Clear Sky Science · en
A hybrid machine learning approach for detecting DDoS attacks in software-defined networks
Why stopping internet traffic floods matters
When you watch a movie online, shop, or use cloud apps, your data travels through networks that must stay fast and reliable. A popular new way to run these networks, called software-defined networking (SDN), gives companies more control and flexibility—but it also opens the door to powerful cyberattacks known as distributed denial-of-service (DDoS) attacks. These attacks overwhelm systems with junk traffic until real users are locked out. This study shows how a tailored form of machine learning can spot these traffic floods early and accurately, helping keep online services available when we need them most. 
A new kind of network, with new weak spots
Traditional networks rely on devices like routers that both decide where to send data and actually move it. SDN separates these roles: a central “brain” called a controller decides how traffic should flow, while simpler switches just follow its instructions. This separation makes networks easier to manage, cheaper to build, and more adaptable for heavy-duty uses such as data centers, cloud platforms, 5G, and the Internet of Things. But there is a trade-off. Because so much power is concentrated in the controller and exposed through open software interfaces, attackers can focus their efforts there. If they can drown the controller in bogus requests, they can cripple the entire network at once.
How attackers turn helpful features into weapons
DDoS attacks enlist armies of hacked devices—anything from home computers to unsecured cameras—to send waves of unwanted traffic at a target. In SDN, this target is often the controller or the switches that report to it. Each new or unusual flow of data can force the controller to make a decision and update rules in the switches. During a DDoS flood, the number of flows and control messages can soar, clogging the controller’s resources and blocking normal users. Previous detection tools often relied on old, non-SDN data or fixed thresholds, meaning they struggled with newer, sneakier attacks and the shifting patterns of modern network traffic.
Building a realistic picture of attack and normal life
To address these gaps, the researchers built their own SDN test environment instead of recycling legacy datasets. Using a widely used open-source SDN controller (Ryu) and a virtual switch, they created a simple but carefully controlled network in which they could generate both everyday traffic and several types of DDoS floods (based on TCP, UDP, and ICMP). The controller regularly collected detailed statistics about each flow of data and each switch port, such as how long flows lasted, how many packets and bytes passed through, how many flows were active, and how much bandwidth each port used. These measurements were turned into 22 focused features, including new averages that capture how much data each flow carries. Every flow record was automatically labeled as either benign or malicious, resulting in a medium-sized, SDN-specific dataset of 99,225 examples.
A teamed-up learning engine to spot trouble
Armed with this dataset, the team compared a range of machine-learning methods for classifying flows as normal or attack traffic. They found that simple models like logistic regression or basic decision trees missed many of the subtle patterns hidden in the statistics. Two tree-based “ensemble” methods—Random Forest and XGBoost—stood out, each handling complex relationships in different ways. The researchers then combined them into a hybrid model that lets both methods vote on the outcome. This teamed-up detector reached an accuracy of 99.36%, with very few false alarms and almost no missed attacks. Tests using receiver operating characteristic (ROC) curves showed performance close to perfect, meaning the model can distinguish attack traffic from normal traffic across a wide range of settings. 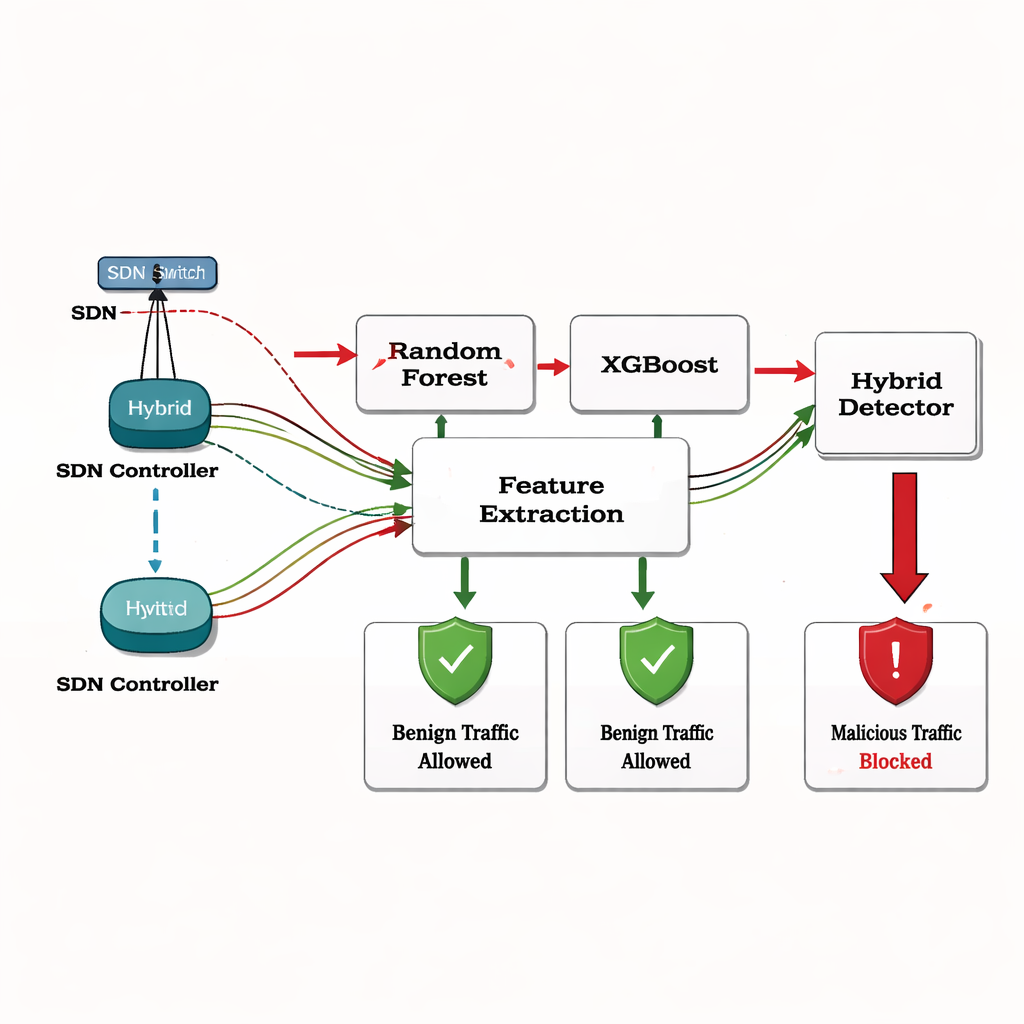
From early warning to automatic defense
Beyond detection, the authors outline how such a model could be wired directly into an SDN controller. As the controller gathers live statistics, it could feed them into the trained model and, when a flow looks malicious, instantly push new rules to the switches to drop, slow, or block that traffic. While this study tested only in a controlled, single-switch setup with synthetic traffic, it shows that carefully chosen SDN-aware features, combined with a smart hybrid learning approach, can reliably spot DDoS attacks in time to respond. For non-specialists, the key message is that pairing modern network designs with equally modern, data-driven defenses can make the online services we depend on more resilient against large-scale traffic floods.
Citation: Mahar, I.A., Aziz, K., Chakrabarti, P. et al. A hybrid machine learning approach for detecting DDoS attacks in software-defined networks. Sci Rep 16, 6533 (2026). https://doi.org/10.1038/s41598-026-35458-w
Keywords: software-defined networking, DDoS attacks, machine learning, network security, traffic detection