Clear Sky Science · en
Efficient feature ranked hybrid framework for android Iot malware detection
Why your smart gadgets need better bodyguards
From smart doorbells and TVs to factory sensors and connected cars, billions of devices now run on Android. That convenience comes with a hidden cost: these gadgets are increasingly targeted by malware that can steal data, spy on users, or hijack whole networks. This paper presents a new way to spot such attacks quickly and efficiently, even on low‑power devices, offering a path to safer homes, hospitals, cities, and industries.

The growing problem inside everyday devices
Android has become the default operating system for many Internet of Things (IoT) devices because it is flexible, open, and cheap to adapt. The same openness makes it attractive to criminals. Many Android‑based gadgets have no antivirus protection, rely on untrusted app stores, and rarely receive timely security updates. Recent threats—including large botnets that launch internet‑clogging attacks and spyware that silently harvests passwords, messages, and even biometrics—show how quickly mobile and IoT malware is evolving. Traditional defenses, such as signature matching and simple permission checks, struggle to keep up, especially when attackers hide their code or change their behavior on the fly.
Looking at apps from two angles at once
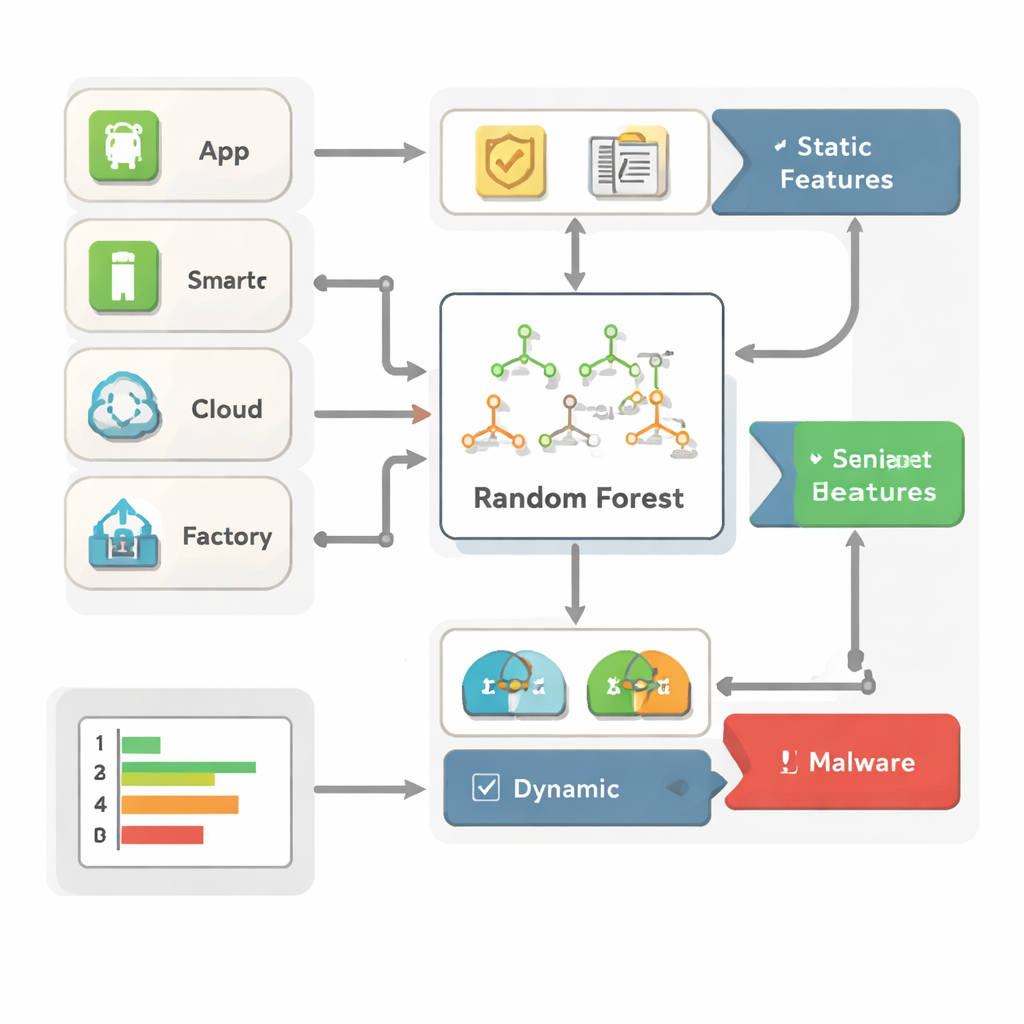
The authors argue that no single view of an app is enough anymore. Instead, they combine two complementary views. The first, often called static analysis, inspects what an app asks for and how it is built—its permissions, the programming interfaces it touches, and basic metadata—without ever running it. The second, dynamic analysis, watches what the app actually does when it runs: how it uses memory and the processor, what system calls it makes, and how it communicates over the network. By fusing these two kinds of clues, the framework can catch both obvious threats and more subtle, shape‑shifting malware that might fool one method alone.
Teaching a forest of decision trees to spot bad behavior
To turn this rich mix of clues into decisions, the system uses a machine‑learning method called Random Forest, which can be thought of as a crowd of simple decision trees that vote on whether an app is benign or malicious. Crucially, the authors do not feed every raw detail into this model. Instead, they rank features using two measures of usefulness and keep only the most informative ones. This trimming step cuts the size of the data the model has to process, speeds up detection, and makes it clearer which signals—such as certain text‑message permissions, suspicious network ports, or odd memory patterns—are driving its verdicts. Because Random Forests naturally highlight which inputs matter most, security analysts can better understand and trust the system’s choices.
Testing across different types of attacks and data
The framework is evaluated on four well‑known collections of Android and industrial IoT data. One (Drebin) focuses on app permissions and code, another (TUANDROMD) includes more detailed app traits, a third (CCCS‑CIC‑AndMal‑2020) tracks how apps behave at runtime, and a fourth (CIMD‑2024) logs years of network activity from real industrial devices. On the first three, the system reaches strikingly high accuracy—around 99 to 100 percent—with similarly strong precision and recall, meaning it rarely misses malware or mislabels clean apps. It also runs quickly and with modest memory needs, making it suitable for edge devices that cannot host heavy deep‑learning models. The industrial dataset exposes an important limitation: because benign traffic vastly outnumbers attacks, a simple model can appear accurate while still missing many rare but dangerous threats, underscoring the need for special techniques to handle skewed data.
Limits today and how this can improve tomorrow
While the proposed approach performs extremely well on several benchmarks, it is less effective when malicious traffic is rare and varied, as in real industrial networks. The authors openly note that, in such cases, the model tends to favor the majority “safe” class and overlooks smaller families of malware. They suggest improving this with smarter sampling, cost‑sensitive training, and continued feature engineering, as well as testing against cleverly disguised malware that attempts to fool learning‑based systems. Even so, the work shows that a carefully crafted, transparent model can deliver near‑state‑of‑the‑art protection without the heavy costs of deep learning, offering a practical blueprint for defending the growing universe of Android‑powered things.
What this means for everyday security
For non‑experts, the takeaway is simple: it is possible to build malware defenses that are both smart and light enough to run on everyday devices, and clear enough that human experts can audit how they work. By combining what apps claim they will do with what they actually do in practice, and by focusing on the most telling warning signs, this framework turns Android‑based phones and gadgets into far less inviting targets. With further refinement for highly unbalanced, real‑world data, similar systems could become a key part of the invisible safety net shielding our connected homes, hospitals, factories, and cities from digital intrusion.
Citation: Saeed, N.H., Hamza, A.A., Sobh, M.A. et al. Efficient feature ranked hybrid framework for android Iot malware detection. Sci Rep 16, 3726 (2026). https://doi.org/10.1038/s41598-026-35238-6
Keywords: Android malware, IoT security, machine learning, hybrid analysis, random forest