Clear Sky Science · en
Improving malware detection performance using hybrid deep representation learning with heuristic search algorithms
Why Your Phone’s Safety Is Getting Harder to Guarantee
Most of us now depend on smartphones for banking, shopping, work, and private conversations. At the same time, criminals are crafting ever more elusive malicious apps that can steal data, spy on users, or hijack devices. Traditional antivirus tools struggle to keep up. This study introduces a new way to spot dangerous Android apps using an advanced mix of deep‑learning techniques, aiming to deliver faster and more reliable protection in real‑world settings.
The Growing Threat Inside Everyday Apps
Malware—malicious software—has evolved from annoying viruses into a sophisticated toolset for cybercrime. On Android phones in particular, fake apps and poisoned downloads can quietly unlock access to banking details, personal photos, corporate secrets, or even whole networks. Criminals increasingly hide their code through tricks like encryption, code “packing,” and delaying when harmful functions are triggered, so that simple, one‑time scans no longer reveal what an app truly does. As a result, security systems must learn to recognize subtle behavior patterns rather than rely on fixed signatures or a limited list of known threats.
Teaching Machines to Recognize Dangerous Patterns
Machine learning and deep learning—forms of artificial intelligence that learn from data—have shown promise for malware detection. Instead of relying on handwritten rules, these systems are trained on large collections of apps labeled as safe or malicious. They learn which combinations of features, such as permissions, programming instructions, or usage histories, tend to signal danger. However, existing models often stumble when datasets are huge, imbalanced, or noisy, and many demand too much computing power for practical use on phones or other resource‑limited devices. They may also fail to adapt when criminals invent entirely new styles of attack, leaving gaps in protection.
A Hybrid Brain for Smarter App Screening
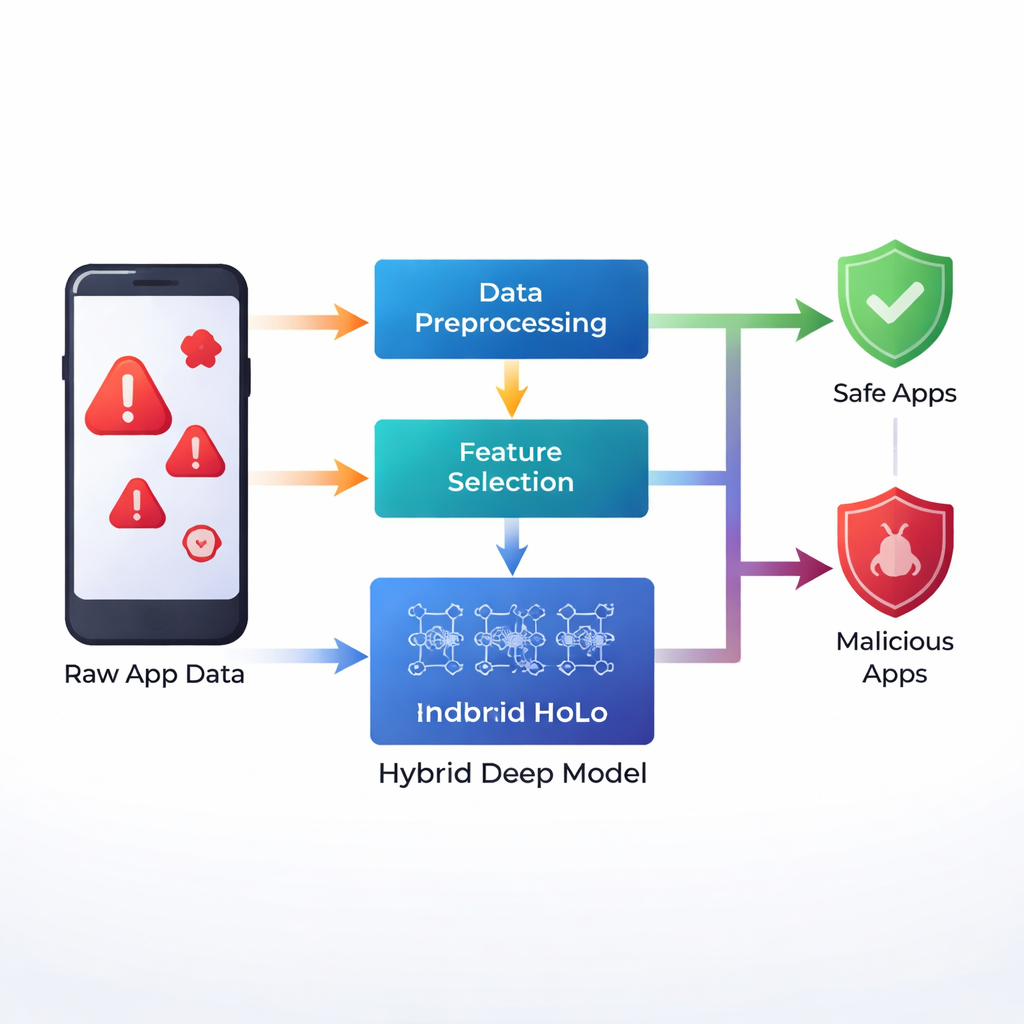
The authors propose a new framework, called IMDP‑HDL, that combines several deep‑learning building blocks to better capture the clues hidden in Android app data. First, they use a statistical step known as Z‑score standardization, which rescales every feature into a common range so that no single type of information dominates the learning process. They then apply a heuristic search method to select only the most informative features, which trims away noise and speeds up training. The heart of their system is a hybrid network that blends three ideas: convolutional layers, which are good at finding local patterns; a bidirectional long short‑term memory (BiLSTM) module, which can follow sequences of events forward and backward in time; and a self‑attention mechanism, which teaches the model to focus on the most relevant parts of the data when making a decision.

How Well the New System Performs
To test their approach, the researchers used several publicly available Android malware datasets, together comprising over fifteen thousand apps and hundreds of descriptive features per app. They trained their hybrid model in stages, gradually increasing the number of training cycles, and tracked classic performance measures such as accuracy, precision, recall, and a combined score called F1. With the main Android malware dataset, the IMDP‑HDL framework reached an accuracy of about 99.2 percent, outpacing a variety of rival methods, including conventional neural networks, recurrent networks, and other hybrid deep‑learning models. It also ran noticeably faster than competing deep‑learning systems, finishing its analysis in less than five seconds where others needed roughly twice or three times as long.
Limits Today and Hopes for Tomorrow
Despite these strong results, the authors acknowledge that the model was trained on specific datasets that may not reflect the full diversity of threats circulating in the wild. Fast‑moving tactics like zero‑day exploits and heavily mutated malware families could still slip through. Running such a model directly on phones, cars, or tiny Internet‑of‑Things devices may also be challenging when memory and processing power are scarce. The researchers therefore see this work as a foundation. They recommend expanding to broader datasets, adding mechanisms that allow the model to update itself as new threats emerge, and exploring ways to explain its decisions so security analysts and users can understand why a given app was flagged.
What This Means for Everyday Users
In simple terms, this study shows that by blending several advanced learning techniques, computers can become markedly better at telling safe apps from dangerous ones, even when the bad actors try hard to hide. While it will not eliminate the need for careful user behavior—such as downloading apps only from trusted sources—it points the way toward lighter, quicker, and more accurate defenses built into future security tools. If refined and deployed widely, approaches like IMDP‑HDL could make it much harder for hidden malware to live undetected on the smartphones and connected devices we rely on every day.
Citation: Anuradha, A., Chouhan, A.S. & Srinivas Rao, S. Improving malware detection performance using hybrid deep representation learning with heuristic search algorithms. Sci Rep 16, 4847 (2026). https://doi.org/10.1038/s41598-026-35481-x
Keywords: Android malware, deep learning security, mobile cybersecurity, malicious apps, neural networks