Clear Sky Science · en
Construction of multi-state chaotic systems and applications to image encryption
Why scrambling pictures matters for your privacy
Photos and videos now flow constantly through phones, clouds, and social networks, making it vital to lock them away from prying eyes. Conventional encryption tools like AES work well for text and small files, but they can be slow or inefficient for the huge, colorful images that dominate modern data traffic. This article explores a different approach: using the natural unpredictability of chaotic systems—mathematical models that behave like turbulence or weather—to design faster, harder‑to‑crack image locks.
A new way to stir up digital chaos
The authors start from a simple question: can we build stronger chaos not by inventing entirely new equations, but by carefully tweaking what we already know? They focus on the classic Lorenz system, a three‑equation model famous for its butterfly‑shaped attractor, and show that its wild behavior can be enriched by adjusting two ingredients. First, they raise each internal variable to different powers, which subtly reshapes how the system evolves over time. Second, they add tiny constant offsets—"small parameters"—to these variables. Even though these changes look modest on paper, simulations reveal that they significantly alter the motion of the system while still keeping it in a fully chaotic state. 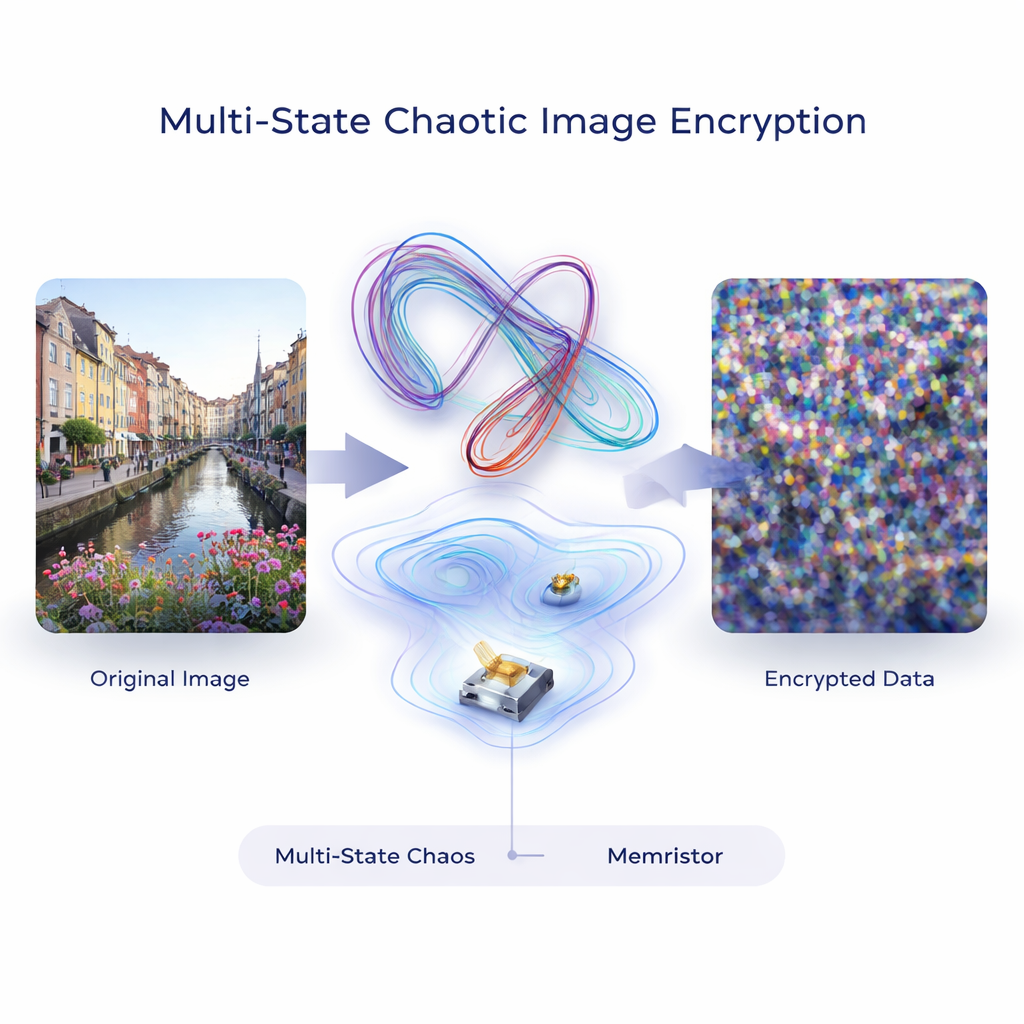
Adding memory to chaos with electronic “ink”
To push this idea further, the team connects the chaotic model to a memristor, an electronic component whose resistance depends on its past—like a wire that remembers the currents that once flowed through it. By feeding the memristor’s time‑varying behavior back into the equations, the system’s trajectories unfold into multi‑wing patterns: instead of the classic two‑lobed “butterfly,” the model can display four, eight, or even sixteen wings, depending on how strongly the memristor is coupled. Changing starting conditions or parameters reshapes these wings but does not destroy the underlying chaos. Tests using Lyapunov exponents and a diagnostic called SALI confirm that, across many settings, the system stays highly sensitive and unpredictable, two hallmarks of good cryptographic randomness.
Making sure the recipe works in many settings
Real‑world signals often have memory and long‑range effects, so the authors check whether their construction still functions when they move beyond ordinary calculus to fractional calculus, which allows derivatives of non‑integer order. Rewriting their equations in this framework and simulating them with specialized numerical methods, they again observe robust multi‑wing chaotic motion. They also plug the same design strategy into two other well‑known models, the T system and the Liu system. In each case, combining state‑variable reshaping, small parameters, and memristor‑like terms produces rich chaotic attractors. This suggests that their method is not tied to one particular equation, but offers a general recipe for engineering complex chaos.
From swirling math to stronger image locks
Building on this chaotic engine, the authors design a full image encryption scheme. The chaotic system generates long sequences of seemingly random numbers, which are turned into two‑dimensional maps that shuffle the rows and columns of an image (permutation) and then alter pixel values (diffusion). Because tiny changes in initial conditions drastically change the chaotic sequence, the effective key space is enormous—on the order of 2^172 possible keys—well beyond the reach of brute‑force search. Tests on standard color photographs show that the encrypted pictures look like uniform noise, with flat histograms, high information entropy close to the theoretical maximum, and almost no correlation between neighboring pixels. 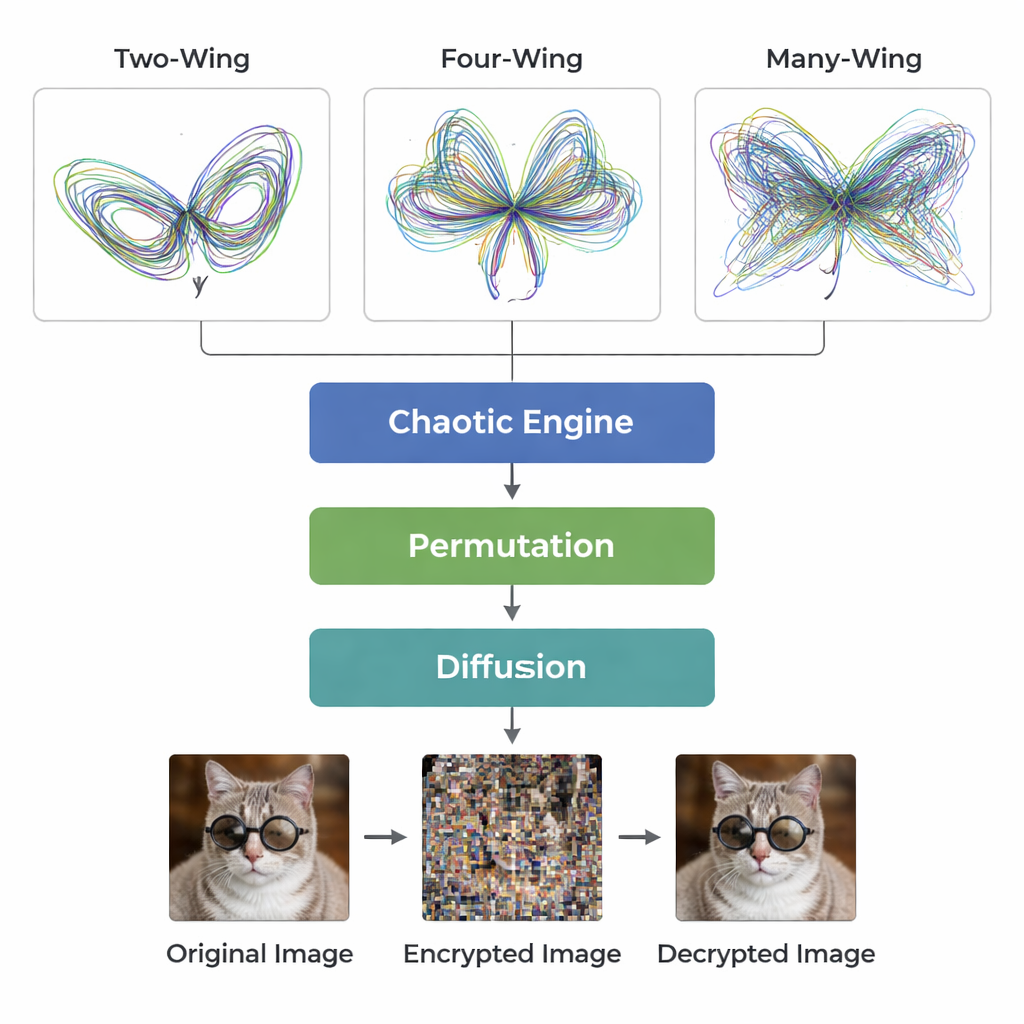
Standing up to noise and attacks
The team also asks how their system behaves under realistic abuse. When random “salt and pepper” noise or large blacked‑out regions are injected into the encrypted images, the decrypted results still preserve recognizable content, and quality scores degrade gracefully rather than collapsing. Statistical tests such as chi‑square analysis, and measures of how much the ciphertext changes when a single pixel in the original image is modified, all point to strong resistance against common cryptanalytic strategies. In short, the scheme is both sensitive enough to changes to thwart attackers and robust enough to tolerate data loss and interference.
What this means for everyday security
For non‑specialists, the main message is that the same kind of delicate, butterfly‑effect chaos that shapes weather forecasts can also be engineered and harnessed to protect digital pictures. By systematically tuning existing chaotic models with small parameter shifts, variable reshaping, and memory‑like components, the authors create a flexible family of chaotic generators and show how to turn one of them into an efficient image cipher. Their tests indicate that this approach can hide visual information extremely well while remaining fast enough for practical use, suggesting a promising path toward future encryption tools tailored to the massive image streams of the digital age.
Citation: Wang, X., Wu, H., Yan, A. et al. Construction of multi-state chaotic systems and applications to image encryption. Sci Rep 16, 5518 (2026). https://doi.org/10.1038/s41598-026-35222-0
Keywords: chaotic image encryption, multi-wing attractor, memristor, fractional-order chaos, information security