Clear Sky Science · en
Combination of quantum-based optimizer and feature pyramid network for intrusion detection in Cloud-IoT environments
Smarter shields for a world of connected gadgets
From smart locks and baby monitors to factory sensors and hospital gear, billions of Internet‑of‑Things (IoT) devices now talk to powerful cloud servers. That convenience comes with a hidden cost: attackers can slip in through tiny gadgets and spread across the cloud, stealing data or knocking services offline. This paper introduces a new, AI‑driven defense system designed to spot such intrusions more accurately and adapt to fast‑changing attack tricks in modern Cloud‑IoT networks.
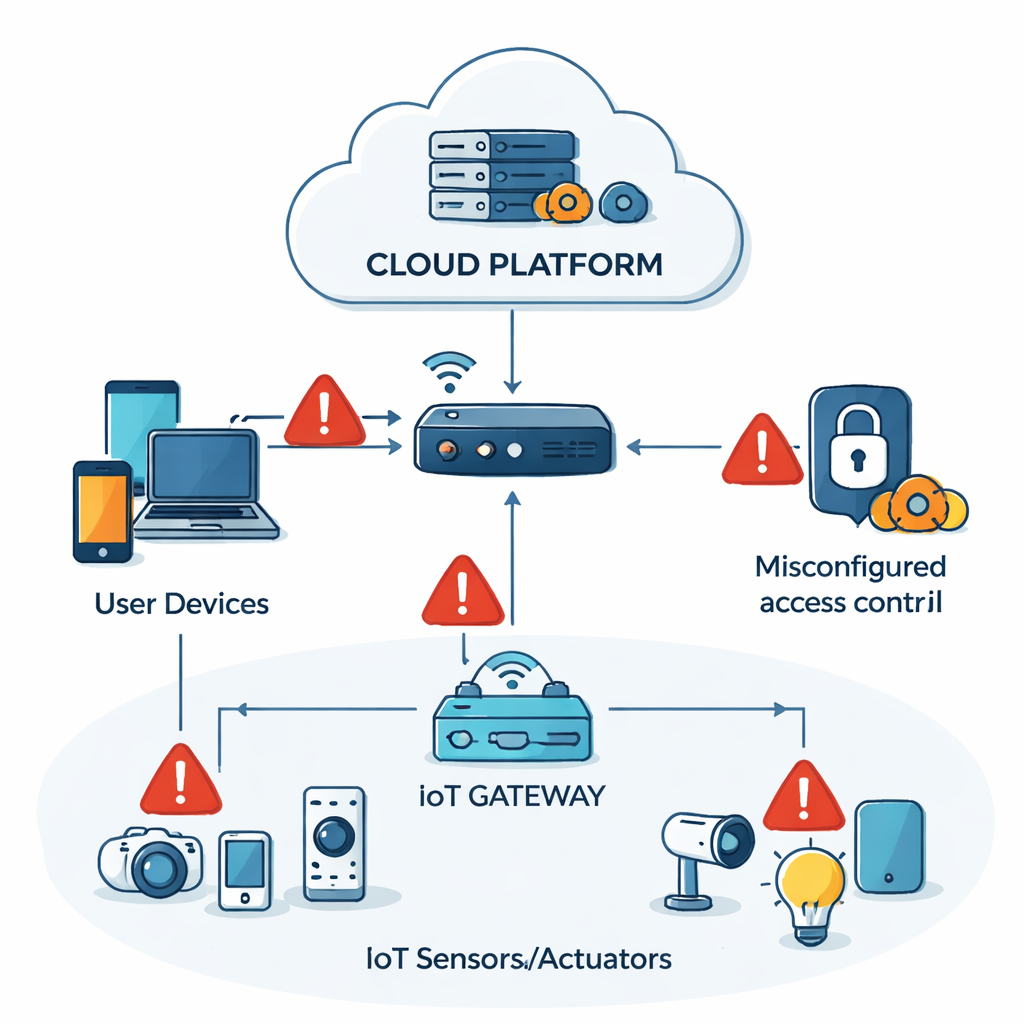
Why everyday smart devices are easy targets
Most IoT gadgets are built to be cheap, small, and power‑efficient, not heavily armored. They often run weak encryption and outdated firmware, while the cloud platforms that manage them present many doors and corridors an attacker can exploit. A real‑world example cited by the authors involves a 2023 breach of a chain of smart hotels, where hackers abused vulnerable door locks and HVAC sensors, then moved through the cloud backend to disrupt operations in dozens of properties. Traditional intrusion detection systems, which either look for known attack signatures or crude anomalies, struggle in this setting: network traffic is high‑dimensional, mixes many numeric and categorical fields, and attack patterns evolve quickly. As a result, subtle, multi‑stage attacks often blend into normal background activity.
Turning network logs into images the AI can truly see
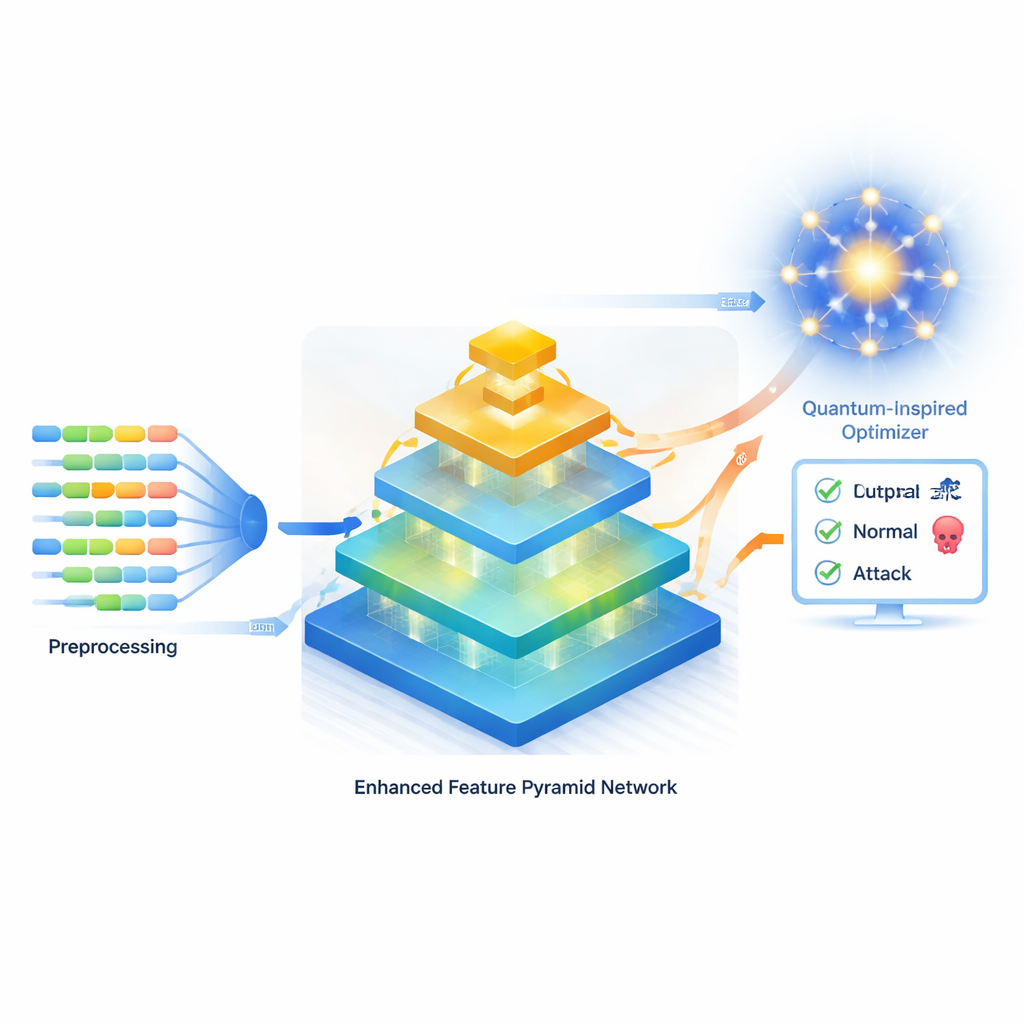
The authors propose a fresh approach that starts by carefully cleaning and reshaping raw network logs. Categorical fields such as protocol type or service name are turned into numerical vectors, while continuous quantities like packet size and flow duration are normalized so none dominates the learning process. To cope with the fact that real attacks are rare compared with normal traffic, they use a technique called SMOTE to generate realistic synthetic examples of underrepresented attack classes, reducing bias toward the majority class. Crucially, they then rearrange this tabular data into structured “pseudo‑images,” allowing a powerful vision‑style neural network, their Enhanced Feature Pyramid Network (EFPN), to analyze patterns at multiple scales instead of treating each feature in isolation.
A multi‑layered “pyramid” that reads patterns big and small
The EFPN is inspired by image‑recognition systems that excel at spotting both fine details and broad shapes. At its core is a backbone similar to ResNet34, which builds a hierarchy of feature maps. A bottom‑up pathway captures increasingly abstract patterns, while a top‑down pathway uses deconvolution (a smarter form of upsampling) to recover finer spatial detail that simpler methods often blur away. A Deep Semantic Embedding module then blends low‑level, detail‑rich signals with high‑level, context‑aware ones, preserving both “close‑up” and “wide‑angle” views of the traffic. Finally, a two‑branch fusion stage processes global patterns and local nuances in parallel—using specialized convolutions that effectively widen the receptive field—before merging them into a single, compact representation used for classification.
Borrowing ideas from children’s sketches and quantum physics
Designing the network is only half the battle; tuning its many knobs—such as learning rate, filter sizes, and the number of feature maps—strongly affects accuracy. Instead of relying on slow grid search or standard optimizers, the authors introduce a quantum‑enhanced metaheuristic called Q‑CDDO (Quantum‑Enhanced Child Drawing Development Optimizer). It is loosely inspired by how children’s drawings evolve: early scribbles, imitation of better examples, an emerging sense of proportion (linked to the golden ratio), creativity, and memory of successful patterns. Mathematically, this is encoded in a population‑based search that explores and refines candidate hyperparameter sets. The “quantum‑enhanced” part represents each candidate as a string of qubits in superposition; by applying rotation gates guided by the best solutions found so far, the algorithm can explore the vast search space more broadly while still homing in on promising regions.
Putting the new defense to the test
The full EFPN–Q‑CDDO framework was evaluated on two widely used benchmark datasets: CIC‑IDS‑2017, which mimics a conventional enterprise network with multiple attack types, and Bot‑IoT, which focuses on IoT‑style botnet traffic. After five‑fold cross‑validation and careful handling of class imbalance, the system achieved 96.3% accuracy on CIC‑IDS‑2017 and 94.6% on Bot‑IoT, beating several strong baselines, including advanced deep‑learning hybrids and other metaheuristic‑tuned models. It also showed higher F1‑scores—a balance of precision and recall—indicating fewer missed attacks and fewer false alarms. Ablation studies demonstrated that both main ingredients matter: upgrading a standard feature pyramid to the enhanced version improves results, and swapping in Q‑CDDO for conventional optimizers further boosts performance and yields smoother, faster convergence during training.
What this means for securing the connected world
For non‑experts, the key takeaway is that defending Cloud‑IoT systems is not just about stronger passwords or better firewalls; it requires smarter pattern recognition that can read complex, noisy traffic without drowning analysts in false alerts. By converting raw network logs into image‑like structures and pairing a multi‑scale neural “pyramid” with a quantum‑inspired tuning strategy, this work delivers an intrusion detector that is both more accurate and more adaptable than many existing systems. While quantum effects here are simulated rather than relying on real quantum hardware, the ideas help the optimizer escape narrow local solutions and find better settings. As IoT deployments continue to expand into homes, cities, and critical infrastructure, approaches like EFPN–Q‑CDDO could form a powerful part of the invisible security fabric that keeps these connected environments resilient against ever‑evolving cyber threats.
Citation: Hajlaoui, R., Shalaby, M., Alfilh, R.H.C. et al. Combination of quantum-based optimizer and feature pyramid network for intrusion detection in Cloud-IoT environments. Sci Rep 16, 7244 (2026). https://doi.org/10.1038/s41598-026-35242-w
Keywords: intrusion detection, cloud IoT security, deep learning, quantum-inspired optimization, network traffic analysis