Clear Sky Science · en
Towards understanding the applicability of runtime moving target defense for the internet of things and cyber physical systems
Why tiny computers need big defenses
From smart thermostats to industrial robots, everyday life now depends on small connected devices that quietly measure, control, and automate our world. But these same gadgets can be hijacked by hackers who exploit long‑known software flaws to take control. This paper explores whether a powerful security trick, called moving target defense, really works on the modest hardware that powers most Internet of Things (IoT) and cyber‑physical systems (CPS) — and what that means for keeping our increasingly automated world safe.
A moving bullseye for hackers
Traditional security tools such as firewalls or antivirus mostly react after an attack has already started. Moving target defense tries a different tactic: it constantly changes key parts of a system so that attackers can never be sure where to aim. The specific technique studied here is Address Space Layout Randomization (ASLR), which shuffles where programs and libraries sit in memory each time they run. That way, even if attackers know there is a weak spot, they cannot easily find its exact address again. ASLR is now standard on major operating systems, but its behavior on small, resource‑limited devices — the kind commonly found in IoT and CPS — has not been well understood.
Putting three systems to the test
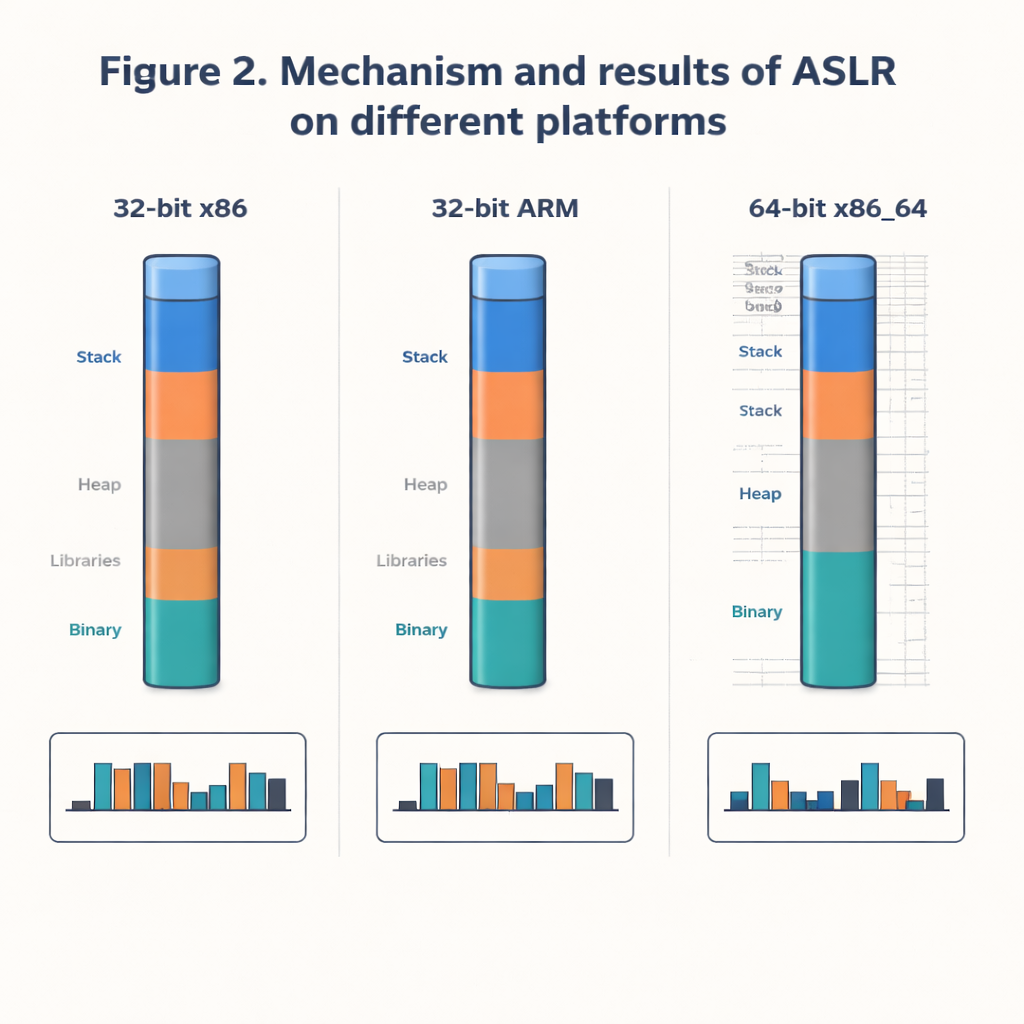
The authors compare how well ASLR works on three Linux‑based setups: a 64‑bit Kali Linux system on a typical Intel processor, and two 32‑bit ARM systems running Raspberry Pi OS and OpenWRT, which are closer to what you would find in edge devices, routers, and gateways. Rather than trying to break in blindly, they take a scientist’s view: they repeatedly record where a common system library (libc) lands in memory, building large datasets of real addresses. They then look at how widely those addresses spread out, how individual bytes of each address change from run to run, and how unpredictable the overall pattern is using a measure called entropy. This lets them quantify how hard it would be for an attacker to guess the right location.
How random is “random enough”?
The results show a sharp contrast between the big 64‑bit system and the 32‑bit devices. On 64‑bit Kali Linux, the addresses are spread almost uniformly across a wide range: most bytes in the address change a lot, very few locations repeat, and a statistical test confirms that the choices look close to truly random. For an attacker, that means a huge search space and little hope of guessing the right spot quickly. On the 32‑bit systems, by contrast, only a small set of 256 distinct addresses actually appear, even when 100,000 samples are collected. Several bytes barely change at all, largely because of architectural constraints and how memory pages must be aligned. In practice, that means an attacker might need only a few hundred tries — not millions or billions — to hit the right address.
Real‑world attack and small costs
To see whether these differences matter in practice, the researchers implement a type of control‑hijacking technique known as a return‑oriented programming (ROP) attack on all three systems. When a key hardening option called Position Independent Executable (PIE) is turned off, the attack succeeds: the program’s normal flow is diverted to hidden functions chosen by the attacker. But once PIE is enabled, combining with ASLR to make even the main program’s location movable, the attack reliably crashes instead of taking over — on both the powerful 64‑bit machine and the modest 32‑bit ARM devices. Measurements also show that enabling ASLR, stack protections, and non‑executable memory adds only a small overhead in memory usage and execution time, on the order of one percent.
What this means for everyday devices
The study concludes that although ASLR on 32‑bit ARM systems is mathematically weaker and less random than on 64‑bit desktops and servers, it still offers protection comparable to older 32‑bit PCs and can successfully block straightforward attacks when combined with other built‑in defenses. For the smallest IoT sensors, ASLR is often impossible because the hardware lacks the necessary memory features; there, other techniques like secure boot and lightweight encryption are better suited. But for edge devices such as routers and Raspberry Pi‑class boards, enabling ASLR, PIE, and related safeguards is both practical and worthwhile. Moving these platforms toward 64‑bit architectures, and pairing ASLR with other moving‑target tricks at the network and software levels, can significantly raise the bar for attackers trying to turn everyday objects into weapons.
Citation: Gurung, D., Pradhan, M.P. & Gurung, S. Towards understanding the applicability of runtime moving target defense for the internet of things and cyber physical systems. Sci Rep 16, 5907 (2026). https://doi.org/10.1038/s41598-026-36797-4
Keywords: moving target defense, ASLR, Internet of Things security, cyber-physical systems, buffer overflow attacks