Clear Sky Science · en
Parametric action of homomorphic image of modular group and it’s application in image encryption
Why hiding pictures is harder than it looks
Every day we send photos across the internet—medical scans, ID documents, family snapshots—often without thinking about who else might see them. Traditional encryption methods were designed for text and numbers, and can struggle with the huge size and structure of images. This paper introduces a mathematically sophisticated way to scramble images so thoroughly that they become resistant to many modern hacking techniques, while still being efficient enough for real-world use.

From simple locks to smarter digital keys
Most modern encryption for data, including images, relies on block ciphers: algorithms that chop information into small blocks and transform them repeatedly. At the heart of many block ciphers is an S-box, or substitution box, which takes a tiny chunk of data (often one byte) and swaps it for another value according to a predefined table. This step is the main source of "nonlinearity"—the controlled chaos that makes it difficult for an attacker to work backwards from encrypted data to the original. If the S-box is poorly designed, the entire cipher becomes easier to crack. The authors focus on building stronger S-boxes tailored for images, where patterns and correlations between neighboring pixels can leak information if not carefully disrupted.
Using exotic geometry to scramble data
The key innovation of the paper is to construct S-boxes from a rich branch of abstract algebra called generalized triangle groups, which are related to the well-known modular group in number theory. Instead of relying on simple arithmetic formulas or chaotic maps alone, the authors study how these groups act on projective lines over finite fields—mathematical structures that organize numbers in a highly symmetric but intricate way. By carefully "parameterizing" these actions, they obtain coset diagrams: graph-like pictures that describe how elements are permuted. Each choice of parameter leads to a different pattern of cycles and connections, which in turn defines a distinct S-box. Because the resulting permutations are less regular and more varied than those produced by classical groups, they offer fewer predictable structures for attackers to exploit.
Designing a stronger substitution box
Building on this algebraic framework, the authors generate an 8×8 S-box (mapping 256 possible input values to 256 outputs) over the finite field with 2⁸ elements, the same size used in the widely deployed AES cipher. They base the substitution on repeated applications of a specific group word, denoted mathematically as a product of transformations like xyxy², and then remove fixed points and singularities to avoid weak spots. The resulting S-box is thoroughly tested using standard cryptographic criteria: nonlinearity (how far it is from any simple linear rule), avalanche effect (how much the output changes when a single input bit is flipped), bit independence (whether output bits behave independently), differential uniformity (resistance to attacks based on input-output differences), and linear approximation probability. Across these measures, their S-box matches or outperforms many recently proposed designs, achieving high nonlinearity, low bias in linear trails, and a favorable profile against differential attacks.
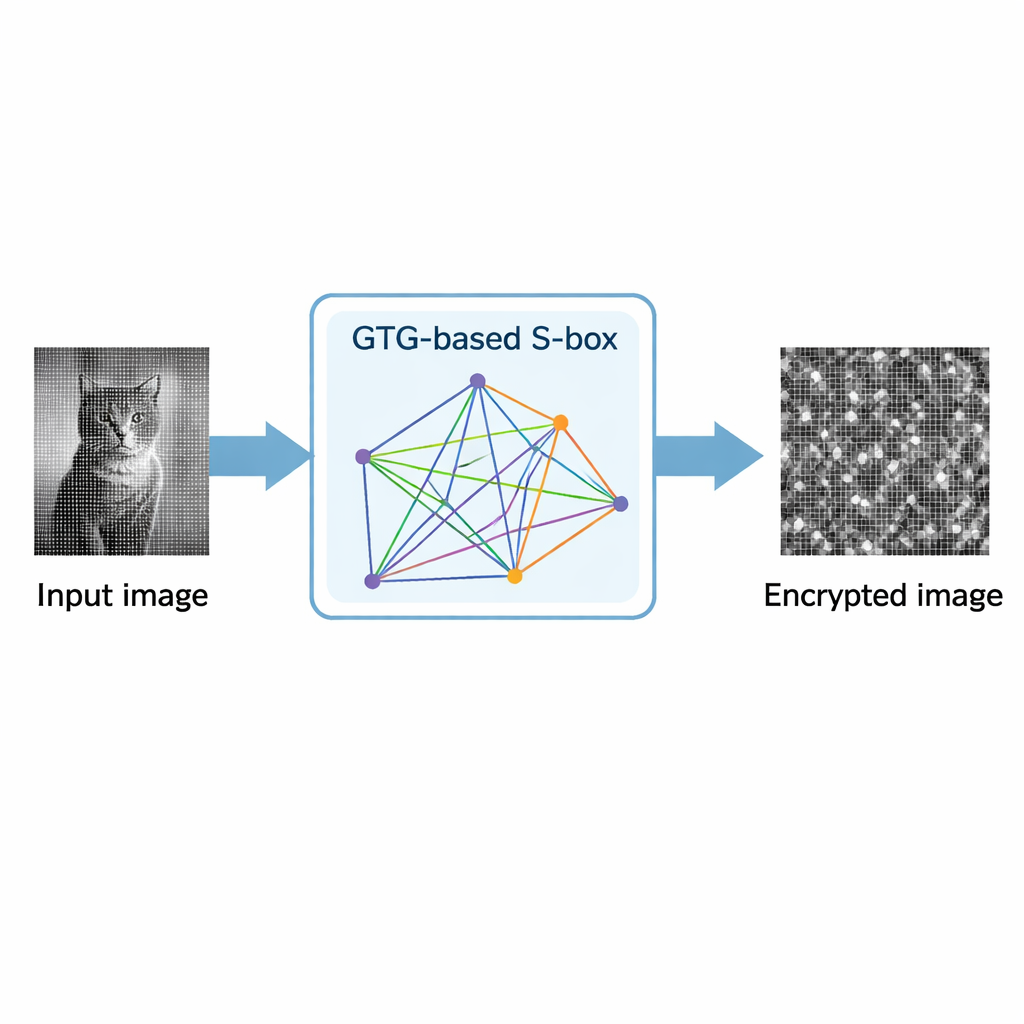
Putting the new design to work on images
To show that their S-box is useful in practice, the researchers embed it in a grayscale image encryption scheme. The process uses the S-box repeatedly: first to shift and substitute pixel values, and then in a mixing step that spreads small changes across the whole image. They test the method on a sample photograph and analyze the result statistically. The encrypted image’s pixel histogram is nearly flat, indicating that brightness values are uniformly distributed and no visual pattern remains. Measures of correlation between neighboring pixels drop from very high (close to 1) in the original picture to almost zero in the cipher image. Other standard indicators, such as entropy (close to the ideal value of 8 bits), NPCR (about 0.9959), and UACI (about 0.3348), show that even tiny changes in the original image lead to large, unpredictable changes after encryption, making differential and statistical attacks extremely difficult.
What this means for everyday security
In simple terms, the paper shows that ideas from deep, seemingly abstract mathematics can be harnessed to build very practical defenses for digital images. By using generalized triangle groups to generate S-boxes, the authors create a flexible family of substitution tables with strong scrambling power and very few detectable patterns. Their prototype image encryption scheme demonstrates both high security and reasonable efficiency, suggesting that such algebraic constructions could become a robust alternative to more traditional or purely chaos-based designs. For users, this kind of work helps ensure that sensitive images—from medical scans to personal photos—can be protected against increasingly sophisticated attacks.
Citation: Rafiq, A., Bibi, S., Abbasi, A.Z. et al. Parametric action of homomorphic image of modular group and it’s application in image encryption. Sci Rep 16, 6264 (2026). https://doi.org/10.1038/s41598-026-37082-0
Keywords: image encryption, substitution box, generalized triangle groups, cryptography, finite fields