Clear Sky Science · en
A lattice-integrated AES framework for ultra-secure biometric protection on resource-constrained edge devices
Why Your Fingerprint Needs Extra Protection
Many of us now unlock phones, pay bills, or sign in to apps with a fingertip instead of a password. That feels convenient and high‑tech, but it hides a serious problem: if someone steals a digital copy of your fingerprint, you cannot change it the way you change a password. This paper presents a new way to lock down fingerprint data on everyday gadgets so that even if hackers get into a device, they still cannot reuse or reverse‑engineer your fingerprint.

From Simple Unlock Code to Digital Treasure
Our phones and other “edge devices” constantly collect sensitive information—what we buy, where we go, and how we interact online. Fingerprints have become a popular way to guard this data because they are unique and easy to use. But today’s systems often store a processed fingerprint “template” that, if copied, can be replayed or used to fool other devices. Older encryption tools such as RSA, ElGamal, or RC5 can protect these templates, but they tend to be slow and power‑hungry on small gadgets like smartphones or smart locks, and they still leave gaps that skilled attackers can exploit.
Turning a Fingerprint into an Unbreakable Key
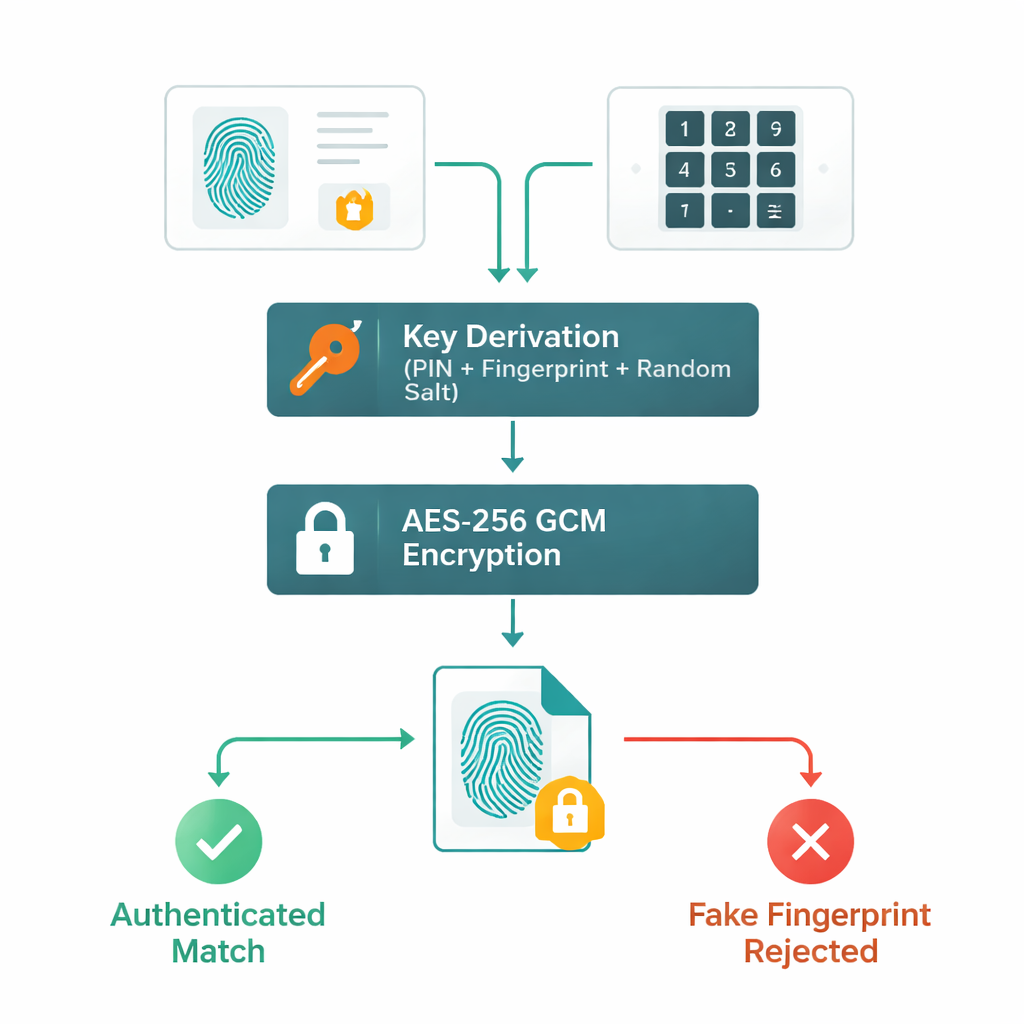
The authors propose a framework that treats your fingerprint not just as an ID, but as part of a one‑time, ultra‑strong cryptographic key. First, a fingerprint image is cleaned and enhanced so that its tiny ridge features, called minutiae, can be captured in a compact digital template. That template is then combined with your personal PIN, but not in a simple way. The PIN is run through a heavy‑duty hashing process (SHA‑512) and a key‑derivation routine that repeats calculations many thousands of times. At the same time, a special random number generator, inspired by lattice mathematics and a technique known as “learning with errors,” produces unpredictable “salt” values and unique nonces. All of these ingredients—fingerprint features, PIN, and lattice‑based randomness—are blended into a 256‑bit key used by the AES‑256 Galois/Counter Mode (GCM) encryption algorithm.
Fast Lock and Key on Small Devices
Once this key is created, the fingerprint template itself is encrypted into a small, scrambled data block less than one kilobyte in size. When you later unlock your device, the system scans a fresh fingerprint, regenerates the key from your new scan and PIN, and attempts to decrypt the stored block. If anything has been tampered with, AES‑GCM’s built‑in integrity check fails and access is denied. Because the random salt is produced by a lightweight lattice‑based generator rather than a full, heavy post‑quantum crypto system, the whole process runs in under a tenth of a second on standard phone‑class hardware, keeping the experience snappy while still resisting brute‑force guessing, replay attempts, and many “side‑channel” tricks that try to read keys indirectly.
Putting the System to the Test
To see how well their design works, the researchers used public fingerprint collections, including the widely used FVC2002 and SOCOFing datasets, plus synthetic prints created to mimic real ridge patterns. They measured how accurately the system could tell real users from imposters, and how long encryption and decryption took. The new framework correctly detected fake or mismatched fingerprints in 98.69% of cases—better than several competing schemes—and encrypted or decrypted templates in only about 20 milliseconds each. Additional analyses showed that encrypted templates looked essentially like random noise, with no visible structure for attackers to exploit, yet could still be perfectly restored during authorized use.
What This Means for Everyday Users
In plain terms, this work shows a way to make fingerprint‑based logins much safer without slowing down your phone or smart device. Your fingerprint never sits on the device as a readable picture or simple template; instead, it helps create a one‑time lock that only your combination of finger, PIN, and built‑in randomness can open. Even if attackers copy the encrypted data, they cannot reverse it to reconstruct your fingerprint or reuse it elsewhere. As future gadgets spread through smart homes, cars, and cities, approaches like this could let us rely on biometrics with greater confidence that our “unchangeable” body signatures stay private.
Citation: Sureshkumar, A., Maragatharajan, M., Jangiti, K. et al. A lattice-integrated AES framework for ultra-secure biometric protection on resource-constrained edge devices. Sci Rep 16, 7254 (2026). https://doi.org/10.1038/s41598-026-36054-8
Keywords: fingerprint security, biometric authentication, AES-256 encryption, edge devices, lattice-based cryptography