Clear Sky Science · en
Hopf-Hopf bifurcation analysis and chaotic delayed-DNA audio encryption using cubic nonlinear optoelectronic oscillator
Locking Sound with Light and DNA
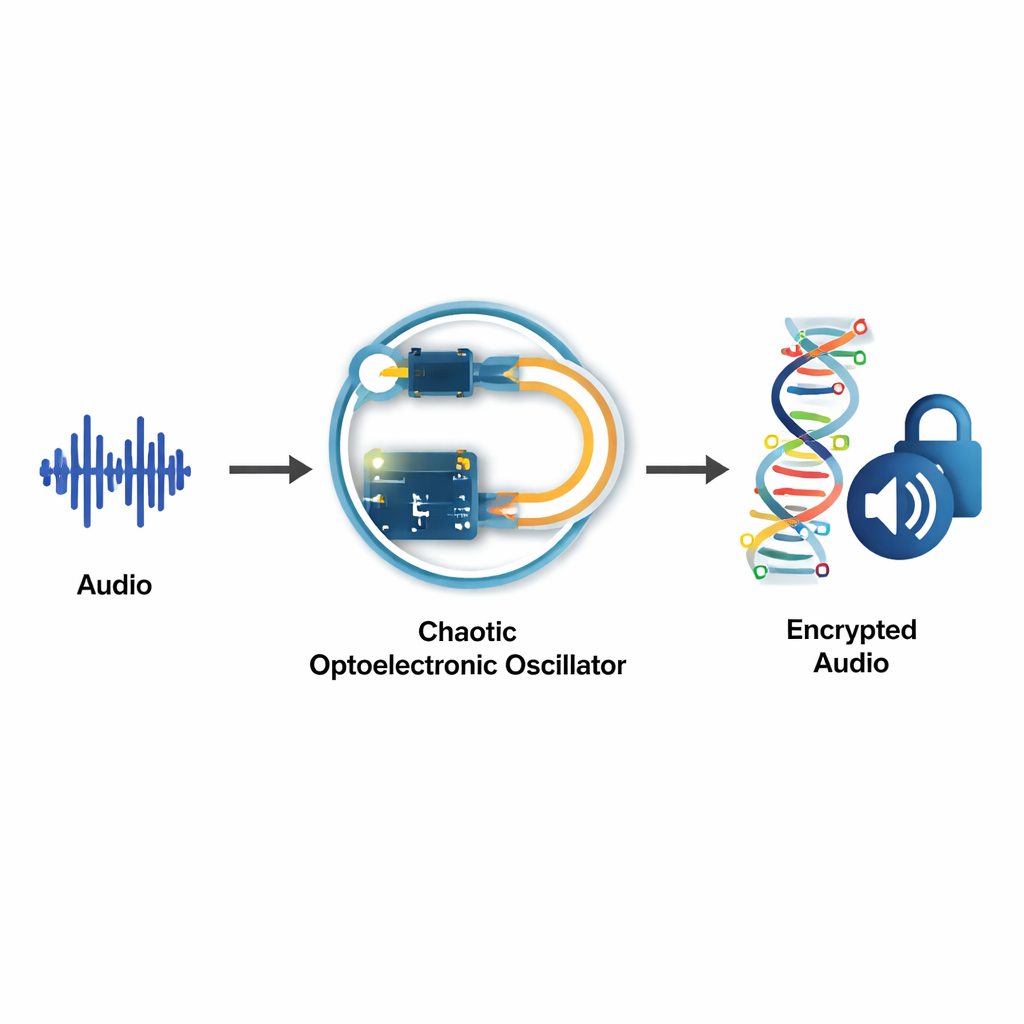
Streaming music, online calls, and voice messages move through the internet as easily as text, but protecting this kind of rich audio data without slowing everything down is hard. This study explores an unusual idea: using the wild, seemingly random behavior of a light‑based electronic circuit, together with DNA‑inspired coding, to scramble audio so thoroughly that it becomes useless to an eavesdropper—yet can still be perfectly recovered by someone with the right key.
A Circuit That Behaves Like a Storm
At the heart of the work is an optoelectronic oscillator, a loop that mixes light and electronics to produce very stable signals used in radar and communications. When engineers add a time delay into this loop and let some nonlinear effects grow, the circuit stops behaving in a simple, clock‑like way. Instead, it can swing between steady tones, gentle rhythms, and fully chaotic, storm‑like oscillations that are extremely sensitive to tiny changes in settings. The authors analyze a particular "cubic" version of this oscillator and show how, at special operating points called double Hopf bifurcations, two distinct rhythms collide and unlock a whole zoo of behaviors: periodic beats, quasi‑periodic patterns, and full chaos. This analysis is not just academic; it identifies precise parameter choices where the circuit produces rich, unpredictable signals that are ideal ingredients for cryptographic keys.
Turning Chaotic Motion into Secret Keys
Using advanced mathematical tools and numerical software, the team maps out where in parameter space these complex motions appear and remain stable. They then simulate the oscillator as a delayed differential system and record its outputs as time series. After normalizing these signals, they convert them into several key sequences: one sequence controls how elements of the data are shuffled, another determines how values are substituted, and a third decides whether certain symbols are flipped. Because the chaotic motion is so sensitive, even a microscopic tweak to any parameter completely changes these key streams, making it essentially impossible for an attacker to guess or reproduce them without perfect knowledge of the system.
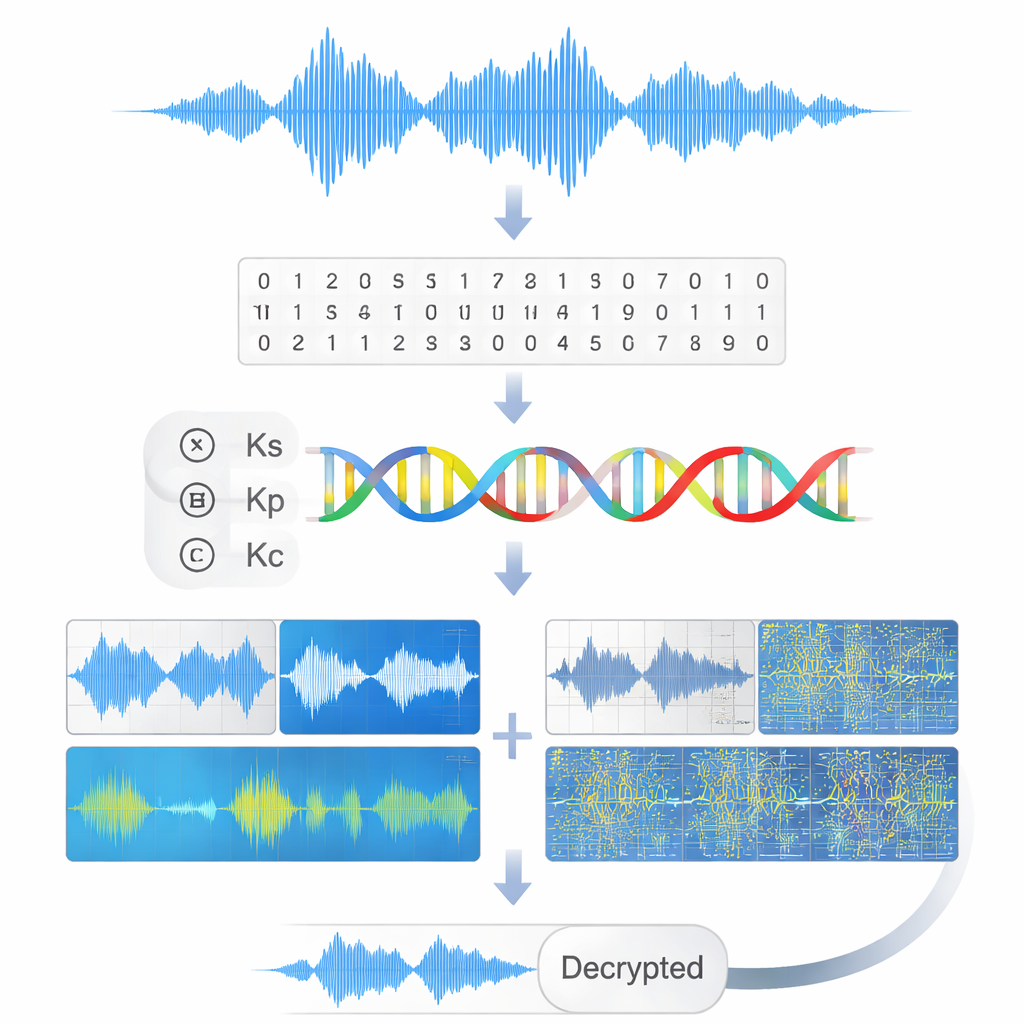
Borrowing Ideas from DNA to Scramble Sound
To act on real audio, the method first converts an input sound file to a uniform format—single channel, fixed sampling rate—and expresses it as 8‑bit numbers. These bits are then grouped into pairs and mapped onto the four DNA bases A, C, G, and T. Working with this synthetic "DNA" sequence, the chaotic keys drive three steps: permutation (reordering the bases so nearby samples lose their relationship), arithmetic‑style substitutions (shifting each base by a chaotic amount, like walking around a four‑letter alphabet), and conditional complementation (swapping bases in a way that mimics biological pairing). After these operations, the DNA sequence is mapped back to bits and then to audio samples, producing an encrypted sound that looks noise‑like in both its waveform and its time–frequency picture.
Checking Security Without Losing Quality
The authors subject their scheme to a battery of tests that are standard in modern cryptography and signal processing. They measure entropy, a gauge of randomness, and find values extremely close to the ideal limit for 8‑bit audio, indicating that the encrypted signals reveal almost no structure. Correlations between neighboring samples, which are normally strong in natural sound, drop essentially to zero after encryption. Histograms of sample values become nearly flat, showing that amplitudes are evenly spread rather than clustered. Differential tests, which ask how much the ciphertext changes when the original audio is altered by just one sample, show that more than 99.9% of the encrypted data is affected and the average change is around the theoretical optimum. At the same time, when the correct keys are used, the decrypted audio matches the original with vanishingly small numerical errors and very high signal‑to‑noise ratios, meaning the ear would notice no degradation.
Why This Matters for Future Secure Audio
In everyday terms, the study demonstrates that a physically realizable light‑and‑electronics circuit, carefully tuned into a chaotic regime, can serve as an exceptionally strong source of randomness, and that DNA‑style encoding provides a flexible, layered way to spread that randomness across an audio signal. Together, they form an encryption method that is both hard to attack and capable of restoring sound perfectly. With further optimization and hardware implementation, such schemes could underpin secure voice calls, protected media streaming, and resilient communication links in demanding settings like satellites and drones, where both speed and security are at a premium.
Citation: Aiyaz, M., Yan, J., Abbasi, A.Z. et al. Hopf-Hopf bifurcation analysis and chaotic delayed-DNA audio encryption using cubic nonlinear optoelectronic oscillator. Sci Rep 16, 6201 (2026). https://doi.org/10.1038/s41598-026-37131-8
Keywords: audio encryption, chaotic oscillators, DNA coding, secure communications, bifurcation dynamics