Clear Sky Science · en
A multi-layered cryptographic trust reinforcement model against AI-driven threat propagation and zero-day cloud vulnerabilities in healthcare data ecosystems
Why smarter cyber defences matter for patients
Modern medicine runs on data. Every heartbeat from a wearable sensor, every scan, and every clinic visit now passes through hospital clouds and connected devices. This digital nervous system brings faster diagnoses and remote care—but it also creates new openings for cyberattacks that can leak private records or disrupt life‑support equipment. This paper explores a next‑generation security blueprint designed specifically for healthcare, aiming to keep care running safely even as attackers use artificial intelligence and previously unknown software flaws to break in.
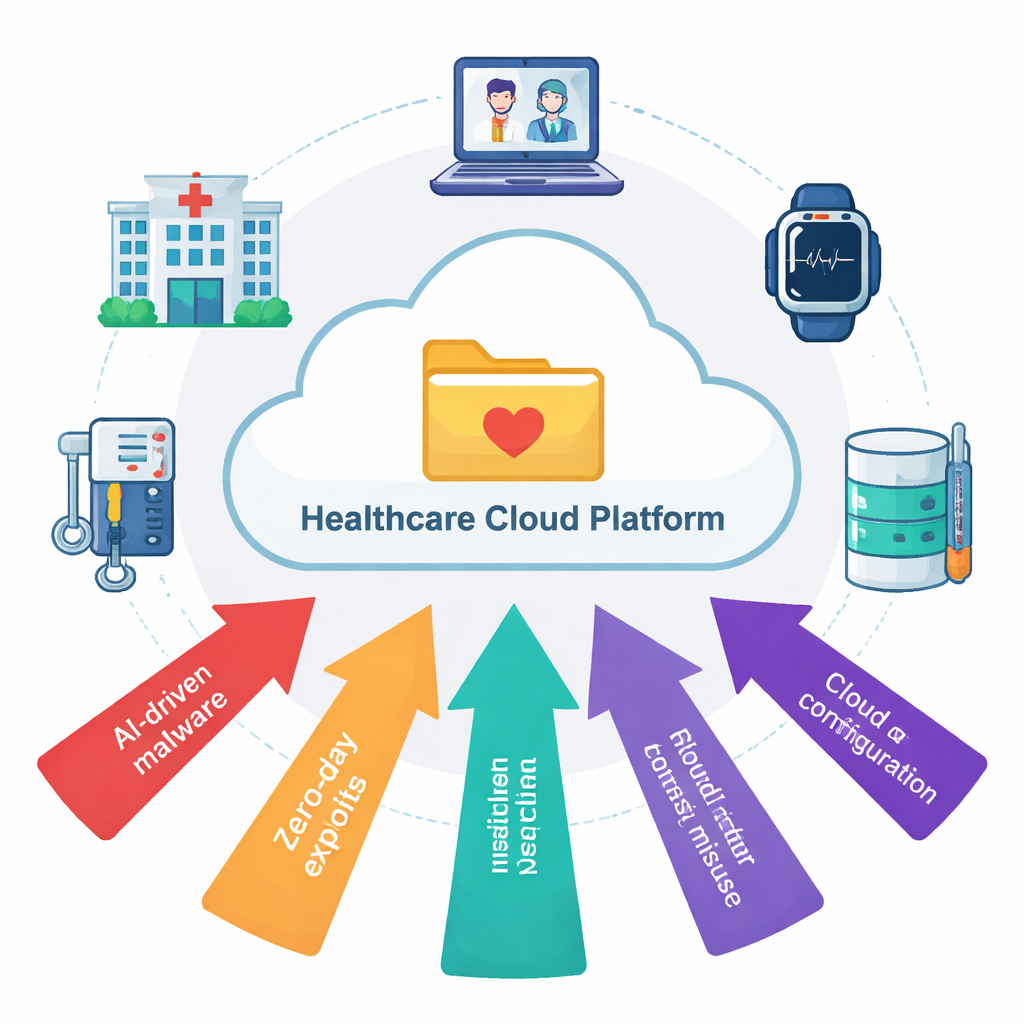
The growing digital attack surface in hospitals
Today’s healthcare systems connect electronic health records, bedside monitors, imaging machines, telehealth apps, and insurance platforms through the cloud. That interconnectedness is powerful but fragile. Criminals and hostile actors increasingly use AI to scan for weaknesses, craft smarter malware, and move laterally across networks at machine speed. Even more worrying are “zero‑day” vulnerabilities—hidden software bugs that no one has patched yet, but which attackers can quietly exploit. In this setting, traditional point solutions such as simple firewalls or signature‑based virus scanners are not enough, especially when clinicians cannot tolerate slow systems or outages during critical care.
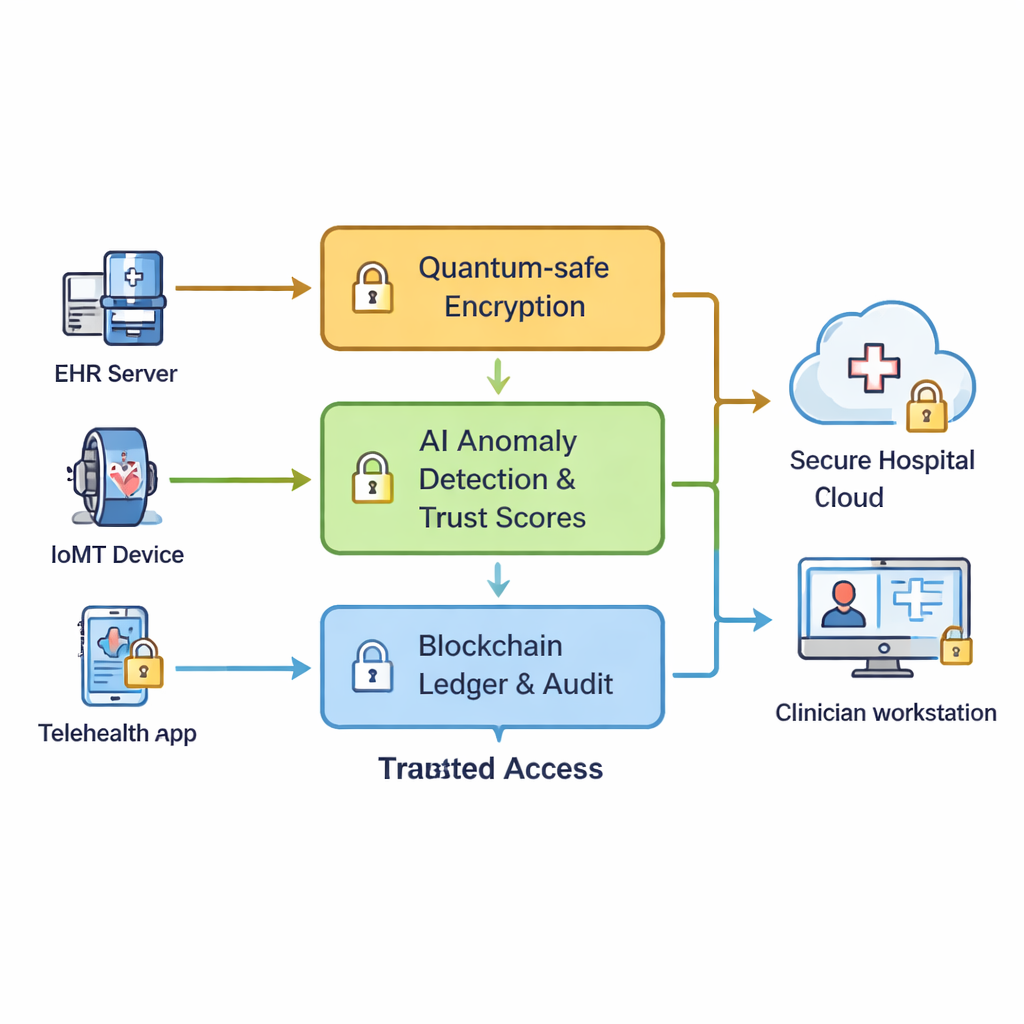
Stacking several strong locks instead of one
The authors propose a Multi‑Layered Cryptographic Trust Reinforcement (MCTR) framework that treats healthcare cybersecurity as a coordinated system rather than a pile of disconnected tools. First, all sensitive data—such as lab results or intensive‑care device readings—is encrypted twice. One layer uses efficient, well‑known methods suited to high‑volume traffic, while a second layer relies on “post‑quantum” techniques intended to stay secure even if future quantum computers become able to crack today’s codes. This dual wrapping is designed so that if one lock is ever broken, the other still protects patients’ records.
Letting machines spot trouble and score trust
Encryption alone cannot stop an insider who already has access, or malware that is cleverly disguised as normal traffic. To address this, the framework embeds AI models at many points in the network. These models continuously watch login patterns, data access behaviour, and device traffic, learning what “normal” looks like for each hospital node. When behaviour starts to drift—say, an infusion pump suddenly talks to an unfamiliar server—the AI assigns a higher anomaly score. Each system in the network receives a dynamic trust score that rises with clean history and falls when suspicious patterns appear. Low‑trust devices or servers can be automatically moved into a monitored or quarantine zone, with keys rotated and permissions reduced before damage spreads.
Using shared ledgers to agree on what really happened
Because hospitals and clinics often share data across organizations and cloud providers, the framework avoids relying on a single central administrator. Instead, it uses a permissioned blockchain—a shared ledger run by approved healthcare partners—to log key security events. Every change in trust scores, cryptographic keys, or suspected zero‑day incidents is written as a tamper‑evident record that all parties can verify. When several sites independently detect similar strange behaviour, they combine their findings through a consensus process and, if needed, trigger network‑wide defences such as accelerated key rotation or tighter access rules. This shared view makes it much harder for attackers—or insiders—to hide traces of an intrusion.
How well does the layered approach work?
To test practicality, the authors built large simulated healthcare networks with up to 250 nodes, using real IoT‑based hospital traffic datasets that include both normal activity and varied attacks. They compared their framework against seven existing approaches, from simple intrusion detection systems to AI‑only and blockchain‑only schemes. Across these trials, MCTR detected 95–98% of threats while keeping false alarms below 2.5%, meaning fewer pointless alerts that might distract IT teams or interrupt care. The blockchain layer sustained over 130 security‑related transactions per second, enough for busy hospital environments, and the system blocked more than 91% of engineered zero‑day attack attempts, all while keeping added delays within ranges compatible with real‑time clinical use.
What this means for everyday care
For non‑specialists, the takeaway is that protecting digital medicine now requires more than a single lock or a single watchdog. This work outlines how a carefully tuned combination of strong encryption, constantly learning AI monitors, and shared, auditable records can work together to keep patient data confidential and medical systems available, even as attackers become more automated and inventive. While real‑world rollout will still face hurdles—such as the need for high‑quality training data and computing power on constrained devices—the study shows that such a multi‑layered defence is both technically feasible and markedly more effective than today’s fragmented protections in guarding healthcare’s most sensitive information.
Citation: Rani, M., Lavanya, R., Shahnaz, K.V. et al. A multi-layered cryptographic trust reinforcement model against AI-driven threat propagation and zero-day cloud vulnerabilities in healthcare data ecosystems. Sci Rep 16, 7150 (2026). https://doi.org/10.1038/s41598-026-36966-5
Keywords: healthcare cybersecurity, AI-driven attacks, zero-day vulnerabilities, blockchain security, quantum-resistant encryption