Clear Sky Science · en
Non-local attention enhanced deep learning for robust cyberattack detection in industrial IoT-based SCADA systems
Why protecting smart industry matters
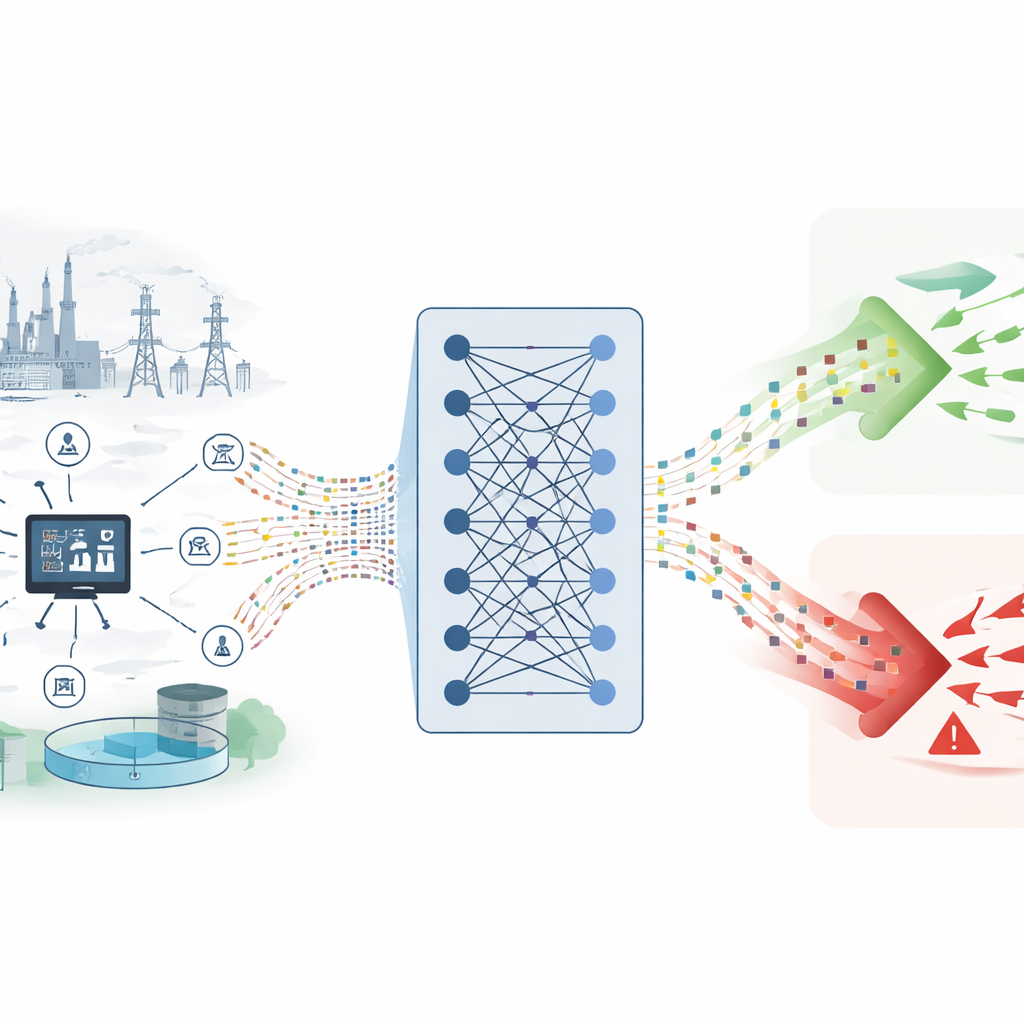
Modern factories, power grids, and water systems increasingly rely on internet-connected sensors and controllers to keep everything running smoothly. This web of devices, often called the industrial Internet of Things, gives operators powerful real-time insight—but it also opens the door to hackers. The paper behind this summary explores a new artificial-intelligence system designed to spot even the rarest and stealthiest cyberattacks on these vital networks before they can cause blackouts, poisoned water, or halted production lines.
How today’s industry is wired together
In many critical sectors, a central control platform known as SCADA oversees thousands of field devices: programmable logic controllers that run pumps and turbines, sensors that measure pressure and flow, and remote units that switch breakers or valves. These components talk constantly over industrial networks, feeding data to control rooms and receiving commands in return. Because these systems are now widely connected—sometimes even reachable from the public internet—they have become attractive targets. A single weak or outdated device, with limited processing power and poor security, can provide a foothold for an attacker to disrupt an entire plant or region.
Why old defenses fall short
Traditional defenses for these networks largely depend on fixed rules: firewalls that block traffic matching known patterns and intrusion detection tools that look for signatures of familiar malware. Such static methods struggle against constantly changing threats. Modern attackers use previously unseen “zero-day” tricks, long-running stealth campaigns, and subtle manipulations of sensor readings or control signals that can slip past rule-based checks. At the same time, human analysts cannot watch the torrent of industrial network data in real time. These limits have driven interest in machine learning and deep learning, which can learn patterns of normal behavior and highlight unusual activity automatically.
A smarter way to watch network traffic
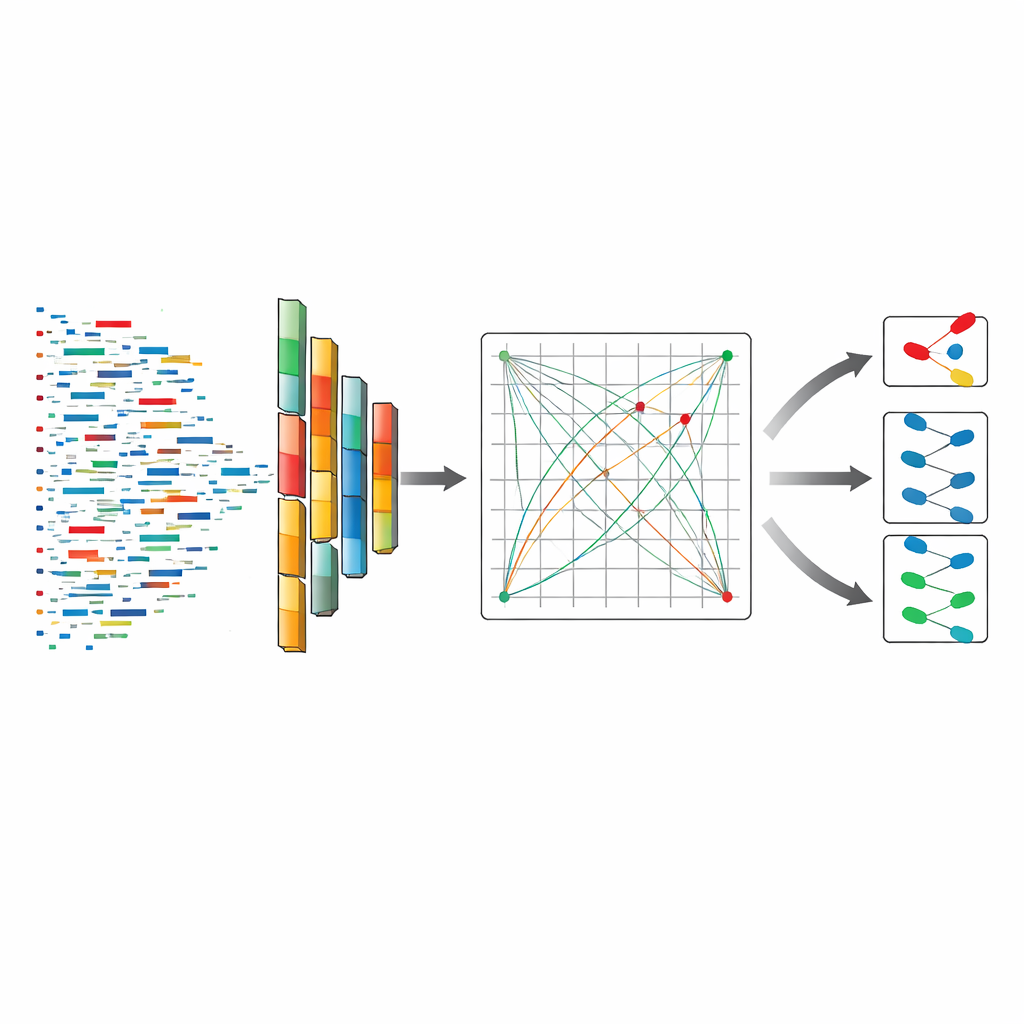
The authors present a deep learning model called DeepNonLocalNN, built specifically for industrial IoT and SCADA traffic. Instead of treating each data point in isolation, the model looks at patterns across time and across many different measurements at once—such as packet sizes, timing gaps, and data rates between devices. It starts with convolution layers that are good at discovering local patterns, like repeated bursts from a misbehaving device. On top of that, it adds “non-local attention” blocks, which allow the model to weigh relationships between distant events in the traffic stream. This combination helps it detect subtle, spread-out signs of malicious behavior that simpler models might miss.
Testing the model in a realistic setting
To judge how well DeepNonLocalNN works, the researchers used a large public dataset that mimics a real industrial network, containing more than a million examples of both everyday and malicious traffic. Most of the data looks normal, while only a tiny fraction corresponds to serious attacks like hidden backdoors or carefully crafted command injections. This imbalance mirrors reality: attacks are rare but critical. The team compared their model with several established deep learning approaches, including recurrent networks that track sequences and other attention-based architectures. They measured not just overall accuracy, but also how well each method recognized every type of attack, especially the rare ones.
What the results reveal
DeepNonLocalNN performed exceptionally well. It correctly classified almost all traffic, reaching near-perfect scores on standard accuracy and detection metrics. More importantly, it did far better than competing models at spotting the scarcest but most dangerous attack types. While other methods often mis-labeled these rare cases as normal, the new model detected most of them, thanks to its ability to combine fine-grained local patterns with a big-picture view of the entire traffic flow. The authors also used specialized training tricks to counter the data imbalance, ensuring that the model did not simply learn to favor the overwhelmingly common normal class.
What this means for everyday life
For non-specialists, the key takeaway is that smarter algorithms can offer a much stronger early-warning system for the critical infrastructure we depend on—power, water, transportation, and manufacturing. DeepNonLocalNN shows that by letting an AI model learn both local details and broad context in network behavior, it becomes possible to catch even stealthy and uncommon cyberattacks before they cause physical harm. The work is not yet plug-and-play for every plant—future efforts must trim its computing demands and test it on more real-world environments—but it points toward intrusion detection tools that are fast, adaptable, and far more capable than the rule-based defenses of the past.
Citation: Yilmaz, M.T., Polat, O., Algul, E. et al. Non-local attention enhanced deep learning for robust cyberattack detection in industrial IoT-based SCADA systems. Sci Rep 16, 7857 (2026). https://doi.org/10.1038/s41598-026-37146-1
Keywords: industrial IoT security, SCADA cyberattacks, intrusion detection, deep learning, non-local attention