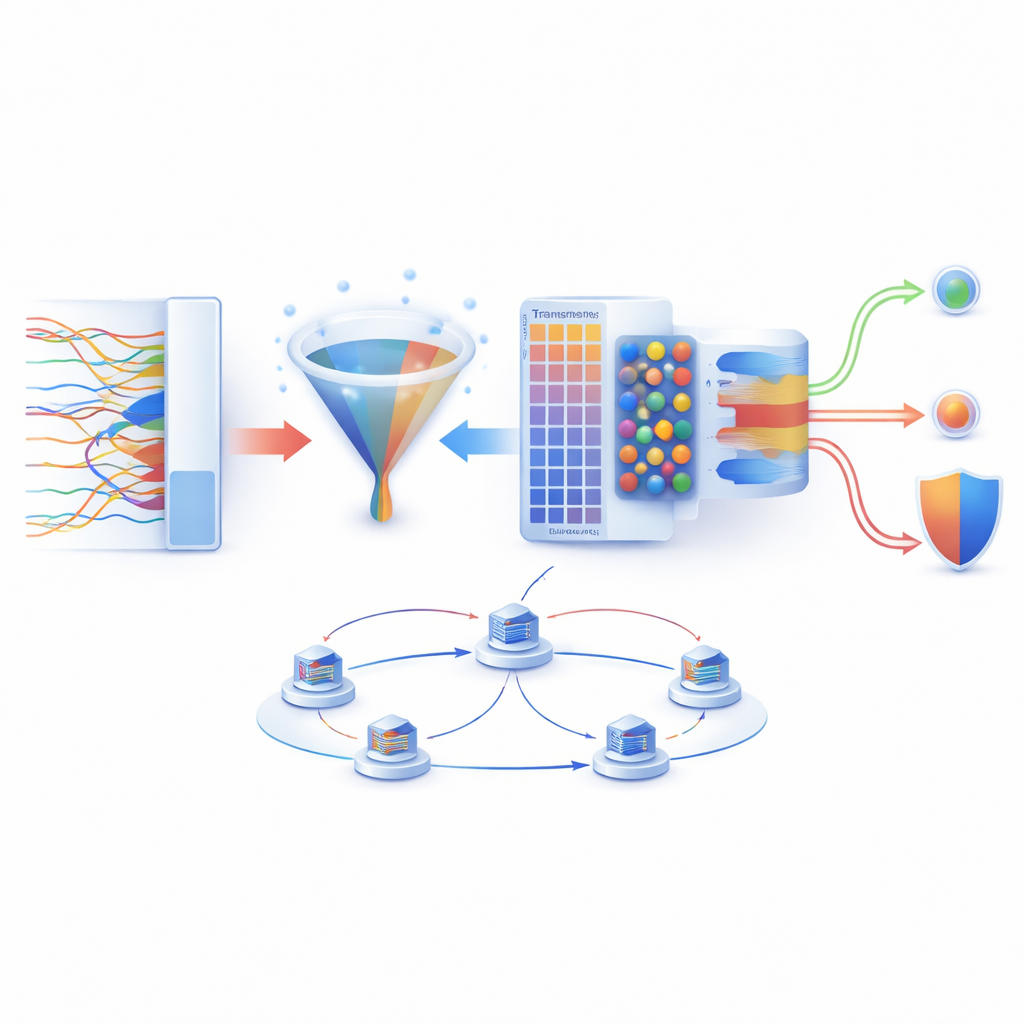
Opening the black box for human analysts
A common complaint about deep-learning security tools is that they are “black boxes” that provide alerts without reasons. LightIDS‑SDN addresses this with an explainability module called Explain‑Edge. It uses SHAP values to show which traffic features most influenced a particular decision, and Grad‑CAM-style visualizations to highlight which internal patterns the model relied on. In experiments, the most influential features matched what network experts already consider important, such as flow duration and controller-related message rates. This alignment helps build trust that the system is learning meaningful signals rather than latching onto accidental correlations.
What the results mean in practice
Tested on a large, SDN-specific dataset containing millions of benign and malicious flows across nine attack types, LightIDS‑SDN achieved about 99% accuracy and similarly high precision and recall, outperforming several popular machine-learning and deep-learning alternatives. It did so while using fewer input features, supporting distributed training, and offering interpretable outputs. For a lay reader, the takeaway is that the authors have built a security “copilot” for modern networks: it watches traffic closely, learns from many locations without copying sensitive data, and can explain why it believes something is wrong. While there are still challenges—such as computational cost and tuning for extreme real-time loads—this work points toward future network defenses that are not only smarter and more private, but also more transparent and easier for humans to trust.
Citation: Rohith, S., Logeswari, G., Tamilarasi, K. et al. A federated deep learning approach for SDN security with quantum optimized feature selection and hybrid MSDC net architecture. Sci Rep 16, 8038 (2026). https://doi.org/10.1038/s41598-026-37289-1
Keywords: software-defined networking security, intrusion detection system, federated learning, deep learning cybersecurity, network traffic analysis